|
Vulnerabilities in C/C++ programs – Part II
Vulnerabilities in C/C++ programs – Part II TDDC90 – Software Security Ulf A similar class of vulnerabilities are sign errors – mixing signed and unsigned |
|
Secure Coding in C and C++: A Look at Common Vulnerabilities
The basic_string class is less prone to security vulnerabilities than C-style strings C-style strings are still a common data type in C++ programs |
|
C Language Issues
The vulnerabilities resulting from type conversions are often fascinating because they can be subtle and difficult to locate in source code and |
Is C Secure or not?
Since memory safety bugs are often security issues, memory safe languages are more secure than languages that are not memory safe.
Memory safe languages include Rust, Go, C#, Java, Swift, Python, and JavaScript.
Languages that are not memory safe include C, C++, and assembly.What are the security threats in C?
Buffer overflow is a common security vulnerability in C programming.
What Is Buffer Overflow? Buffer overflow occurs when data is written outside the boundary of the allocated memory.What are the vulnerabilities in C?
Most vulnerabilities in C are related to buffer overflows and string manipulation.
In most cases, this would result in a segmentation fault, but specially crafted malicious input values, adapted to the architecture and environment could yield to arbitrary code execution.C does not have any of these protections: C heap values are created in a type-unsafe way.
C casts, unchecked array accesses, and unsafe deallocation can corrupt memory during its lifetime.
C deallocation is unsafe, and can lead to dangling pointers.
|
Secure Coding in C and C++: A Look at Common Vulnerabilities
The basic_string class is less prone to security vulnerabilities than C-style strings. C-style strings are still a common data type in C++ programs. Impossible |
|
String Vulnerabilities
vulnerabilities than C-style strings. ? C-style strings are still a common data type in C++ programs. ? Impossible to avoid having multiple string types |
|
Two complementary approaches to detecting vulnerabilities in C
30 Jan 2014 4.4 Injecting Data into a C Code for Detecting Vulnerabilities . ... l'arithmétique des pointeurs le manque d'un type de base pour les ... |
|
TDDC90 - C/C++ Vulnerabilities II
Heed compiler warnings! ? Understand sizes and conversion rules for data types! ? Use the type 'size_t' for variables representing lengths of things. |
|
Secure Coding in C++: Integers
software vulnerabilities (even when this behavior Type conversions occur explicitly in C++ as the result ... each variable (c1 and c2) to int size. |
|
An Analysis of C/C++ Datasets for Machine Learning-Assisted
Vulnerability detection datasets are quite different from other types of an astounding 34435% more than Wild C. The wchar_t data type is found in. |
|
Exploiting Format String Vulnerabilities
1 Sept 2001 It is a conversion function which is used to represent primitive C data types in a human readable string representation. They are used in ... |
|
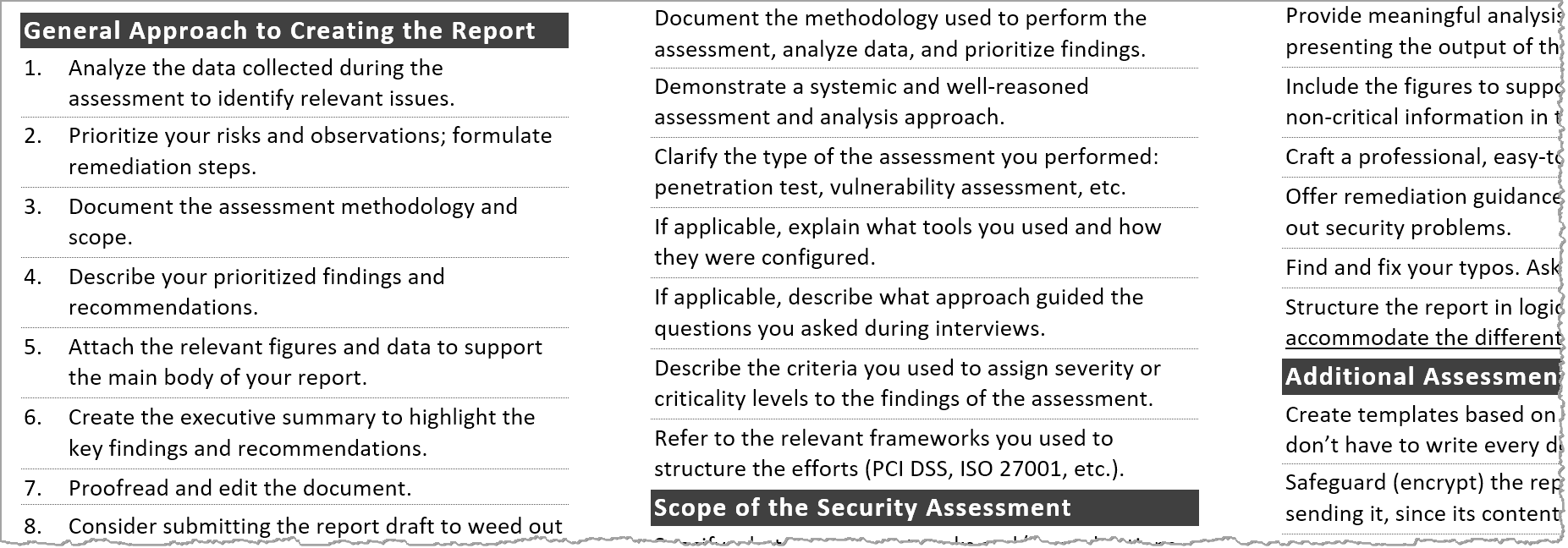
SECURITY POSTURE ASSESSMENT (SPA)
c) Step 3 (security testing and risk analysis) i) conduct vulnerability exploitation and POC; ii) identify the remotely exploitable vulnerability types such |
|
Detecting Vulnerabilities in C Programs Using Trace-Based Testing
proach can handle new types of vulnerabilities by simply formulating new security requirements about the type and size of the declared program variable. |
|
Mitigating Information Leakage Vulnerabilities with Type-based Data
age vulnerabilities (or info leaks) remain a major security threat. Modern systems software is riddled c) TDI: In this paper we present Type-based Data. |
|
TDDC90 - C/C++ Vulnerabilities II - IDALiUse
A similar class of vulnerabilities are sign errors – mixing signed and unsigned data types in an unsafe way 3 // Reads 'size' bytes from file 'f' into buffer 'out' void |
|
String Vulnerabilities - School of Computing and Information
vulnerabilities than C-style strings ○ C-style strings are still a common data type in C++ programs ○ Impossible to avoid having multiple string types in a |
|
Software Vulnerabilities
Software vulnerability enables the attacker to run with privileges of malicious web contents exploit vulnerabilities in When assigning to a different data type |
|
Analysis of Field Data on Web Security Vulnerabilities
critical web application vulnerabilities: SQL Injection and XSS It analyzes the specifies how data types and data structures are managed and constructed by |
|
Pinpointing Vulnerabilities - Computer Science, FSU - Florida State
effectively pinpoint various types of memory vulnerabilities and has low performance sends data outside (e g , send, sendmsg, write), the vulnerability is likely |
|
Memory Corruption Vulnerabilities, Part II - Penn State University
Overflowing Heap Critical User Data ○ Overflow the buffer on the heap so that the function pointer is changed to an arbitrary address /* record type to allocate |
|
Source Code Patterns of Buffer Overflow Vulnerabilities in Firefox
C/C++ does allow the assignment of variables with different data types It will interpret the bits according to the new variable type For example, if a negative value |
|
Format String Vulnerabilities and Exploitation - NCC Group Research
The “ n” specifier, when used, will write the number of characters actually formatted in by printf'ing a format string to a variable To clarify: The “ n” format |
|
[PDF] String Vulnerabilities
vulnerabilities than C style strings ○ C style strings are still a common data type in C++ programs ○ Impossible to avoid having multiple string types in a |
|
[PDF] Code Injection in C and C++ : A Survey of Vulnerabilities and
This report documents possible vulnerabilities in C and C++ ap plications that What follows is a general overview of the types of countermeasures that are allow a program to copy data beyond the end of an array, overwriting adjacent |
|
[PDF] C and C++ vulnerability exploits and countermeasures - SecAppDev
corruption vulnerabilities in C programs 4 Secappdev 2011 Eg bounds checks, type checks, – Correct As a consequence, if a local buffer variable can |
|
[PDF] Secure Coding in C++: Integers
underestimated source of vulnerabilities in Type conversions occur explicitly in C++ as the result Conversions can lead to lost or misinterpreted data |
|
[PDF] TDDC90 - C/C++ Vulnerabilities II - LiU IDA
The value returned by the 'sizeof' operator is always of an unsigned type (size t) ▫ According to the C standard, if two values of different data types are |
|
[PDF] Detecting C Program Vulnerabilities - Semantic Scholar
All these types of vulnerabilities are specified in details in [3] Type overflow occurs in a C code when a variable v is defined as a variable of type t and the value |
|
[PDF] C Language Issues - GitHub Pages
Oct 14, 2006 · of subtle vulnerabilities in software that remain unnoticed and uncorrected for long periods of underlying architecture dependent data type |
|
[PDF] Security vulnerabilities of the top ten programming languages: C
64156 items · create vulnerabilities (Seacord, 2005) Unlike Java, C lacks type safety C has become more prone to errors in recent years because data across the |
- Common vulnerabilities in C
- Code injection example C
- C read function vulnerability
- Strcpy vulnerability
- Detection of security vulnerabilities in C language applicationsonlinelibrary.wiley.com › doi › spy2.8 › pdf
- Dec 19
- 2017 · C language library
- detection
- security
- static analysis
- vulnerability. 1 ... library ( headers files
- constant values
- data types
- function headers and.[PDF] C Language Issues - GitHub Pageshttps://trailofbits.github.io › vulnerabilities › references › Dowd_ch06
- Oct 14
- 2006 · of subtle vulnerabilities in software that remain unnoticed and uncorrected for long periods of ... underlying architecture-dependent data type.[PDF] Security vulnerabilities of the top ten programming languages: C ...https://www.aabri.com › manuscripts
- 64156 items · create vulnerabilities (Seacord
- 2005). Unlike Java
- C lacks type safety. C has become more prone to errors in recent years because data across the ...[PDF] Detecting Vulnerabilities in C Programs Using Trace ... - CiteSeerXciteseerx.ist.psu.edu › viewdoc › download › type=pdf
- is often used in automatic test data generation for find- ing errors that crash a ... proach can handle new types of vulnerabilities by simply formulating new ...Related searchesVulnerable C code examples
- C++ vulnerabilities
- Format string vulnerability
- Buffer overflow exploit
- How to find buffer overflow vulnerabilities
- Buffer overflow explained
- Strcat vulnerability
- Vulnerable C programs
PDF) Security vulnerability categories in major software systems
Source:https://cdn.zeltser.com/wp-content/uploads/2012/01/security-assessment-report-cheat-sheet-preview-large.png

Tips for Creating a Strong Cybersecurity Assessment Report
Source:https://www.guru99.com/images/cassandra/021216_0701_10MostCommo1.jpg

10 Most Common Web Security Vulnerabilities
Source:https://i1.rgstatic.net/publication/261389106_A_survey_on_web_application_vulnerabilities_and_countermeasures/links/581eae3408aeccc08af07bac/largepreview.png

PDF) A survey on web application vulnerabilities and countermeasures
Source:https://mk0resourcesinf5fwsf.kinstacdn.com/wp-content/uploads/1-416.png
![PDF File Format: Basic Structure [updated 2020] - Infosec Resources PDF File Format: Basic Structure [updated 2020] - Infosec Resources](https://ars.els-cdn.com/content/image/3-s2.0-B9780124201149000083-f08-10-9780124201149.jpg)
PDF File Format: Basic Structure [updated 2020] - Infosec Resources
Source:https://ars.els-cdn.com/content/image/3-s2.0-B9780124201149000083-f08-10-9780124201149.jpg
Vulnerability Data - an overview
Source: ScienceDirect Topics
c data types
[PDF] Introduction to Programming (in C++) Data types and visibility
- Data types in C PDF
- Data types in C ppt
- Derived data types in C
- C printf data types
- [PDF] Data Types and Variables - CS50 CDNhttps://cdn.cs50.net › fall › shorts › data_types › data_types
- Data Types and Variables. ○ Unlike a number of modern programming languages
- C requires that you specify the data type of every variable you create
- the first ...[PDF] Summary of C Programming Basic Data Types - UIC CShttps://www.cs.uic.edu › ~jbell › CourseNotes › DataTypesSummary
- Summary of C Programming Basic Data Types. Integral Types - See limits.h for implementation-specific details and certain defined constants. Type aka. Typical.[PDF] Data Typeshttps://www2.southeastern.edu › kyang › Fall › CMPS401 › ClassNotes
- Is it a primitive type or just a special kind of array? 2. Is the length of objects static or dynamic? – C and C++ use char arrays to store char strings and provide a ...[PDF] Introduction to Programming (in C++) Data types and visibilityhttps://www.cs.upc.edu › ~jordicf › Teaching › programming › pdf
- (e.g. integer
- real
- character
- Boolean
- colour
- . Greek letter
- city
- etc.) – The type of operations that can be performed with the data. For example
- two integer ...Related searchesData types in C++
- Data types in Java
- Python data types
- Pascal data types
- More results
- User-defined data types in C PDF
- Real data type in C
- Largest data type in C
- Data types in C definition
- Complex data type in C
- Data types in programming
- Binary data type C
- Data types in programming pdf
- c data types size
- c data types printf
- c data types boolean
- c data types wikipedia
- c data types in python
- c data types uint8_t
- c data types uint
- c data types pdf
c debugging quiz questions with answers
[PDF] C Interview Questions - MIT, Kota
- 100 multiple choice questions in C programming with answers
- C Programming MCQ questions with answers
- C language questions and answers PDF free download
- C debugging questions
- [PDF] C programming I & II - NMUnmu.ac.in › F. Y. B. Sc.(Computer Science) Paper II Question Bank.pdf
- C programming I & II. • Multiple choice & one line questions. 1). The C language consist of ____ number of keywords. A] 32. B] 40. C] 24. D] 56. 2). Which of the ...[PDF] C language mcq questions pdf - Shopifyhttps://cdn.shopify.com › files › files › c_language_mcq_questions
- Programming C Programming Language questions with answer (C coding mcq) ... Where can I get C Programming questions and answers with an explanation?[PDF] C Programming Questions And Answers Basic - We've got what you ...ead.laboro.edu.br › c-programming-questions-and-answers-basic
- Here is the list of over top 500 C Programming Questions and Answers Download C Programming Questions PDF free with. Solutions All solutions are in C ...[PDF] 03-60-440: Sample questions and answershttps://windsorsacco.com › wp-content › uploads › 2018/06 › 440sam...
- 03-60-440: Sample questions and answers ... 1 Multiple choice questions. 1. ... Answer: c. 3. What formal system provides the semantic foundation for Prolog? ... One programming language can support multiple programming paradigms.[PDF] C Interview Questions - MIT
- Kotawww.mitkota.com › PDF › c-interview-questions-techpreparation
- C Interview Questions and Answers. What is C language? The C programming language is a standardized programming language developed in the early 1970s ...Related searchesC Programming multiple choice questions and answers doc
- C programming questions and answers
- C language fill in the blanks questions and answers PDF
- 100 multiple Choice questions in C with Answers pdf free download
- C programming 5 marks Questions with Answers PDF
- C programming Question Bank with answers PDF
- C language question paper with answers
- C programming practice questions and answers
- c debugging quiz questions with answers
- c debugging quiz questions with answers pdf
c diatonic harmonica blues scale
[PDF] JPs Blues From The Vault - Harmonica
- Harmonica scales chart
- Blues harmonica scale chart
- C harmonica notes
- 48 hole harmonica tutorial PDF
- [PDF] Harmonica Method - Petrucci Music Librarypetrucci.mus.auth.gr › imglnks › usimg › IMSLP91827-PMLP18890...
- Other names for the harmonica are harp
- blues harp
- mouth harp
- hand reed
- . Mississippi ... For this method we will use the 10-hole diatonic harmonica in C
- the most common harmonica for ... This allows you to play the whole chromatic scale.[PDF] Playing the Diatonic Harmonica - Mike Moxceymoxcey.net › minstrel › specific › harpbook
- A Diatonic harmonica is one that just plays the regular notes of the key it is. ... The only full C scale on the harmonica goes from the 4th hole to the 7th hole. ... sounds so good playing cross-harp is that the blues scale uses an F instead of an F# ...[PDF] Harmonica key of c blues - Shopifyhttps://cdn.shopify.com › files › files › harmonica_key_of_c_blues
- Blues Viper MS Key C Harmonica. +. TOWER Mouth Organ/HarmonicaKey-C With Scale change option. Total price. The Blues DeVille hole diatonic harmonica ...[PDF] Harmonica songs key of c - Shopifyhttps://cdn.shopify.com › files › files › harmonica_songs_key_of_c
- Low Rider is played by Lee Oskar on a C. Great harmonica songs and music for kids and beginners ... 2nd Position; key of "G" on a standard key of "C" diatonic in 2nd Position. ... I'm trying to make a blues harp "inspiration" mix-tape as a gift for.[PDF] Part A Blues Harmonica Lessons - Harmonica Westwww.harmonicawest.org.au › uploads › part_a_-__blues_harmonica_...
- “Blues Harmonica Lessons” cover page artwork – Dave Brewer. “Blues ... You have a 10 hole diatonic harmonica in C major tuning. The harmonica is a free ... The 7 notes of the diatonic scale are repeated in each octave. Created by Gary ...[PDF] Glossary_ JP Edits_ Diatonic Harmonica Techniques Glossaryhttps://www.harmonica.com › lessons › coaching › diatonic-harmonic...
- They are the same note just shown differently in certain scales. The G blues scale found on the C harp is: G Bb C C# D F G. 2d 3d^ 4b 4d^ ...[PDF] JPs Blues From The Vault - Harmonicahttps://www.harmonica.com › songbooks › jps-blues-from-the-vault
- Walking Blues using JP's Super Simple Blues Scale (19:09) … ... What goes down must come up – C harp (45:20) … ... (preferably a 10-hole diatonic.Related searchesHarmonica songsTake Me Home
- Co...
- L'uomo dell'armon...
- Ain't No Sunshine
- Stairway to Heaven
- More results
- Harmonica songs
- A flat harmonicaHarmonica chord chart PDF
- Harmonica keys for blues
- Harmonica notes chart
- Harmonica key of C
- Best blues harmonica
- How to play harmonica
- Harmonica key chart
- Cross harp
- c diatonic harmonica blues scale
c diatonic harmonica book pdf
[PDF] 101 Blues riffs vol 6 download - Harmonicaworldnet
- Blues harmonica bookHarmonica for Dummi...
- First 50 Songs Yo...
- Blues Harmonic...
- Rock N' Blues Har...
- More results
- Blues harmonica book
- Campfire harmonica songsHarmonica blues songsChromatic harmonica book PDF
- Harmonica For Dummies pdf free download
- 24 hole harmonica note layout PDF
- Blues harmonica PDF
- Harmonica chord chart PDF
- Harmonica For Dummies 2nd Edition PDF free download
- 48 hole harmonica tutorial PDF
- Absolute beginners - harmonica PDF
- c diatonic harmonica book pdf