5g cybersecurity
Is 5G safe from hackers?
5G also comes with potential rogue access points hackers can use to intercept your data.
5) G networks are designed to provide enhanced security features for Internet of Things (IoT) devices.What is 5G security in cyber security?
5G technology potentially increasing the attack surface for malicious actors by introducing new vulnerabilities: The implementation of untrusted components into a 5G network could expose communications infrastructure to malicious or poorly developed hardware and software, and could significantly increases the risk of
What are the cyberattacks of 5G?
Cyber-Attacks: 5G networks will be exposed to various cyber threats, including Distributed Denial of Service (DDoS) attacks, potential data breaches, and ransomware.
The higher data speeds and lower latency provide cybercriminals with new opportunities to launch sophisticated attacks.3 oct. 2023With its low latency, higher bandwidth, and extensive security measures, 5G strengthens the security of cloud connectivity.
This upgrade enables secure and reliable transmission of sensitive information as well as real-time data processing.
|
Enisa
5G CYBERSECURITY STANDARDS. March 2022. 1. ABOUT ENISA. The European Union Agency for Cybersecurity ENISA |
|
COMMISSION RECOMMENDATION (EU) 2019/ 534 - of 26 March
29 mars 2019 As a result ensuring the cybersecurity of 5G networks is an issue of strategic importance for the Union |
|
5G Cybersecurity: Preparing a Secure Evolution to 5G
Cellular networks will be transitioning from 4G to 5G and 5G networks will provide increased cybersecurity protections. This project will identify several 5G |
|
EUROPEAN COMMISSION Brussels 29.1.2020 COM(2020) 50 final
29 janv. 2020 As a result ensuring the cybersecurity of 5G networks is an issue of strategic importance for the Union |
|
Cisco-5g-cybersecurity-guidance.pdf
High-level insights regarding 5G cybersecurity risks to an operator's core network infrastructure and presents six key recommendations for strengthening 5G |
|
5G CYBERSECURITY
26 March 2019 - Commission Recommendation on the cybersecurity of 5G networks. July 2019 - Member States national risk assessments. |
|
Cybersecurity of 5G networks EU Toolbox of risk mitigating measures
The objectives of this toolbox are to identify a possible common set of measures which are able to mitigate the main cybersecurity risks of 5G networks as they |
|
Enisa
7 juin 2021 A CANDIDATE EU 5G CYBERSECURITY. CERTIFICATION SCHEME. INTRODUCTION. The European Union Agency for Cybersecurity ENISA |
|
The EU coordinated approach to 5G cybersecurity
to 5G cybersecurity. CEN-CENELEC – ETSI – ENISA conference on standardisation- Panel 5 4 February 2021. Julie Ruff |
|
EU coordinated risk assessment of the cybersecurity of 5G networks
9 oct. 2019 Key technological novelties of 5G networks. ? 5G ecosystem and deployment in the EU. 2. EU assessment of 5G cybersecurity risks. |
|
Cybersecurity - Inria
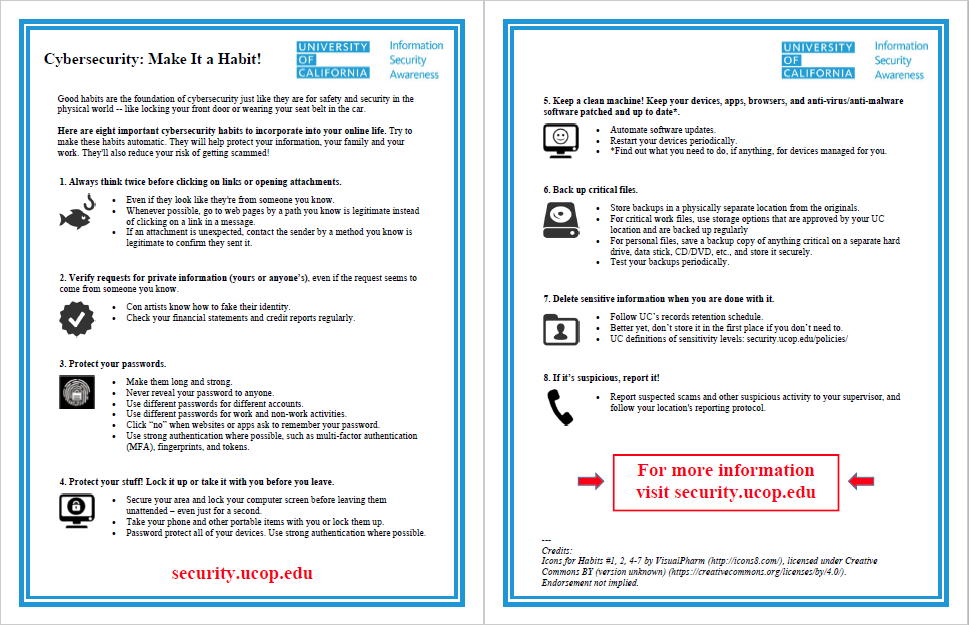
Wikipedia defines cybersecurity as “the protection of computer systems key security properties, as well as some legal (e g cybersecurity regulation) and |
|
Cybersecurity 101 - Broadway Bank
Cybersecurity is the protection of computers and computer systems against unauthorized attacks or intrusion Page 2 CYBER INCIDENT RESPONSE Take |
|
CYBERSECURITY - JRC Publications Repository - EUROPA
A cybersecurity conceptual model 56 5 2 Evolution of the cyber threat landscape 58 5 2 1 Threat actors 58 5 2 2 Financial motivations behind cybercrime 60 |
|
Cybersecurity for Small Business
Knowing some cybersecurity basics and putting them in practice will help you protect your business and reduce the risk of a cyber attack PROTECT YOUR FILES |
|
Cyber Security Planning Guide - Federal Communications
Businesses large and small need to do more to protect against growing cyber threats As larger companies take steps to secure their systems, less secure small |
|
Cours du cursus Cybersecurity - NetAcad
Introduction to Cybersecurity Cybersecurity Essentials Présentation du cours Traite des tendances en matière de cybersécurité, des menaces et des solutions |
|
Guide to Developing a Cyber Security and Risk - Cooperativecom
The Cooperative Research Network (CRN) is the technology research arm of NRECA ©Guide to Developing a Cyber Security and Risk Mitigation Plan Copyright |
|
Cybersecurity - Inter-American Development Bank
regarding cybersecurity in Latin America and the Caribbean Cybersecurity policy and strategy; ii) Cyber culture and society; iii) Cybersecurity education, |
|
2020 Cybersecurity Report: Risks, Progress, and the Way Forward
As of the beginning of 2020, only 12 countries had approved a national cybersecurity strategy (which can be deemed an accomplishment, considering that only |
|
CYBERSECURITY ECOSYSTEM - ITU
CYBERSECURITY ECOSYSTEM Prof Oleksandr POTII Dependability and Resilience at the Cyber Security Centre, De Montfort University |


![PDF] A Leader s Guide to Cybersecurity: Why Boards Need to Lead--and PDF] A Leader s Guide to Cybersecurity: Why Boards Need to Lead--and](https://www.zdnet.com/a/hub/i/r/2020/02/26/da0f388c-caf0-449c-b31e-8d5b1c9f5a25/resize/220x165/2099bd2d507afe5f54b2346cbb3e1764/sf-cybersecurity-2020-thumb.jpg)


![PDF] Machine Learning for Cybersecurity Cookbook by Emmanuel PDF] Machine Learning for Cybersecurity Cookbook by Emmanuel](https://www.cob.nl/wp-content/uploads/2020/02/null.jpeg)





![cyber security engineering book [PDF] - Programmer Books cyber security engineering book [PDF] - Programmer Books](https://www.hisa.org.au/wp-content/uploads/2019/04/cybersecurity-229x300.jpg)




![PDF] Cybersecurity Program Development for Business: The Essential P PDF] Cybersecurity Program Development for Business: The Essential P](https://storage.googleapis.com/ldo3-files-prod/uploads/asset/cover/2106/thumb_original_PDF_Carbon_Black_Research_Report_BeyondtheHype.png)


![Kindle] Cybersecurity Law Download PDF read Online: book download Kindle] Cybersecurity Law Download PDF read Online: book download](https://inxo-bizlive-enterprise-rep.s3.amazonaws.com/24695-b2tzWqeyIT/att_how_to_manage_cyber_risks_during_digital_transformation.pdf_1.jpg)
