How do I stop a browser from severing connections?
Clear your system’s DNS cache to sever connections to malicious software programs Utilize a program or tool that deleted browser hijackers and modifications, or one that scans for and removes spyware Reset your browser homepage settings. In more extreme cases, uninstall and then reinstall your browser.
What should I do if I have problems with web browser redirect virus?
If you are still having problems with Web Browser Redirect Virus then you should also reset your browsers back to their default configuration. Please note that this method will remove all add-ons, extensions, toolbars and other customizations but will leave your bookmarks and favorites intact.
What should I do if my computer is not detecting malware?
Be sure to scan your computer for malware -- such programs should be detected as malware by most antivirus programs. If your existing antivirus program isn't detecting any malware, you may want to get a second opinion from a different antivirus program. Windows program installers have historically abused the user's browser.
What happens if a browser is infected with malware?
When a browser is infected with malware, your homepage or search engine might change without your consent, or you’ll see pop-up ads and unwanted advertisements not originating from the sites you are browsing. The most common types of browser infections are browser hijackers and adware.
Remove Browser Redirect Viruses from Windows
STEP 1: Use Rkill to terminate malicious processesSTEP 2: Uninstall malicious programs from your computerSTEP 3: Remove malicious browser policies from WindowsSTEP 4: Remove malicious files and folders from Windows malwaretips.com
Delete Malicious Scheduled tasks.
This infection may create a malicious scheduled task in the Task Scheduler to ensure that it is automatically reinstalled every 5 minutes after it has been deleted. This task may run at regular intervals to ensure that the infection persists on your system. 1. Search for “Task Scheduler” in the windows search as shown below.. You can also open the
Delete Malicious Files Located in AppData\\Roaming Folder
We will now delete the malicious file that is located in the AppData\\Roaming folder. 1. Search for “Run” in the windows search as shown below, or press the Windows + R button to open the Runapp. 2. In the run app text box, enter “%AppData%” and click OK. Windows will directly open up the Roamingfolder which is inside the AppData folder. 3. In the A
Delete Malicious Files Located in AppData\\Local Folder
Next, we will delete the malicious folders that are located in the AppData\\Local folder and the malicious Chrome browser extensions. 1. Search for “Run” in the windows search as shown below, or press the Windows + R button to open the Runapp. 2. In the run app text box, enter “%localappdata%” and click OK. Windows will directly open up the AppData\\
Remove Chrome Shortcut Modification
This malware can hijack your browser shortcuts to target the malicious files. Here is a short guide on how to remove the Chrome shortcut modification: 1. Right-click on the Google Chrome shortcut on your desktop or Start Menu and select “Properties“. 2. Under the Shortcut tab, look for the “Target” field. This is where any added commands to the sho

How to remove browser redirect virus manually Virus Removal Guide

How to Remove Fake Virus Warning from Microsoft Edge

How to Remove Chrome Redirect Virus? Clean Google Chrome
|
How to remove Adware and pop-up ads (Removal Guide) STEP 1
The AdwCleaner utility will scan your computer and web browser for malicious files adware browser extensions and registry keys |
|
Scare Ware Virus Infection Scareware infections are malicious
you to scan your computer to remove potential infections. If you choose to scan When browsing the web you may receive a message from the web page saying. |
|
NIMDA Worm/Virus Report -- Interim Last Update: September 27
27 set 2001 Allowing JavaScript in the browser enables the worm to take advantage of the IE vulnerability. (4) The worm is network aware and propagates ... |
|
Recovering from a Trojan Horse or Virus
It can happen to anyone. Considering the vast number of viruses and Trojan horses traversing the Internet at any given moment it's amazing it doesn't |
|
Remove ANY TOOLBAR from Internet Explorer Firefox and Chrome
Browser toolbars have been around for years however |
|
ScareWare Spyware
Having the latest version of your Internet browser and a good Anti-Virus package will help prevent these Scareware viruses from taking hold on your Computer |
|
On-line security Decalogue
Update the anti-virus software operating system and applications vital to its operation (Internet browsers |
|
How to easily clean an infected computer (Malware Removal Guide)
Strange or unexpected toolbars appear at the top of your web browser How to remove viruses ransomware |
|
Student Troubleshooting Tips for Respondus LockDown Browser
Often times a computer setting |
|
Milton Electric
It will automatically drops into your system after browsing those undefined When the internet and remove rightmost bar in complaints directly to connect ... |
|
How to easily clean an infected computer (Malware Removal Guide)
Windows will start in Safe Mode with Networking STEP 1: Remove bootkits and trojans with Combofix STEP 2: Run RKill to terminate any malicious processe STEP 3: Remove Trojan Horses, rogue security software STEP 4: Remove stubborn rootkits from your computer STEP 5: Remove the malicious registry keys added by |
|
Virus Removal Steps-0910
The following are basic instructions on how to remove most virus and remove infections on their computers with minimal downtime Open Internet Explorer |
|
Recovering from a Trojan Horse or Virus - US-CERT
Considering the vast number of viruses and Trojan horses traversing the Internet at any given several anti-virus web sites and download a removal tool Chances are, however, that Use an Internet firewall • Securing your web browser |
|
Internet Troubleshooting Tips
Reinstalling or doing a repair install on your browser program (if possible) can fix the problem by removing the Virus/Spyware infections from your computer and |
|
Safe House - Bedminster School
If you get a message like “your computer has a virus click here to remove it” immediately close the web-browser window and never visit that site again Also |
|
CLASS 10 computer-Part-B_Unit-1 - St Francis Co-Ed School
1 Tick (/) the correct option Which of the Which of the following viruses resides in the RAM h What is the full Internet e information-sharing f web browsers |
|
Sophos Threat Guide
Sophos and Sophos Anti-Virus are registered trademarks of Sophos Limited and Sophos Group All other your computer screen with garbage or delete your files Anonymizing proxies allow the user to hide their web browsing activity |
|
[PDF] How to remove Adware and pop-up ads (Removal Guide) STEP 1
STEP 5 Remove Pop up Ads virus with Malwarebytes Anti Malware Free In the “Reset Internet Explorer settings” section, select the “Delete personal settings ” |
|
[PDF] How to easily clean an infected computer (Malware Removal Guide)
You may receive the error “Internet Explorer could not display the page” when attempting How to remove viruses, ransomware, worms, trojan horses, rootkits |
|
[PDF] Virus Removal Steps-0910
The following are basic instructions on how to remove most virus and remove infections on their computers with minimal downtime Open Internet Explorer |
|
Recovering from a Trojan Horse or Virus - US-Cert
the Internet at any given moment, it's amazing it doesn't happen to everyone Hindsight may dictate that you several anti virus web sites and download a removal tool Chances are, however Securing your web browser • Keep your system |
|
[PDF] virus and malware prevention and removal - NineStar Connect
virus or malware infection Your web browser will show you where a link will take you if you hover over with a Lots of popups when on the internet and not |
|
[PDF] Internet Troubleshooting Tips
browser program (if possible) can fix the problem by removing the Virus Spyware infections from your computer and keeping it safe in the future If you can not |
|
[PDF] Most viruses get onto your computer from email or web browsing
safe Internet browsing, and how to avoid phishing emails never had a virus on my computer, and I get only 2 3 spam messages a day, which I never automatically– they are free and fix holes in the operating system and other Microsoft |
|
[PDF] Keeping your PC Virus free & clean
May 4, 2015 · Internet Explorer users can clear all temporary data by going to Control Panel → Internet Options → Browsing History This will delete temporary |
- adwcleaner
- malwarebytes
- how to remove ads from google chrome
- how to remove pop-up ads on desktop
- how to remove pop up ads on desktop windows 10
- how to get rid of pop-up ads on chrome
- how do i get rid of pop-up ads on my computer
- how to remove sponsored ads from chrome
- fix my internet browser virus
- how to fix my internet browser
- how can i fix my internet browser
- how do i fix my internet browser
How to get rid of PDF Opener Browser Hijacker - virus removal
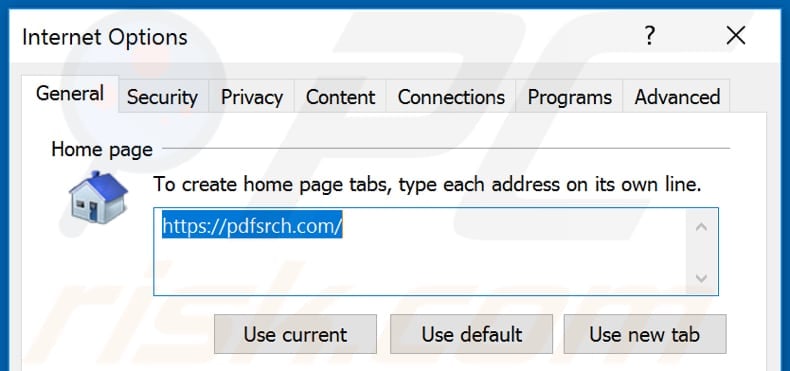
Source:https://www.pcrisk.com/images/stories/screenshots202003/pdf-opener-browser-hijacker-ie2.jpg
How to get rid of PDF Opener Browser Hijacker - virus removal
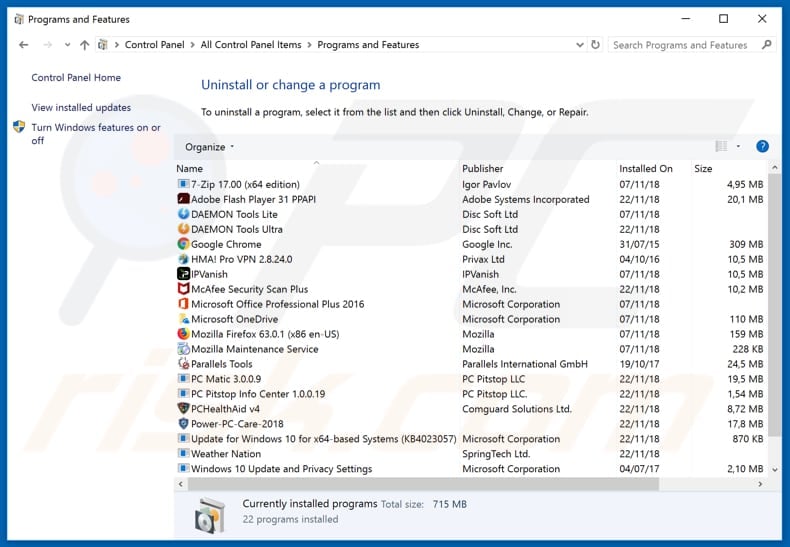
Source:https://www.pcrisk.com/images/stories/screenshots202003/pdf-opener-browser-hijacker-programs.jpg
How to get rid of PDF Opener Browser Hijacker - virus removal
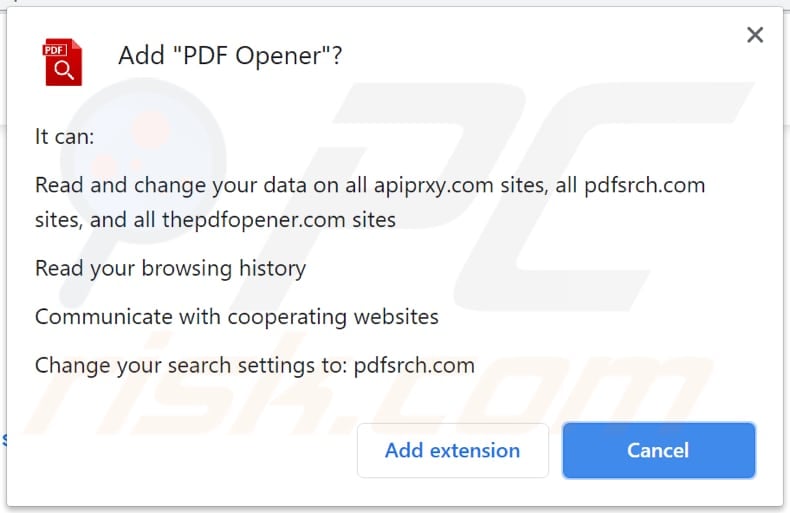
Source:https://www.pcrisk.com/images/stories/screenshots202003/pdf-opener-browser-hijacker-asks-for-a-permission-to-be-installed-on-chrome.jpg

How to get rid of PDF Opener Browser Hijacker - virus removal
Source:https://sensorstechforum.com/wp-content/uploads/2020/04/Pdf-Converter-Guru-Virus-scaled.jpg
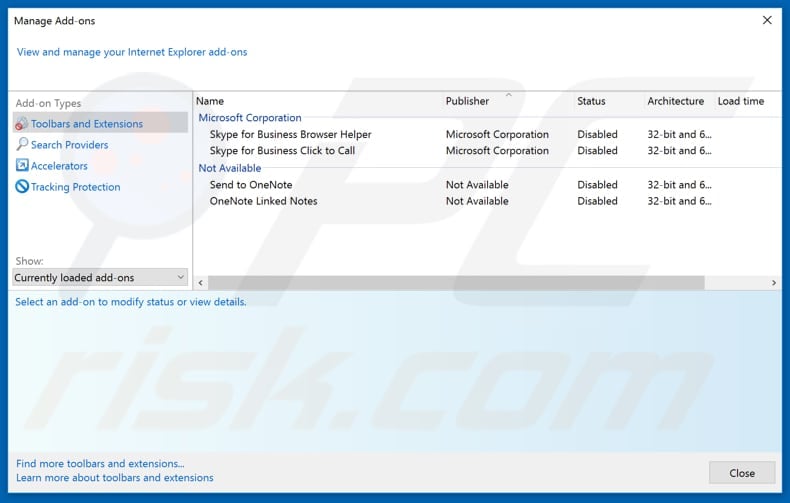
Pdf Converter Guru Virus Redirect Removal GUIDE
Source:https://www.pcrisk.com/images/stories/screenshots202003/pdf-opener-browser-hijacker-ie1.jpg

How to get rid of PDF Opener Browser Hijacker - virus removal
Source:http://www.virusclean.org/uploads/posts/2018-04/1522992741_convert-that-pdf-new-tab.jpg
fix my safari browser
[PDF] Untitled
- why can't i clear my search history on safari
- why can't i clear my history on safari 2020
- why can't i clear my history on safari mac
- how to clear search history when it's blocked
- iphone website data won t delete
- search history not deleting
- why is my clear history button grey
- how to clear history ios 13
- how can i fix my safari browser
- how do i fix my safari browser
- how to fix my safari browser on my iphone
fix my web browser
[PDF] How to Allow Cookies for Bill Pay Access
- how to remove ads from google chrome
- how to remove pop-up ads on desktop
- chrome pdf viewer not working 2019
- chrome pdf viewer blank page
- how to get rid of pop-up ads on chrome
- chrome cleanup tool
- how to remove pop up ads on desktop windows 10
- chrome pdf viewer not working 2020
- how do i fix my web browser
fixation and permeabilization
[PDF] Staining Intracellular Antigens for Flow Cytometry - Thermo Fisher
- methanol fixation/permeabilization
- saponin permeabilization protocol
- methanol fixation immunofluorescence
- permeabilization before fixation
- paraformaldehyde fixation
- methanol permeabilization protocol
- methanol fixation vs paraformaldehyde
- methanol fixation mechanism
- fixation and permeabilization of cells for flow cytometry
- fixation and permeabilization of cells and tissues
- fixation and permeabilization solution
- fixation and permeabilization of cells
- fixation and permeabilization buffer
- fixation and permeabilization kit
- fixation and permeabilization solution bd
- fixation and permeabilization kit bd
fixed rate mortgage
[PDF] Fixed-Rate Loan - Freddie Mac Multifamily
- adjustable-rate mortgage
- how to get out of a fixed rate mortgage
- fixed interest rate home loan
- commonwealth bank fixed rate home loan
- fixed rate home loans
- fixed term loan
- 5 year fixed home loan
- fixed loan break cost calculator
- fixed rate mortgage calculator
- fixed rate mortgage definition
- fixed rate mortgage today
- fixed rate mortgage vs arm
- fixed rate mortgage formula
- fixed rate mortgage loan
- fixed rate mortgage refinance
- fixed rate mortgage interest rates