system hacking in ethical hacking pdf
|
CEH-brochure.pdf
Bug bounty researchers are expert ethical hackers who use their attack skills to uncover vulnerabilities in the systems. The World's No. 1. Ethical Hacking. |
|
Gray Hat Hacking The Ethical Hackers Handbook
٢٦ ذو القعدة ١٤٢٨ هـ ... pdf. “How C Programming Works” (Marshall Brain) computer.howstuffworks ... system interrupt signal to the processor. The common interrupt you ... |
|
CEH: Certified Ethical Hacker Study Guide
An ethical hacker should know the penalties of unauthorized hacking into a system. No ethical hacking activities associated with a network-penetration test |
|
EN-Ethical Hacking.pdf
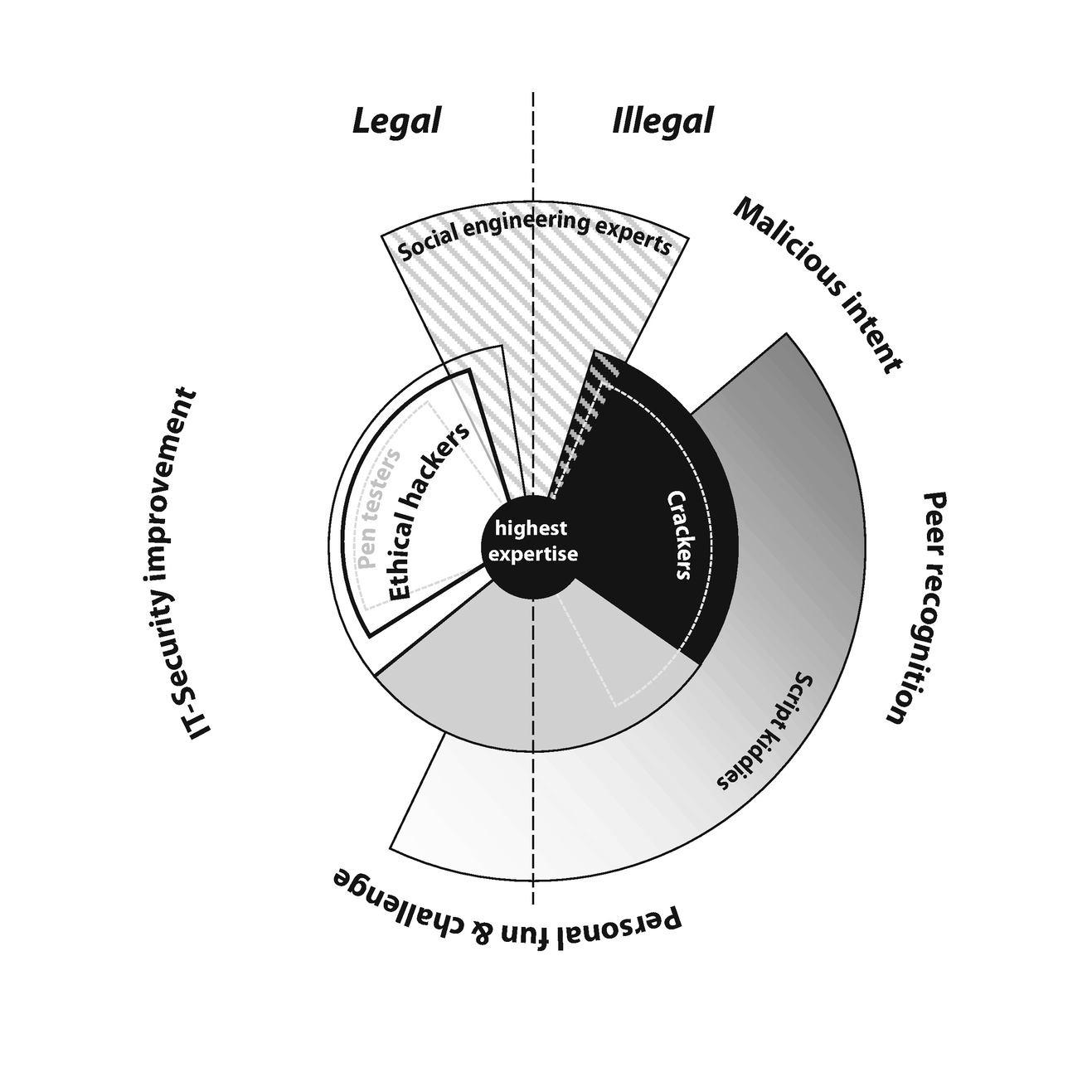
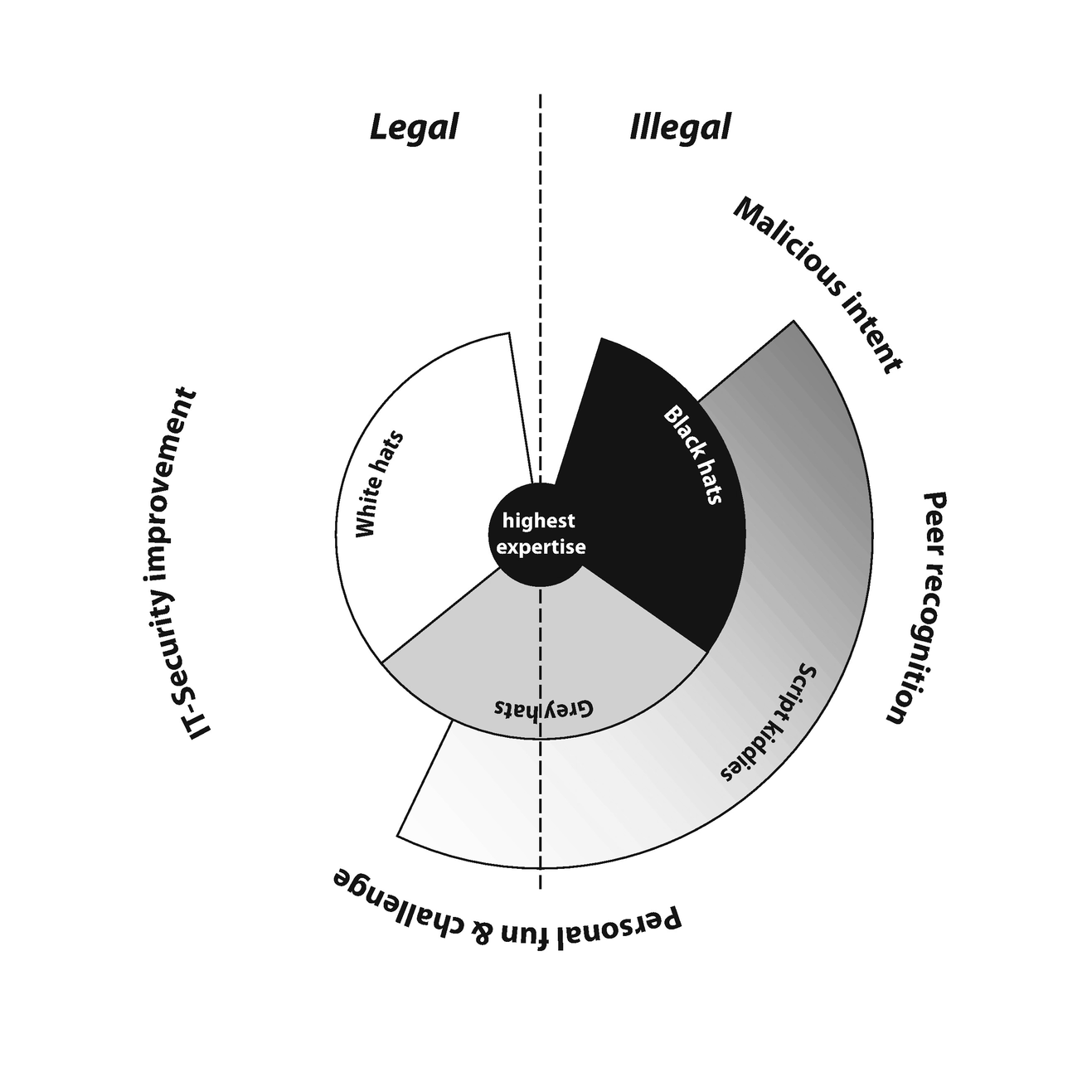
skills for offensive purposes. ◉ The term 'ethical hacker' refers to security professionals who apply their hacking skills for defensive purposes. |
|
Ethical Hacking and Countermeasures
The best ethical hacker candidates will have successfully mastered hacking tools and their exploits. What do Ethical Hackers do? An ethical hacker's evaluation |
|
Untitled
Unlike malicious hackers and actors Certified Ethical Hackers operate with permission from the system owners and take Hacker (CEH) credential is the most ... |
|
AN EMPIRICAL ANALYSIS OF ETHICAL HACKING
١٣ رمضان ١٤٤٤ هـ and the hacking stages that ethical hackers pursue to protect a network or system. ... pdf.”. 9. R. Slayton “Certifying 'Ethical Hackers |
|
Attacker acquires information through techniques such as foot
Footprinting eases the process of system hacking by revealing its vulnerabilities. This is a procedure for The Ethical Hacker's Guide To System Hacking. |
|
Faculty Attitudes Toward Teaching Ethical Hacking to Computer and
This paper deals with faculty attitudes toward teaching ethical hacking to Computer and Information Systems pdf. Ryan J. |
|
EC-Council
Whether you are a beginner or an experienced ethical hacker the Web Application Hacking and Security course Please read the Host System Requirement and ... |
|
CEH: Certified Ethical Hacker Study Guide
Entire Book in PDF. SERIOUS SKILLS. Exam 312-50. Exam EC0-350. Y GUIDE. Graves. 312-50. EC0-350. CEH™. C ertifi ed Ethical Hacker |
|
Faculty Attitudes Toward Teaching Ethical Hacking to Computer and
Computer and Information Systems Undergraduates Students computer security programs as the ethics of teaching hacking as an ongoing professional ... |
|
History & Impact of Hacking: Final Paper - HistoryOfComputing
6 ?.?. 2549 The white hats the "ethical hackers" |
|
CERTIFIED ETHICAL HACKER V10 CERTIFIED ETHICAL HACKER
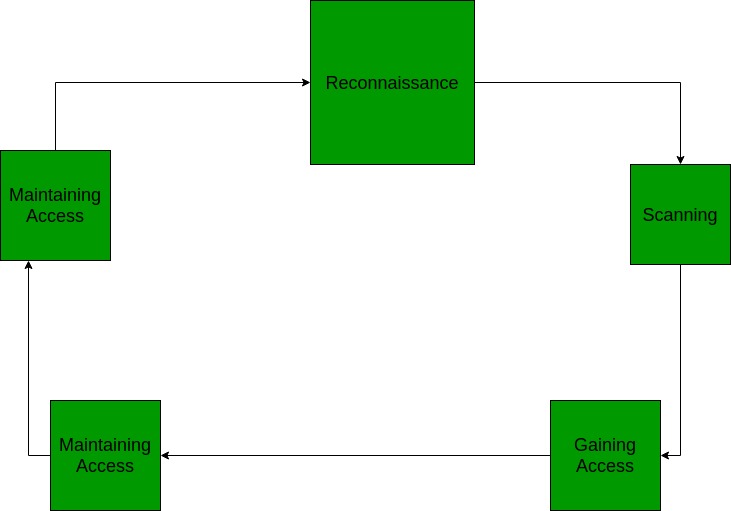
test hack and secure target systems. The course covers the Five Phases of Ethical. Hacking |
|
HACKING INTO COMPUTER SYSTEMS A Beginners Guide
GUIDE TO (mostly) HARMLESS HACKING. Beginners' Series #1. So you want to be a harmless hacker? "You mean you can hack without breaking the law?" That was the |
|
Ethical Hacking And Countermeasures.pdf
The goal of the ethical hacker is to help the organization take preemptive measures against mali- cious attacks by attacking the system himself; |
|
CEH Exam Blueprint v4.0
Introduction to Ethical. Hacking. • Information Security Overview. • Cyber Kill Chain Concepts System. Hacking Phases and Attack. Techniques. |
|
Ethical Hacking and the Legal System
The crux is that ethical and unethical hackers carry out basically the same activities only with different intentions. If the ethical hacker does not identify |
|
EN-Ethical Hacking.pdf
Lab Manual / Workbook The term 'ethical hacker' refers to security professionals ... Attack – An assault on system security that derives. |
|
The Ethical Hack: A Framework for Business Value Penetration
Component Parts of Information. Security Programs. Risk Assessment. Management System. Controls. Maintenance Plan. Risk Analysis and Ethical Hacking. |
|
Hacking 101 - OWASP Foundation
the web application hacker's handbook: finding and exploiting security flaws 2nd edition [Dafydd Stuttard Marcus Pinto] OWASP testing guide v4 free https://www owasp org/index php/OWASP_Testing_Project the hacker playbook 3: practical guide to penetration testing [Peter Kim] hacking: the art of exploitation [Jon Erickson] |
|
Ethical Hacking: Understanding the Basics - Cybersecurity Exchange
an ethical hacker and a malicious hacker and to understand what ethical hackers do Identifying Different Types of Hacking Technologies Many methods and tools exist for locating vulnerabilities running exploits and compromising systems Trojans backdoors sniffers rootkits exploits buffer overflows and SQL injection are |
|
Ethical Hacking as a Career - EC-Council
Enter the HackerverseTM With the CEH® v12Enhance Your Ethical Hacking Career 5 days of training 20 modules 3000+ pages of student manual 1900+ pages of lab manual Over 200 hands-on labs with competition flags Over 3500 hacking tools Learn how to hack multiple operating systems (Windows 11 Windows servers Linux Ubuntu Android) |
|
Chapter 1 Introduction to Ethical Hacking - Principle Logic
Ethical hacking is performed with the target’s permission The intent of ethical hacking is to discover vulnera-bilities from a hacker’s viewpoint so systems can be better secured It’s part of an overall information risk management program that allows for ongoing security improvements Ethical hacking can also ensure that vendors’ claims |
What is a ethical hacker?
Ethical hackers, on the other hand, are security experts retained by organizations to proactively identify vulnerabilities before someone with ill intent discovers them. Ethical hackers improve a company’s security by finding weaknesses and providing remediation advice.
What is the difference between ethical hacking and malicious hacking?
In the more commonly known illegal counterpart to ethical hacking, cybercriminals (also known as malicious hackers) seek vulnerabilities to exploit in an organization’s network. Ethical hackers, on the other hand, are security experts retained by organizations to proactively identify vulnerabilities before someone with ill intent discovers them.
What education do ethical hackers need?
Most ethical hackers also have a degree in a technology-related field, such as computer science, information technology, or cybersecurity. Beyond these basics, it’s important for ethical hackers to engage in ongoing education, as cybersecurity is continually evolving.
How does a hacking company work?
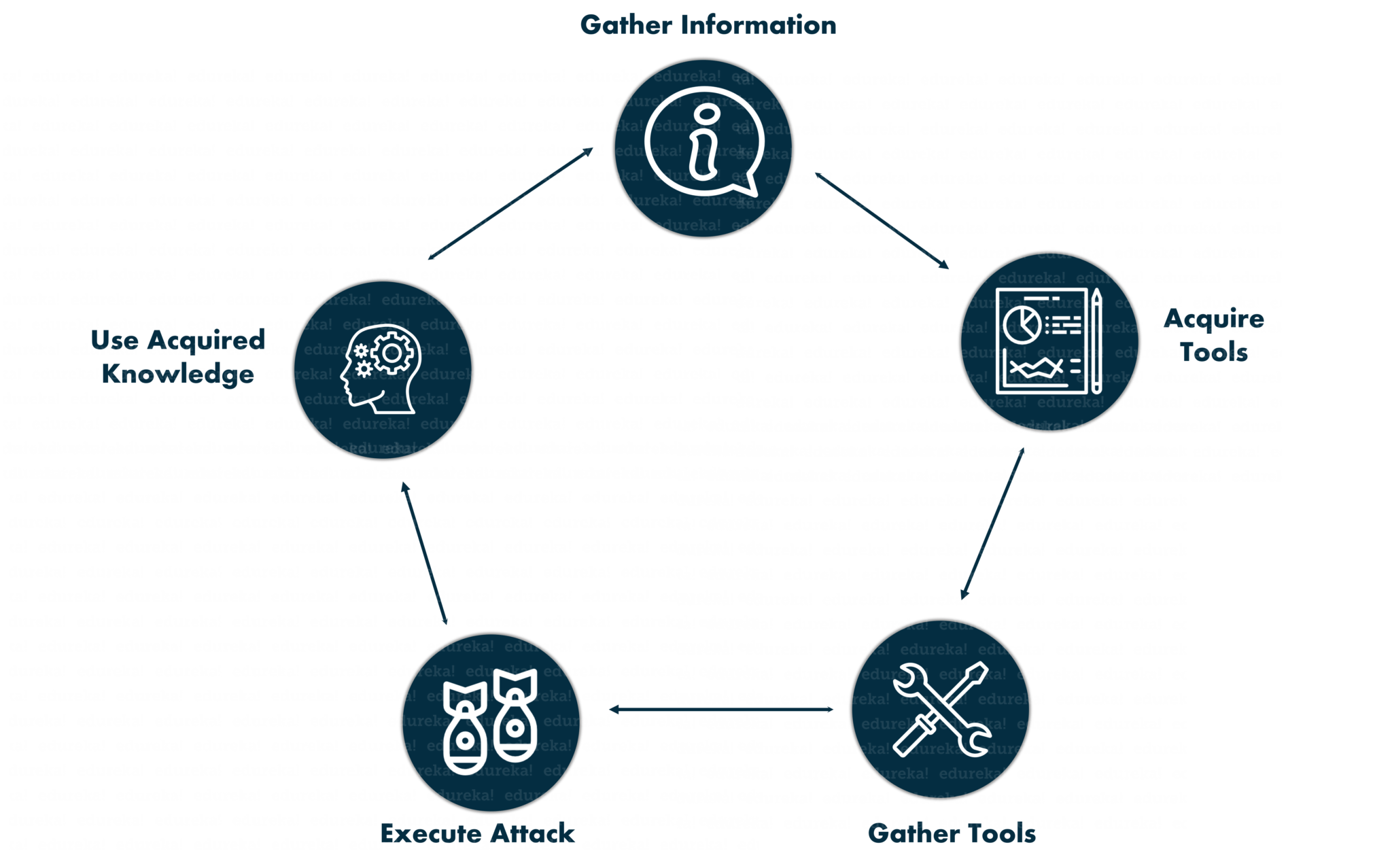
Upon receiving explicit and contractual consent from the organization, the reconnaissance portion of the hacking process can begin. This involves collecting as much information as possible about the “target” using the various tools at the hacker’s disposal, including the company website, internet research, and even social engineering.
|
Ethical Hacking and Countermeasures - AnonFiles
Version 6 Module VII System Hacking CEH Hacking Cycle Enumeration Features: • Decrypts PDF files protected with the owner passwords yp p p |
|
Ethical Hacking - Zenk - Security
Module I : Introduction to Ethical Hacking ◉ Module II: The term 'ethical hacker ' refers to security professionals who apply Attack – An assault on system security that derives from an Ask the student to read “Social Engineering-story pdf ” |
|
Hacking: Computer Hacking, Security Testing,Penetration - Pirate
This book provides great tips on how to become an ethical hacker for an organization that needs to fix any vulnerabilities in its systems The book is split into three |
|
Hacking Methodology
The process used for ethical hacking is basically the same as the one a mali- Your main task is to simulate the information gathering and system com- promises Use this search for PDF documents that might contain sensitive information |
|
Introduction to Ethical Hacking - Principle Logic, LLC
An ethical hacker possesses the skills, mindset, and tools of a hacker but is also trustworthy Ethical hack- ers perform the hacks as security tests for their systems |
|
CEH: Certified Ethical Hacker Study Guide - Bina Darma e-Journal
Entire Book in PDF SERIOUS SKILLS Exam 312-50 Exam EC0-350 Y GUIDE Graves 312-50 EC0-350 CEH™ C ertifi ed Ethical Hacker |
|
Ethical Hacking - EconStor
Chapter VI: Select Ethical-Hacking Incidences: Chaos Computer ized access to data or a computer system in pursuit of a cause or political ends 1 gov uscourts cand 242989/gov uscourts cand 242989 1 0 pdf Legislative provisions: |
|
Ethical Hacking - X-Files
Describe how hackers are able to defeat security controls in operating systems, networked environments and generally circumvent security mechanisms |
|
Hacker Techniques and Tools - Jones & Bartlett Learning
techniques and technologies that attackers use to compromise a system Differentiate between hacking, ethical hacking, penetration testing, and auditing (http://nvlpubs nist gov/nistpubs/Legacy/SP/nistspecialpublication800-115 pdf ) |
|
ETHICAL HACKING - Scinapse
Ethical Hacking which attempts to increase security protection by identifying and patching known security vulnerabilities on systems owned by other parties |















![Ethical Hacking Mod 5 System Hacking P [1\u00262] - YouTube Ethical Hacking Mod 5 System Hacking P [1\u00262] - YouTube](https://techviral.net/wp-content/uploads/2018/09/The-Practical-Guide-to-Become-a-Hacker.jpg)