security testing tools comparison
|
Comparison of penetration testing tools for web applications
15 août 2011 These tools test the security by performing an attack without malicious payload (i.e. they will not delete parts of the web application or the ... |
|
A Comparison Study of Penetration Testing Tools in Linux
The purpose of this pilot study was to compare various the open source penetration testing tools available in Linux. Key Words--cyber security testing |
|
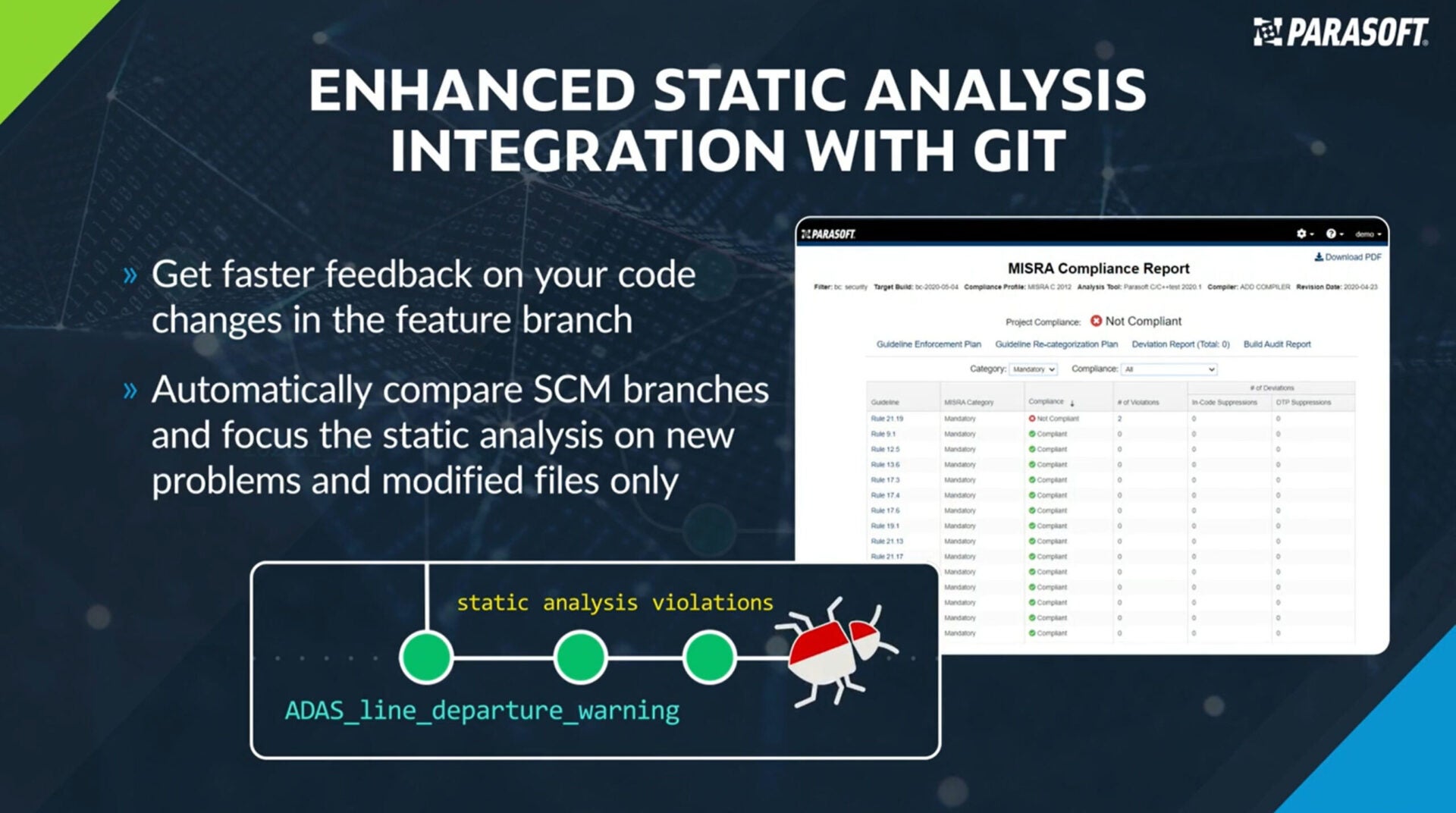
Comparing the Effectiveness of Penetration Testing and Static Code
more SQL Injection vulnerabilities than penetration testing tools. Another key observation is that tools implementing the same detection approach frequently |
|
Comparison of Wireless Network Penetration Testing Tools on
security. In this paper we investigate three popular open source wireless penetration testing tools (Aircrack –ng |
|
SECURITY TESTING OF ETHIOPIAN E-GOVERNMENTAL
By using three penetration testing tools we test the security of websites. We use Acunetix |
|
On Combining Static Dynamic and Interactive Analysis Security
20 déc. 2020 Analysis Security Testing Tools to Improve OWASP ... work they describe the comparison of these tools separately analyzing 63 open source ... |
|
Selection of penetration testing methodologies: A comparison and
Penetration testing is one strategy used to mitigate the risk of cyber-attack. Penetration testers attempt to compromise systems using the same tools and |
|
Comparative Analysis of the Automated Penetration Testing Tools
8 jan. 2020 In this research based thesis we look at the modern day automated web penetration testing tools and compare them with industry known. OWASP ... |
|
Comparative Analysis of the Automated Penetration Testing Tools
8 jan. 2020 In this research based thesis we look at the modern day automated web penetration testing tools and compare them with industry known. OWASP ... |
|
Penetration Testing Security Tools: A Comparison
Abstract:—Penetration testing (additionally referred as pen testing) is the exercise related to the checking out your PC framework network or even internet |
|
10 Types of Application Security Testing Tools and How to UseThem
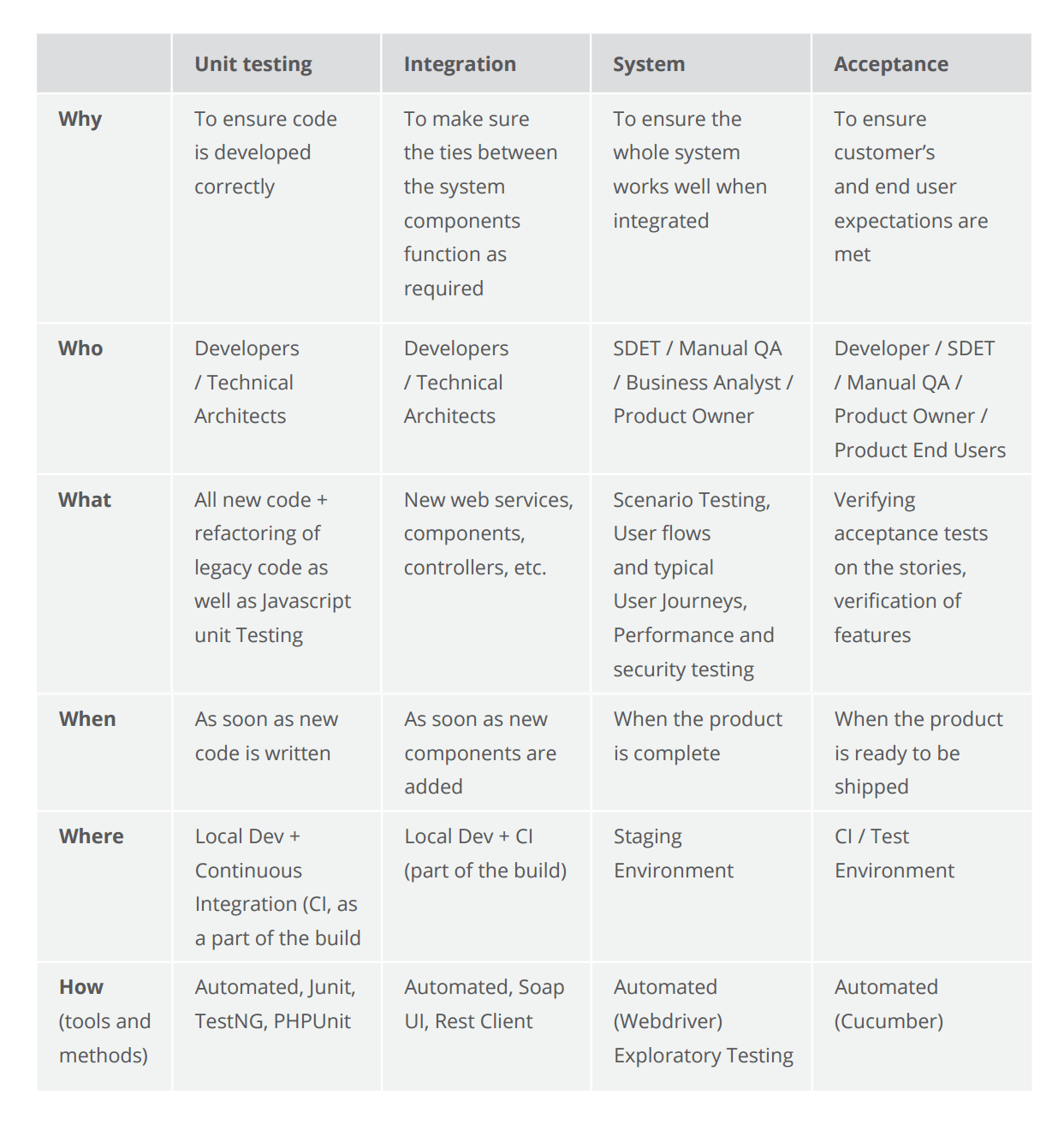
10 Types of Application Security Testing Tools www sei cmu edu/podcasts For instance the most basic one that people do is static code analysis Those are tools that read your code They have a copy of the source code and they read through it and look for vulnerabilities and weaknesses |
|
Technical guide to information security testing and - NIST
Apr 3 2017 · Automated Security Testing popular free security tools” Comparison with Zap Active Scan Better coverage of the tested app |
|
Technical guide to information security testing and assessment
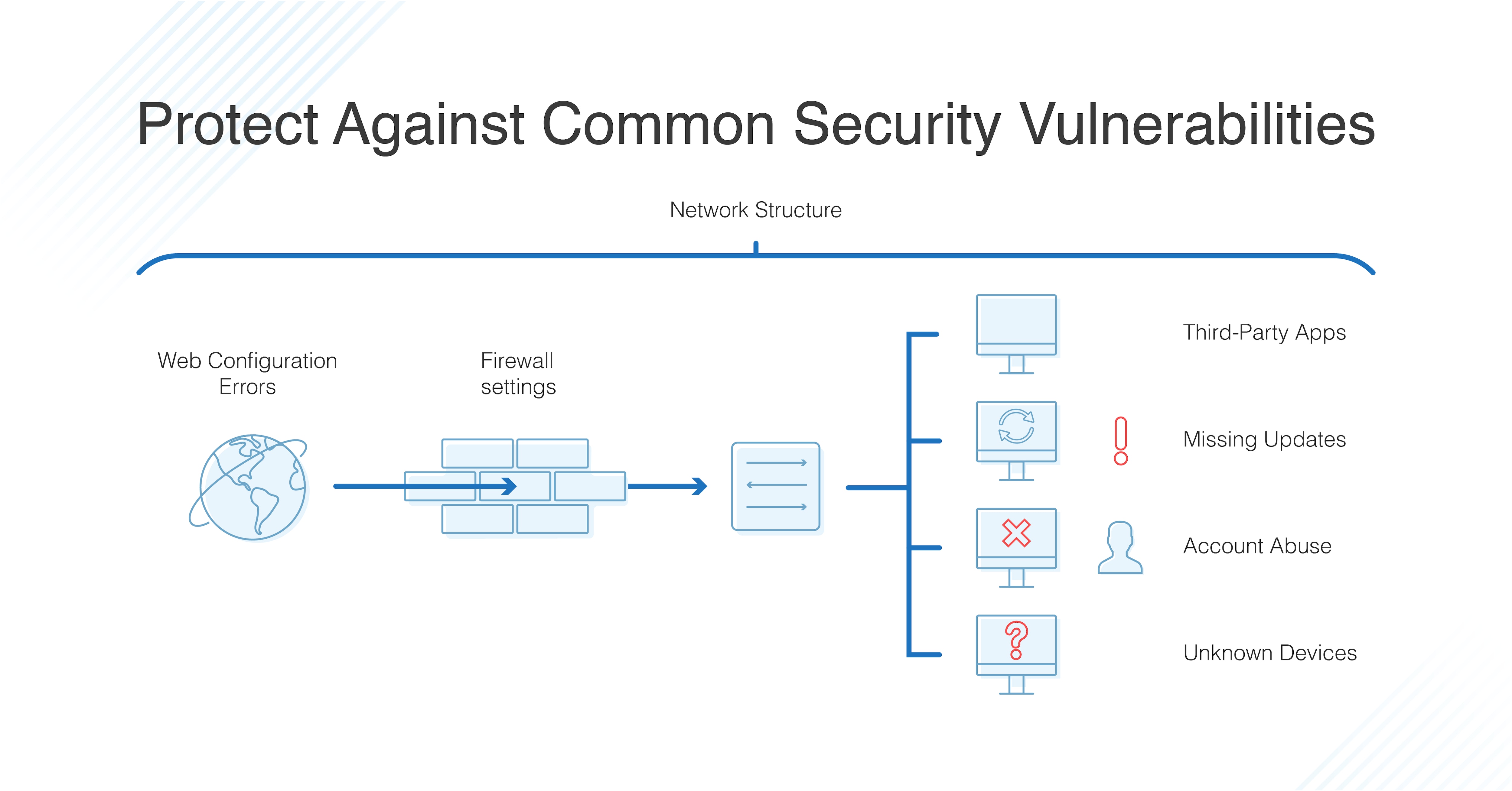
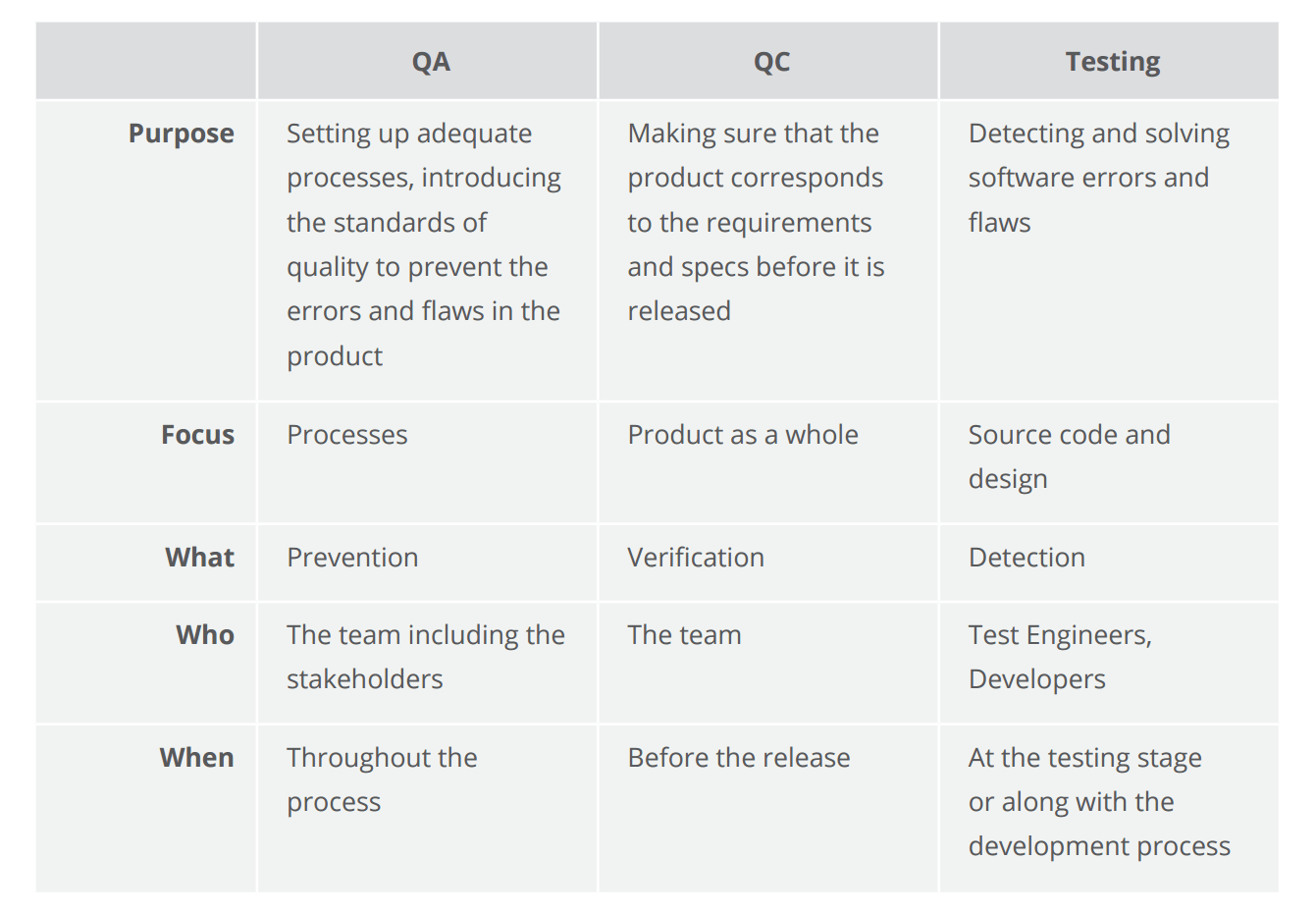
Security assessments have specific objectives acceptable levels of risk and available resources Because no individual technique provides a comprehensive picture of an organization’s security when executed alone organizations should use a combination of techniques |
|
OWASP Top 10 - 2017
•Application security tools and standards •Complete books on application security testing secure code development and secure code review •Presentations and videos •Cheat sheets on many common topics •Standard security controls and libraries •Local chapters worldwide •Cutting edge research •Extensive conferences worldwide |
|
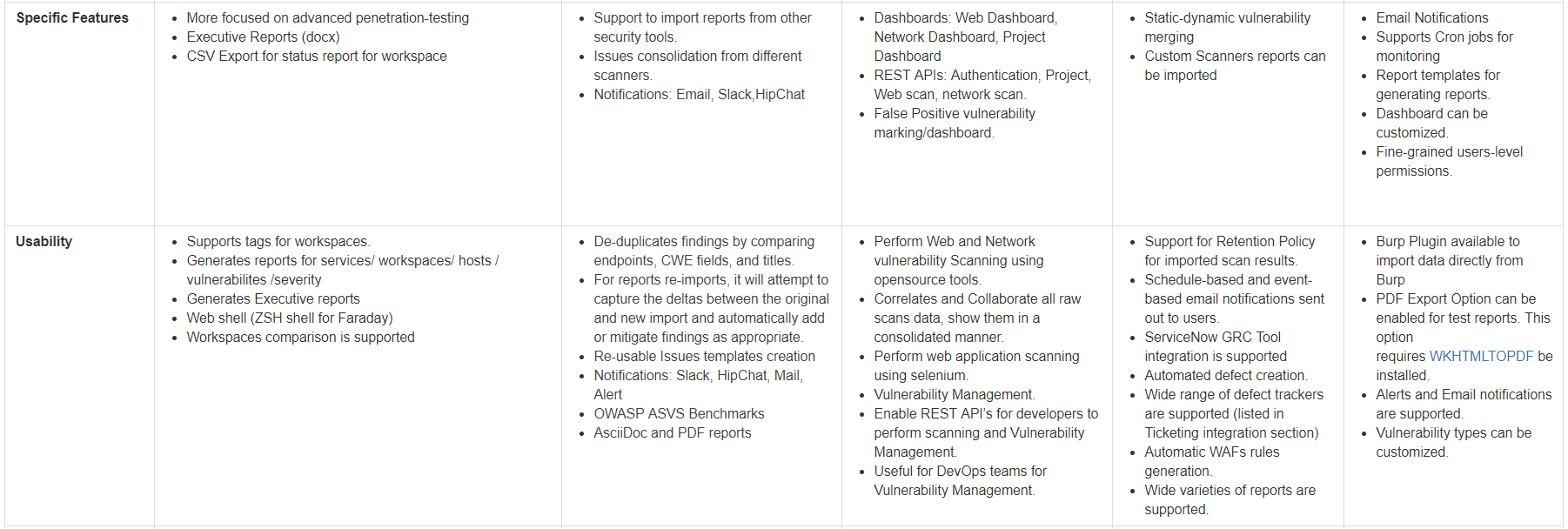
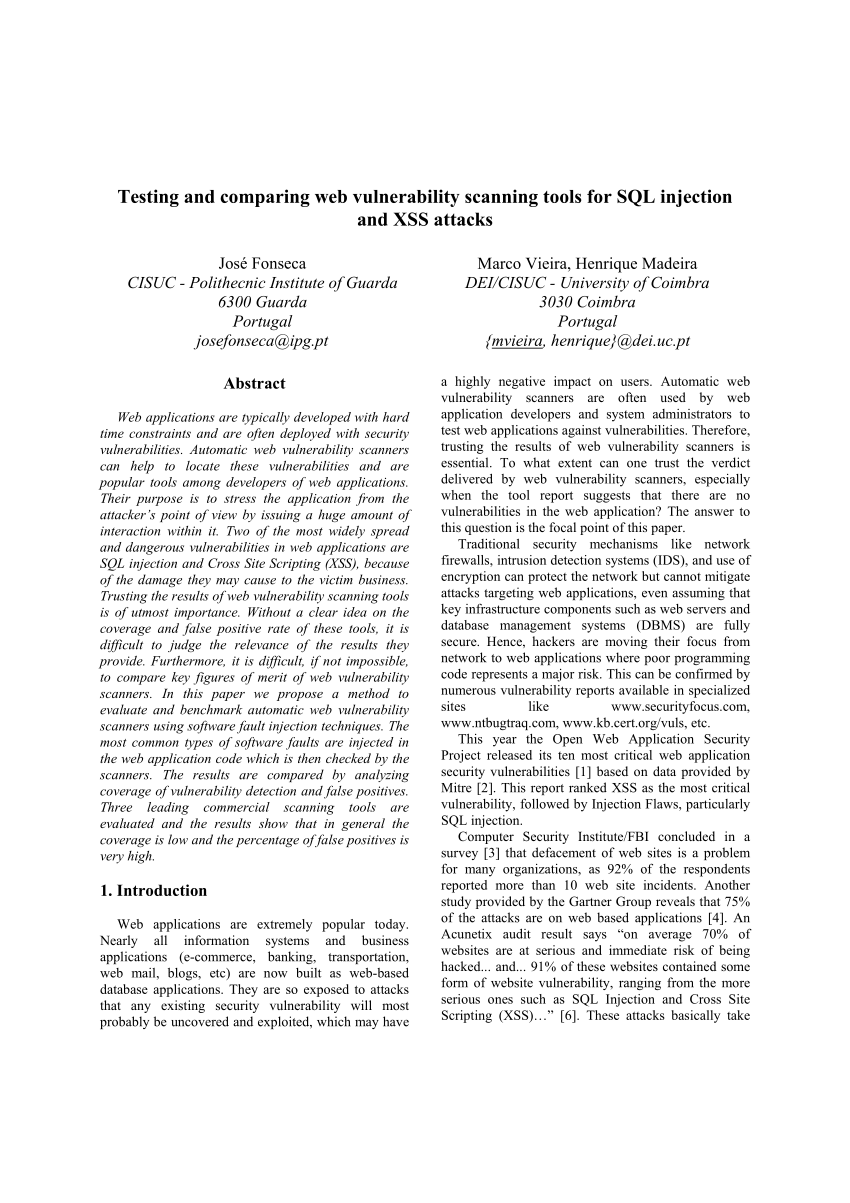
Comparison of penetration testing tools for web applications
estingT the security of web applications is very important There are several ways to do this One such way is by using penetration testing tools These tools test the security by performing an attack without malicious payload (i e they will not delete parts of the web application or the database it uses) against |
|
Le d-ib td-hu va-top mxw-100p>Commercial Application Testing - Synopsys Cybersecurity Report
Security assessment and testing tools such as vulnerability scanners and penetration testing tools have become a key factor to evaluate the security configuration of computer systems |
What is information security testing and assessment?
- TECHNICAL GUIDE TO INFORMATION SECURITY TESTING AND ASSESSMENT maximum level of potential access to an attacker. They may instead result in the testers learning more about the targeted network and its potential vulnerabilities, or induce a change in the state of the targeted network’s security.
What should be included in the scope of security testing?
- If physical security of information systems is in the scope of the testing, procedures should be determined and a form—with appropriate signatures and contact information—generated for the test team to show to law enforcement or onsite security personnel in the event that they are questioned. 5.2.
Should I use an independent network for covert testing?
- 25Using an independent network is particularly advantageous if covert testing is being conducted. This can make it more difficult for the security staff to identify the source of the activity (i.e., the IP addresses are not associated with a test team or organization).
What are the different types of application protection?
- There are commercial and open source application protection frameworks such as OWASP AppSensor, web application firewalls such as ModSecurity with the OWASP ModSecurity Core Rule Set, and log correlation software with custom dashboards and alerting. A10 :2017 Insufficient Logging & Monitoring Exploitability: 2 Prevalence: 3 Detectability: 1
|
Comparing Application Security Tools - Defcon
Tools Used “Market Leading” Dynamic Testing Tools A Static Code Analyzer Dynamic Test Tracing Tool The Application Open source Java based Blog |
|
A Comparison Study of Penetration Testing Tools in Linux - IJSER
The purpose of this pilot study was to compare various the open source penetration testing tools available in Linux Key Words--cyber security, testing, network — |
|
SECURITY TESTING AND COMPARING VULNERABILITY
SECURITY TESTING AND COMPARING VULNERABILITY DETECTION TOOLS FOR CLOUD BASED SAAS APPLICATIONS Krishnaveni S1 , Prabakaran |
|
Comparative Analysis of the Automated Penetration Testing Tools
8 jan 2020 · day automated web penetration testing tools and compare them with industry known OWASP Benchmark for vulnerabilities We also address |
|
Security Testing of Web Based Applications - CORE
Furthermore, a short introduction to security testing tools and their different categories are given review (touchpoint 1), and penetration testing (touchpoint 3) |
|
Investigation and Comparison of Web Application Vulnerabilities
aimed to analyse the frequently used web vulnerability test tools with sample scenarios and security testing tools that can be used with user friendly interface , |
|
A Comparative Study of Pen Testing Tools - International Journal of
5 jui 2018 · that are possible on a web application and comparison of various penetration tools to find best tools for penetration testing Keywords |
|
Assessing and Comparing Vulnerability Detection In - IOSR Journal
The first targets tools capable of detecting SQL Injection vulnerabilities in SOAP web serv-ices, including detection approaches based on penetration testing |
![PDF] Comparison of penetration testing tools for web applications PDF] Comparison of penetration testing tools for web applications](https://phoenixnap.com/blog/wp-content/uploads/2019/02/types-of-pen-testing.png)
![PDF] Comparison of penetration testing tools for web applications PDF] Comparison of penetration testing tools for web applications](https://d3i71xaburhd42.cloudfront.net/7564a3c5608e52e0c8d69b8819726e07f409b005/33-Table5.13-1.png)
![PDF] Comparison of penetration testing tools for web applications PDF] Comparison of penetration testing tools for web applications](https://d3i71xaburhd42.cloudfront.net/7564a3c5608e52e0c8d69b8819726e07f409b005/24-Figure5.1-1.png)
![PDF] Comparison of penetration testing tools for web applications PDF] Comparison of penetration testing tools for web applications](https://www.guru99.com/images/securityt2.png)


![35+ Best GUI Testing Tools with Complete Details [2021 LIST] 35+ Best GUI Testing Tools with Complete Details [2021 LIST]](https://d3i71xaburhd42.cloudfront.net/7564a3c5608e52e0c8d69b8819726e07f409b005/28-Figure5.5-1.png)
![PDF] Comparison of penetration testing tools for web applications PDF] Comparison of penetration testing tools for web applications](https://i1.rgstatic.net/publication/282019457_A_Comparative_Overview_on_Penetration_Testing/links/56214fd808ae93a5c927de6a/largepreview.png)






![PDF] Comparison of penetration testing tools for web applications PDF] Comparison of penetration testing tools for web applications](https://mk0softwaretest02r6g.kinstacdn.com/wp-content/uploads/2018/07/API-Testing-Tools.png)