return stack
|
Ret2spec: Speculative Execution Using Return Stack Buffers
In our work we show how return stack buffers (RSBs) |
|
Spectre Returns! Speculation Attacks using the Return Stack Buffer
exploits the return stack buffer (RSB) a common pre- dictor structure in modern CPUs used to predict return addresses. We show that both local attacks |
|
Ret2spec: Speculative Execution Using Return Stack Buffers
ret2spec: Speculative Execution Using Return Stack Buffers. Accepted at ACM CCS 2018 (preliminary version). Giorgi Maisuradze. CISPA Saarland University. |
|
What If We Dont Pop the Stack? The Return of 2nd-Class Values
every function return pops the stack it is difficult to return stack-allocated data from a callee upwards to its caller – especially variable-size data |
|
Return-Stack Orchard Heater
The Return-Stack heater-developed at the University of California-has been available commercially for about 10 years. Most of the heaters from the first. |
|
Return Address Stack (RAS)
designated stack pointer) is maintained to store all the return addresses. ? In Assembly language programs before Jal |
|
Spectre Returns! Speculation Attacks using the Return Stack Buffer
The recent Spectre attacks exploit speculative execution a pervasively used feature of modern microprocessors |
|
Correct Alignment of a Return-Address-Stack after Call and Return
It is accepted that the alignment of a return-address- stack can be preserved by checkpointing on branches and recovering on branch mispredictions the |
|
Armv8-M Architecture Stack sealing and why it is needed in
28 avr. 2021 When a Non-secure API that is called by Secure software is completed and returns to the. Secure world that is |
|
Improving Prediction for Procedure Returns with Return-Address
But wrong-path execution after mispredictions frequently corrupts the return-address stack making repair mechanisms necessary. If the proces- sor implements |
| Improving Prediction for Procedure Returns with Return |
|
RDIP: Return-address-stack Directed Instruction Prefetching - Iowa Stat
exploits the return stack buffer (RSB) a common pre-dictor structure in modern CPUs used to predict return addresses We show that both local attacks (within the same process such as Spectre 1) and attacks on SGX are possible by constructing proof of concept attacks We also analyze additional types of the attack on the ker- |
| Lecture Notes on Stacks - CMU School of Computer Science |
|
Ret2spec: Speculative Execution Using Return Stack Buffers
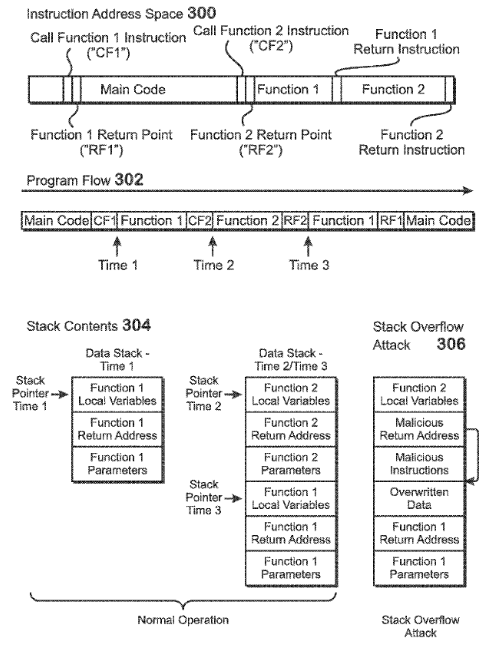
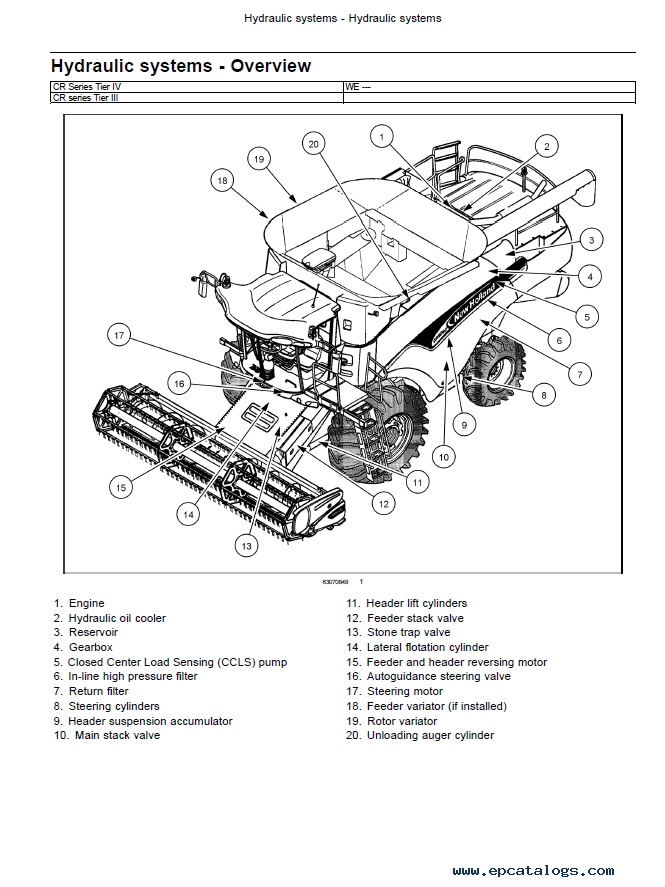
Stack C B A Z Y X W RSB throw ret (a) Exception handling: While the RSB predicts a return to func-tion Z the exception is caught by function C causing a chain of misspeculations when C returns as the RSB is misaligned to the returnaddressesonthestack P1 D K Y K X P1 D P1 C P1 B P1 A P1 C K Y K X P1 D P1 C RSB of P1 RSB of P2 RSB of OS |
|
Ret2spec: Speculative Execution Using Return Stack Buffers
properties of return stack buffers (RSBs) RSBs are small microarchitecturalbuffersthatrememberreturnaddressesof themostrecentcallsandspeedupfunctionreturns Given thatreturnaddressesarestoredonthestackwithoutsuch RSBsamemoryaccessisrequiredtofetchareturndesti-nationpossiblytakinghundredsofcyclesifretrievedfrom |
|
Searches related to return stack filetype:pdf
The RSB is a processor structure used to predict return address by pushing the return address from a call instruc-tion on an internal hardware stack (typically of size 16 entries) When the return is encountered the processor uses the top of the RSB to predict the return address to support speculation with very high accuracy |
What is the state of the return address stack?
- The state of the return address stack succinctly sum- marizes program context. The current call stack accurately re ects the program ex- ecution path taken to reach a particular point in the code. The contents of the instruction cache are determined by the instruction fetches encountered along this execution path.
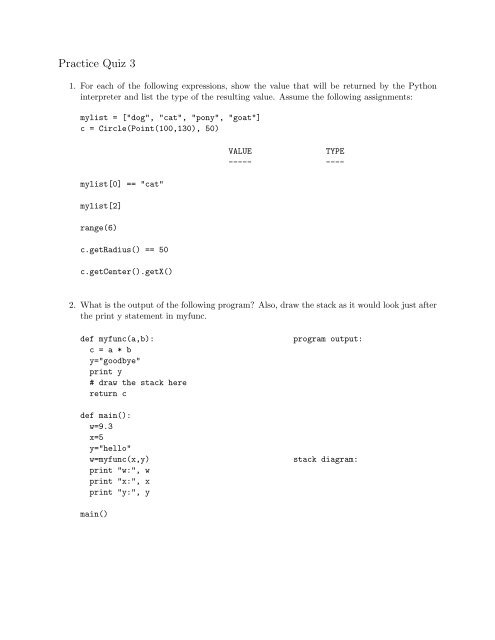
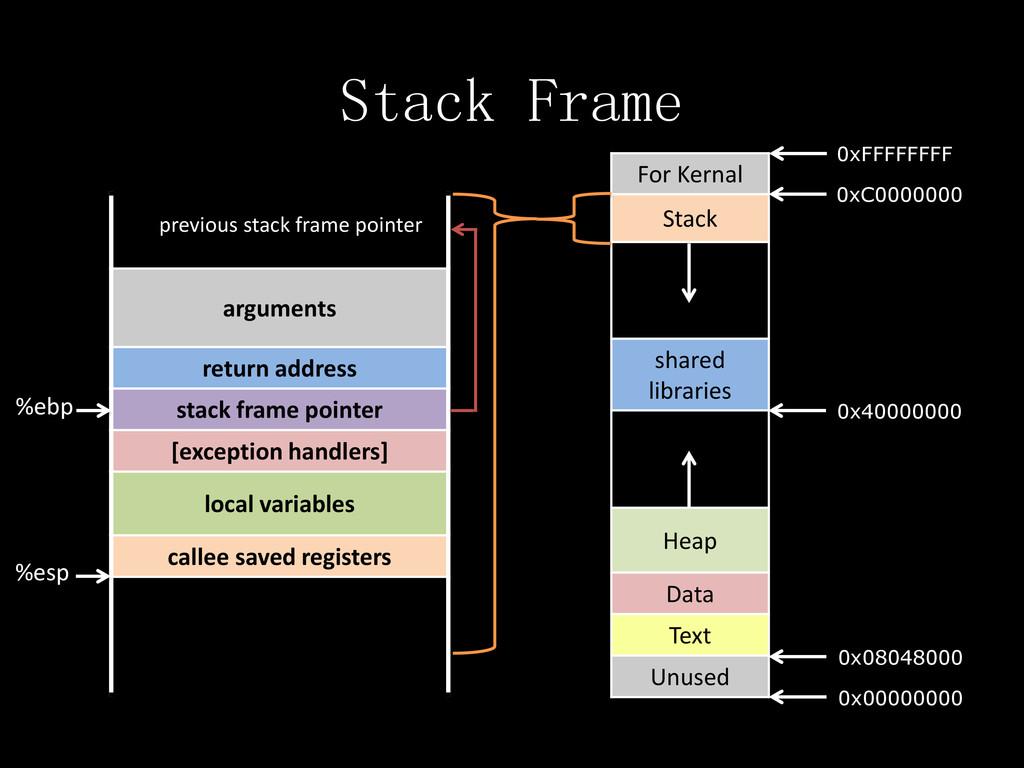
How to push an element onto the stack?
- To push an element onto the stack, we create a new list item, set its data?eld and then its next ?eld to the current top of the stack. Finally, we needto update thetop?eld of the stack to point to the new list item. While thisis simple, it is still a good idea to draw a diagram. We go from data? next? top? bo.om? data? next? top? boom
How to check if a list is a valid stack?
- To test if some structure is a valid stack, we only need to check that thelist starting attopends inbottom, which is the same as checking that thisis a list segment (as introduced in the last lecture). To check if the stack is empty, we only need to verify thattopisNULL.
What is the difference between a queue and a stack?
- Stacks are similar to queues in that we can insert and remove items. But weremove them from the same end that we add them, which makes stacks aLIFO (Last In First Out) data structure. We want the creation of a new (empty) stack as well as pushing and pop-ping an item all to be constant-time operations.
|
Improving Prediction for Procedure Returns with Return-Address
A simple stack, however, fails in the presence of spec- ulative execution The fetch engine predicts branch out- comes and speculatively fetches subsequent |
|
Return Address Stack (RAS)
designated stack pointer) is maintained to store all the return addresses ▫ In Assembly language programs, before Jal, we have two instructions to push the |
|
Spectre Returns Speculation Attacks using the Return Stack Buffer
In particular, rather than exploiting the branch predictor unit, SpectreRSB exploits the return stack buffer (RSB), a common pre- dictor structure in modern CPUs |
|
Correct Alignment of a Return-Address-Stack after Call - PHARM
This paper suggests that on call and return mispredictions the recovered top-of- stack pointer should point to the next and previous stack po- sition respectively |
|
Reinforcing Meltdown Attack by Using a Return Stack - IEEE Xplore
31 déc 2019 · Our method utilizes a return stack buffer (RSB), a type of branch prediction unit equipped in most commodity x86 processors The basic concept is |
|
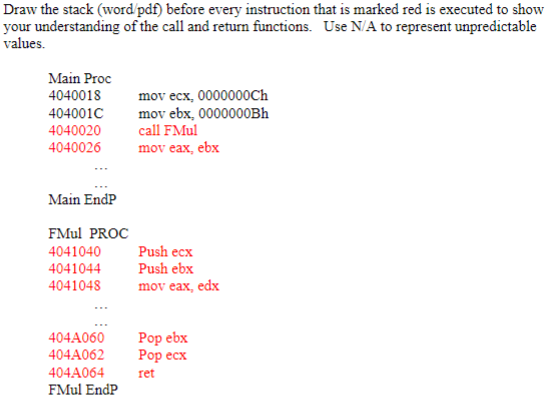
The CALL/RET Instructions and the Stack
If we push the return point values on to the stack when a call is executed, then we just have the ret instruction pop off the most recent value to use as the new value |
|
Speculative Return Address Stack Management Revisited
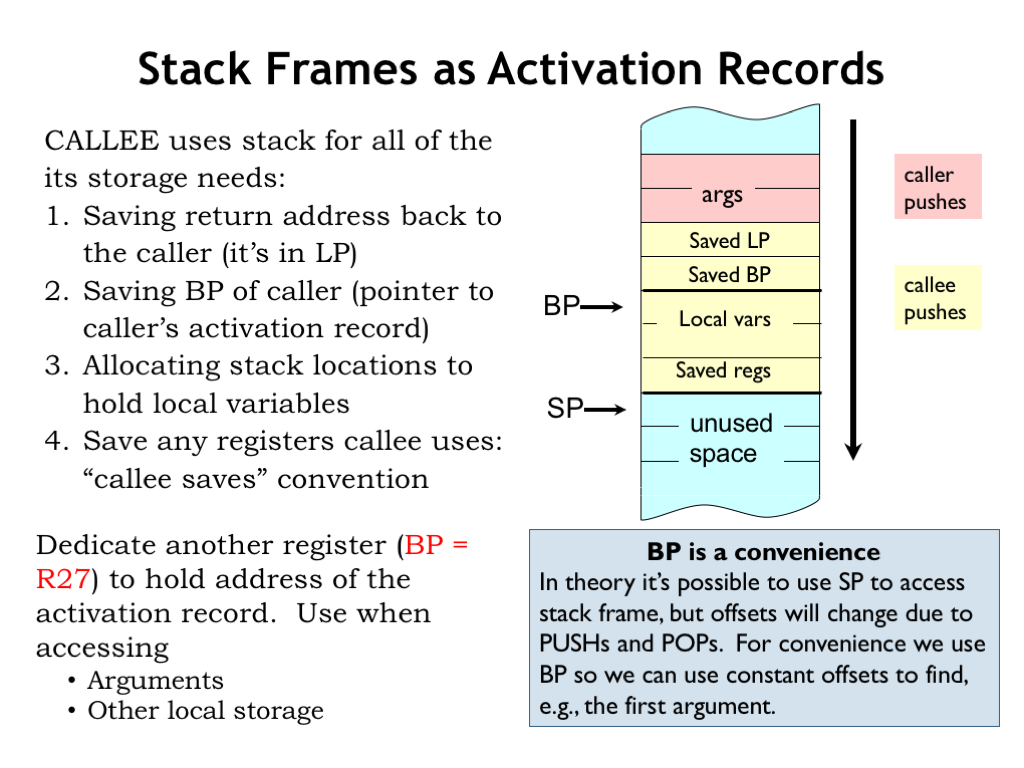
In this article, we address the prediction of procedure returns On modern processors, proce- dure returns are predicted through a return address stack ( RAS) |
|
Subroutines & Stack
18 fév 2019 · A subroutine may pass a return value back to the caller ○ Space in data memory must be reserved for parameters, local variables, and the return |
|
A Reliable Return Address Stack: Microarchitectural - ResearchGate
Because return addresses stored on the microarchitectural stack are only updated upon function calls and returns, it is impossible for memory-based attacks such |