|
Black Hat Python: Python Programming for Hackers and Pentesters
Justin Seitz is a senior security researcher for Immunity Inc where he spends his time bug hunting reverse engineering writing exploits and coding Python |
|
Gray Hat Hacking The Ethical Hackers Handbook
6 déc 2007 · This is one book that should be in every security professional's library—the coverage is that good ” —Simple Nomad Hacker “The Third Edition |
Is black hat Python a good book?
White hat hackers probe cybersecurity weaknesses to help organizations develop stronger security; black hat hackers are motivated by malicious intent; and Gray hat hackers operate in the nebulous area in between — they're not malicious, but they're not always ethical either.
What black hat hackers use?
Definitely a recommended read for the technical security professional with some basic previous exposure to Python.
What's the best hacking book?
Black hat hacking makes use of ransomware, malware, and other tactics to break through a system's defenses.
The black hat hackers can then access, steal, and leverage the data found.
Some of their techniques involve social engineering, botnets, DDoS attacks, spyware, and more.
|
Rocking the pocket book: Hacking chemical plants for competition
pdf. [34] Jason Larsen. “Miniaturization”. In: Black Hat USA (2014). http://http://blackhat. |
|
Google Hacking for Penetration Testers
I hate pimpin' but we're covering many techniques covered in the “Google Hacking” book. • For much more detail |
|
Marina Krotofil
Marina Krotofil. Black Hat Las Vegas |
|
Hacking Mifare Classic Cards
21 oct. 2014 hack Mifare Classic cards are developed what completely jeopardized the card reputation. ... Mifare.pdf ... Curtouis Dark-Side Attack. |
|
Becoming a Black Hat Hacker
This book is one of my favorites. It combines the knowledge of computer architecture and programming and introduces you to the world of computer security. This |
|
Hacking Intranet Websites from the Outside: JavaScript Malware
8 mars 2006 Hacking Intranet Websites from the Outside. Black Hat (USA) - Las Vegas ... Hacking the Intranet special thanks to: ... WHXSSThreats.pdf. |
|
How to Hack a Turned-Off Computer or Running Unsigned Code in
[ASM17] Dmitriy Evdokimov Alexander Ermolov |
|
Hacking a Professional Drone
The goal of this talk is to give insights into the security of. Unmanned Aerial Vehicles (UAVs) and to show that professional. |
|
Gray Hat Hacking 2-nd Edition.pdf
Founder and Director of Black Hat. “The second edition of Gray Hat Hacking moves well beyond current 'intro to hacking' books and presents a well |
|
JavaScript malware just got a lot more dangerous
Hacking Intranet Websites from the Outside. Black Hat (Japan). 10.05.2006. "JavaScript malware just got a lot more dangerous" WHXSSThreats.pdf. |
|
Gray Hat Hacking, 2-nd Editionpdf - X-Files
Founder and Director of Black Hat “The second edition of Gray Hat Hacking moves well beyond current 'intro to hacking' books and presents a well thought- out |
|
The Hackers Underground Handbook
The word “Hack” or “Hacking” in this eBook should be regarded as Imagine a black hat discovers a vulnerability and codes an exploit for it that no one else |
|
Hacking
Ethical issues between a white hat and a black hat hacker This book has not Was this book written to teach today's hackers how to cause damage in more effective ways? Answer: No pages/frontline/shows/hackers/risks/csi-fbi2000 pdf |
|
Black Hat Hackers Handbooks
10 jan 2021 · hat hacker home facebook, black hat hacking tutorials pdf free download wordpress com, the hackers underground handbook hacking tricks, hacking |
|
Blackhat Hacking - BlARROW
Blackhat Hacking How to hack and not get caught Brady Bloxham Silent Break Security TTPs ▫ Data exfiltration techniques – Archive files (usually rar) |
|
Becoming a Black Hat Hacker - DocDroid
Since the person is becoming a Blackhat Hacker, there is absolutely no reason to follow There are almost no penalties when it comes to downloading ebooks |
|
Gray Hat Hacking - Caribbean Environment Programme - UNEP
[Books] Gray Hat Hacking: The Ethical Hacker's Handbook Thank you Black Hat Python-Justin Seitz 2014-12-14 In Black Hat Python, the latest from Justin product description or the product text may not be available in the ebook version |
|
Preview Ethical Hacking Tutorial (PDF Version) - Tutorialspoint
Hacking and make a career as an ethical hacker All the content and graphics published in this e-book are the property of Tutorials Point Black Hat Hackers |
|
211 free ethical hacking books now - Squarespace
20 avr 2020 · Best Ethical Hacking pdf Books for free download 2020 1(Black Belt Hat Hacking Complete Guide to XSS Attacks 5(Cross Site Scripting and |
|
Gray Hat Hacking - Computer Sciences User Pages
6 déc 2007 · “Gray Hat Hacking is an excellent 'Hack-by-example' book The material in this eBook also appears in the print version of this title: talented team includes Black Hat Instructors, received a 2010 Department of Defense CIO |
|
[PDF] The Hackers Underground Handbook - Index of ES
The word “Hack” or “Hacking” in this eBook should be regarded as Imagine a black hat discovers a vulnerability and codes an exploit for it that no one else |
|
[PDF] Gray Hat Hacking, 2-nd Editionpdf - X-Files
Founder and Director of Black Hat “The second edition of Gray Hat Hacking moves well beyond current 'intro to hacking' books and presents a well thought out |
|
[PDF] Blackhat Hacking - ISSA-Utahorg
Blackhat Hacking How to hack and not get caught Brady Bloxham Silent Break Security TTPs ▫ Data exfiltration techniques – Archive files (usually rar) |
|
[PDF] Preview Ethical Hacking Tutorial (PDF Version) - Tutorialspoint
Hacking and make a career as an ethical hacker All the content and graphics published in this e book are the property of Tutorials Point Black Hat Hackers |
|
[PDF] Becoming a Black Hat Hacker - DocDroid
Since the person is becoming a Blackhat Hacker, there is absolutely no reason to follow There are almost no penalties when it comes to downloading ebooks |
|
[PDF] Gray Hat Hacking - UW Computer Sciences User Pages
Dec 6, 2007 · “Gray Hat Hacking is an excellent 'Hack by example' book McGraw Hill eBooks are available at special quantity discounts to use talented team includes Black Hat Instructors, received a 2010 Department of Defense CIO |
|
[PDF] atellite Hacking for Fun & Pr0fit - Black Hat
$atellite Hacking for Fun Pr0fit Adam Laurie Hacking a Bird in The Sky ○ Old Skewl – Started doing Poking in the dark Analyse config files – Tools to |
|
[PDF] Hacking - TechTarget
Ethical issues between a white hat and a black hat hacker This book has not Was this book written to teach today's hackers how to cause damage in more effective ways? Answer No pages frontline shows hackers risks csi fbi2000 pdf |
|
[PDF] Hacking for Dummies - Zenk - Security
addition, he is technical editor of the book Network Security For Dummies by the good guys wore white cowboy hats and the bad guys wore black cowboy hats Ethical hacking — also known as penetration testing or white hat hacking — Regular HTML and PDF files are probably okay, because they're most likely |
- Ethical hacking coding booksBlack Hat Python: Py...
- Gray Hat Hacking: T...
- Hacking: The Art of...
- Rtfm: Red Team Fiel...
- More results
- Ethical hacking coding books
- White hat hacking PDF
- Hackers Black Book pdf free download
- Grey Hat Hacking book pdf
- Black hat hacking books
- Gray Hat Hacking 5th Edition PDF
- Ethical hacking PDF
- Black Hat Python pdf
- Introduction to ethical hacking PDF
- black hat hacking pdf download
- black hat hacking pdf
- black hat hacking course pdf
- black hat hacking books pdf free download
- learn black hat hacking pdf
- black hat hacking tutorials pdf
- black hat hacking tutorials pdf free download
- black hat hacking tricks pdf
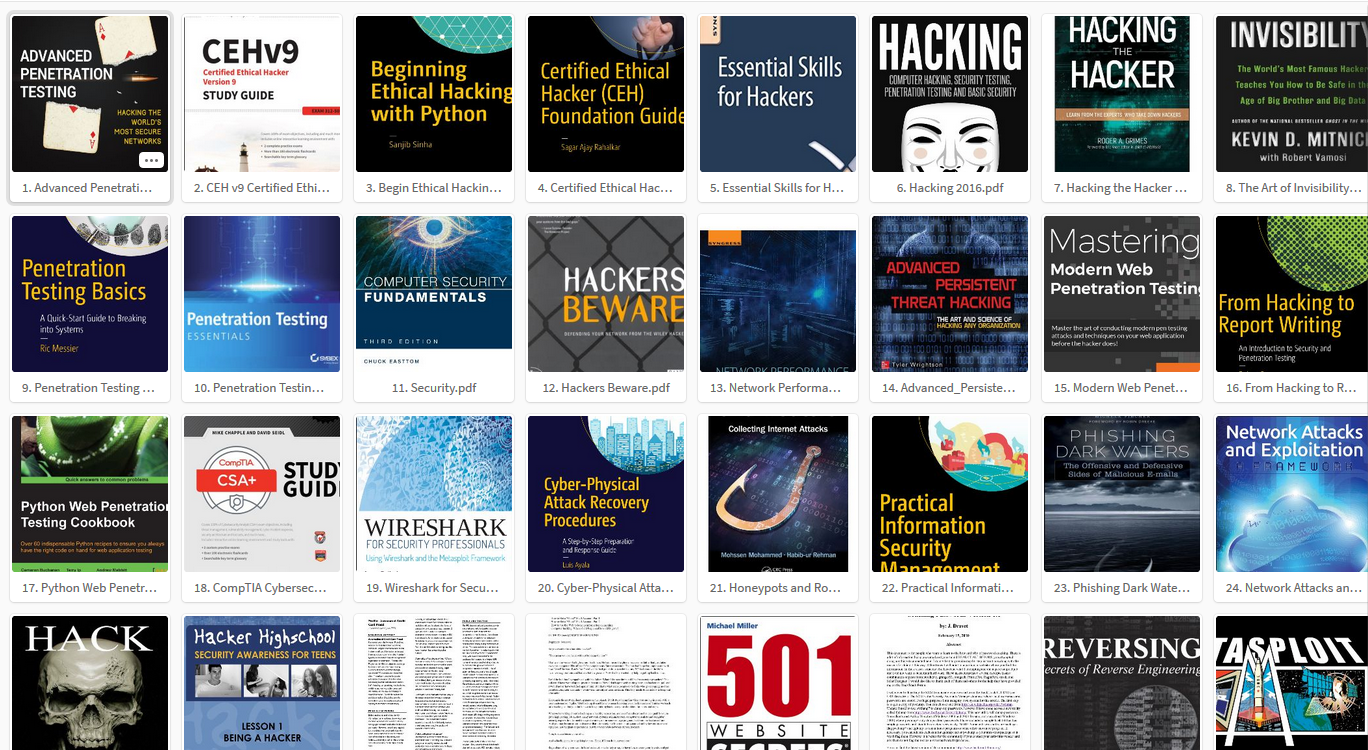
90+ Best Hacking eBooks Free Download in PDF (2021 List)
Source:https://hackingvision.com/wp-content/uploads/2018/03/ebooks.png

Top 100 Free Hacking Books PDF Collection - HackingVision
Source:https://techwafer.com/wp-content/uploads/2018/11/Hacking-Book-PDF.jpg

40+ Best Hacking Books and Courses Free Download PDF – TechWafer
Source:https://image.slidesharecdn.com/theblackbookethicalhackingreferencebook-191015051755/95/pdf-the-black-book-ethical-hacking-reference-book-fullpages-1-638.jpg?cb\u003d1571116711

Source:https://shasihacksec.files.wordpress.com/2016/07/best-hacking-books.jpg

Best Hacking Books PDF 2016 \u0026 Hacking Tutorials – Shasi Hacksec
Source:https://icssindia.in/wp-content/uploads/2020/01/free-hacking-books.jpg

20 Best Free Hacking Books For 2020 – Beginners to Advanced Level
Source:https://i0.wp.com/1.bp.blogspot.com/-NsWbytukKYg/XgSjBpmYu3I/AAAAAAAAGtc/R4rbuDfJOooL2SaVAOKOhF_SEdN6KOMgACLcBGAsYHQ/s1600/Hacking%2BBooks.png?ssl\u003d1
black hat hacking tools
[PDF] IN5290 Ethical Hacking Lecture 1: Introduction to Ethical - UiO
- Black hat Hacking PDF
- Black hat Hacking course
- Black Hat Python pdf
- Gray Hat Hacking Fifth Edition PDF
- [PDF] THE HACKING BIBLE: The Dark secrets of the hacking world: How ...index-of.es › Varios-2 › The Dark Secrets of The Hacking World The...
- Hacking can be dangerous for the Black Hat hackers and it can bring them the death
- in the ... software
- pirated music
- pornography
- hacking tools etc. They can ...[PDF] Becoming a Black Hat Hacker - DocDroidhttps://www.docdroid.net › file › download › article
- When hacking
- I will use any tool that gets the job done. It is usually better to craft your own tools. Creating your programs has the advantage of doing exactly what ...[PDF] Ethical Hacking - Tutorialspointhttps://www.tutorialspoint.com › ethical_hacking_tutorial
- Hacking and make a career as an ethical hacker. Prerequisites. Before proceeding with this tutorial
- ... Black Hat Hackers . ... ETHICAL HACKING − TOOLS .3 case-study 2 – the hacker community - jstorhttps://www.jstor.org › stable › resrep12574
- Black hat hacking occurs in varying degrees of severity: whereas ... availability of cybercrime-related tools and services enable a much higher sophistication.[PDF] IN5290 Ethical Hacking Lecture 1: Introduction to Ethical ... - UiOhttps://www.uio.no › studier › emner › matnat › ifi › in5290_2019_l0...
- available software tools to attack. • Protest hackers (Protest against something e.g. anonymous). • Grey hat hackers: Usually white hat
- but can be black hat.Related searchesHow hackers h...
- Hacking virus
- Hacking animation
- Hacker room
- More results
- Black hat hacking books
- Hackers Black Book pdf free download
- Gray Hat Hacking PDF
- Gray Hat Hacking 1st edition pdf
- Index of Black Hat hacking tutorials
- Gray Hat Hacking 5th Edition GitHub
- Gray Hat Hacking 6th Edition
- Gray Hat Hacking 3rd Edition
- black hat hacking tools github
- black hat hacking tools download
- best black hat hacking tools
- black hat hacking training and tools
black hat hacking tricks pdf
[PDF] WHY HACKERS HACK
- Black hat Hacking PDF
- White hat hacking PDF
- Hackers Black Book pdf free download
- Ethical hacking PDF
- [PDF] OS Command Injection - Black Hathttps://www.blackhat.com › presentations › bh-dc-10 › Bannedit › Bla...
- A malevolent hacker (also known as a cracker) can exploit that vulnerability to gain unauthorized. ) p y g access to data or network resources. When users visit an ...[PDF] Hacking With Expertsdocshare01.docshare.tips › files
- Hacking
- Programming
- editing
- cracking
- web designing and writing books. He Wants To ... Free Download SMS Bomber For Android Phones. How To Know ... 5 Rarely known Google I'm Feeling Tricks. How To ... Hats. Black Hat– These are considered the bad guys. Black hat hackers usually use their skills maliciously ...[PDF] Computer Hacking - Joe Benton.pdf - Index-of.co.ukindex-of.co.uk › Hacking › Computer Hacking - Joe Benton
- This book contains helpful information about computer hacking
- and the skills required to ... before the bad guys (aka the black hat hackers) use them against you. ... Some tricks include creating a denial of service by flooding the network with a.[PDF] Gray Hat Hacking
- 2-nd Edition.pdf - X-Fileshttps://doc.lagout.org › network › 2_Hack › Gray Hat Hacking
- 2-nd ...
- even the novice
- Gray Hat Hacking
- Second Edition is a fantastic book for anyone ... Ethical issues among white hat
- black hat
- and gray hat hackers ... tools in your bag of tricks to fight the bad guys—technology
- knowledge of how to use.[PDF] Hacking for Dummies - Zenk - Securityhttps://repo.zenk-security.com › EN-Hacking for Dummies
- tricks and techniques — in plain English — to assess the security of your own ... the good guys wore white cowboy hats and the bad guys wore black cowboy hats . ... Ethical hacking — also known as penetration testing or white-hat hacking — ... always will try to take down your computer systems through manual hacking.[PDF] Gray Hat Hacking - UW Computer Sciences User Pagespages.cs.wisc.edu › ~ace › media › gray-hat-hacking
- Dec 6
- 2007 · help with Chapter 16 (and for providing the free PDF analysis tools at http://blog ... malicious hacker or “black hat” will place hidden text within a page. ... tools in your bag of tricks to fight the bad guys—technology
- knowledge.[PDF] WHY HACKERS HACKhttps://i.crn.com › ckfinderimages › userfiles › images › crn › custom
- categories: black hat
- white hat
- and grey hat. Their methods and motives vary
- from financial gain to disruption
- and some even hack for the fun of it. Learn why it matters for ... Who They Breach: The Tricks of the Trade. Along the same lines as ...Related searchesEthical hacking booksBlack Hat Python: Py...
- ABCD of Hacking: T...
- Hacking for Dummies
- Ethical Hacking...
- More results
- Ethical hacking books
- Hacking coding booksIntroduction to ethical hacking PDF
- Network Hacking pdf
- Hacking tricks PDF free download
- Hacking codes PDF
- Hackers bible PDF
- Index of Black Hat hacking tutorials
- Ethical hacking and cyber security PDF
- The real Hackers Handbook pdf
- black hat hacking tricks pdf
- black hat hacking tricks
- black hat hacker tricks
- black hat hacking tips and tricks
black hat hacking tutorials pdf
[PDF] Hacking for Dummies - Zenk - Security
- Phone hacking booksAn Ethical Guide to H...
- ABCD of Hacking: T...
- Android Hacker's...
- 50 Android Hacks
- More results
- Phone hacking books
- Ethical hacking coding booksHackers Black Book pdf free download
- White hat hacking PDF
- [PDF] atellite Hacking for Fun & Pr0fit! - Black Hathttps://www.blackhat.com › presentations › bh-dc-09 › Laurie › Black...
- Started doing this in late 90's. – So
- err... why did it take so long to publish? Page 4. Feed Hunting. ○ Look for 'interesting' satellite feeds. – Scan all satellites.[PDF] Gray Hat Hacking
- 2-nd Edition.pdf - X-Fileshttps://doc.lagout.org › network › 2_Hack › Gray Hat Hacking
- 2-nd ...
- tations of a gray hat hacker. This section: • Clears up the confusion about white
- black
- and gray hat definitions and characteristics. • Reviews the slippery ethical ...[PDF] The Basics of Hacking and Penetration.pdfhttps://lira.epac.to › DOCS-TECH › The Basics of Hacking and Penetr...
- “black hat” to describe the Jedis and siths. throughout this book
- the terms. “white hat
- ” “ethical hacker
- ” or “penetration tester” will be used interchange-.[PDF] Computer Hacking - Joe Benton.pdf - Index-of.co.ukindex-of.co.uk › Hacking › Computer Hacking - Joe Benton
- How one uses those skills will clearly define whether one is a white hat or a black hat hacker. The skills and tools are always neutral; only when they are used for ...[PDF] INF5290 Ethical Hacking Lecture 1 - UiOhttps://www.uio.no › studier › emner › matnat › ifi › lectures › inf529...
- The «attacker» thinks like a real hacker (but not totally) ... Red hat hackers: Stopping black hat hackers by attacking ... Green hat hackers: beginners to hacking.[PDF] Hacking for Dummies - Zenk - Securityhttps://repo.zenk-security.com › EN-Hacking for Dummies
- the good guys wore white cowboy hats and the bad guys wore black cowboy hats .) Whatever the case
- most people give hacker a negative connotation. ... Regular HTML and PDF files are probably okay
- because they're most likely needed for ...Related searchesEthical hacking PDF
- Introduction to ethical hacking PDF
- Black Hat Python pdf
- Black Hat hacking tools
- Ethical hacking and cyber security PDF
- Network Hacking pdf
- Hackers bible PDF
- Black hat hacking book
- black hat hacking tutorials pdf
- black hat hacking tutorials for beginners
- black hat hacking tutorials
- black hat hacker tutorials
- black hat hacker tutorial pdf
- black hat hacking guide
- black hat hacking video tutorials
- index of black hat hacking tutorials
black hat hacking tutorials pdf free download
[PDF] Ethical hacking tutorial point pdf free download - Shopify
- Hackers Black Book pdf free download
- White hat hacking PDF
- Ethical hacking PDF
- Introduction to ethical hacking PDF
- [PDF] atellite Hacking for Fun & Pr0fit! - Black Hathttps://www.blackhat.com › presentations › bh-dc-09 › Laurie › Black...
- Started doing this in late 90's. – So
- err... why did it take so long to publish? Page 4. Feed Hunting. ○ Look for 'interesting' satellite feeds. – Scan all satellites.[PDF] The Basics of Hacking and Penetration.pdfhttps://lira.epac.to › DOCS-TECH › The Basics of Hacking and Penetr...
- Beyond just being written for beginners
- this book actually presents the infor- mation in a ... ation
- an ethical hacker should strive to act and think like a real black hat ... if you choose to download the Vmware image
- you will also need software.[PDF] Computer Hacking - Joe Benton.pdf - Index-of.co.ukindex-of.co.uk › Hacking › Computer Hacking - Joe Benton
- The premise of this book is to help you learn the basics of ethical hacking (the stuff ... before the bad guys (aka the black hat hackers) use them against you. ... they do not always ask a subscriber or customer to download something “free.[PDF] Ethical hacking tutorial point pdf free download - Shopifyhttps://cdn.shopify.com › files › files › ethical_hacking_tutorial_point...
- Ethical hacking tutorial point pdf free download. Continue ... you like to learn how to hack systems like black hat hackers and secure them as security experts?Related searchesHackers bible PDF
- Network Hacking pdf
- Android Hacker's Handbook pdf free download
- Hacker Methodology Handbook PDF download
- Black Hat Python pdf
- Hacking codes PDF
- The real Hackers Handbook pdf
- Ethical hacking and cyber security PDF
- black hat hacking tutorials pdf
- black hat hacking tutorials for beginners
- black hat hacking tutorials
- black hat hacker tutorials
- black hat hacker tutorial pdf
- black hat hacking guide
- black hat hacking video tutorials
- index of black hat hacking tutorials