security risk assessment pdf
|
C-TPATs Five Step Risk Assessment
Through this program CBP works with the trade community to strengthen international supply chains and improve United States border security; in exchange |
|
NIST SP 800-39 Managing Information Security Risk: Organization
ISO/IEC 31010 Risk management – Risk assessment techniques;. • ISO/IEC 27001 |
|
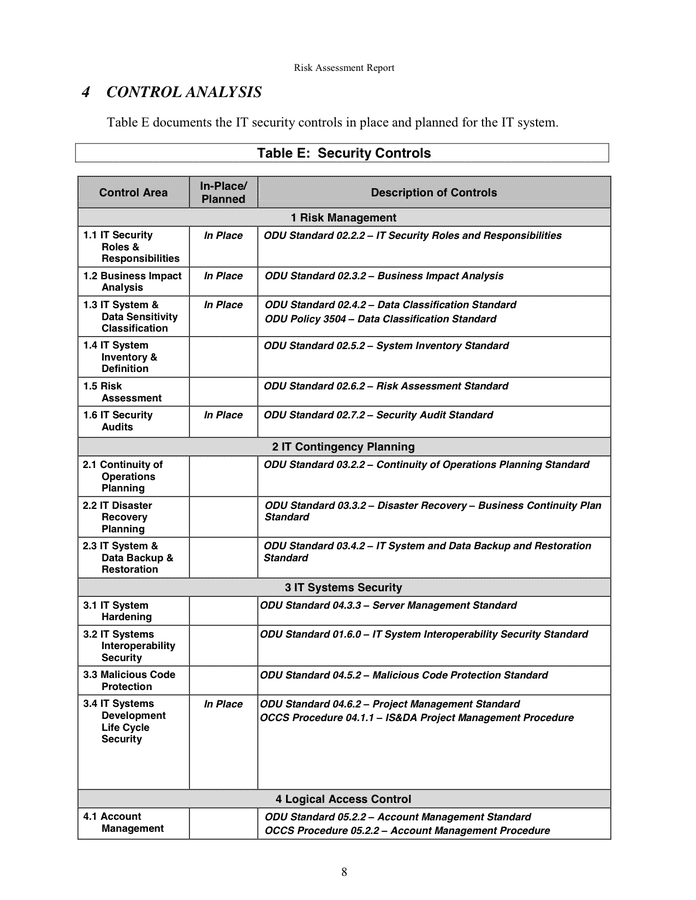
Handbook for Information Technology Security Risk Assessment
pdf). NIST SP 800-18. National Institute of Standards and Technology (NIST) Procedures for. Developing Security Plans for Information Technology Systems |
|
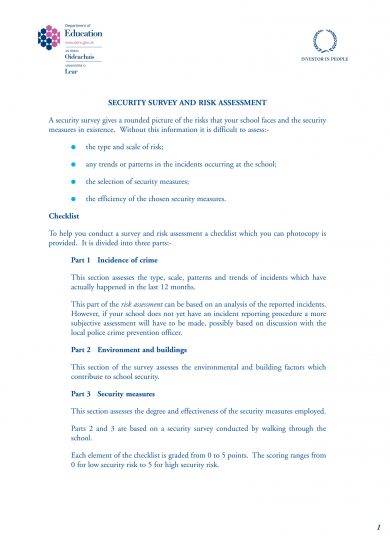
General Security Risk Assessment
13 nov. 2002 The General Security Risk Assessment seven-step process creates a methodology for security professionals by which security risks at a ... |
|
NIST Special Publication 800-30 Revision 1 Guide for Conducting
Risk assessment is the process of identifying estimating |
|
Annual Threat Assessment of the U.S. Intelligence Community
6 févr. 2023 This annual report of worldwide threats to the national security of the United States responds to. Section 617 of the FY21 Intelligence ... |
|
Harmonized Threat and Risk Assessment (TRA) Methodology
23 oct. 2007 • R1-001 Threat and Risk Assessment Involving On-site Physical Security Examination; ... pdf. Page 56. TRA-1 Harmonized Threat and Risk Assessment ... |
|
RISK ASSESSMENT FOR PERSONNEL SECURITY A GUIDE
Personnel security risk assessment focuses on employees their access to the organisation's assets |
|
Homeland Threat Assessment October 2020
6 oct. 2020 This Homeland Threat Assessment (HTA) the first of its kind for the U.S. Department of Homeland Security (DHS) |
|
Security Series - Paper 6 - Basics of Risk Analysis and Risk
1)(ii)(A) for. Risk Analysis |
|
General Security Risk Assessment
Aban 22 1381 AP The possibility of loss resulting from a threat |
|
Iraq: Climate-related security risk assessment
Mordad 23 1397 AP pdf>. Food and Agriculture Organization of the United Nations |
|
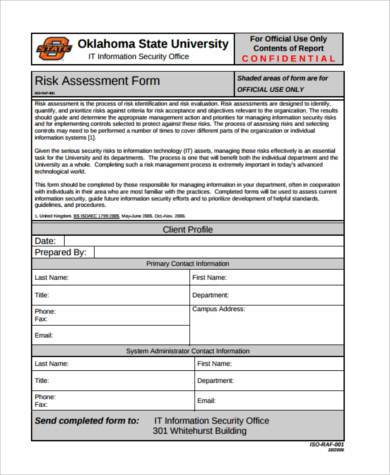
Security Risk Assessment Tool v3.2 User Guide
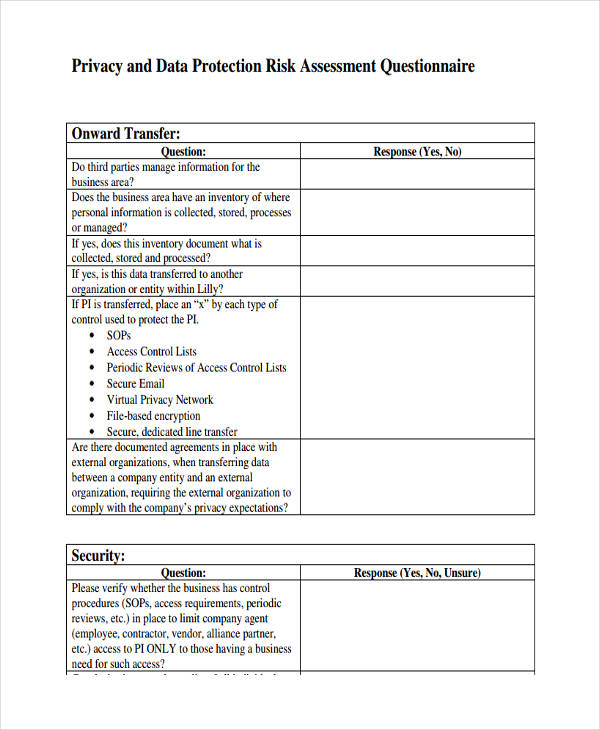
The Security Risk Assessment Tool at HealthIT.gov is provided for definitive source on safeguarding health information from privacy and security risks. |
|
ATA-2021-Unclassified-Report.pdf
Farvardin 20 1400 AP This annual report of worldwide threats to the national security of the United ... 2021 Annual Threat Assessment highlights some of those ... |
|
ACT Alliance
The safety and security risk environment can cover a broad range of threats from violence conflict |
|
Homeland Threat Assessment October 2020
Mehr 15 1399 AP Homeland Threat Assessment. U.S. Department of Homeland Security. 3. “DHS has a vital mission: to secure the nation from the many. |
|
The Strategic National Risk Assessment in Support of PPD 8: A
To inform homeland security preparedness and resilience activities the SNRA evaluated the risk from known threats and hazards that have the potential to |
|
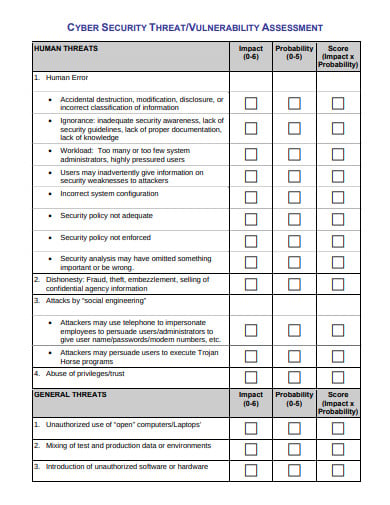
Guidance on Risk Analysis Requirements under the HIPAA Security
Tir 23 1389 AP The Security Rule requires entities to evaluate risks and ... hhs.gov/ocr/privacy/hipaa/administrative/securityrule/riskassessment.pdf. |
|
Security Series - Paper 6 - Basics of Risk Analysis and Risk
Risk Analysis requires a covered entity to |
|
EISF
The safety and security risk environment can cover a broad range of threats including violence conflict |
|
Guide for conducting risk assessments - NIST
manage the risk to organizational operations and assets individuals other organizations and the Nation that results from the operation and use of information systems A common foundation for information security will also provide a strong basis for reciprocal acceptance of security authorization decisions and facilitate information sharing |
|
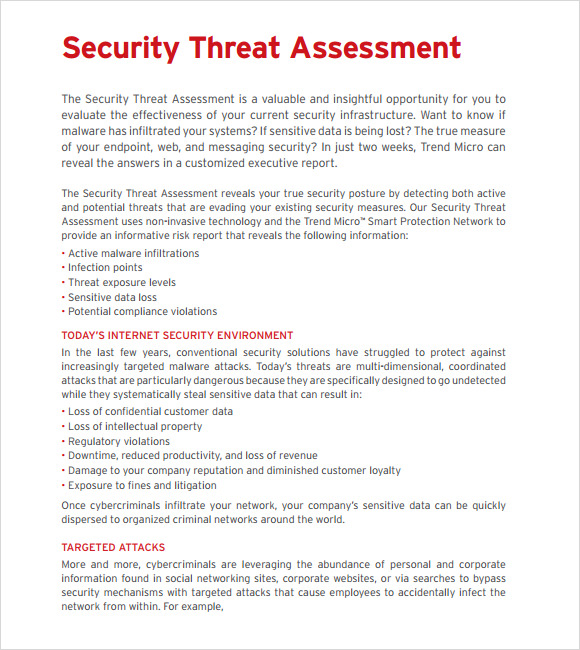
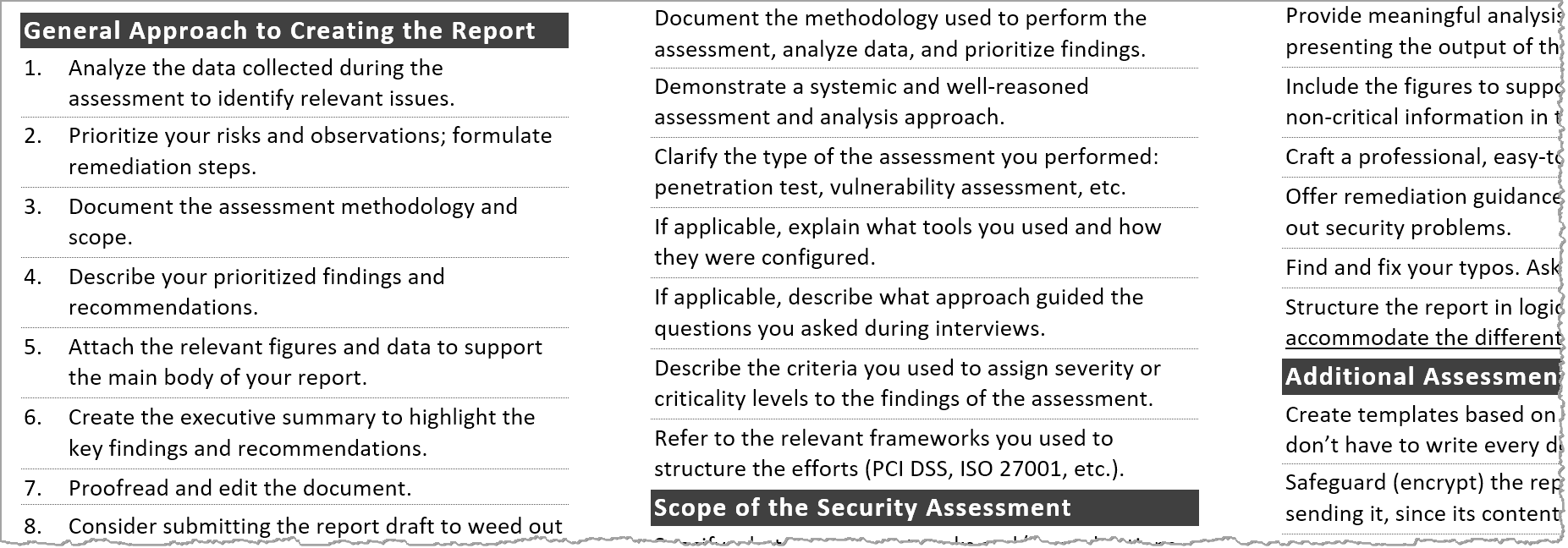
Guide to Getting Started with a Cybersecurity Risk Assessment
Cybersecurity (cyber) risk assessments assist public safety organizations in understanding the cyber risks to their operations (e g mission functions critical service image reputation) organizational assets and individuals 1 To strengthen operational and cyber resiliency SAFECOM has developed this guide to assist public safety |
|
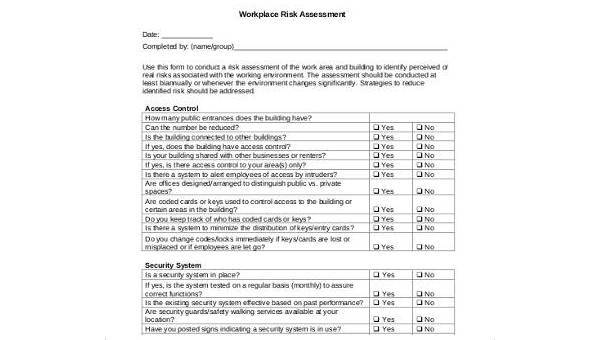
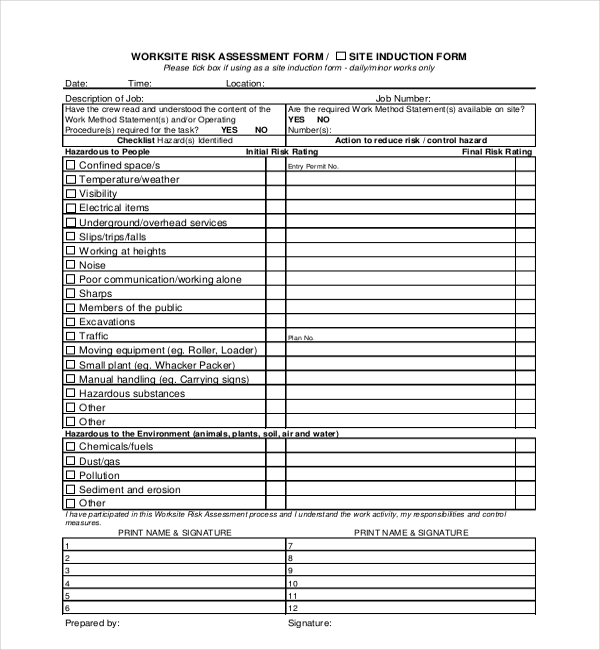
Site security assessment guide - Zurich Insurance
Site security assessment guide An in-depth risk assessment and analysis are the first steps in effective site security planning This guide will help you determine the likelihood and consequences of a security issue or gap and help you prioritize the appropriate protective actions to take |
|
5 Reasons Why a Security Risk Assessment is Important Abacus T
Information Security Risk Management Standard Risk Assessment Policy Identify: Supply Chain Risk Management (ID SC) ID SC-2 Suppliers and third-party partners of information systems components and services are identified prioritized and assessed using a cyber supply chain risk assessment process Identification and Authentication Policy |
|
Searches related to security risk assessment pdf filetype:pdf
Assessing Cybersecurity Risk Assessing Cybersecurity Risk Roles of the Three Lines of Defense Executive Summary Organizations of all types are becoming more vulnerable to cyber threats due to their increasing reliance on computers networks programs and applications social media and data |
What's the importance of a security risk assessment?
- 5 Reasons Why a Security Risk Assessment is Important Avoid Security Breaches. Regardless of how sophisticated your system is, you're never invulnerable to cybersecurity threats. ... Protects Your Reputation. Without frequent assessments, the danger of security breaches is high. ... Reduce Cost. ... Avoid Violations. ... Increase Self-Awareness. ...
What is security risk assessment and how does it work?
- Security Risk Assessments are performed by a security assessor who will evaluate all aspects of your companies systems to identify areas of risk. These may be as simple as a system that allows weak passwords, or could be more complex issues, such as insecure business processes.
What is HIPAA security risk assessment?
- The objective of a HIPAA risk assessment is to identify potential risks and vulnerabilities to the confidentiality, availability, and integrity of all protected health information (PHI) that an organization creates, receives, maintains, or transmits.
|
The Security Risk Assessment Methodology - CORE
There is an increasing demand for physical security risk assessments in which the span of assessment usually encompasses threats from terrorism This paper |
|
The Security Risk Assessment Handbook : A Complete Guide for
and Technology, NIST Special Publication 800-30, July 2002 http://csrc nist gov/ publications/nistpubs/800-30/sp800-30 pdf 26 The Security Risk Assessment |
|
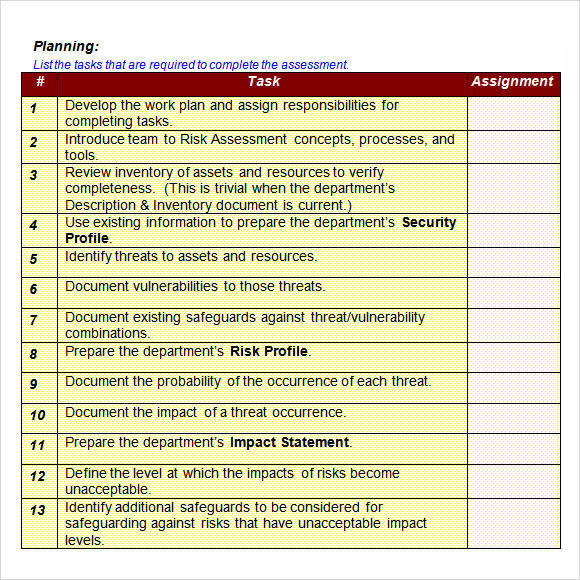
SECURITY RISK ANALYSIS AND MANAGEMENT
Threat identification, usually on a form, includes a title, a brief definition, and written rational for the inclusion of the threat in the assessment process A written |
|
General Security Risk Assessment
13 nov 2002 · Risk, Assessment, Vulnerability, Threat, Asset, Security Survey V Guidelines Designation This guideline is designated as ASIS GLCO 01 |
|
Site security assessment guide
Site information Summary Risk assessment Management policies Physical security Access control Employee security Information security Material security |
|
Guide for Conducting Risk Assessments - NIST Technical Series
responsible for developing information security standards and guidelines, Establishing the scope of the risk assessment helps to determine the form and |
|
Risk Assessment Process - Information Security - Digitalgovtnz
All-of-Government Risk Assessment Process: Information Security February 2014 Attribution to the Department of Internal Affairs should be in written form and |
|
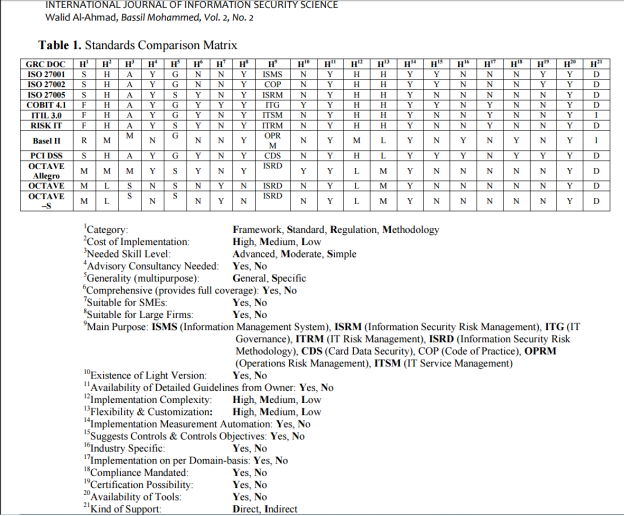
Running Head: Information Security Risk Assessment Methods
Information Security Risk Assessment Methods, Frameworks and Guidelines 2 Abstract Assessing risk is a fundamental responsibility of information security |
|
Risk Assessment - HHSgov
reports on ITL's research, guidance, and outreach efforts in computer security, Risk management is the process of identifying risk, assessing risk, presented in table form, with each requirement accompanied by an explanation of how the |


![PDF Free Download] Information Security Risk Assessment Toolkit PDF Free Download] Information Security Risk Assessment Toolkit](https://imgv2-1-f.scribdassets.com/img/document/360051941/298x396/91e9e94efe/1507072958?v\u003d1)







![download]_pdf The Security Risk Assessment Handbook A Complete Gui download]_pdf The Security Risk Assessment Handbook A Complete Gui](https://asset-pdf.scinapse.io/prod/2104800148/figures/table-2.jpg)
![PDF] Introducing OCTAVE Allegro: Improving the Information PDF] Introducing OCTAVE Allegro: Improving the Information](https://img.17qq.com/images/fhmfwwgnmqy.jpeg)









![PDF] IT Security Risk Management Model for Cloud Computing: A Need PDF] IT Security Risk Management Model for Cloud Computing: A Need](https://zbook.org/img/2002/26422-guidancemethodologynationalsafetyan_090220035701.jpg)