tcp/ip vulnerabilities
|
Lecture 16: TCP/IP Vulnerabilities and DoS Attacks: IP Spoofing
Lecture 16: TCP/IP Vulnerabilities and DoS Attacks: IP Spoofing SYN Flooding |
|
AMNESIA:33 How TCP/IP Stacks Breed Critical Vulnerabilities in IoT
3 jui. 2000 This means that some vulnerabilities in a TCP/IP stack allow for a device to be exploited even when it simply sits on a network without running ... |
|
Security Advisory: NuttX TCP/IP vulnerabilities – AMNESIA:33
8 déc. 2020 TagMaster PSIRT. Initial public release. Security Advisory: NuttX TCP/IP vulnerabilities – AMNESIA:33. Overview. Initial release date. |
|
Eaton-security-bulletin-treck-tcp-ip-stack-vulnerabilities-ripple20.pdf
23 jui. 2020 vulnerabilities affecting Treck Inc.'s TCP/IP stack which is used in some Eaton products to implement IPv4. IPv6 |
|
Multiple vulnerabilities in TCP/IP function on MELSEC C Controller
14 fév. 2020 ?Overview. Multiple vulnerabilities were found in TCP/IP function (IPnet) of VxWorks version 6.5 and later a real-time OS distributed by. |
|
Advisory - Treck TCP/IP Vulnerabilities (Ripple20) affecting Ethernet
8 juil. 2020 Vulnerability (Ripple20) in Ethernet Communication Module XKM3000 L MED. Page 1. Treck TCP/IP Vulnerabilities (Ripple20) affecting Ethernet. |
|
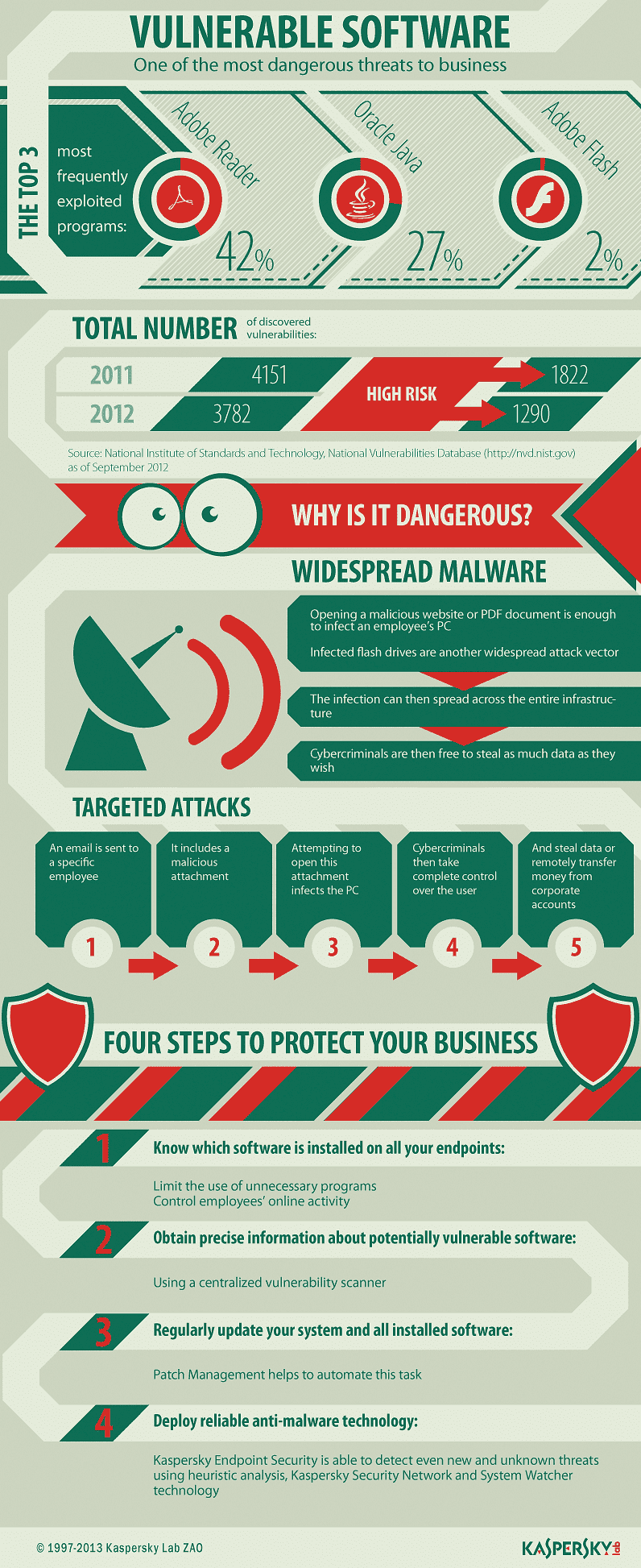
How Embedded TCP/IP Stacks Breed Critical Vulnerabilities
AMNESIA:33 - vulnerabilities on open-source TCP/IP stacks. • Analysis of TCP/IP stack vulnerabilities o Affected components o Vulnerability types & Anti- |
|
SSA-044112: Multiple Vulnerabilities (NUCLEUS:13) in the TCP/IP
SSA-044112: Multiple Vulnerabilities (NUCLEUS:13) in the TCP/IP. Stack of Nucleus RTOS. Publication Date: 2021-11-09. Last Update: 2021-12-14. |
|
SSA-541017: Embedded TCP/IP Stack Vulnerabilities (AMNESIA:33
8 déc. 2020 Security researchers discovered and disclosed 33 vulnerabilities in several open-source TCP/IP stacks for embedded devices also known as ... |
|
FANUC
26 nov. 2020 ?Outline. There are multiple vulnerabilities in TCP/IP stack of FANUC CNC. If these vulnerabilities are exploited by malicious attackers ... |
|
Lecture 16: TCP/IP Vulnerabilities and DoS Attacks: IP
The TCP/IP protocol stack is most commonly conceived of as consisting of the following seven layers: 7 Application Layer (HTTP HTTPS FTP SMTP SSH SMB POP3 DNS NFS etc ) 6 Presentation Layer (MIME XDR) 5 Session Layer (TLS/SSL NetBIOS SOCKS RPC RMI etc ) 4 Transport Layer (TCP UDP etc ) 3 |
|
Attacks on TCP/IP Protocols - University of Tennessee at Chattanooga
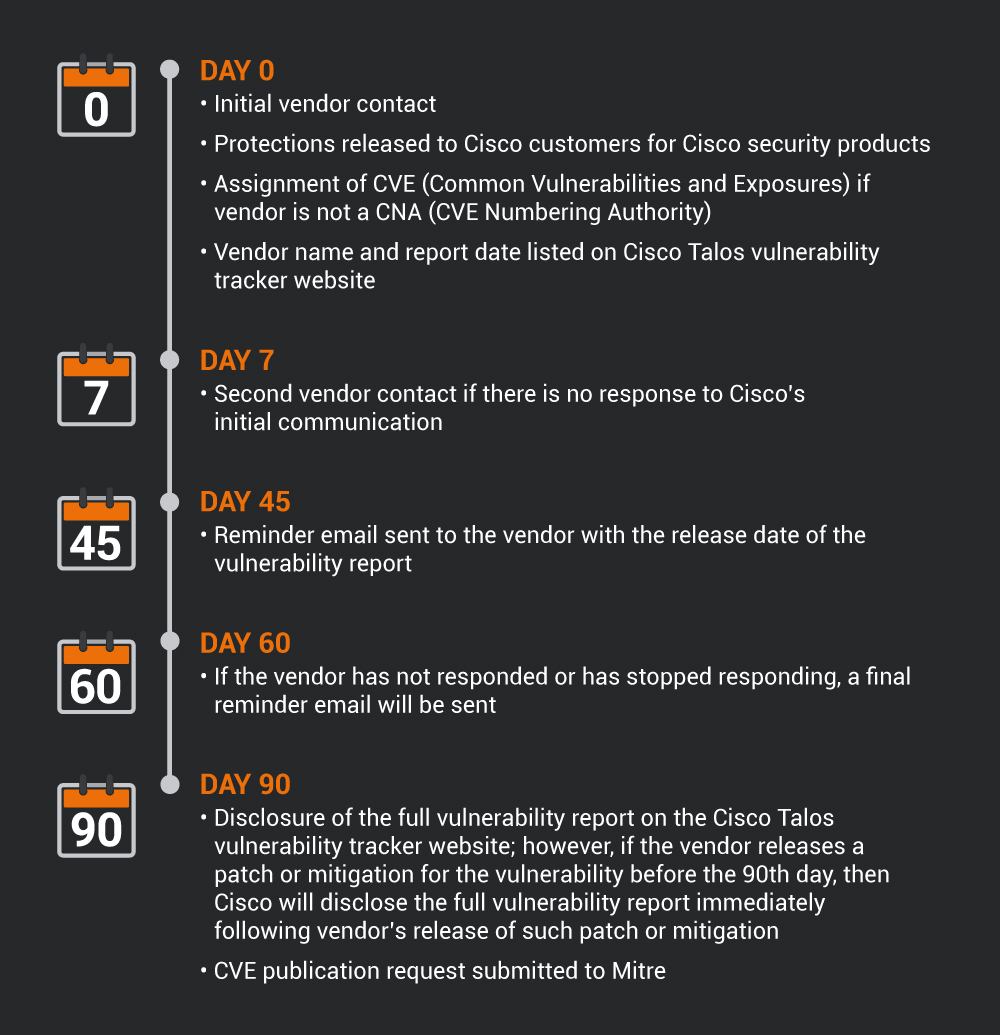
Executive Summary On December 8 2020 a report titled Amnesia:33 developed by Forescout disclosed multiple zero-day vulnerabilities in the TCP/IP stacks impacting numerous Operational Technology (OT) Internet of Things (IoT) Building Automation Systems and Information Technology (IT) devices |
|
Attacks on TCP/IP Protocols - University of Tennessee at
Attacks on TCP/IP Protocols CPSC4620: Computer Network Security Robbie Myers Abstract: TCP/IP protocols serve as the backbone of the Internet transmission structure As such an important component of this system their use is ubiquitous with any network system implemented |
|
Attack Lab: Attacks on TCP/IP Protocols
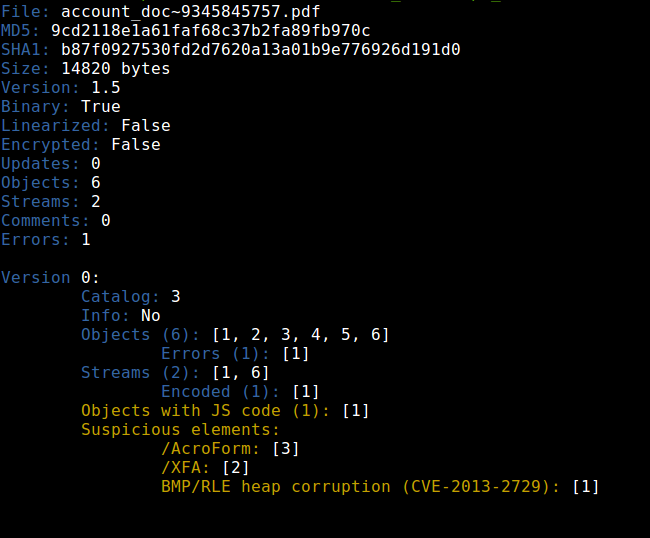
The vulnerabilities in the TCP/IPprotocols represent a special genre of vulnerabilities in protocol designs and implementations; they providean invaluable lesson as to why security should be designed in from the beginning rather than being added asan afterthought |
|
Security Problems in the TCP/IP Protocol Suite
The TCP/IP protocol suite which is very widely used today was developed under the sponsorship of the Department of Defense Despite that there are a number of serious security ?aws inherent in the protocols regardless of the correctness of any implementations |
Are TCP/IP protocols secure?
When TCP/IP protocols were first being developed for communication over a network, security concerns were minimal for these protocols as access to the network itself was highly restricted.
What is TCP/IP and why is it important?
TCP/IP protocols serve as the backbone of the Internet transmission structure. As such an important component of this system, their use is ubiquitous with any network system implemented. Because of their fundamental importance and necessary usage, these protocols are a prime target for exploitive attacks and are used as the vector of an attack.
What is a TCP SYN flood attack?
The TCP SYN Flood Attack for Denial of Service IP Source Address Spoo?ng Attacks BCP 38 for Thwarting IP Address Spoo?ng for DoS Attacks Python and Perl Scripts for Mounting DoS Attacks with IPAddress Spoo?ng and SYN Flooding Troubleshooting Networks with the Netstat Utility
What is a less reliable version of TCP?
A less reliable version of TCP is UDP (User Datagram Protocol).Despite the pejorative sense associated with thephrase “less reliable”,UDP is extremely important to theworking of the internet, as you will discover in this and thenext lecture.
|
TCP/IP Vulnerabilities and DoS Attacks - College of Engineering
16 mar 2021 · Lecture 16: TCP/IP Vulnerabilities and DoS Attacks: IP Spoofing, SYN Flooding, and The Shrew DoS Attack Lecture Notes on “Computer and |
|
How TCP/IP Stacks Breed Critical Vulnerabilities in IoT - Black Hat
This means that some vulnerabilities in a TCP/IP stack allow for a device to be exploited, even when it simply sits on a network without running a specific |
|
25C3 TCP Vulnerabilities - Recurity Labs
Robustness vs attacks from within ▫ The TCP/IP protocol-suite focuses on robustness but fails to specify security-mechanisms to counter attacks on availability |
|
TCP/IP and its Weaknesses and Vulnerabilities
SYN Flooding is a Denial of Service (DOS) attack that exploits a “feature” in the TCP/IP protocol stack (a layer 4 attack) ✍ Allows attacker to deny access to any |
|
Security Problems in the TCP/IP Protocol Suite
Serious security flaws inherent the TCP/IP protocol, regardless of its implementation ▫ Major causes of vulnerabilities □ Rely on IP source address for |
|
Attacks on TCP/IP Protocols - UTC
ICMP which can impact the TCP/IP connections themselves In the case of ICMP, vulnerabilities persist due to some 'Request for Comments' (RFC) |
|
1 Network Protocols and Vulnerabilities Outline Internet
Find IP address TCP Protocol Stack Application Transport Network Link Application protocol TCP protocol IP protocol Data Link IP Network Access |
|
Just how secure is the TCP/IP protocol? - EBU-Tech
Wrapping up packets Web Data HTTP Header TCP Header IP Header TCP/ IP is not to blame for many computer security Scanning for vulnerabilities |
|
Microsoft TCP/IP Vulnerabilities - Boston Scientific
9 mar 2021 · Two vulnerabilities are Remote Code Execution (RCE) vulnerabilities identified in the Windows TCP/IP implementation The other vulnerability |


![Cryptographic Design Vulnerabilities [PDF] - Schneier on Security Cryptographic Design Vulnerabilities [PDF] - Schneier on Security](https://nakedsecurity.sophos.com/wp-content/uploads/sites/2/2012/07/pdf-malware-thumb.jpg?w\u003d250)






![PDF] Download I Might Regret This: Essays Drawings Vulnerabilities PDF] Download I Might Regret This: Essays Drawings Vulnerabilities](https://s3.amazonaws.com/downloads.ithemes.com/public/Infographics/Top+5+WordPress+Security+Vulnerabilities.png)






![PDF] Security Vulnerabilities of Mobile Devices free tutorial for PDF] Security Vulnerabilities of Mobile Devices free tutorial for](https://blog.semmle.com/static/f9ec64f04128b94f77d0527108fe0622/5c646/pacman-image.png)








![PDF] Download I Might Regret This: Essays Drawings Vulnerabilities PDF] Download I Might Regret This: Essays Drawings Vulnerabilities](https://mms.businesswire.com/media/20210209005461/en/858053/5/All_That_We_Let_In_REV.07_-_Infographics_Only_-_LG%281%29.jpg)