|
IT – Bring Your Own Device (BYOD) Policy
Introduction and Purpose 1 1 This policy stipulates how Bring Your Own Device (BYOD) equipment should be used at NMITE |
|
Ten rules for Bring Your Own Device (BYOD)
Should you allow BYOD? The rapid proliferation of mobile devices entering the work- place appears to be like divine intervention to many IT leaders |
|
BRING YOUR OWN DEVICE (BYOD) POLICY
BYOD Policy Buckinghamshire New University Page 2 of 4 Introduction 1 The University is committed to meeting its legal and duty of care obligations while |
|
Bring Your Own Device (BYOD) Policy
This policy defines the appropriate use and procedures for using personally owned computing devices on the Centenary network and the storage of intellectual |
|
Bring Your Own Device (BYOD) Policy
This policy applies to all University staff that process University data on personally owned devices and covers computers and mobile devices (phones and tablets) |
|
Bring Your Own Device Policy (BYOD) Newman University
17 nov 2022 · This policy covers the use of non-University owned/issued electronic devices which could be used to access corporate systems and store |
Bring your Own Device (BYOD) is the set of policies in a business that allows employees to use their own devices – phone, laptop, tablet or whatever – to access business applications and data, rather than forcing employees to use company-provided devices for that purpose.
What are 3 levels of BYOD?
What level of access does BYOD offer?
Level 1.This is the basic access level. Level 2.
This is also called controlled access. Level 3.
This is the full access level which grants employees complete access to all corporate resources -- including confidential data and apps -- on their own devices.
|
POLICY - Bring Your Own Device (BYOD) and Acceptable Use
This policy provides guidelines for using personally owned devices and related software for corporate use. Applicability. The BYOD policy applies to all |
|
BYOD-Policy.pdf
Bring your own device (BYOD) is the act of using a personal computing device (computer tablet |
|
Bring Your Own Device (BYOD) Policy
It sets out the responsibilities of all those. (here on known as the R&R Data and Digital Services “Customers”) who use Bring Your Own Devices. (BYOD) to |
|
HubSpot
Developing a company BYOD policy is a good project for thinking things through before allowing employees to use their own smartphones and tablets within an |
|
BRING YOUR OWN DEVICE (BYOD) POLICY
BYOD Policy. Buckinghamshire New University. Page 2 of 4. Introduction. 1. The University is committed to meeting its legal and duty of care obligations |
|
BYOD Policy: Use of Personally Owned Devices for University Work
This policy is for all staff using personally owned devices such as smart phones tablet computers |
|
SCHOOL BYOD POLICY
By facilitating Bring Your Own Device (BYOD) MFHS empowers its students and gives /technology/computers/mobile-device/BYOD_2013_Literature_Review.pdf. |
|
Information Security BYOD Procedure
1 July 2017 Mobile device management (MDM). The University has the ability through the MDM capabilities of Office 365 |
|
BRING YOUR OWN DEVICE (BYOD) POLICY
Policy Overview. Bring Your Own Device (BYOD) refers to employees using personally-owned mobile devices (i.e. smartphones tablets and wearables) to connect |
|
Bring Your Own Device Policy (BYOD)
24 May 2018 This policy covers the use of non-University owned/issued electronic devices which could be used to access corporate systems and store ... |
|
Bring Your Own Device (BYOD) and Acceptable - The Horton Group
This policy provides guidelines for using personally owned devices and related software for corporate use Applicability The BYOD policy applies to all employees |
|
BYOD Policy - Q-CERT
Bring Your Own Device (BYOD) Security Policy Version: 1 1 Author: Cyber Security Policy and Standards Document Classification: Public Published Date: |
|
BYOD-Policypdf - Newman University, Birmingham
24 mai 2018 · Bring Your Own Device Policy (BYOD) The Purpose of this Document: This document describes acceptable use pertaining to using your own |
|
Bring Your Own Device (“BYOD”) Policy
Bring Your Own Device (“BYOD”) Policy MIoD grants its employees the privilege of purchasing and using smartphones and tablets of their choosing at work for |
|
BYOD Policy: Use of Personally Owned Devices for University Work
This policy is about reducing the risk in using BYOD Such risks may come from your BYOD being lost, stolen, used or exploited in such a way to take advantage of |
|
BYOD POLICY - WhistleBlower Security
Share this eBook: 9 ITEMS TO INCLUDE IN YOUR BYOD POLICY BYOD policy 1 [http://www cisco com/web/about/ac79/docs/re/BYOD_Horizons-Global pdf |
|
Bring Your Own Device BYOD Policy - Clayton State University
BYOD Policy July 2017 BYOD Bring Your Own Device Policy Personally- Owned Device Usage at Clayton State University This policy applies to any hardware |
|
Bring Your Own Device (BYOD) Policy - University of Reading
1 Bring Your Own Device (BYOD) Policy 1 Purpose This policy applies to all University staff that process University data on personally owned devices 1 1 |
|
IDENTIFYING BEST PRACTICES FOR A BYOD POLICY - CORE
The categories are BYOD Risks and Disadvantages, BYOD Mitigation Strategies , and BYOD Benefits The View PDF or View Online functions provide the ability to |
|
SAMPLE BYOD POLICY TEMPLATE - HubSpot
Developing a company BYOD policy is a good project for thinking things through before allowing employees to use their own smartphones and tablets within an |
|
[PDF] Bring Your Own Device
This policy document is intended to provide guidance on questions that companies should ask themselves when establishing their own policies and related |
|
[PDF] Bring your own device - EY
typically called bring your own device (BYOD), presents an attractive option to organizations BYOD security policy controls, often through a unified management approach combining automated tools and manual penetration testing, and |
|
[PDF] Bring Your Own Device (“BYOD”) Policy
Bring Your Own Device (“BYOD”) Policy MIoD grants its employees the privilege of purchasing and using smartphones and tablets of their choosing at work for |
|
[PDF] BYOD Policy: Use of Personally Owned Devices for University Work
This policy is for all staff using personally owned devices such as smart phones, tablet computers, laptops, netbooks and similar equipment, to store, access |
|
[PDF] BYOD Policy - Q-CERT
Bring Your Own Device (BYOD) Security Policy Version 11 Author Cyber Security Policy and Standards Document Classification Public Published Date |
|
[PDF] BYOD-Policypdf - 694 KB - Newman University, Birmingham
May 24, 2018 · Bring Your Own Device Policy (BYOD) The Purpose of this Document This document describes acceptable use pertaining to using your own |
|
[PDF] Bring Your Own Device Policy - University of Strathclyde
2 Information Security Policies All relevant University policies still apply to staff using BYOD Staff should note, in particular, the University's Information Security |
|
[PDF] byod policy - WhistleBlower Security
following are nine important items to include in your BYOD policy 1 [ ciscocom web about ac79 docs re BYOD Horizons Global pdf Percentage of |
|
[PDF] Bring Your Own Device (BYOD) and Acceptable - The Horton Group
The BYOD and Acceptable Use Policy are part of the corporate Information Security Program Information security policies are the principles that direct managerial |
- byod policy template
- simple byod policy
- gdpr byod policy template
- byod security policy
- byod acceptable use policy
- byod pdf
- byod standards pdf
- bring your own device policy gdpr
- byod policy sample pdf
- byod policy example pdf
- byod security policy pdf

Sample Bring-Your-Own-Device (Byod) Policy Download Printable PDF
Source:https://www.wordlayouts.com/wp-content/uploads/2016/06/BYOD-Policy-Example-pdf-1.png
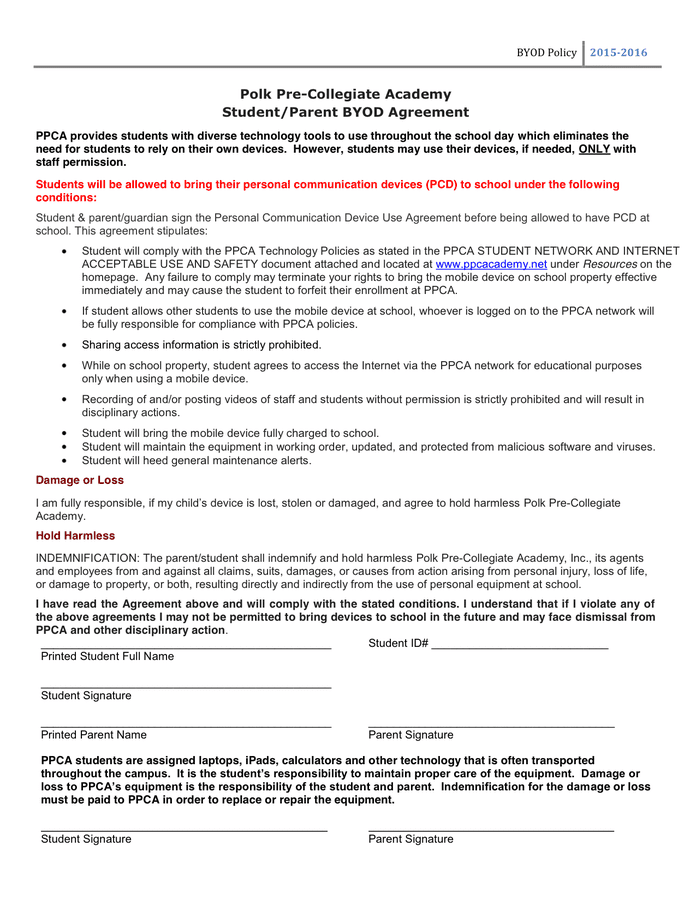
BYOD Policy Templates - 4 Best Samples and Examples
Source:https://static.dexform.com/media/docs/2867/byod-policy_1.png

BYOD Policy Sample - download free documents for PDF Word and Excel
Source:https://s1.manualzz.com/store/data/010720039_1-5000d49b167be860c471bbc0a2aeaa48.png
Sample BYOD Policy
Source: Manualzz
Bring Your Own Device Policy Byod Template
Source: by Business-in-a-Box™

BYOD Policy Templates - 4 Best Samples and Examples
Source:https://www.pdffiller.com/preview/61/541/61541804.png
byod policy sans
[PDF] identifying best practices for a byod policy - Semantic Scholar
- mdm byod policy
- simple byod policy
- byod security policy
- bring your own device policy pdf
- mobile device policy template
- byod policy for small business
- byod pdf
- byod remote access policy
- byod policy template sans
- byod policy sample sans
byod policy template for healthcare
[PDF] Mobile Devices and Health Information Privacy and - HealthITgov
- byod policy template for healthcare
- byod policy template for schools
- byod policy for small business template
byod policy template sans
[PDF] Mobile Device Acceptable Use Policy
- mdm byod policy
- byod policy for small business
- byod security policy
- mobile device policy template
- simple byod policy
- byod reimbursement policy
- company owned electronic device policy
- byod remote access policy
byod policy university
[PDF] Bring Your Own Device Policy - Newman University, Birmingham
- byod policy pdf
- byod policy template
- gdpr byod policy template
- byod policy for small business
- byod policy 2019
- bring your own device policy uk
- google byod policy
- simple byod policy