What are the limitations of DNS sinkholing?
There are several limitations related to DNS sinkholing. To block malware or its traffic by using a DNS sinkhole, it is required by the malware to use the organization’s DNS server itself. Malware with its own hardcoded DNS server and IP address cannot be detected by the DNS sinkholing mechanism.
Does DNS sinkhole require a license?
Note: DNS Sinkhole can be applied to firewalls with an active Threat Prevention or DNS Security license. EDL of type Domain is also supported and does not require a license. Custom Anti-Spyware DNS Signatures are not supported for a Sinkhole action. Configure the DNS Sinkhole action in the Anti-Spyware profile.
How does a DNS sinkhole work?
When a DNS request attempts to connect to known malicious or unwanted destinations like botnets or Command-and-Control (C&C) servers, the sinkholing mechanism intercepts these requests, and returns a controlled IP address, which points to a sinkhole server that has been designed for just this purpose.

What is DNS sinkhole? Learning Happy Hour Quick Shot

Video Tutorial: How to Configure DNS Sinkhole

How to Configure DNS Sinkhole What is DNS sinkhole Concept LAB DAY 44 #PaloAltoTraining
|
DNS Sinkhole
A DNS sinkhole works by Qspoofings the authoritative DNS servers for malicious and unwanted hosts and domains. An administrator configures the DNS forwarder |
|
How to Configure DNS Sinkholing in the Firewall
From the Enable DNS Sinkhole list select Yes. To avoid clients from circumventing the DNS sinkhole block DNS queries via TCP for IPv4 and IPv6. |
|
Blackholing VS. Sinkholing: a Comparative Analysis
DNS sinkholing. Black holing redirects the malicious traffic to a”black hole” where it is dropped completely. Sinkholing. Revised Manuscript Received on May |
|
Build Securely a DNS Sinkhole Step-by-Step Powered by Slackware
DNS Sinkhole Server Installation . PowerDNS DNS Sinkhole Setup . ... This configuration process is used to deploy DNS sinkhole powered by the Slackware. |
|
Challenges in Effective DNS Query Monitoring
Sep 27 2019 The DNS Sinkhole approach also may be referred to as the “DNS. Firewall” or “DNS Blackhole” approach. These approaches may include optional ... |
|
Research Topic: DNS Sinkhole
For instance in DNS cache poisoning |
|
Sink Holes
Primary DNS Servers. Sink Hole. Network. 171.68.19.0/24. 171.68.19.1. DNS Caching. Server Cluster. SAFE - Architecture. DNS Caching. Server Cluster. |
|
Using DNS to protect clients from malicious domains
With DNS Sinkhole vanilla DNS. 12.3.4.56 m icrosoft.com .xyz.net ? 192.168.1.2. G. ET /dangerous.htm l. DNS Sinkhole. 192.168.1.2 safe.htm. |
|
SonicOS and SonicOSX 7 Network DNS
About DNS Sinkholes. 27. Configuring DNS Security Settings. 27. Deleting Entries in the Lists. 28. Configuring DNS Tunnel Detection. |
|
Attivo networks threatdefend® and mcafee® nsp integration dns
integrates with the McAfee NSP 8.2 taking the DNS sinkhole concept to the next level |
|
A Methodology for Multipurpose DNS Sinkhole Analyzing Double
Abstract DNS sinkhole is one of the powerful techniques to mitigate attack activities of bots, i e , zombie PCs, by blocking the communica- tion between C&C |
|
Blackholing VS Sinkholing: a Comparative Analysis - International
DNS sinkholing Black holing redirects the malicious traffic to a”black hole” where it is dropped completely Sinkholing Revised Manuscript Received on May 29, |
|
Using DNS to protect clients from malicious - Boston University
With DNS Sinkhole vanilla DNS 12 3 4 56 m icrosoft com xyz net ? 192 168 1 2 G ET /dangerous htm l DNS Sinkhole 192 168 1 2 safe htm l www upenn edu |
|
ATTIVO NETWORKS THREATDEFEND® AND MCAFEE® NSP
NSP INTEGRATION DNS SINKHOLE WITH URL SANDBOXING Botnets are a complex and pervasive form of cyber attack that has been used by attackers, |
|
From the same workstation that you administer domain - Cisco Live
DNS Sinkholing • Problem: DNS request goes via internal DNS, which hides which client is infected • Solution: Return fake “sinkhole” DNS response and note |
|
OWASP Plan - Strawman - OWASP Foundation
DNS Sinkholing – Through registering expired domain names previously used in cyber espionage attacks as command and control servers, investigators were are |
|
Block DNS with Security Intelligence using Firepower - Cisco
A DNS sinkhole is a DNS server that provides false information Instead of returning a “No such name” DNS response to DNS queries on domains you're blocking, |
|
SonicOS and SonicOSX 7 Network DNS - SonicWall
Enabling DNS Host Name Lookup over TCP for FQDN 7 DNS Cache Configuring Domain-Specific DNS Servers for Split DNS 9 About DNS Sinkholes 26 |
|
A Methodology for Multipurpose DNS Sinkhole Analyzing Double
DNS sinkhole is one of the powerful techniques to mitigate attack activities of bots, ie, zombie PCs, by blocking the communica tion between C&C server and them |
|
[PDF] Blackholing VS Sinkholing: a Comparative Analysis - IJITEE
This is what a sinkhole is DNS is a service that is used to access the internet A DNS sinkhole routes traffic to a valid IP address which analyzes the traffic and rejects the bad packets which is handled by researchers so that each of these packets can be later analyzed by them |
|
[PDF] Using DNS to protect clients from malicious - Boston University
With DNS Sinkhole vanilla DNS 123456 m icrosoftcom xyznet ? 19216812 G ET dangeroushtm l DNS Sinkhole 19216812 safehtm l upennedu |
|
[PDF] Mining Botnet Sinkholes for Fun and Profit 1 - Semantic Scholar
and control (C&C) domains [1] Essentially, sinkhol ing consists of re writing the DNS resource records of C&C domains to point to one or more sinkhole IP ad |
|
[PDF] Block DNS with Security Intelligence using Firepower - Cisco
A DNS sinkhole is a DNS server that provides false information Instead of returning a “No such name” DNS response to DNS queries on domains you're blocking, |
|
[PDF] using dns to protect clients from malicious domains - idrbt
DNS sinkhole is one among them DNS sinkhole, also called as black hole DNS, is used to spoof DNS servers to prevent resolving hostnames of specified |
- DNS sinkhole Windows
- Anubis sinkhole
- [PDF] Mining Botnet Sinkholes for Fun and Profit 1 ... - Semantic Scholarpdfs.semanticscholar.org › ...
- and control (C&C) domains [1]. Essentially
- sinkhol- ing consists of re-writing the DNS resource records of. C&C domains to point to one or more sinkhole IP ad-.[PDF] Block DNS with Security Intelligence using Firepower ... - Ciscowww.cisco.com › docs › security › firepower-management-center › 2...
- A DNS sinkhole is a DNS server that provides false information. Instead of returning a “No such name” DNS response to DNS queries on domains you're blocking
- ...[PDF] DNS in Computer Forensics - Scholarly Commonscommons.erau.edu › cgi › viewcontent
- came together to lock down
- pre-register and sinkhole as many as possible of the hundreds of algorithmically generated DNS names being used by the ...[PDF] using dns to protect clients from malicious domains - idrbtwww.idrbt.ac.in › assets › publications › Reports › IPTS2017
- DNS sinkhole is one among them. DNS sinkhole
- also called as black hole DNS
- is used to spoof. DNS servers to prevent resolving hostnames of specified ...

PDF) Sinkhole formation hazard assessment
Source:https://1e418a.medialib.edu.glogster.com/94zAX5hfR1kmO2Y7Qzgb/thumbnails/94/94zAX5hfR1kmO2Y7Qzgb-6jo2s9si1bocmjus8npoff7/1410375425-source.jpg

Sinkholes: acidic dissolves en limestone nature sinkhole
Source:https://i1.rgstatic.net/publication/245378400_Sinkhole_hazard_case_histories_in_karst_terrains/links/54abb95d0cf25c4c472f8d07/largepreview.png

PDF) Sinkhole hazard case histories in karst terrains
Source:https://dnr.mo.gov/geology/images/sinkholedevelopmentsteps.jpg

Missouri Geological Survey
Source:https://0.academia-photos.com/attachment_thumbnails/51566623/mini_magick20190125-1235-pr5gb6.png?1548408066
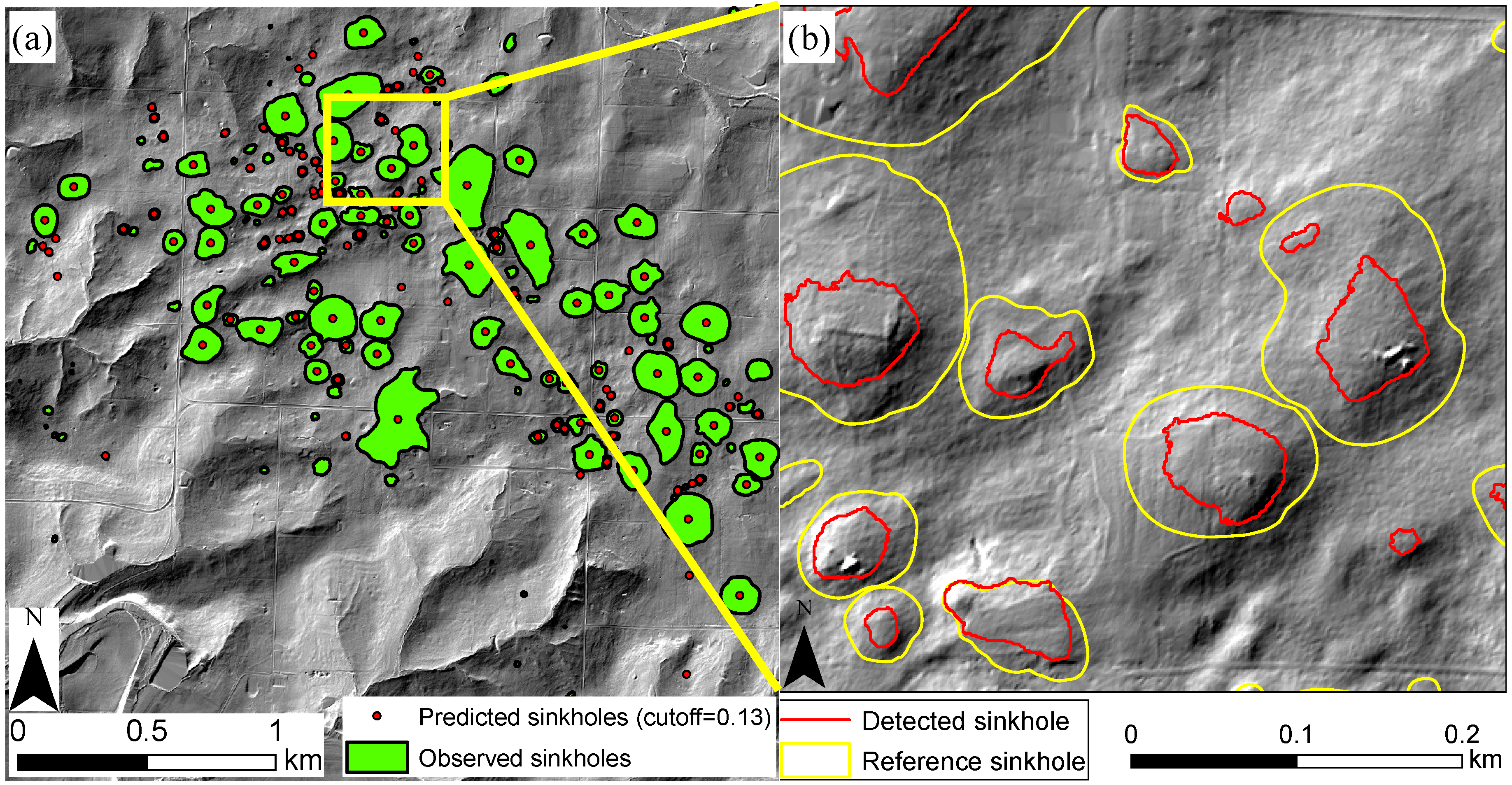
PDF) Potential of sinkhole precursor detection through
Source:https://www.mdpi.com/remotesensing/remotesensing-11-01592/article_deploy/html/images/remotesensing-11-01592-g008.png
Remote Sensing
Source: Free Full-Text
dns sinkhole list
[PDF] Paper - NDSS Symposium
- palo alto dns sinkhole list
dns sinkhole software
[PDF] Schrödinger's RAT - Damon McCoy
- DNS sinkhole Windows
- DNS sinkhole Cisco
- DNS sinkhole Palo Alto
- Setup DNS sinkhole
- [PDF] Botnet Detection Using Passive DNSwww.ru.nl › publish › pages › z-thesis_pedroluz
- The Domain Name System (DNS) is a distributed naming system ... large amount of bots and to withstand attempts of sinkholing or shutdown. ... the availability of open-source/free IRC client and server software makes this protocol very.[PDF] Countering Malicious Processes with Process-DNS Associationwww.cs.columbia.edu › papers › ssivakorn.ndss2019.pdns.pdf
- the program-DNS profile for Skype.exe captured by PDNS. Skype.exe ... or assigned to DNS sinkholes (still active and undetected)
- this feature rank low for the ...[PDF] DNS in Computer Forensics - Scholarly Commonscommons.erau.edu › cgi › viewcontent
- The core name service software is based on the ISC BIND distribution
- which is ... “It is a ready to install DNS Sinkhole server for those who would like to test.[PDF] Schrödinger's RAT - Damon McCoydamonmccoy.com › papers › Schrodinger
- A typical RAT software package consists of two compo- nents: a builder program and a ... Ideally
- a DNS sinkhole operation would be able to identify all victims ...Related searchesDNS sinkhole Android
- DNS sinkhole Linux
- DNS sinkhole definition
- How to create a DNS sinkhole
- DNS sinkhole Ubuntu
- DNS Sinkhole Service SonicWall
- FortiGate DNS sinkhole
- Why use DNS sinkhole
dns sinkhole windows
[PDF] Countering Malicious Processes with Process-DNS Association
- DNS sinkhole list
- Anubis sinkhole
- Trojan malware sinkhole
- BIND DNS sinkhole
- [PDF] using dns to protect clients from malicious domains - idrbtwww.idrbt.ac.in › assets › publications › Reports › IPTS2017
- DNS sinkhole
- also called as black hole DNS
- is used to spoof ... The next prompt window will be asking if we want to format the root partition. Since
- it has been ...[PDF] Seven Most Dangerous New Attack Techniques - RSA Conferencewww.rsaconference.com › rsa_webcast_follow-up_slides_-_3-16-17_v2
- A Windows file share
- free honeyd
- or KFsensor honeypot. • If phishing is the primary ... References. • Windows DNS Sinkhole for malware
- by Jason Fossen:.[PDF] Mining Botnet Sinkholes for Fun and Profit 1 ... - Semantic Scholarpdfs.semanticscholar.org › ...
- sinkhole IPs
- we can leverage passive DNS databases to monitor the “behavior” or their ... operate botnet sinkholes (e.g.
- Microsoft
- Verisign
- ISC
- etc.).[PDF] Blackholing VS. Sinkholing: a Comparative Analysis - IJITEEwww.ijitee.org › wp-content › uploads › papers
- DNS sinkholing. Black holing ... [13]DNS sinkhole is used to detect and prevent DOS ... MS Windows operating systems and encrypted important data and files ...[PDF] Countering Malicious Processes with Process-DNS Associationwww.cs.columbia.edu › papers › ssivakorn.ndss2019.pdns.pdf
- end-point DNS sensors to 126 Windows hosts on an enterprise network. ... or assigned to DNS sinkholes (still active and undetected)
- this feature rank low for ...Related searchesDNS sinkhole software
- DNS sinkhole Android
- How to create a DNS sinkhole
- DNS sinkhole Palo Alto
- DNS sinkhole Linux
- DNS sinkhole Cisco
- FortiGate DNS sinkhole
- Open source DNS sinkhole
dns spoof script
[PDF] DNS Cache Poisoning – The Next Generation - LiU IDA
- DDoS tutorial PDF
- TCP/IP vulnerabilities
- DDoS attack PDF
- TCP/IP vulnerabilities PPT
- [PDF] DNS Cache Poisoning Lab - DISI Security Research Group Wikisecuritylab.disi.unitn.it › lib › exe › fetch
- DNS root through the Authoritative name servers of the queried domain. In order ... This is the python script exploiting scapy we used to perform the birthday attack : ... two variables representing the domain name we are trying to spoof and the.[PDF] 3 Network and Web security - Eindhoven University of Technologywww.win.tue.nl › ~jhartog › CourseSecurity › materials
- spoofing. MAC spoofing. ARP poisoning. DNS spoofing. Application. Layer. Transport ... given username-password combination resulting in the script line:.[PDF] DNS Cache Poisoning – The Next Generation - LiU IDAwww.ida.liu.se › ~TDDD17 › literature › dnscache
- The power of this method of spoofing versus conventional DNS spoofing is shown in ... This script MUST be run from an authoritative nameserver's IP #.[PDF] A wrinkle in time: A case study in DNS poisoning - arXivarxiv.org › pdf
- Jun 26
- 2019 · threat to the DNS's wellbeing is a DNS poisoning attack
- in which the DNS ... attacker provides spoofed records in the responses to redirect the victims to ... a software application that runs automated tasks (scripts) over.Related searchesDDoS attack book PDF
- TCP/IP attacks
- TCP/IP weaknesses
- Botnets PDF
- Types of proxy server pdf
- Proxy firewall pdf
- DDoS bots
- Intitle Report Qualys Acunetix Nessus Netsparker Nmap