|
HTTP Request Smuggling in 2020 – New Variants New Defenses
“Technical Note: Detecting and Preventing HTTP Response Splitting and HTTP Request how I implemented my payloads is available in SafeBreach Labs' GitHub. |
|
HTTP Request Smuggling in 2020
However HTTP Request Smuggling payloads can get blocked as HTTP. Response Splitting attacks… • Variant 1 with SP (payload) is blocked by two rules: 921130 |
|
Karate
2 abr de 2020 Karate github.com/intuit/karate ... Given path response.id ... Payload assertion in one line. Second HTTP call using response data. |
|
AWS Lambda - Developer Guide
Request and response payloads . version or split traffic between two versions. ... assign a dedicated HTTP endpoint to your Lambda function. |
|
AWS Step Functions - Developer Guide
Starting a State Machine Execution in Response to Amazon S3 Events . and let Step Functions progress to the next state after it gets an HTTP response. |
|
DETECT BYPASS VULNERABILITIES IN CELLULAR ISP
30 dic de 2015 HTTP request or inserting a malicious payload into the web application. ... Response Splitting HTTP Request Smuggling and HTTP Response ... |
|
SDN Framework
In order to receive a response from the switch create an event handler that Next |
|
Scarecrow: Deactivating Evasive Malware via Its Own Evasive Logic
payload-agnostic such that it is able to deactivate highly obfuscated zero-day evasive HTTP response from the non-existent domain it exits without. |
|
SSRF bible. Cheatsheet
statuses 300305 |
|
AWS Command Line Interface - User Guide for Version 2
18 sept de 2019 AWS CLI GitHub repository You can view and fork the source code for the AWS CLI ... values exactly as received in the HTTP query response. |
|
Hacktricks/crlf-0d-0amd at master - GitHub
HTTP Response Splitting Description Since the header of a HTTP response and its body are separated by CRLF characters an attacker can try to inject |
|
HTTP Response Splittingbb at master · 1N3/IntruderPayloads - GitHub
A collection of Burpsuite Intruder payloads BurpBounty payloads fuzz lists malicious file uploads and web pentesting methodologies and checklists |
|
Http-response-splitting · GitHub Topics
To associate your repository with the http-response-splitting topic visit your repo's landing page and select "manage topics " Learn more Footer © 2023 |
|
Bugbounty-cheatsheet/crlfmd at master · EdOverflow - GitHub
A list of interesting payloads tips and tricks for bug bounty hunters - bugbounty-cheatsheet/crlf md at CRLF Injection HTTP Response Splitting |
|
CRLF (%0D%0A) Injection - HackTricks
An example of HTTP Response Splitting leading to XSS You can send the payload inside the URL path to control the response from the server: |
|
HTTP Response Splitting
HTTP Response Splitting is a protocol manipulation attack similar to The attack is valid only for applications that use HTTP to exchange data |
|
Attacking Websites: Detecting and Preventing HTTP Request
27 oct 2022 · This paper proposes a general solution to deal with various HTTP request smuggling attacks A reverse proxy implemented by Flask validates |
|
Web Application Firewall DRS rule groups and rules - Microsoft Learn
3 jan 2023 · This article provides information on Web Application Firewall DRS rule groups and rules |
|
CRLF injection attack Examples and Prevention - Wallarm
28 mar 2022 · HTTP Response Splitting infers the utilization of CRLF combination to separate a HTTP reaction header Information input that isn't killed |
|
Karate Test Automation Made Simple
Karate is the only open-source tool to combine API test-automation mocks performance-testing and even UI automation into a single unified framework |
What is CRLF injection and HTTP response splitting vulnerability?
CRLF injection is a software application coding vulnerability that occurs when an attacker injects a CRLF character sequence where it is not expected. When CRLF injection is used to split an HTTP response header, it is referred to as HTTP Response Splitting.What is the risk of CRLF injection?
CRLF injections are vulnerabilities where the attacker is able to inject CR (carriage return, ASCII 13) and LF (line feed, ASCII 10) characters into the web application. This lets the attacker add extra headers to HTTP responses or even make the browser ignore the original content and process injected content instead.What is the CRLF character sequence?
In the HTTP protocol, the CR-LF sequence is always used to terminate a line. A CRLF Injection attack occurs when a user manages to submit a CRLF into an application. This is most commonly done by modifying an HTTP parameter or URL.- Carriage return line feed not only marks where a new HTTP header begins or ends, but it also tells the user where a line begins or ends in a file or a block of text. The operating systems also use these CRLF characters. CR and LF are used to end lines in Windows, but only LF is used in UNIX/Linux.
|
Introduction - Black Hat
“Technical Note: Detecting and Preventing HTTP Response Splitting and HTTP how I implemented my payloads is available in SafeBreach Labs' GitHub |
|
SSRF bible Cheatsheet
HTTP response encapsulation into XML formatted response Console PHP ( require dlopen, but not exec): https://github com/dhotson/fdopen-php Basically restrictions which you may find in SSRF exploitation can be split into two groups: |
|
Your Cache Has Fallen: Cache-Poisoned Denial-of - CPDoS
Web caching enables the reuse of HTTP responses with the aim to reduce the number of is successful, the response splitting attack exploits a parsing issue in the origin zon S3, Github Pages, Gitlab Pages, Google Storage and Heroku As with the first error code 413 Payload Too Large for oversized headers and this |
|
Practical Web Cache Poisoning: Redefining - PortSwigger
poisoning caches - you can also use HTTP Response Splitting and Request Exploiting an unkeyed input isn't always as easy as pasting an XSS payload wordlist by downloading and scouring the top 20,000 PHP projects on GitHub for |
|
Cached and Confused: Web Cache Deception in the Wild
file in return, and treat the HTTP response accordingly (e g , web caches may cache poisoning attack is malicious payload injection and not private data |
|
HTTP REQUEST SMUGGLING - CGISecurity
We describe a new web entity attack technique – “HTTP Request Smuggling request/response sequencing which can allow for credential hijacking and other Splitting, for example, to be effective HRS does not require the existence of an Now let's see how the W/S interprets the same payload, once it has been |
|
CODDLE: Code-Injection Detection With Deep Learning - IEEE Xplore
20 sept 2019 · For more information, see http://creativecommons org/licenses/by/4 0/ 128617 proposed, by using an autoencoder for dynamic response anomaly recognition Dataset of XSS payloads was taken from the GitHub repos- itory [50] masquerade the injection splitting the operator with escape characters |
|
[PDF] CRLF & OpenRedirect - Zeronights 2017
HTTP Response Splitting • CRLF = HTTP Response Splitting • Add in TCP Session new response (Usually 200 HTTP Status Code) |
|
[PDF] HTTP Request Smuggling in 2020 - Black Hat
Technical Note Detecting and Preventing HTTP Response Splitting and HTTP · Request However, HTTP Request Smuggling payloads can get blocked as HTTP Demo Smuggling demo script githubcom SafeBreach Labs HRS |
|
[PDF] Introduction - Black Hat
“Technical Note Detecting and Preventing HTTP Response Splitting and HTTP how I implemented my payloads is available in SafeBreach Labs' |
|
[PDF] SSRF bible Cheatsheet - OWASP Cheat Sheet Series
HTTP response encapsulation into XML formatted response Console PHP ( require dlopen, but not exec) githubcom dhotson fdopen php Basically restrictions which you may find in SSRF exploitation can be split into two groups |
|
[PDF] Code-Reuse Attacks for the Web: Breaking Cross - ACM CCS Blog
Oct 30, 2017 · injected content and involuntarily transform its payload into exe cutable code Thus 5 githubcom SpiderLabs owasp modsecurity crs Session H2 Code In this exam ple the expressiveness of the framework is used to split an exploit it, or remove it from the HTTP response In this approach, |
|
[PDF] Cached and Confused: Web Cache Deception in the Wild - Sajjad
file in return, and treat the HTTP response accordingly (eg, web caches may choose to store the response payload) How ever, in reality, the web service will |
|
[PDF] Automatic and Context-Aware Cross-Site Scripting Filter Evasion p g
than in the reflected XSS, since the payload is displayed to any visitor another severe vulnerability, called HTTP response splitting,5 which is associated with many 9Symphony CMS, xssfilter, githubcom symphonycms xssfilter 32 |
|
[PDF] Practical Web Cache Poisoning: Redefining - PortSwigger
poisoning caches you can also use HTTP Response Splitting and Request Exploiting an unkeyed input isn't always as easy as pasting an XSS payload wordlist by downloading and scouring the top 20,000 PHP projects on for |
|
[PDF] SSRF bible Cheatsheet - Zenk - Security
HTTP response encapsulation into XML formatted response 2 PHP (require dlopen, but not exec) а githubcom dhotson fdopenphp Basically restrictions which you may find in SSRF exploitation can be split into two groups |
- SSRF cheat sheet
- SSRF cheat sheet GitHub
- CRLF injection
- SSRF payloads
- [PDF] Automatic and Context-Aware Cross-Site Scripting Filter Evasion p g ...www.dis.uniroma1.it › biblioteca › RePEc › aeg › report
- than in the reflected XSS
- since the payload is displayed to any visitor. ... another severe vulnerability
- called HTTP response splitting
- 5 which is associated with many ... 9Symphony CMS
- xssfilter
- https://github.com/symphonycms/xssfilter. 32 ...[PDF] Practical Web Cache Poisoning: Redefining ... - PortSwiggerportswigger.net › papers › web-cache-poisoning
- poisoning caches - you can also use HTTP Response Splitting and Request ... Exploiting an unkeyed input isn't always as easy as pasting an XSS payload. ... wordlist by downloading and scouring the top 20
- 000 PHP projects on GitHub for.[PDF] Uplink Documentationuplink.readthedocs.io › downloads › pdf
- Mar 13
- 2019 · Uplink turns your HTTP API into a Python class. ... so the response we get back from GitHub is wrapped inside a requests. ... The Body annotation declares the JSON payload: ... owner
- repo_name = data["full_name"].split("/").[PDF] SSRF bible. Cheatsheet - Zenk - Securityrepo.zenk-security.com › ...
- HTTP response encapsulation into XML formatted response. 2 ... PHP (require dlopen
- but not exec):аhttps://github.com/dhotson/fdopenphp ... Basically restrictions which you may find in SSRF exploitation can be split into two groups:.Related searchesCRLF injection payloads
- CRLF injection Tutorial
- SSRF bible
- SSRF attack cheat sheet
- Ssrf bypass orange
- Xip io SSRF
- SSRF filter bypass
- SSRF exploit
Serverless PDF news renderer in Nodejs
Source: by Miron Machnicki
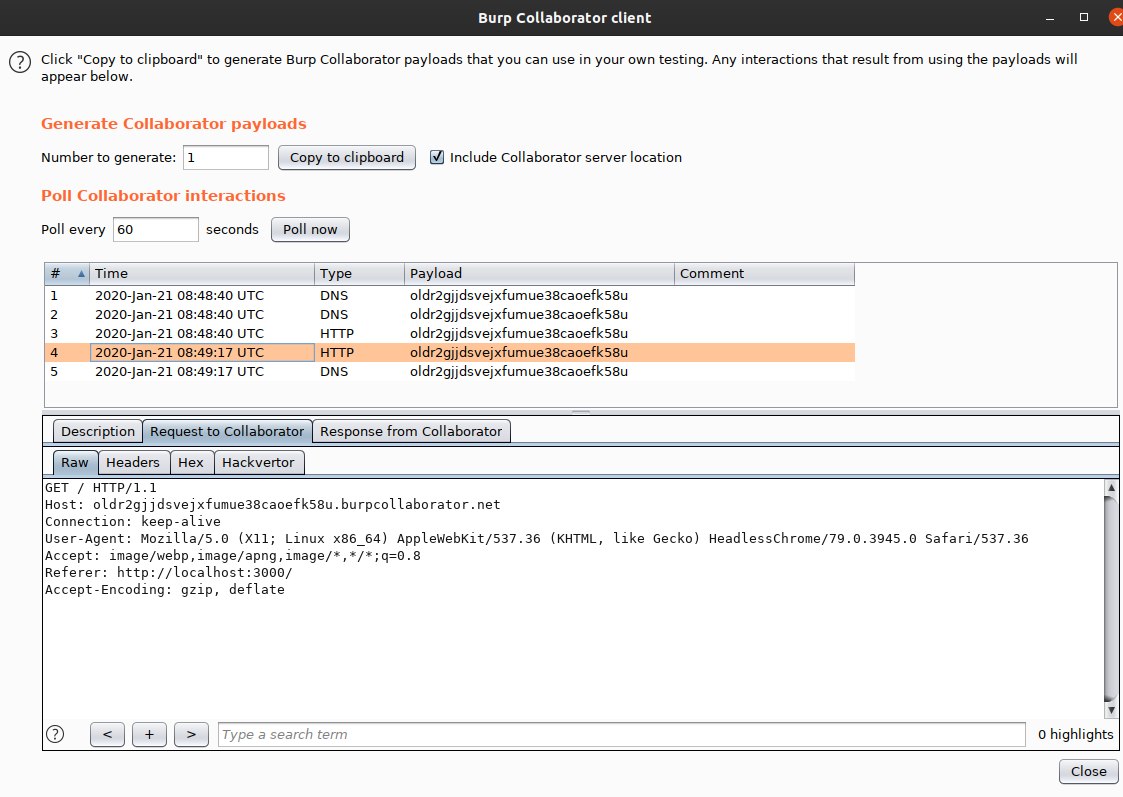
Source:https://p4fg.github.io/images/2020-01-21-09-49-55_first_burpcollab.png
H1-415-CTF
Source:https://p4fg.github.io/images/pdf-generated.png
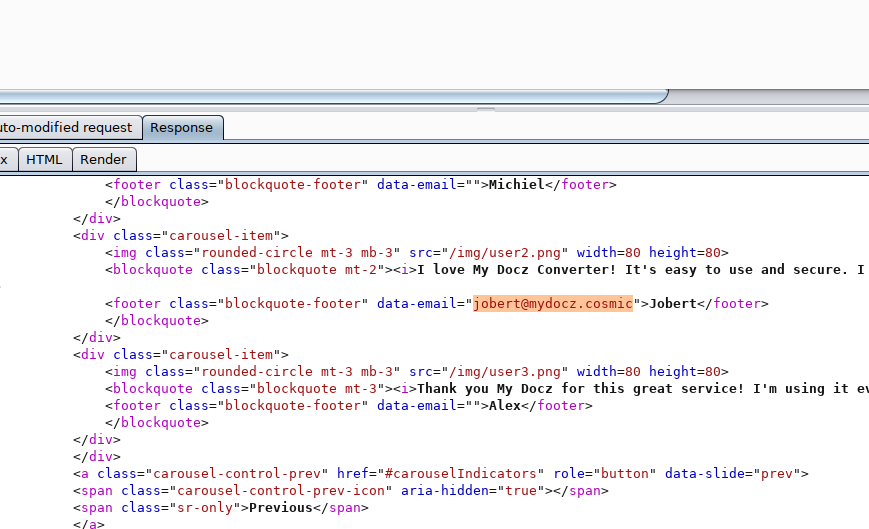
H1-415-CTF
Source:https://p4fg.github.io/images/2020-01-17-11-30-49-html-testimonial.png
H1-415-CTF
Source:https://miro.medium.com/max/2624/0*aG3-Zl0ilcnkROeM

Source:https://gblobscdn.gitbook.com/assets%2F-M8-SyxgckWEMfZfndbo%2F-MD--UY2p2iA2W5_qfhY%2F-MD-08hkAFiid2w4Ov4h%2Fimage.png?alt\u003dmedia\u0026token\u003d04658793-4ab5-4f43-9711-1c6ec7463300
http response splitting prevention
[PDF] Finding Security Vulnerabilities in Java Applications with - Usenix
- http response splitting prevention in java
- http response splitting prevention c#
- http response splitting prevention owasp
http tutorial pdf
[PDF] Introduction to Sockets Programming in C using TCP/IP
- HTTP Tutorial PDF download
- Explain HTTP protocol PDF
- HTTP Notes pdf
- HTTP explained
- HyperText Transfer Protocol - DePaul Universitycondor.depaul.edu › dmumaugh › readings › handouts › HTTP › http
- Aug 8
- 2003 · transport of Postscript and PDF material respectively. Other expected ... after the question ”Did you search the site and read the HTTP tutorial?”.[PDF] HttpCore Tutorial - Apachehc.apache.org › httpcomponents-core-ga › tutorial › pdf › httpcore-tu...
- HTTP response is a message sent by the server back to the client after having received and interpreted a request message. The first line of that message consists ...[PDF] O'Reilly - HTTP: The Definitive Guidewww.staroceans.org › e-book › O'Reilly - HTTP - The Definitive Guide
- Jun 11
- 2010 · http://www.bgw.org/tutorials/utilities/nc.php for details. ... http://www.acm.org/ sigcomm/ccr/archive/2001/jan01/ccr-200101-mogul.pdf.[PDF] TCP/IP Tutorial and Technical Overview - IBM Redbookswww.redbooks.ibm.com › redbooks › pdfs
- TCP/IP Tutorial and Technical Overview. TCP/IP and System p: http://www.ibm. com/systems/p/library/index.html. TCP/IP and System i:.[PDF] Introduction to Sockets Programming in C using TCP/IPwww.csd.uoc.gr › material › tutorials › cs556-3rd-tutorial
- DNS lookup. UDP 53. FTP. TCP 21. HTTP. TCP 80. POP3. TCP 110. Telnet. TCP 23. CS556 - Distributed Systems. Tutorial by Eleftherios Kosmas. 9 ...Related searchesHttp standard pdf
- HTTP PDF
- HTTP tutorialspoint
- HTTP documentation PDF
- HTTP and HTTPS protocol pdf
- HTTP in Computer Networks pdf
- HTTP example
- HTTP protocol explained
http www acea be
[PDF] Commercial vehicles in Europe - BNP Paribas Leasing Solutions UK
- http://asea.net
http www adobe com is correct
[PDF] instructions on the annotation of pdf files - Elsevier
- Adobe Reader
- Adobe Acrobat Pro
- Adobe PDF editor
- Adobe Acrobat DC
- Marking Corrections in Adobe Reader or Acrobat (Pro) - Brillbrill.com › downloads_static › static_preparingmanuscripts_adobecorrections
- The easiest way to correct your proofs is by using Adobe Reader or Acrobat. This document will ... Reader from http://get.adobe.com/reader/. 1. Setting up Adobe ...[PDF] Adobe Reader Helpwww.parkerstore.jp › phj › catalog
- The How To window appears on the right side of the document pane and never ... http://partners.adobe.com/ans/developer/acrosdk/main.html (English only) on ...[PDF] How to make corrections to your proofs using Adobe Acrobat ...eprints.lincoln.ac.uk › eprint
- right-hand side to view the Comments pane. 4. ... Acrobat help: http://helpx.adobe .com/acrobat.html ... http://dx.doi.org/10.1080/14702541.2014.978805. 5. 10.[PDF] instructions on the annotation of pdf files - Elsevierwww.elsevier.com › Annotating-PDFs-Adobe-Reader-9-X-or-XI
- http://www.adobe.com/products/reader/tech-specs.html. Note: if you opt ... that your Adobe Acrobat version is lower than 9 or the PDF ... the top right-hand corner.Related searchesPDF screen reader
- Adobe installer
- Adobe Acrobat Pro DC user guide PDF
- PDF screen reader test
- Adobe screen reader
- PDF reader for visually impaired
- An assistive technology like a screen reader may be running
- Adobe Acrobat Pro DC quick reference guide