Is a hash-based signature a good choice for cryptography?
The current development toward quantum attack has shocked our confidence on classical digital signature schemes. As one of the mainstreams of post quantum cryptography primitives, hash-based signature has attracted more and more concern in both cryptographic research and application in recent years.
What are the different types of digital signature attacks?
As the digital signature provides authenticity and non-repudiation in order to secure important data, it is very much susceptible to various attacks. 1. Chosen-message Attack 2. Known-message Attack 3. Key-only Attack Let us consider an example where c is the attacker and A is the victim whose message and signature are under attack. 1.
Can digital signatures be hacked?
Moreover, an intensive survey and classification of 117 attacks has been done, supporting the correctness and exhaustiveness of our taxonomy. The results obtained from the survey suggest that there is an array of methods an attacker can employ to subvert the security of digital signatures.
Is a digital signature vulnerable to a man-in-the-middle attack?
The private key used in the digital signature is confidential; if attackers find it by using various techniques, then this can result in an attack. This paper presents a brief introduction about the digital signature and how it is vulnerable to a man-in-the-middle attack.

Attacks on Digital Signature Digital Signature attack

Digital signature

2
|
Lattice Attacks on Digital Signature Schemes
3 août 1999 digital signatures lattices. We describe a lattice attack on the Digital Signature. Algorithm (DSA) when used to sign many messages |
|
Practical Attacks on Digital Signatures Using MD5 Message Digest
2 déc. 2004 Practical Attacks on Digital Signatures Using MD5 ... Homepage of this project: http://cryptography.hyperlink.cz/2004/collisions.htm. |
|
Practical attacks against the Walnut digital signature scheme
Keywords: WalnutDSA NIST PQC |
|
A Digital Signature Scheme Secure Against Adaptive Chosen
Keywords: Cryptography digital signatures |
|
A taxonomy and survey of attacks on digital signatures
A digital signature (Rivest et al. 1978) based on public key cryptography (Diffie and Hellman |
|
Implementation Attacks with Countermeasures on the FALCON
Lattice-based cryptography fault attacks |
|
Differential Attacks on Deterministic Signatures
Keywords: Public-key algorithms; Elliptic curve cryptography; Digital signatures; Implementation attacks and defenses; Hardware security. 1 Introduction. |
|
AN ATTACK ON THE WALNUT DIGITAL SIGNATURE ALGORITHM
30 avr. 2018 WalnutDSA group-based cryptography |
|
Lattice Attacks against Elliptic-Curve Signatures with Blinded Scalar
Elliptic curve cryptography is today the prevailing approach to get efficient public-key cryptosystems and digital signatures. Most of elliptic curve signature |
|
Practical attacks against the Walnut digital signature scheme
Keywords: WalnutDSA NIST PQC |
|
A Digital Signature Scheme Secure Against Adaptive Chosen
attacks might aid an enemy in "breaking" the scheme authentication, are used in the present paper a signature for any given message without obtaining the secret trap-door information |
|
Digital Signatures
A digital signature is a number dependent on some secret known only Alice selects a private key which defines a signing algorithm SA which is a one-to-one mapping KEY-ONLY ATTACKS – adversary knows only the signer's public key |
|
Digital Signatures
A digital signature is a number dependent on some secret known A digital signature must be verifiable, i e , if a Alice selects a private key which defines a signing algorithm S A KEY-ONLY ATTACKS – adversary knows only the signer's |
|
Digital Signatures - Introduction to Cryptography CS 355
Digital Signature: a data string which associates a a signing algorithm: takes a message and a (private) signing key Attack Models for Digital Signatures |
|
Attacking Deterministic Signature Schemes using Fault Attacks
14 oct 2017 · The Elliptic Curve Digital Signature Algorithm (ECDSA) is a variant of DSA using elliptic curve cryptography Both depend on a crypto- |
|
Role of Digital Signature in Network Security and Cryptography
The common attacks on digital signature was reviewed The first method was the RSA signature scheme, Fiat-Shamir signature schemes, DSA and related |
|
Digital Signature Trust Vulnerability:
it using the RSA algorithm with the user's private key, thus obtaining A new Attack on Digital Signature,” in Proc of the IEEE International Conference on the |
|
Signature Schemes
We want a similar mechanism for digital documents For all k, there is a signature algorithm sigk in Sand Existential forgery using a known-message attack: |
|
A Digital Signature Scheme Secure Against Adaptive Chosen
signatures are compact Keywords: Cryptography, digital signatures, factoring, chosen-message attacks, authentication, trap- door permutations, randomization |
|
[PDF] Digital Signatures
When a hash function h is used in a digital signature scheme (as is often the case), h should be a fixed part of the signature process so that an adversary is unable to take a valid signature, replace h with a weak hash function, and then mount a selective forgery attack |
|
[PDF] Digital Signatures
Elements of applied cryptography A digital signature is a number dependent on some secret KEY ONLY ATTACKS – adversary knows only the signer's |
|
[PDF] Modern Cryptography: Lecture 13 Digital Signatures - of Daniel
Jan 31, 2019 · DEFINITION 121 A (digital) signature scheme is a triple of PPT Random message attack (RMA) Adversary can obtain signatures for random |
|
[PDF] Cryptography and Network Security Chapter 13
Cryptography and Network digital signature algorithm and standard Digital Signature Model Attacks and Forgeries • attacks – (public) key only attack |
|
[PDF] Practical attacks against the Walnut digital signature scheme
Keywords WalnutDSA, NIST PQC, post quantum digital signatures, cryptanalysis , group based cryptography 1 Introduction As more and more progress is |
|
[PDF] A Digital Signature Scheme Secure Against Adaptive - People - MIT
signatures are compact Keywords Cryptography, digital signatures, factoring, chosen message attacks, authentication, trap door permutations, randomization |
|
[PDF] A digital signature scheme secure against adaptive - People - MIT
signatures are compact Keywords, cryptography, digital signatures, factoring, chosen message attacks, authentication, trap door permutations, randomization |
- key-only attack in digital signature
- digital signature in cryptography example
- digital signature algorithm
- digital signature authentication protocol
- elgamal digital signature problem
- direct digital signature in cryptography
- digital signature in cryptography and network security pdf
- authentication of digital signature
- attacks on digital signature in cryptography
- attacks on digital signature
- attacks on digital signature pdf
- attacks on digital signature scheme
- lattice attacks on digital signature schemes
- attacks on rsa digital signature
- possible attacks on digital signature
- forgery attacks on digital signature schemes
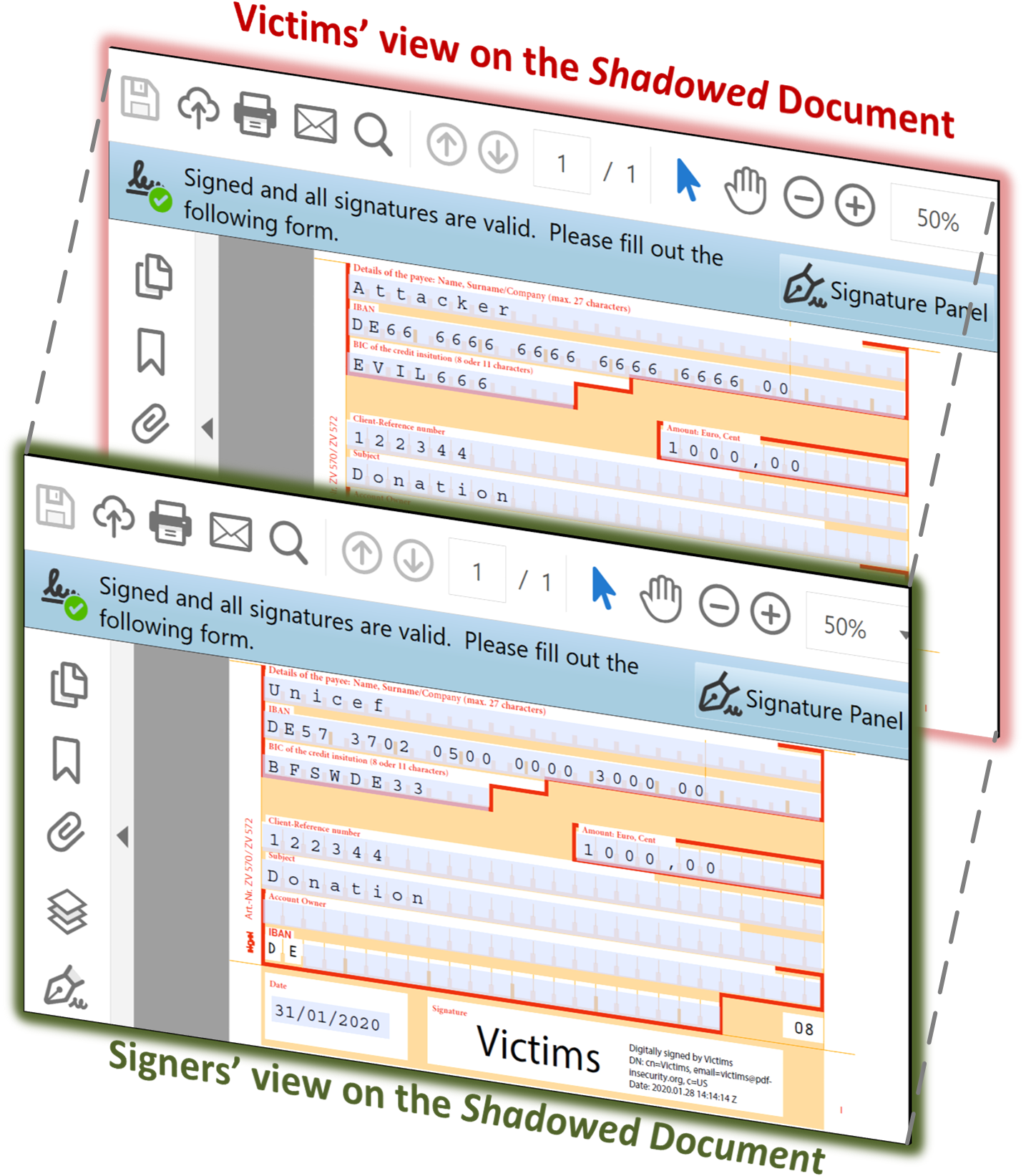
Recently identified PDF digital signature vulnerabilities – PDF
Source:https://pdf-insecurity.org/images/pdf-shadow/shadow-forms.png

PDF Insecurity Website
Source:https://i1.rgstatic.net/publication/225240686_Lattice_Attacks_on_Digital_Signature_Schemes/links/00b7d537c8f3c36a53000000/largepreview.png
PDF) Lattice Attacks on Digital Signature Schemes
Source:https://www.thesslstore.com/blog/wp-content/uploads/2019/08/Digital-Signature-Feature.png

Digital Signatures - Hashed Out by The SSL Store™
Source:https://media.kasperskydaily.com/wp-content/uploads/sites/92/2020/01/14053801/36C3-PDF-digital-signature-2.png
Cracking a PDF digital signature
Source: Kaspersky official blog

Digital Signatures and Certificates - GeeksforGeeks
Source:https://upload.wikimedia.org/wikipedia/commons/thumb/7/78/Private_key_signing.svg/1200px-Private_key_signing.svg.png
attend anywhere
[PDF] Using Video Consultations in Primary Care: A Toolkit for Clinicians
- attend anywhere video
- attend anywhere pricing
- attend anywhere screen share
- attend anywhere resource centre
- attend anywhere virtual clinics
- attend anywhere training
- attend anywhere aws
- attend anywhere logo
- attend anywhere login
- attend anywhere hse
- attend anywhere nhs england login
- attend anywhere nhs wales
- attend anywhere video
- attend anywhere app
- attend anywhere nhs scotland
- attend anywhere nhs lanarkshire
attend anywhere group calls
[PDF] Video Consultation SOP - Document Control
- attend anywhere resource centre
- attend anywhere virtual clinics
- attend anywhere video
- attend anywhere pricing
- attend anywhere training
- anywhere video call
- attend anywhere logo
- attend anywhere screen share
attend anywhere pty ltd
[PDF] EMIS Group plc annual report and accounts 2016
attend anywhere video
[PDF] Troubleshooting Attend Anywhere video calls
- attend anywhere video consultations
- anywhere video call
- download attend anywhere
- attend anywhere training
- attend anywhere patient leaflet
- can you record on attend anywhere
- attend anywhere resource centre
- attend anywhere screen share
- attend anywhere video consultations
- attend anywhere video conferencing
- attend anywhere video platform
- attend anywhere video conference
- attend anywhere video link
- attend anywhere video appointments
- attend anywhere video calls