rsa attacks
|
Twenty Years of Attacks on the RSA Cryptosystem 1 Introduction
These attacks illustrate blatant misuse of. RSA. Although many such attacks exist we give only two examples. 3In this context |
|
RSA Attacks
Our objective is to explorer some of these attacks. RSA encryption in its simple form is explained as follow. Let N = pq be the product of two large primes of |
|
On Some Attacks on Multi-prime RSA
attacks on specific instances on the RSA cryptosystem are known that apply if for example |
|
Fault Attacks on RSA Signatures with Partially Unknown Messages?
In this paper we successfully extends rsa fault attacks to a large class of partially known message configu- rations. The new attacks rely on Coppersmith's |
|
Modulus Fault Attacks Against RSA-CRT Signatures
These key-recovery attacks only apply to RSA without CRT and they require significantly more faults than Boneh et al.'s attack |
|
Side-Channel Attacks on Textbook RSA and ElGamal Encryption
This paper describes very efficient attacks on plain RSA en- cryption as usually described in textbooks. These attacks exploit side channels caused by |
|
Classical Attacks on a Variant of the RSA Cryptosystem
claimed that the classical small private attacks on RSA such as Wiener's continued fraction attack do not apply to their scheme. In this paper we. |
|
New Partial Key Exposure Attacks on RSA
therefore the method belongs to the strongest known partial key exposure attacks. Keywords: RSA known bits |
|
Algorithmic Countermeasures Against Fault Attacks and Power
14 Feb 2017 analysis and many kinds of fault attacks. Keywords: Bellcore attack RSA-CRT |
|
RSA Attacks - University of Tennessee at Chattanooga
RSA Attacks By Abdulaziz Alrasheed and Fatima Introduction Invented by Ron Rivest Adi Shamir and Len Adleman [1] the RSA cryptosystem was first revealed in the August 1977 issue of Scientific American The RSA is most commonly used for providing privacy and ensuring authenticity of digital data RSA is used by many commercial systems |
|
Twenty Years of Attacks on the RSA Cryptosystem
Attacks on RSA that take longer than this time bound are not interesting These include at-tacks such as an exhaustive search for Mand some older attacks published right after the ini-tial publication of RSA Our objective is to survey attacks on RSA that decrypt messages without directly factoring the RSA modulus N Nevertheless it is worth |
|
Attacks on the RSA Cryptosystem - 65610csailmitedu
Attacks on the RSA Cryptosystem Notes by Henry Corrigan-Gibbs MIT - 6 5610 Lecture 14 (March 22 2023) Warning: This document is a rough draft so it may contain bugs Please feel free to email me with corrections Outline •Recap: The RSA function •Rabin’s function •Hastad’s broadcast attack •Fault attack •Small-root attacks |
|
Lecture 12: Public-Key Cryptography and the RSA Algorithm
(RSA) ALGORITHM FOR PUBLIC-KEY CRYPTOGRAPHY — THE BASIC IDEA The RSA algorithm is named after Ron Rivest Adi Shamir and Leonard Adleman The public-key cryptography that was made possible by this algorithm was foundational to the e-commerce revolution that followed The starting point for learning the RSA algorithm is Euler’s |
|
Textbook RSA Encryption - UMD
Additional Attacks Encrypting a partially known message: Coppersmith’s Theorem: Let ( )be a polynomial of degree Then in time (log???? )one can find all such that =0 ????and ?????1/???? In the following we assume =3 Assume message is = 1 2 where 1 is known but not 2 So =2????? |
|
Searches related to rsa attacks filetype:pdf
RSA Implementation Attacks Attacks 1 RSA RSA oPublic key: (eN) oPrivate key: dEncrypt M C = Me (mod N) Decrypt C M = Cd (mod N) Digital signature oSign h(M) In protocolssign “challenge”: S = Md (mod N) |
Are there any attacks on RSA that take longer than this?
- Attacks on RSA that take longer than thistime bound are not interesting. These include at-tacks such as an exhaustive search for Mandsome older attacks published right after the ini-tial publication of RSA.Our objective is to survey attacks on RSA thatdecrypt messages without directly factoring theRSA modulus N.
Is improper use of RSA dangerous?
- Although twenty years of research haveled to a number of fascinating attacks, none ofthem is devastating. They mostly illustrate thedangers of improper use of RSA. Indeed, securelyimplementing RSA is a nontrivial task. Our goal isto survey some of these attacks and describe theunderlying mathematical tools they use.
What is the first attack on an RSA public key?
- The first attack on an RSA public key hN;eito con-sider is factoring the modulus N. Given the fac-torization of N, an attacker can easily construct 2A source that explains semantic security and gives ex-amples of semantically secure ciphers is . '(N), from which the decryption exponentd=e?1mod'(N) can be found.
Is FAC-toring the modulus a brute-force attack on RSA?
- We refer to fac-toring the modulus as a brute-force attackon RSA.Although factoring algorithms have been steadilyimproving, the current state of the art is still farfrom posing a threat to the security of RSA whenRSA is used properly.
|
Twenty Years of Attacks on the RSA Cryptosystem - Applied
rise to a chosen ciphertext attack"3 on RSA Therefore, a negative answer may be welcome Next we show that exposing the private key d and factoring N are |
|
RSA Attacks - UTC
N is called the RSA modulus, e is called the encryption exponent, and d is called the decryption This is known as the first attack on RSA public key (N, e) |
|
Cryptanalytic Attacks on RSA
attack It is common that to speed-up the computation of RSA encryption, a short public exponent e is often used It is also true for |
|
Twenty Years of Attacks on the RSA Cryptosystem
The first attack on an RSA public key 〈N,e〉 to con- sider is factoring the modulus N Given the fac- torization of N, an attacker can easily construct ϕ(N), from |
|
Attack on RSA Cryptosystem - Root Me
The security of RSA algorithm depends on the ability of the hacker to factorize num- bers New the attacks on RSA cryptosystem were dangerous Indeed |
|
Mathematical Attacks on RSA Cryptosystem - Science Publications
We describe the integer factoring attacks, attacks on the underlying Key words: RSA, cryptography, cryptanalysis, attack, factorization, low-exponent, one-way |
|
New Attacks on the RSA Cryptosystem - Cryptology ePrint Archive
three attacks improve the bounds of some former attacks that make RSA attack in the presence of many decryption exponents for a single RSA modulus |
|
A Survey of Cryptanalytic Attacks on RSA Mathematics and
RSA was the first public key cryptosystem to be published and it is one of the most some attacks on RSA sessions using low public or private exponent and |
|
A generalized attack on RSA type cryptosystems - Abderrahmane Nitaj
the hardness of factoring large composite integers, nevertheless, RSA has been extensively studied for vulnerabilities by various non factorization attacks The |
























![PDF] Cybersecurity Threats Malware Trends and Strategies by Tim PDF] Cybersecurity Threats Malware Trends and Strategies by Tim](https://0.academia-photos.com/attachment_thumbnails/36024183/mini_magick20180818-24174-1geallb.png?1534628485)



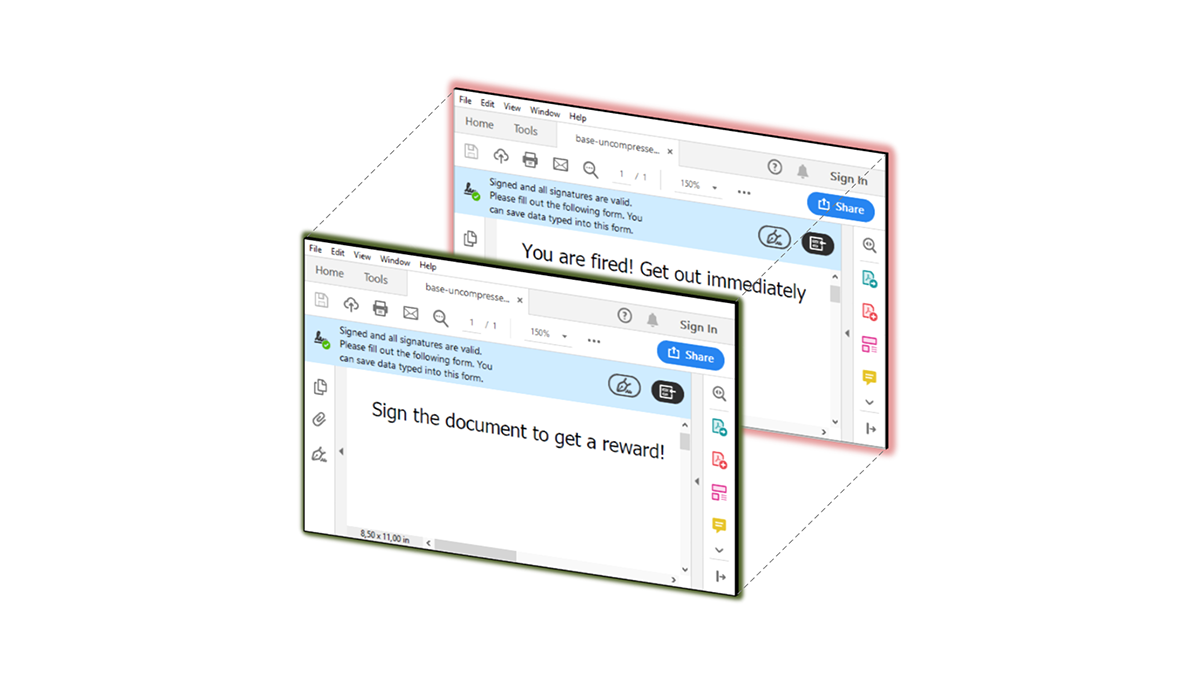
![PDF][Download] When Panic Attacks: The New Drug-Free Anxiety PDF][Download] When Panic Attacks: The New Drug-Free Anxiety](https://www.cybercureme.com/wp-content/uploads/2020/07/shadow-attack-technical-fkNv9s-770x439_c.png)

![Bestsellers***) Read Book [PDF] Badass Ways to End Anxiety \u0026 Stop Bestsellers***) Read Book [PDF] Badass Ways to End Anxiety \u0026 Stop](https://1.bp.blogspot.com/-CH7YhckKeXo/Xyf2L_CR3YI/AAAAAAAAAK0/rjsks7oMU7YxyXgJ2FWj5eFzP5N4u0rHACPcBGAsYHg/s697/Annotation%2B2020-08-03%2B183213.png)