|
Advanced SQL Injection
I HACK • I CURSE • I DRINK (Rum Coke) How I Throw Down Page 4 Identify – How to find SQLI Attack Methodology – The process and syntax I use |
What are 5 types of SQL injection?
5 Common types of SQL Injection attacks
In-band SQL Injection.
An attacker uses this technique to compromise a web application by inserting malicious SQL code into any available input fields. Error-based SQL Injection. UNION-based SQL Injection. Blind (inferential) SQL Injection. Out-of-band SQL Injection.Yes, using an SQL injection on someone else's website is considered illegal.
SQL injections are a type of computer attack in which malicious code is inserted into a database in order to gain access to sensitive information.
What is advanced SQL injection?
SQL Injection can be broken up into 3 classes.
Inband - data is extracted using the same channel that is used to inject the SQL code.
This is the most straightforward kind of attack, in which the retrieved data is presented. directly in the application web page.
Does SQL injection still work 2023?
SQL injection (or SQLi) is when a user tries to insert malicious SQL statements into a web application.
If they're successful, they'll be able to access sensitive data in the database.
In 2023, SQL injections remain some of the most common attacks on the web.
|
Advanced SQL Injection
14 Mar 2009 We'll spend a little bit of time on MySQL and not too much time on Oracle as its injection syntax is fairly similar to MS-SQL. But primarily ... |
|
DEF CON 24 Hacking Conference
Advanced Blind SQL Injection. David Caissy pentestmonkey.net/cheat-sheet/sql-injection/oracle-sql-injection-cheat-sheet. |
|
Advanced SQL Injection
Most example and tutorials are only for MySQL and SQL Server. Detailed explanations for SQL Injection in web apps with Oracle databases are rare and often buggy |
|
Advanced SQL Injection.pdf
14 Mar 2009 Data is extracted using the same channel that is used to inject the SQL code. This is the most straightforward kind of attack in which the ... |
|
Advanced SQL injection by Joseph Giron
check out http://pentestmonkey.net/blog/db2-sql-injection-cheat-sheet/. Version detection is vital to SQL injection. Hacking is half information gathering. |
|
Webapp security: SQL injection
SQL queries are built using (unsanitized) data provided by the users F. Mavituna SQL Injection Cheat Sheet. • B. Damele and A. Guimaraes |
|
OWASP Top 10 - 2017
And finally we'd like to thank in advance all the translators out there who will translate this release of OWASP Cheat Sheet: SQL Injection Prevention. |
|
Advanced Threat Modelling Knowledge Session
Use Attack Trees (CI4AM). ? Think like an Attacker (STRIDE/DREAD OCTAVE etc). > Create the threat list. ? SQL Injection. ? XSS. ? Replay Attacks. |
|
A Classification of SQL Injection Attacks and Countermeasures
SQL injection attacks pose a serious security threat to Web appli- cations: they allow attackers to obtain unrestricted access to the databases underlying the |
|
OWASP Cheat Sheets
27 Sept 2009 20 SQL Injection Prevention Cheat Sheet ... NET Framework is the set of APIs that support an advanced type system data |
|
Advanced SQL Injection
14 mar 2009 · I submitted a talk entitled “SQL Injection for Mere Mortals” and it didn't get http:// pentestmonkey net/blog/mysql-sql-injection-cheat-sheet/ |
|
Advanced SQL Injection
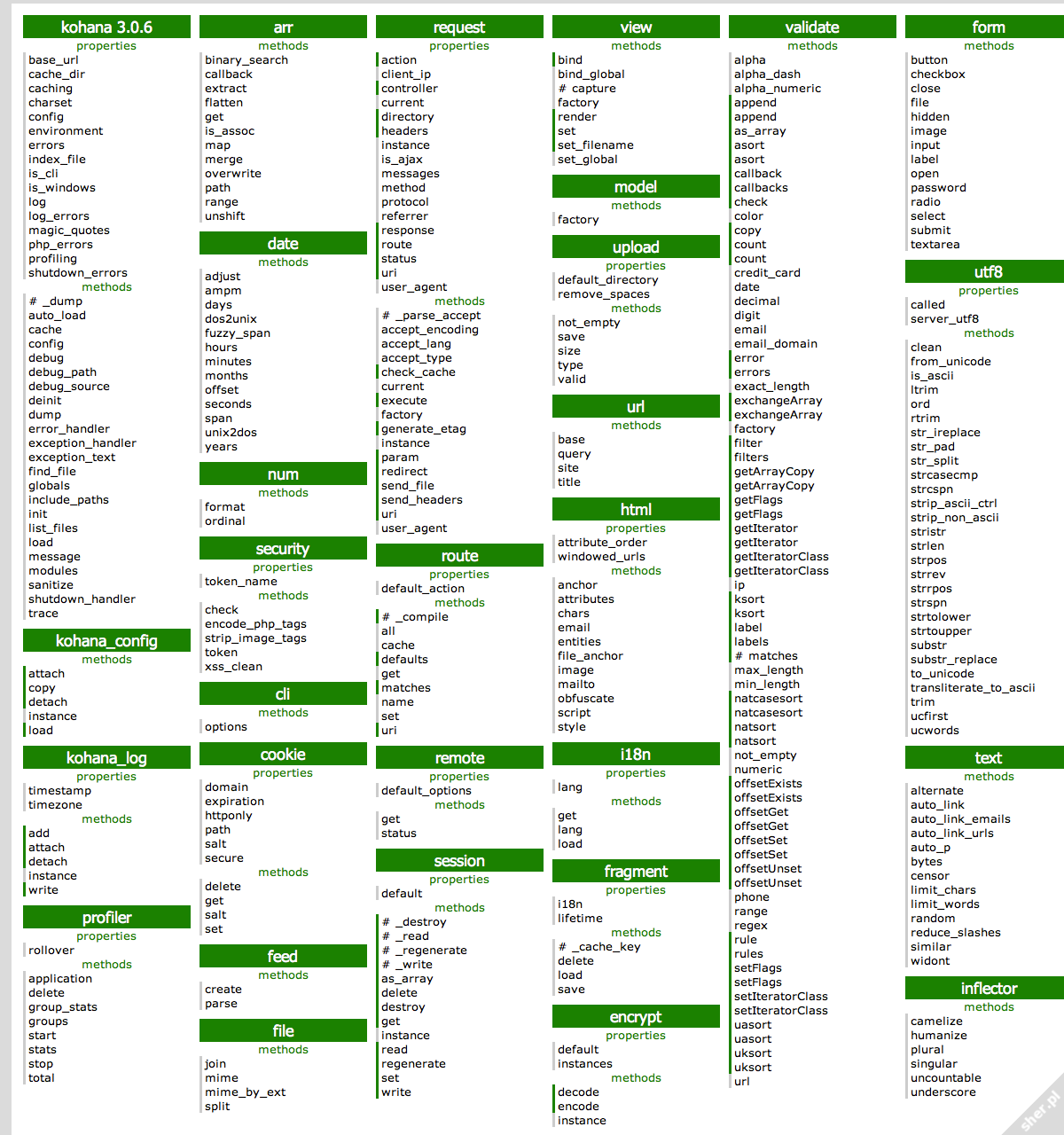
Detailed explanations for SQL Injection in web apps with Oracle databases 126 Red-Database-Security GmbH MySQL Cheat Sheet MySQL Cheat Sheet |
|
Advanced SQL injection by Joseph Giron - GironSec
check out http://pentestmonkey net/blog/db2-sql-injection-cheat-sheet/ Version Another advanced type of mysql injection is one of my favorites Load_file can |
|
SQL Injection Cheat Sheet 2
Currently only for MySQL and Microsoft SQL Server, some ORACLE and some PostgreSQL Most of samples are not correct for every single situation Most of the |
|
Webapp security: SQL injection
F Mavituna, SQL Injection Cheat Sheet • B Damele and A Guimaraes, Advanced SQL injection to operating system full control Eike Ritter Network Security |
|
SQL Injection Attacks and Defensepdf
Mr Hemler was a senior security engineer at Ernst Young's Advanced a SQL Injection vulnerability on a web application based on Microsoft of handy reference resources, pointers, and cheat sheets intended to help you quickly find |
|
Sql injection cheat sheet filetype pdf - Weebly
Currently SQL Cheat Sheet contains only information for MySQL, Microsoft SQL Server, and some limited information for ORACLE and PostgreSQL SQL servers |
|
IN5290 Ethical Hacking Lecture 7: Web hacking 3, SQL injection
Types of SQL injection exploitations oracle) should be run that is accessible by Etc , see detail: http://pentestmonkey net/cheat-sheet/sql-injection/mysql-sql- |
|
SQL Injection Attacks and Defense - X-Files
TELUS Security Intelligence Analysis practice where he delivers advanced event toolkit that has become a “weapon of choice” when exploiting SQL Injection present a number of handy reference resources, pointers, and cheat sheets |
|
[PDF] Advanced SQL Injection - Index of ES
Mar 14, 2009 · Inband data is extracted using the same channel that is used to inject the SQL code This is the most straightforward kind of attack, in which |
|
[PDF] Advanced SQL Injection
Most common attack This year we can celebrate it's the 10th anniversary of SQL Injection Detailed explanations for SQL Injection in web apps with Oracle |
|
[PDF] Advanced SQL injection by Joseph Giron - GironSec
How does a load file look in our attack? I was getting to that example com news indexphp?newsID=null UNION ALL SELECT |
|
[PDF] Advanced sql injection cheat codes
Read our SQL injection cheat sheet to learn everything you need to know about SQL injection (SQLi) is an application security weakness that allows attackers to |
|
[PDF] Advanced sql injection cheat sheet
The SQL Injection Cheat Sheet is the definitive resource for all the technical details about the different variants EXEC sp configure 'show advanced options' |
|
[PDF] SQL Injection Cheat Sheet 2
About SQL Injection Cheat Sheet Currently only for MySQL and Microsoft SQL Server, some ORACLE and some PostgreSQL Most of samples are not correct |
|
[PDF] Webapp security: SQL injection Today SQL injection SQL injection
SQL queries are built using (unsanitized) data provided by the users F Mavituna, SQL Injection Cheat Sheet • B Damele and A Guimaraes, Advanced SQL |
|
[PDF] SQL Injection Attacks and Defense - X-Files
TELUS Security Intelligence Analysis practice where he delivers advanced event SQL injection, at industry conferences such as BlackHat USA and DefCon present a number of handy reference resources, pointers, and cheat sheets |
|
[PDF] Advanced sql injection with sqlmap - Seesaa Wiki
sqlmap is an attack tool which can be effectively used to perform SQL injection attacks and post exploitation acts It is a versatile tool when it comes to SQL |
|
[PDF] IN5290 Ethical Hacking Lecture 7: Web hacking 3, SQL injection
Types of SQL injection exploitations oracle) should be run that is accessible by Etc, see detail pentestmonkeynet cheat sheet sql injection mysql sql |
- sql injection attack
- sql injection example url
- sql injection types
- advanced sql injection cheat sheet
Injection Site Cheat Sheetpdf
Source: Injection (Medicine)

SQL Injection Cheat Sheet - - PDF Free Download
Source:https://imgv2-2-f.scribdassets.com/img/document/26149950/298x396/bc2f3f340b/1369322917?v\u003d1
SQL Injection Cheat Sheet
Source: Microsoft Sql Server
Memory forensics cheat sheet
Source:http://www.cheat-sheets.org/saved-copy/cs.png
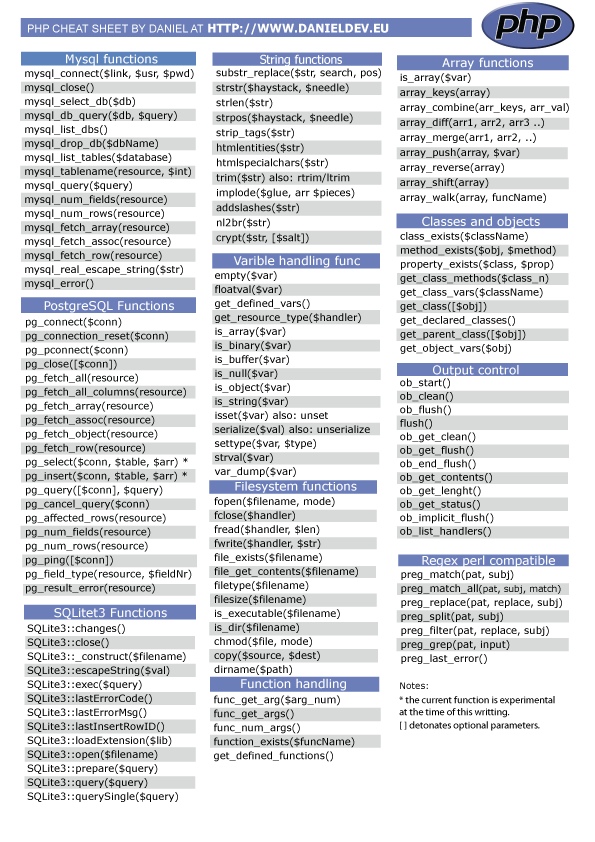
Cheat Sheet : All Cheat Sheets in one page
Source:http://www.cheat-sheets.org/saved-copy/PHP-cheatsheet.Daniel.png

Cheat Sheet : All Cheat Sheets in one page
Source:https://dpsvdv74uwwos.cloudfront.net/statics/img/ogimage/sql-injection-cheat-sheet.jpg
advanced sql join examples
[PDF] Chapter 7 Advanced SQL Objectives
- complex sql join interview questions
- joins in sql
- complex sql queries for practice with answers
- advanced sql server queries examples
- complex joins in oracle
- all sql queries with examples pdf
- what is a complex query
- advanced sql techniques
advanced sql notes pdf
[PDF] Chapter 5 Advanced SQL - Department of Computer Science
- advanced sql tutorial pdf
- advanced sql queries examples with answers pdf
- sql handwritten notes
- advanced sql tutorial with examples
- advanced sql in dbms pdf
- sql server advanced tutorial pdf
- sql pdf
- all sql queries with examples pdf
advanced sql pdf
[PDF] Advanced SQL - nemug
- advanced sql queries examples with answers pdf
- advanced sql tutorial with examples
- advanced sql exercises with answers pdf
- oracle advanced sql pdf
- advanced sql in dbms pdf
- teradata advanced sql pdf
- sql tutorial pdf
- all sql queries with examples pdf
- advanced sql pdf free download
- advanced sql pdf book
- advanced sql tutorial pdf
- advanced sql queries pdf
- advanced pl sql pdf
- advanced sql topics pdf
- advanced sql injection pdf
- advanced sql programming pdf
advanced sql queries
[PDF] Lecture 4: Advanced SQL – Part II - GitHub Pages
- advanced sql queries examples with answers pdf
- complex sql queries for practice with answers
- sql queries for practice with answers pdf
- advanced sql join examples
- sql query example
- all sql queries with examples pdf
- sql server advanced tutorial pdf
- complex sql queries tutorial
- advanced sql queries practice
- advanced sql queries examples
- advanced sql queries interview questions
- advanced sql queries course
- advanced sql queries for data analysis
- advanced sql queries pdf
- advanced sql queries youtube
- advanced sql queries examples with answers pdf