three tier security checks definition
|
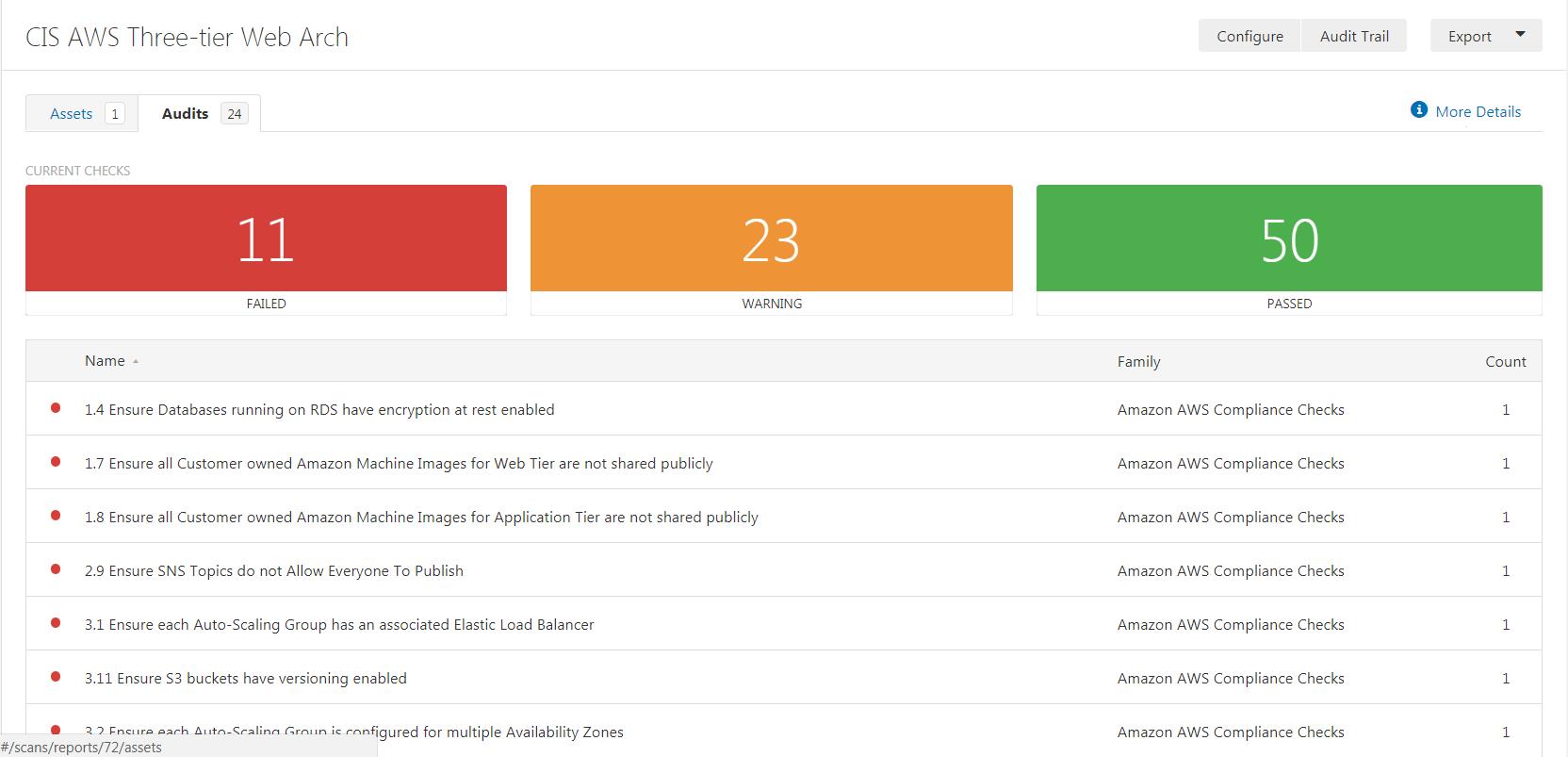
CIS Amazon Web Services Three-tier Web Architecture Benchmark
9 Nov 2016 follow security best practices as is defined within the ... Check if your application DB instances are configured to use the Data Tier Security. |
|
NIST SP 800-137 Information Security Continuous Monitoring
Tier 2 criteria for continuous monitoring of information security are defined by related information is used to determine security status at all three tiers. |
|
NIST SP 800-39 Managing Information Security Risk: Organization
Tier 1 risk management activities directly affect the activities carried out at Tiers 2 and 3. For example the missions and business functions defined at Tier |
|
AUTHORISED ECONOMIC OPERATOR (AEO) SCHEME
The security standards are detailed in World Customs Organ- isation Safe There is a three-tier programme for importers and exporters i.e.. AEO-T1 AEO ... |
|
PCI PIN Security Requirements v2.0
1 Dec 2014 ... three-tier physical security boundary as follows: • Level One ... 3 barrier must: • Have successfully completed a background security check. |
|
Securing Enterprise Web Applications at the Source: An Application
security checks in those modules. Special care should be taken to make sure three security-role elements namely employees |
|
Security Measures for polled EVM and VVPAT stored in Strong
Guarding of strong rooms:- There shall be a three tier guarding system for strong check the log book and videography and send a report to the DEO on the ... |
|
Security and Privacy Controls for Federal Information Systems and
23 Sept 2021 ... Three and the use of overlays described in Appendix I. It should ... Definition of Cloud Computing September 2011. APPENDIX A. PAGE A-10. Page ... |
|
NIST Special Publication 800-30 Revision 1 Guide for Conducting
Risk assessments can also inform other risk management activities across the three tiers that are not security-related. For example at Tier 1 |
|
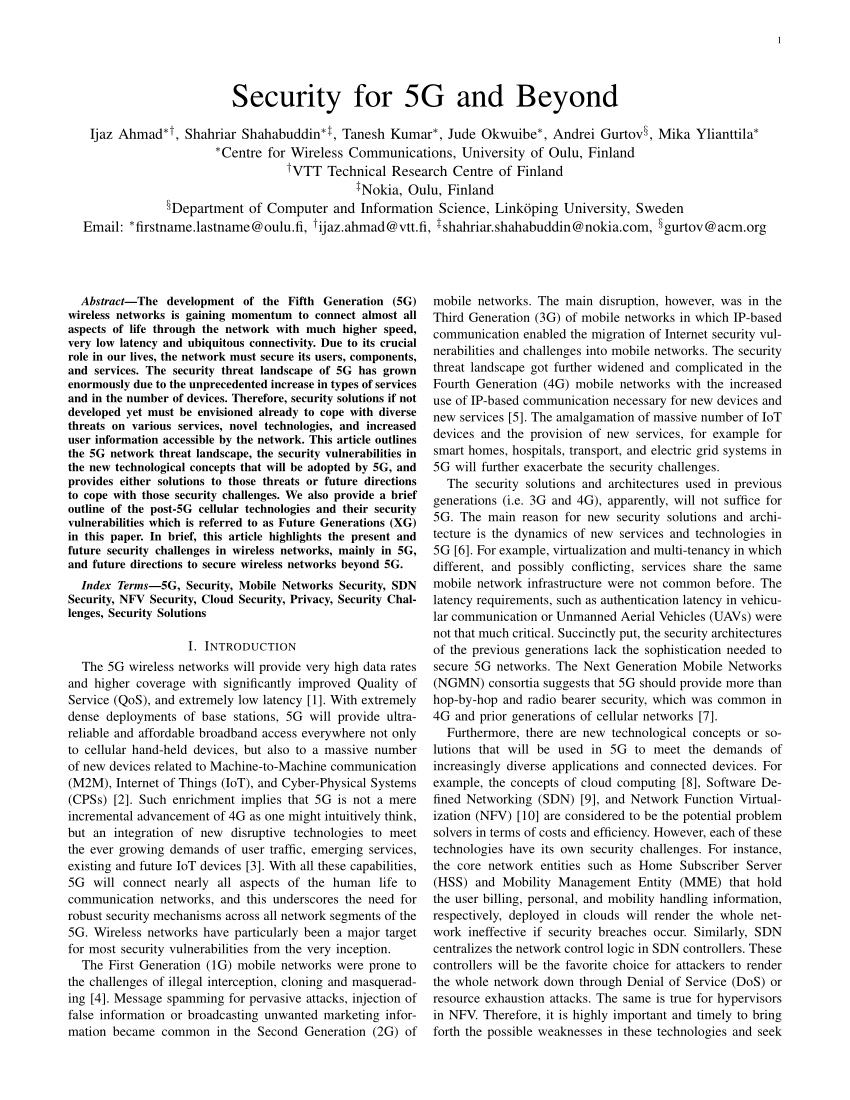
A Three-Tier Approach for Lightweight Data Security of Body Area
3 Nov 2021 Some studies focus only on this service under the assumption that confidentiality or access control is ensured by other means. Authentication ... |
|
CIS Amazon Web Services Three-tier Web Architecture Benchmark
09-Nov-2016 6.19 Create the Web tier Security Group and ensure it allows inbound connections from Web tier ELB Security Group for explicit ports ... |
|
NIST SP 800-137 Information Security Continuous Monitoring
Many of the technical security controls defined in NIST Special Publication Tier 1 is organization Tier 2 is mission/business processes |
|
The Protection of Civilians in United Nations Peacekeeping
and military capabilities available to the mission under the three tiers checks of individuals and units strategic and policy advice on security. |
|
NIST SP 800-39 Managing Information Security Risk: Organization
Tier 1 risk management activities directly affect the activities carried out at Tiers 2 and 3. For example the missions and business functions defined at Tier |
|
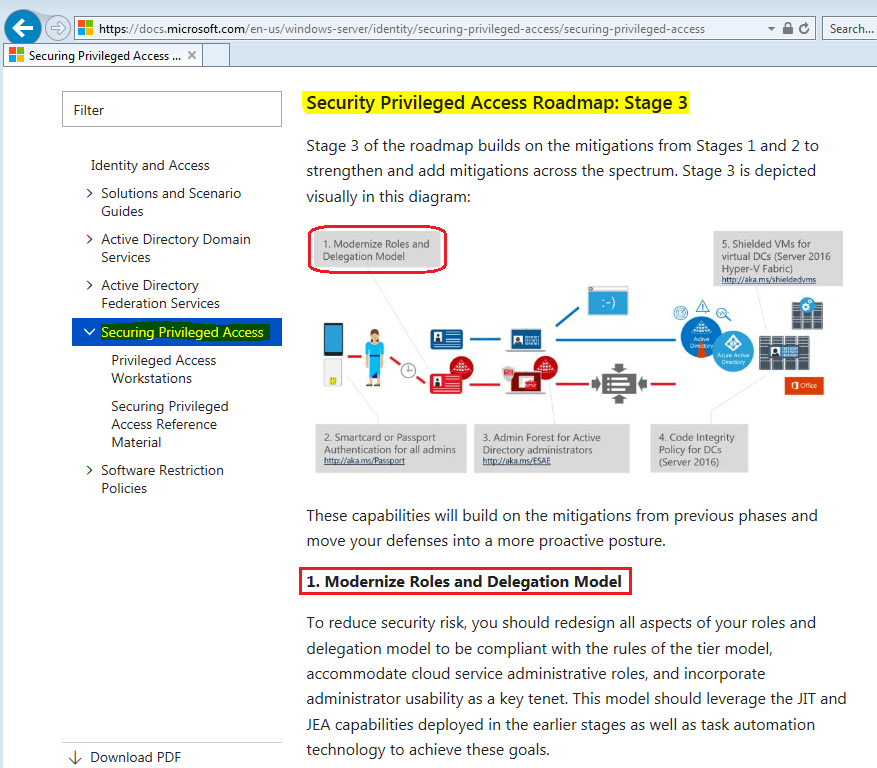
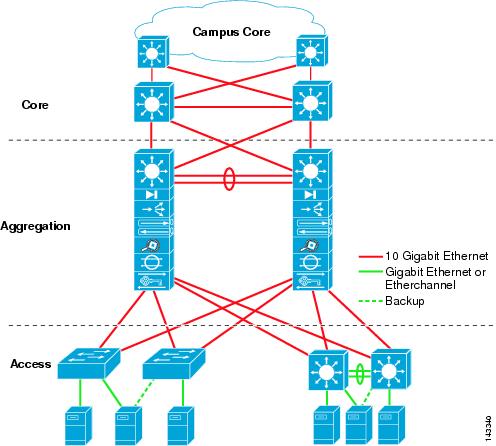
SECURING THREE-TIER SYSTEMS WITH ORACLE8I
Although security is one of the reasons for moving to a three-tier architecture for the database must enforce some means for managing user access ... |
|
SAP HANA Security Guide
24-Jan-2018 SAP HANA can be used as a relational database in a classic 3-tier ... It is recommended security practice to have a well-defined network ... |
|
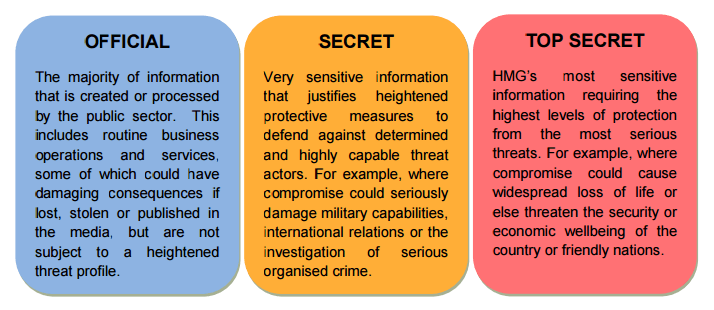
Government Security Classifications - GOV.UK
01-May-2018 Page 7 of 37. Security Classification Definitions. 15. The three security classifications (OFFICIAL SECRET and TOP SECRET) indicate the. |
|
The Security Content Automation Program (SCAP): Automating
OVAL could then define how that check should be performed on a particular type of Tier 3. The checklist is specific to Federal agencies8 so it is ... |
|
Oracle Cloud Infrastructure Security Architecture (PDF)
3 Oracle Cloud Infrastructure Security Architecture / version 2.0 OCI benefits from tiered defenses and highly secure operations that span from the ... |
|
AUTHORISED ECONOMIC OPERATOR (AEO) SCHEME
What is the structure of. Indian AEO programme? ANS. There is a three-tier programme for importers and exporters i.e.. AEO-T1 AEO- |
|
Information Security Continuous Monitoring (ISCM) for federal
In the model data is collected (for predefined metrics or in response to a user query) toinclud e those related to security control implementation and effectiveness The types of data sources include people processes technologies and the computing environment (including security control assessment results) |
|
A Breakdown of the Tier 3 Background Investigation
Tiered Investigations Three basic reasons for conducting background investigations National Security – access to classified Suitability / Fitness for government employment Personal Identity Verification in support of credentialing Homeland Security Presidential Directive 12 (HSPD-12) |
|
Personnel Suitability and Security Handbook - US Fish and
Tier 3 – Non-Critical Sensitive positions requiring access eligibility (Confidential Secret or Top Secret) Tier 4 - Non-Sensitive High Risk (Public Trust) positions Tier 5 - Critical Sensitive positions requiring Top Secret Sensitive Compartmented Information (SCI) Access Eligibility |
What is Tier 3 security clearance?
Here is what the Tier 3 (formerly known as the NACLC) covers for those applying for a security clearance: National Agency Check (NAC) – this check is a part of all background investigations and queries OPM’s Suitability/Security Index (SII) and DoD’s Defense Central Index of Investigations (DCII) files for any previous investigations.
What is a security tier?
Each tier monitors security metrics and assesses security control effectiveness with established monitoring and assessment frequencies and status reports customized to support tier-specific decision making.
Does a favorable national security adjudicative determination provide a tier 1/low risk position?
A favorable national security adjudicative determination does not provide for automatic eligible to occupy a public trust or Tier 1/Low Risk position per 5 CFR 731. Suitability and fitness requirements for employment are separate and distinct from job qualifications (e.g., education or experience requirements).
What is a Tier 1 HSPD credential?
Tier 1 - Non-Sensitive/Low Risk (NS/LR) positions, HSPD-12 Credential, Tier 2 – Non-Sensitive Moderate Risk (Public Trust) positions. Tier 3 – Non-Critical Sensitive positions requiring access eligibility (Confidential, Secret, or Top Secret). Tier 4 - Non-Sensitive High Risk (Public Trust) positions.
|
CIS Amazon Web Services Three-tier Web Architecture - Awsstatic
9 nov 2016 · 1 10 Ensure Web Tier ELB have the latest SSL Security Policies route (0 0 0 0/ 0) defined to allow connectivity to the VPC Internet Gateway Note the EBS volume id's, Instance id's, Availability Zones, and check if Encrypted |
|
SECURING THREE-TIER SYSTEMS WITH ORACLE8I - CGISecurity
These include assuring user authentication, controlling user access, auditing user actions, protecting data security between tiers, limiting privilege of the middle tier, managing identities across tiers, and building scalable systems AUTHENTICATING THE USER |
|
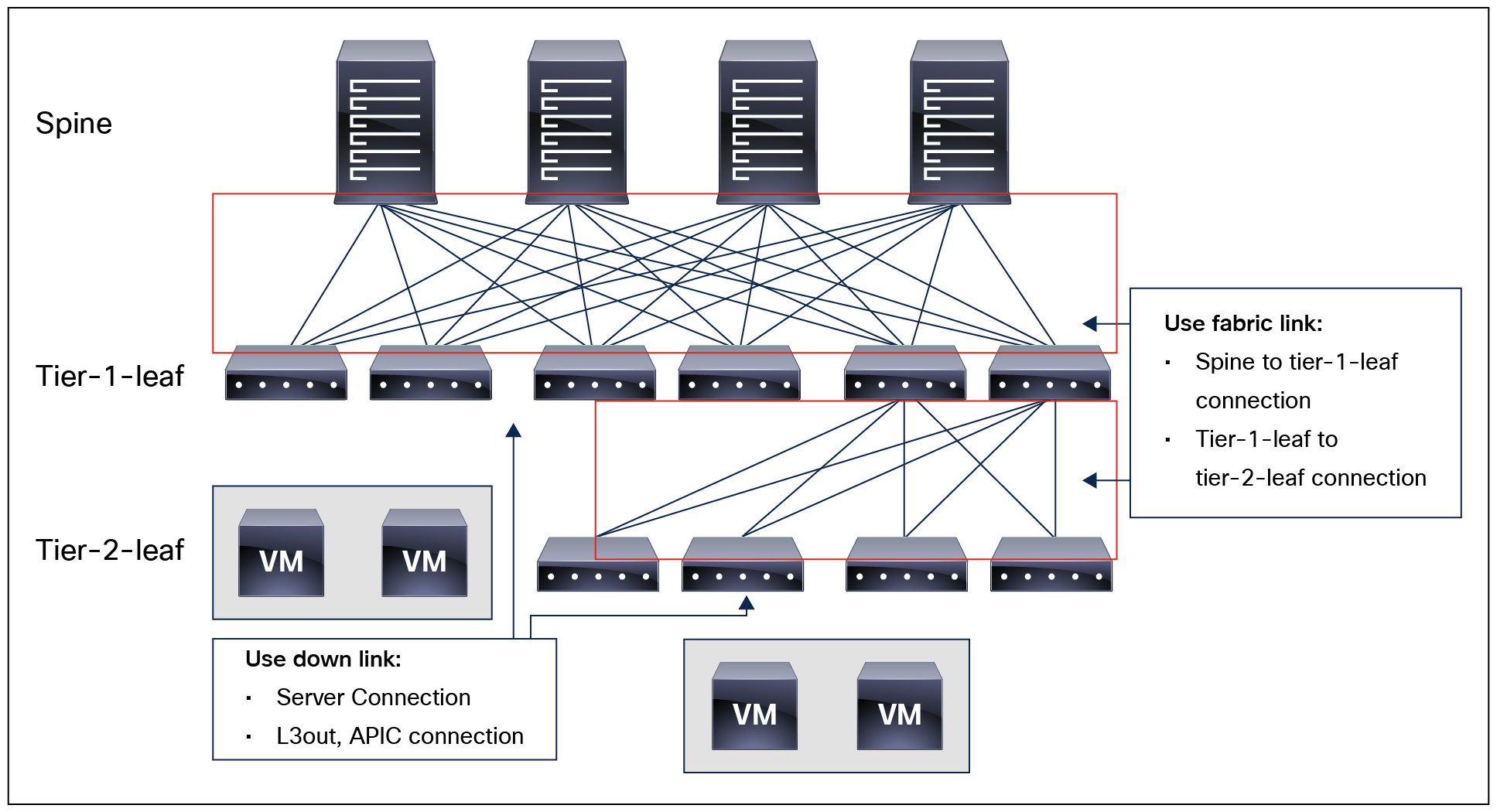
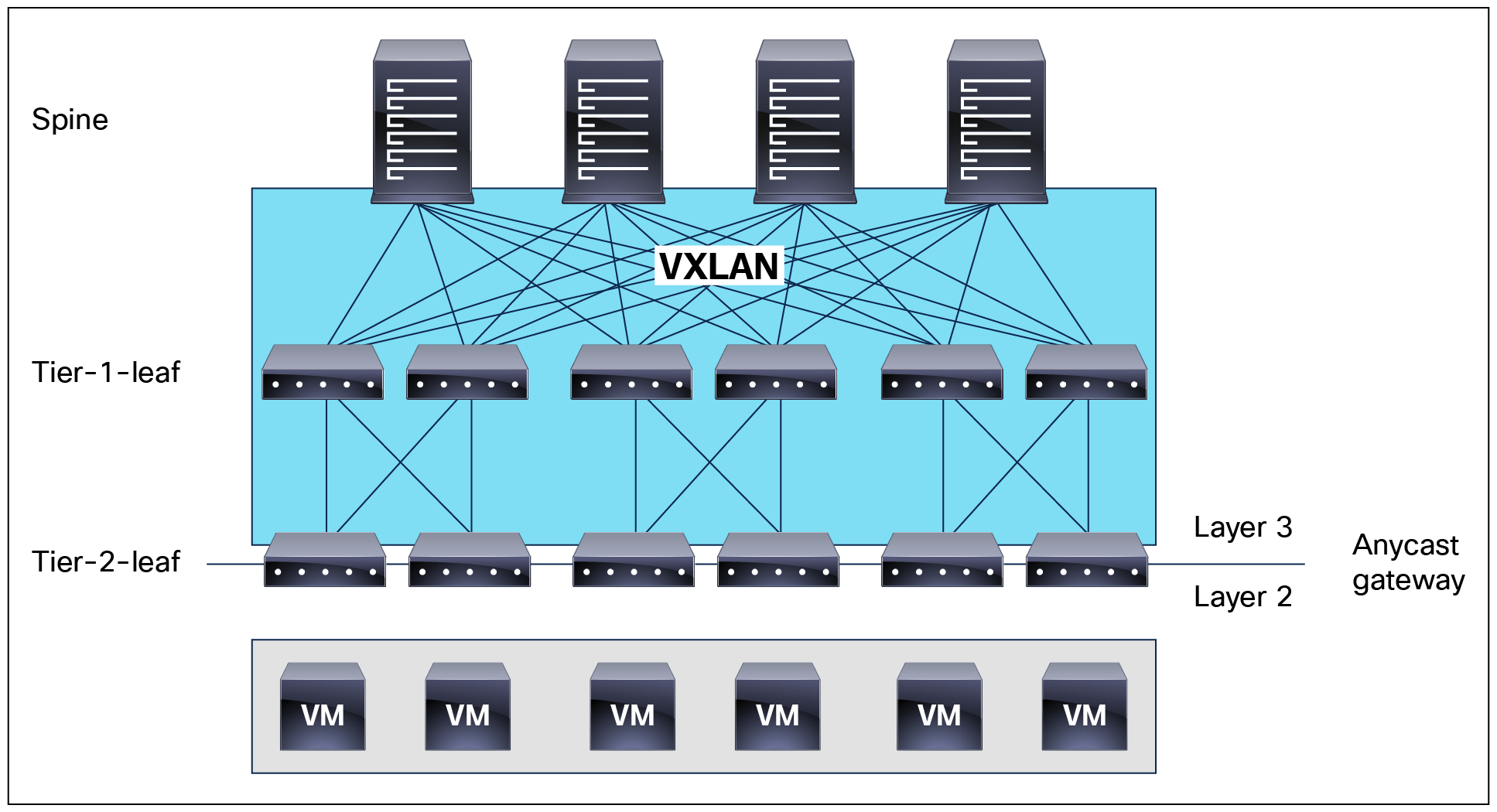
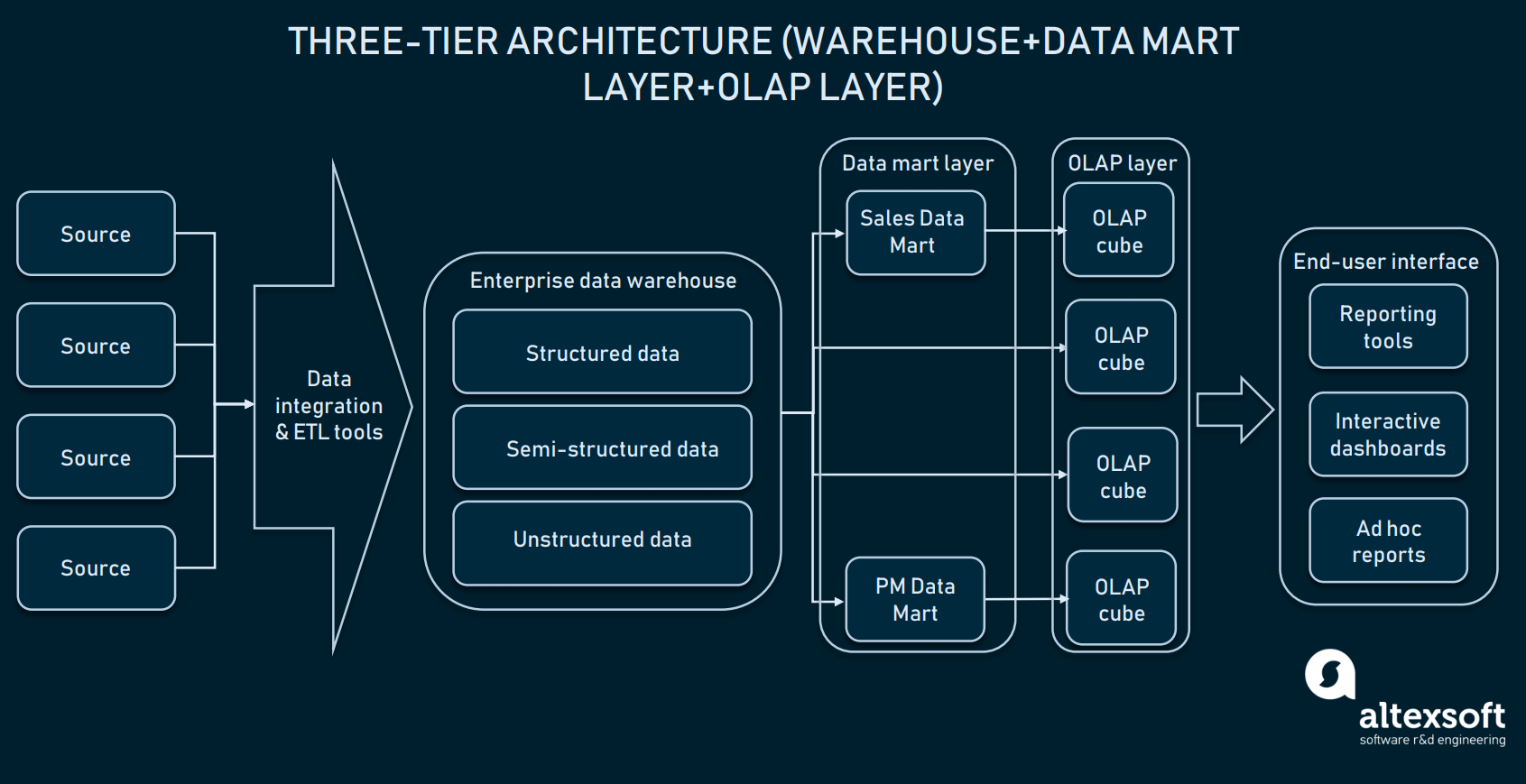
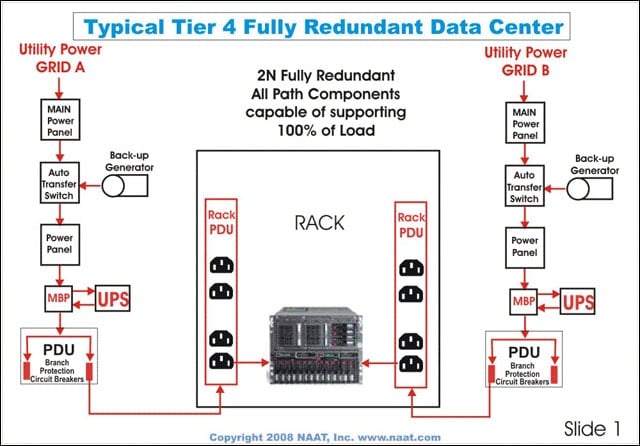
91 Two-tier Architecture Typical client/server systems have fallen
A client is defined as a requester of services and a server is defined as the provider Thus three-tier client/server applications employ an intermediary or middle-tier application systems as the business logic and services such as security, persistence, services (including check-in and check-o*ut, version control, security |
|
A Secure Multi-Tier Mobile Edge Computing Model for Data - CORE
23 sept 2018 · Section 3 describes the security model for mobile edge computing architectures, for example, if the next tier requires authentication, it will be and, the integrity manager—to periodically check the integrity of the tasks— |
|
Web Application Security Standard
Level 3 – Sensitive Data “Tier 1 – mission critical” Web Applications represent core functions that example of security through obscurity services to receive warnings on packages during development and as a scheduled periodic check |
|
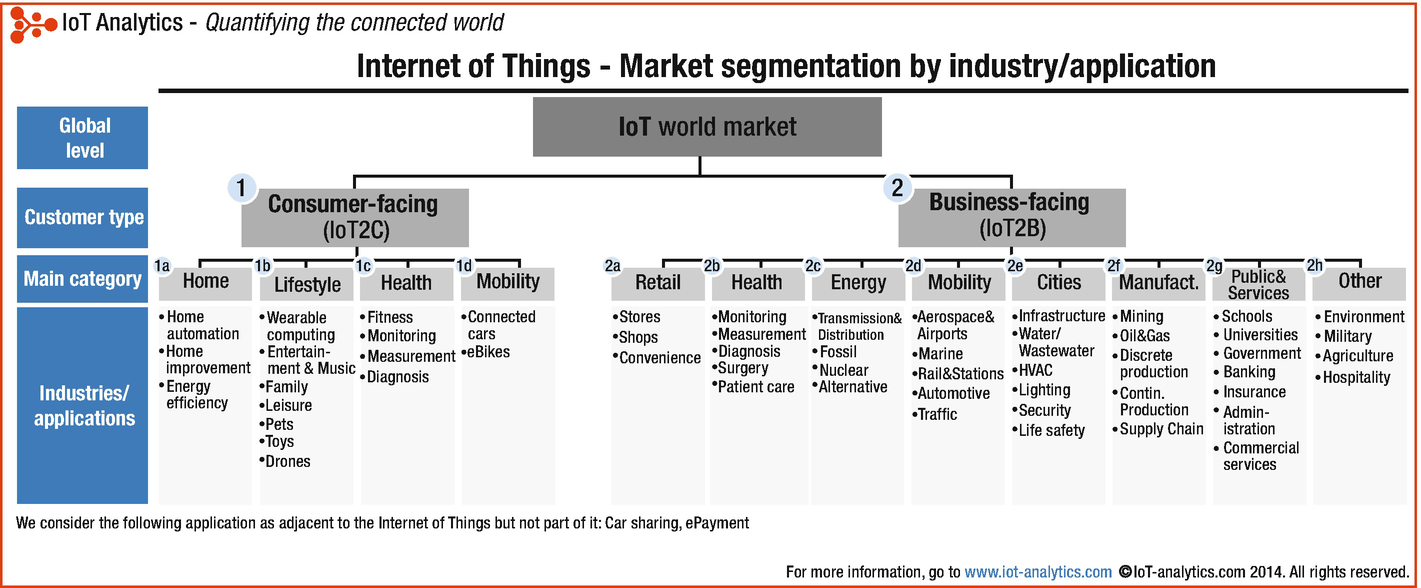
Industrial Internet Reference Architecture
4 jui 2015 · 7 1 1 Three-tier architecture pattern 7 Examples of security related compliances include Common Criteria [23] and various Federal |
|
Securing Enterprise Web Applications at the Source - OWASP
tiered enterprise web application are discussed with focus on threat modeling instance, ZF1 mandates the definition of web security guidance which is an ids, forced browsing past access control checks (URL tampering), path traversal, file |
|
A Three Tier Secure System for Online Voting - IRJET
- Conventional voting process can be overwhelming, time consuming and prone to security breaches and electoral fraud Over the years technology related |
|
Building Multi-Tier Scenarios for WebSphere - IBM Redbooks
Records 70 - 79 · 1 1 Multi-tiered environment considerations e-business infrastructure, e- business security concepts, large scale ISP architectures and |
|
Fine-Granularity Access Control in 3-tier Laboratory - PLG
cess control models that define a permission as the right of a user/role to With this, access control can be integrated into a legacy 3-tier infor- based on a three-tier architecture Access is via fines the routines to check data access, and specifies in a declarative National Computer Security Conference, 1992 [7 ] D F |