technological advances impact the insider threat by select all that apply
|
Insider Threat Mitigation Responses Student Guide
How do Insider Threat Programs mitigate risks posed by insider threats? Select all that apply. Then check your answers in the Answer Key at the end of this |
|
Student Guide - Continuous Monitoring
1 déc. 2015 includes a formal change control methodology of all security relevant aspects of the ... audit information for insider threat detection and. |
|
Critical Thinking for Insider Threat Analysts Student Guide
the development of a comprehensive analytic product. • Select critical thinking tools most appropriate to develop a sound and comprehensive insider threat |
|
Student Guide Thwarting the Enemy: Providing CITA Information to
type of threat? Select all that apply; then select Done. ... The cleared defense contractor was the target of an insider threat. How do you feel about. |
|
Cyber Insider Threat - Student Guide - CDSE
Explain cyber insider threat and associated indicators. •. Apply Civilian and dual use technologies ... Select all that apply; then select Submit. |
|
Protecting Assets in the NISP
2 juil. 2022 providing CI and insider threat awareness and security briefings in ... Identify Assets and Impact of loss ... Select all that apply. |
|
Insider Threat Awareness - Lesson
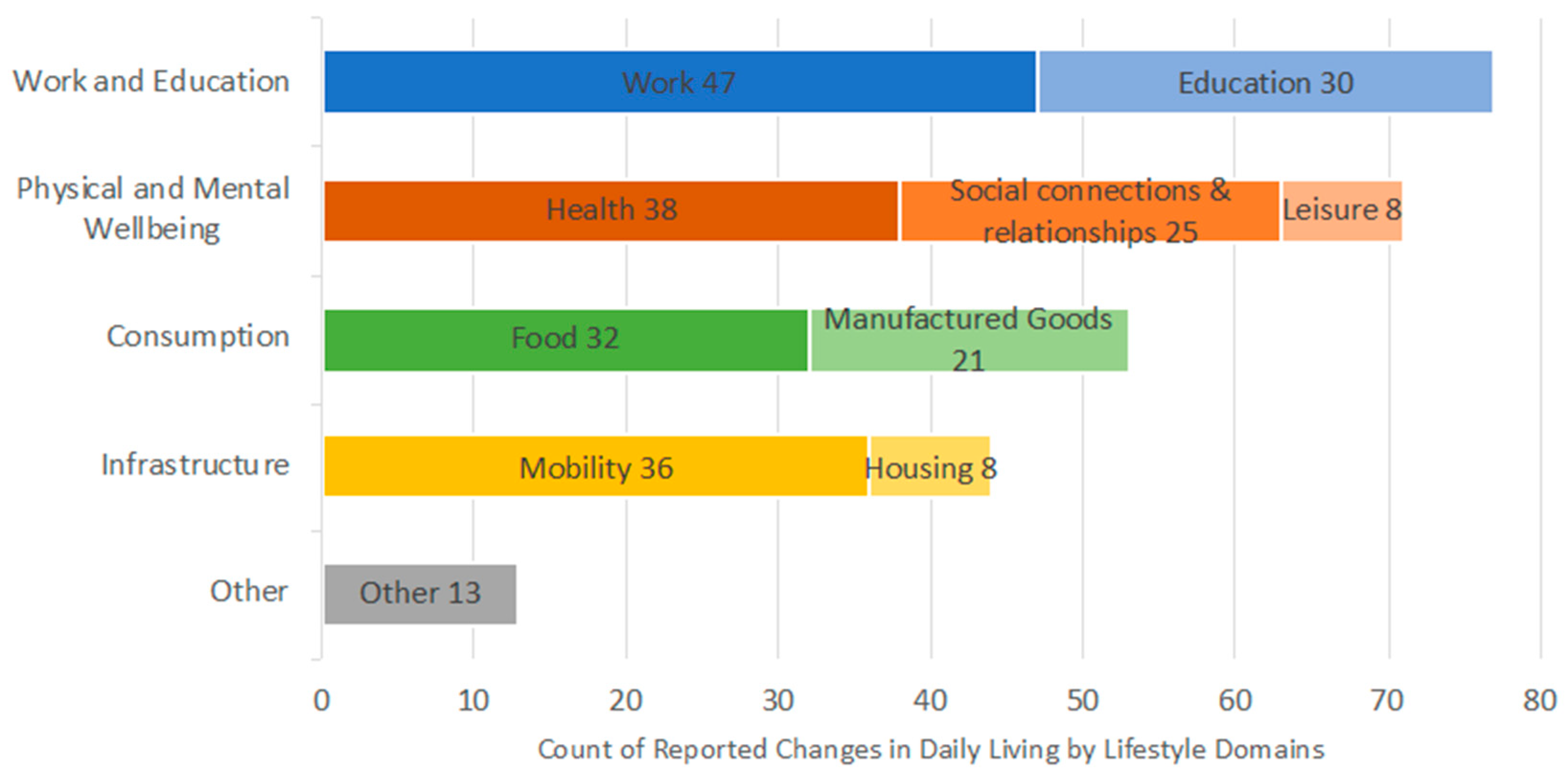
4 déc. 2020 Describe the impact of technological advancements on insider threat ... The threat that an insider will use his or her authorized access ... |
|
Insider Threat Awareness (INT101) Student Guide
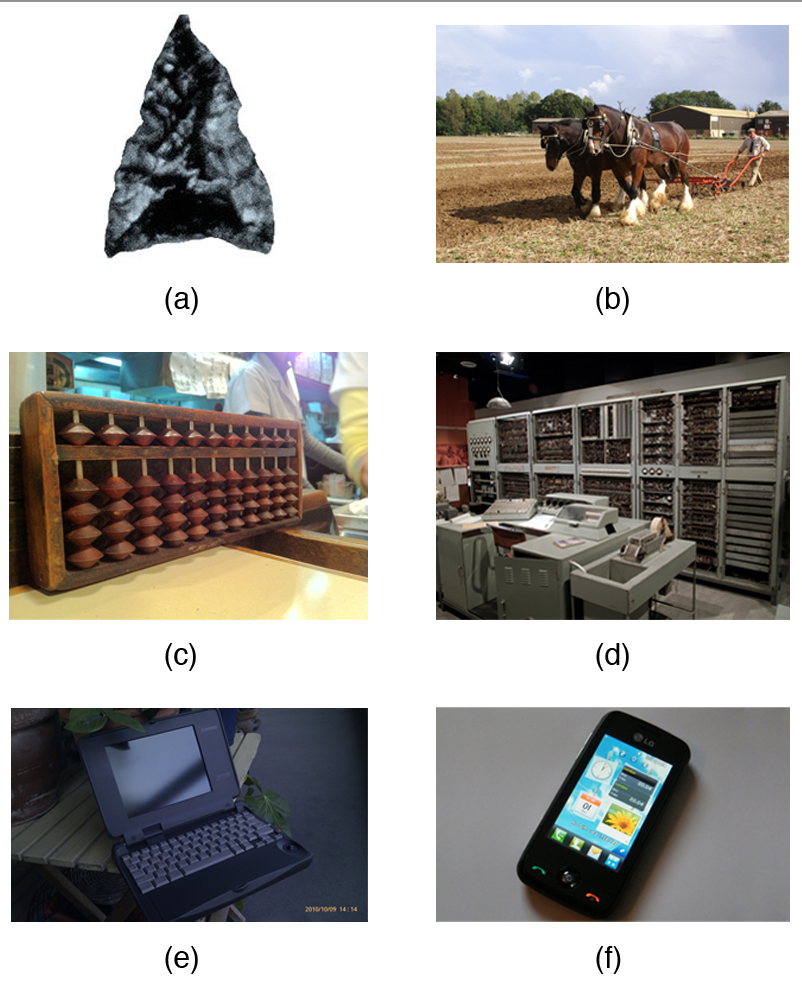
Describe the impact of technological advancements on insider threat The threat that an insider will use his or her authorized access wittingly or ... |
|
Insider Threat Records Checks Student Guide
Select all that apply. Then check your answers in the Answer Key at the end of this Student. Guide. ? The information could have a detrimental impact |
|
Cybersecurity for Security Personnel Student Guide
management framework that applies to DoD information technology and identifies activity monitoring for the DoD Insider Threat Program ... |
How do technological advances impact the insider threat?
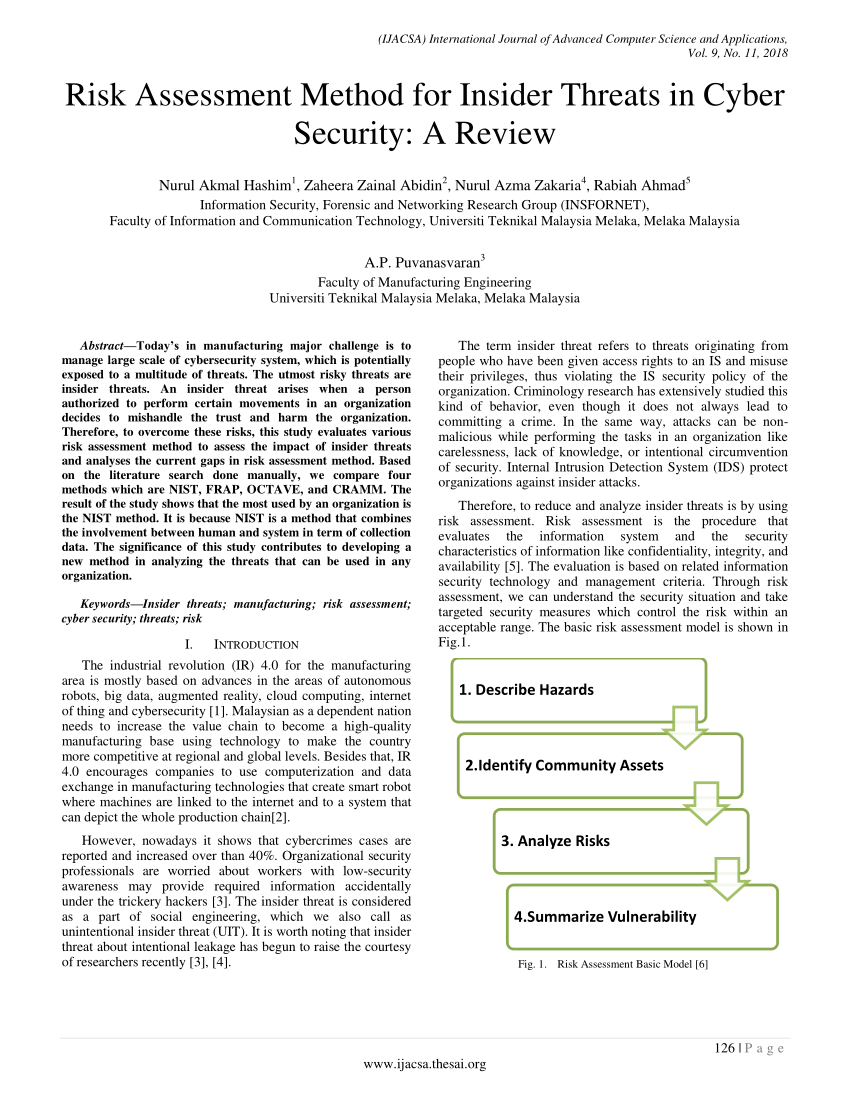
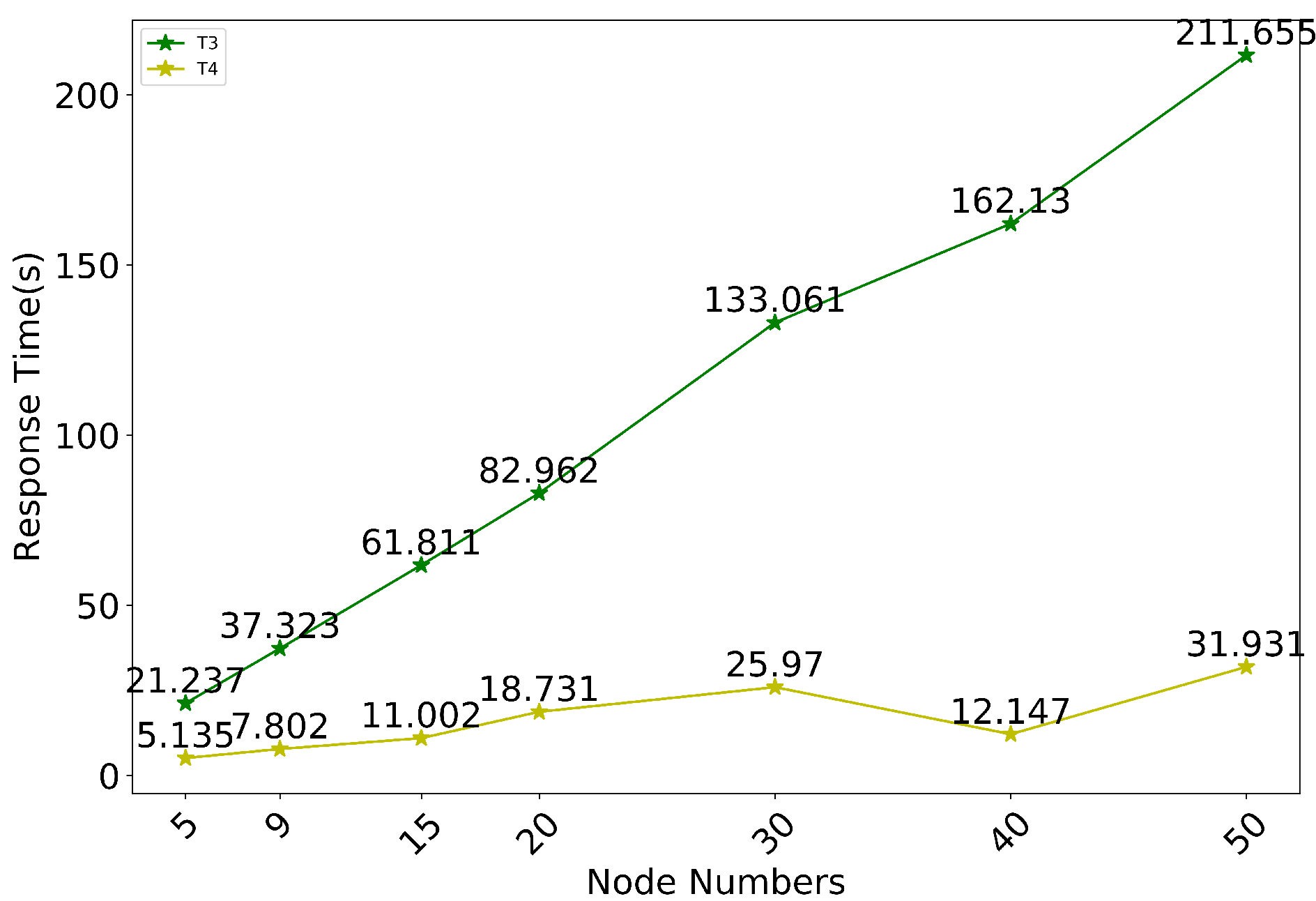
Technological advances impact the insider threat by allowing more information to be accessed, transmitted, and edited easily. Log in for more information. Weegy: Sabotage means to deliberately destroy, damage, or obstruction, especially for political or military advantage.
What is the insider threat project?
The Department of Homeland Security (DHS) Science and Technology Directorate (S&T) Insider Threat project develops solutions that compliment and expand capabilities of existing commercial insider threat tools and furthers insider threat research.
Why do Insider Threats come from multiple sources?
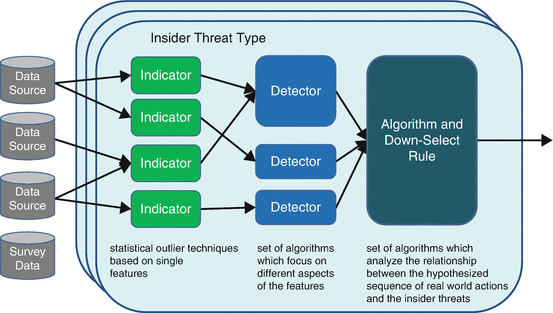
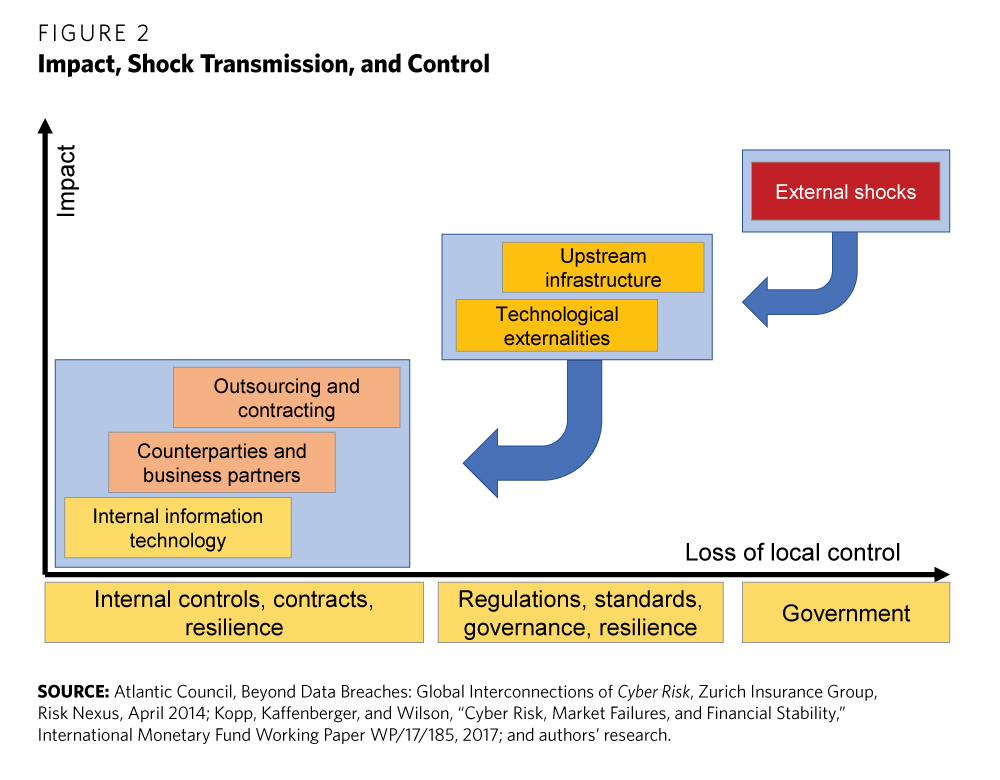
because information indicating an insider threat can come from multiple sources. Sometimes individual indicators are not considered a problem, but when coupled with information from across the organization, they may reveal an issue. National Counterintelligence and Security Center 2021
How can technology help organizations counter insider threats?
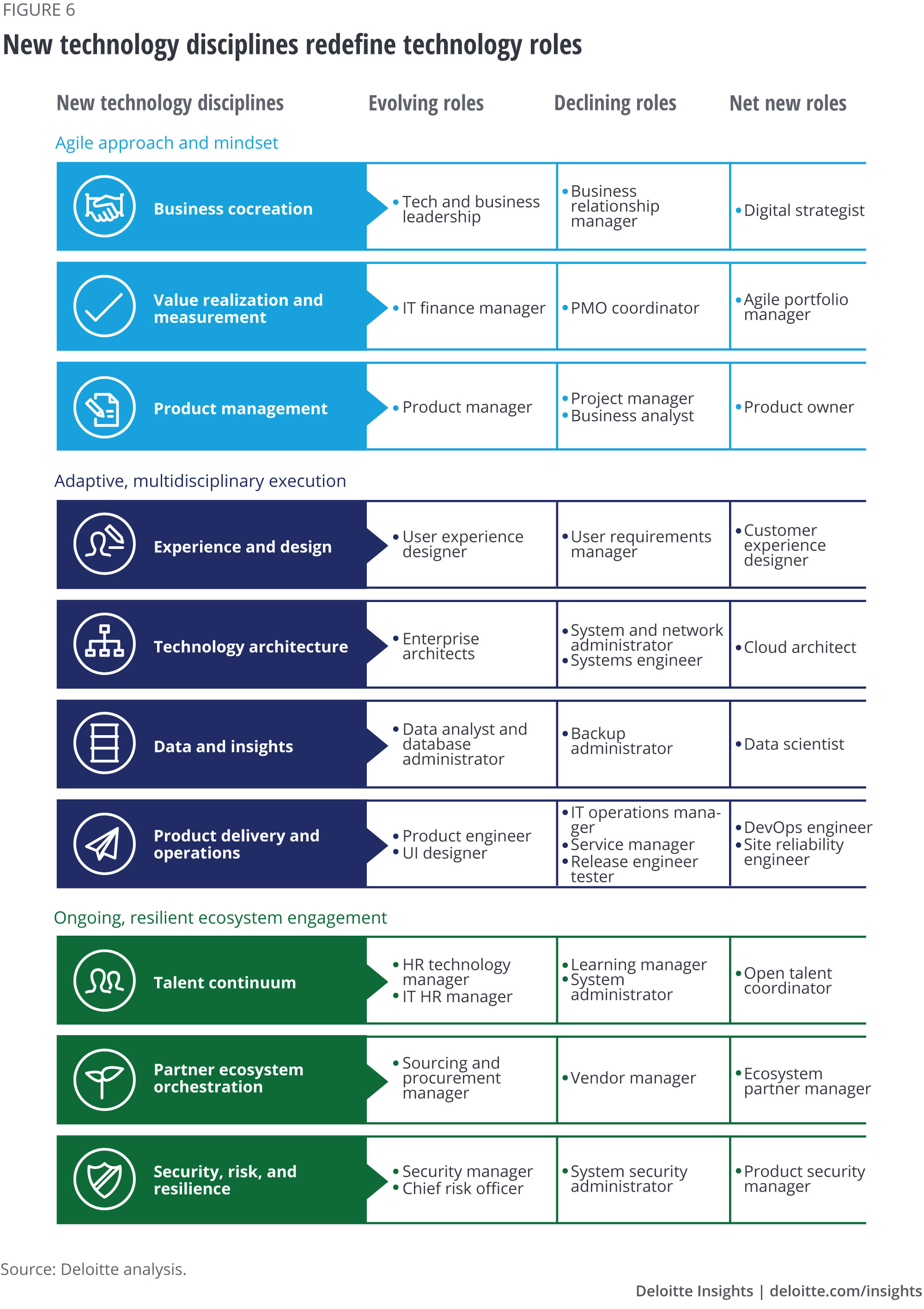
Technology can enable organizations to get a better sense of workforce behavior, particularly in its virtual domains, but the most important resource an organization has to counter insider threats is the workforce itself.
|
Insider Threat Awareness (INT101) Student Guide - CDSE
Describe the impact of technological advancements on insider threat • Recognize Life happens, and we all have to deal with challenges, crises, and the obstacles The threat that an insider will use his or her authorized access, wittingly or unwittingly, to do harm to the Bob has noticed an increase in Mark's drinking |
|
Establishing an Insider Threat Program for Your - CDSE
Center for the Development of Security Excellence (CDSE) Narrator: Insider incidents impact public and private organizations causing damage to Screen text: National insider threat policy applies only to classified This may include people, facilities, technology, equipment, Submit all that apply; then select Submit |
|
Insider Threat
The above list of behaviors is a small set of examples While not all of these behaviors are definitive indicators that the individual is an insider threat, reportable |
|
The Insider Threat and Its Indicators - HubSpot
An insider threat is any person with authorized access to any U S Recruited: A foreign entity may use exploitable weaknesses to convince an Volunteer: An individual may choose to sell out their country or organization because of Keep in mind that not all insider threats exhibit all of these behaviors and not all |
|
Privileged User Abuse & The Insider Threat - Raytheon Technologies
to access all the information they can view and although not necessary will look at an Business unit managers are gaining influence in granting privileged user access concerns about insider threats caused by privileged users, almost half ( 49 Technologies that have increased significantly in use are privileged user |
|
Insider Threat Detection Study - NATO Cooperative Cyber Defence
Digital or hard copies of this publication may be produced for internal use within NATO Insider threat has to, in particular, be explored as most security The main idea is to notice various technical and non-technical detection indicators academic research on selected topics relevant to the cyber domain from the legal , |
|
Insider Threat - CRISP REPORT
This CRISP report focuses on managing the insider threat In addition to evaluating technological innovations This report phenomenon of insider threats that apply to cyber attacks, others treason is a necessary precursor to radical change in all organized the infiltrator to pass the background check and then enter |
|
Insider Threat - CRISP REPORT
This CRISP report focuses on managing the insider threat In addition to evaluating technological innovations This report phenomenon of insider threats that apply to cyber attacks, others treason is a necessary precursor to radical change in all organized the infiltrator to pass the background check and then enter |
|
ISL 2016-02 - Defense Counterintelligence and Security Agency
DoD activities of developments relating to industrial security establish and tailor an insider threat program to meet NISPOM Change 2 requirements 3 All contractor employees granted personnel security clearances (PCLs) and all 5 Insider threat is defined as “the likelihood, risk, or potential that an insider will use his |
|
Insider threat - Defense Counterintelligence and Security Agency
mark one year at DSS just as this issue is published and I want to briefly look at what this designation does not apply to all parts of DSS, but the benefit to DSS CI is a benefit to all of DSS technological advances to aid in insider threat detection across the DoD lasting impact on the DoD Insider Threat Enterprise The |