configuration vpn ipsec cisco router
|
Cisco IOS VPN Configuration Guide
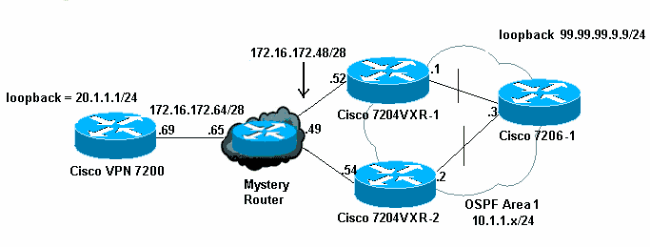
cover every available feature; it is not intended to be a comprehensive VPN configuration guide Instead this guide simply explains the basic tasks necessary to configure site-to-site and remote access VPNs on your Cisco 7200 series router |
|
Configuring a VPN Using Easy VPN and an IPSec Tunnel
The router acting as the IPSec remote router must create an Easy VPN remote configuration and assign it to the outgoing interface Creates a Cisco Easy VPN remote configuration and enters Cisco Easy VPN remote configuration mode Specifies the IPSec group and IPSec key value for the VPN connection |
|
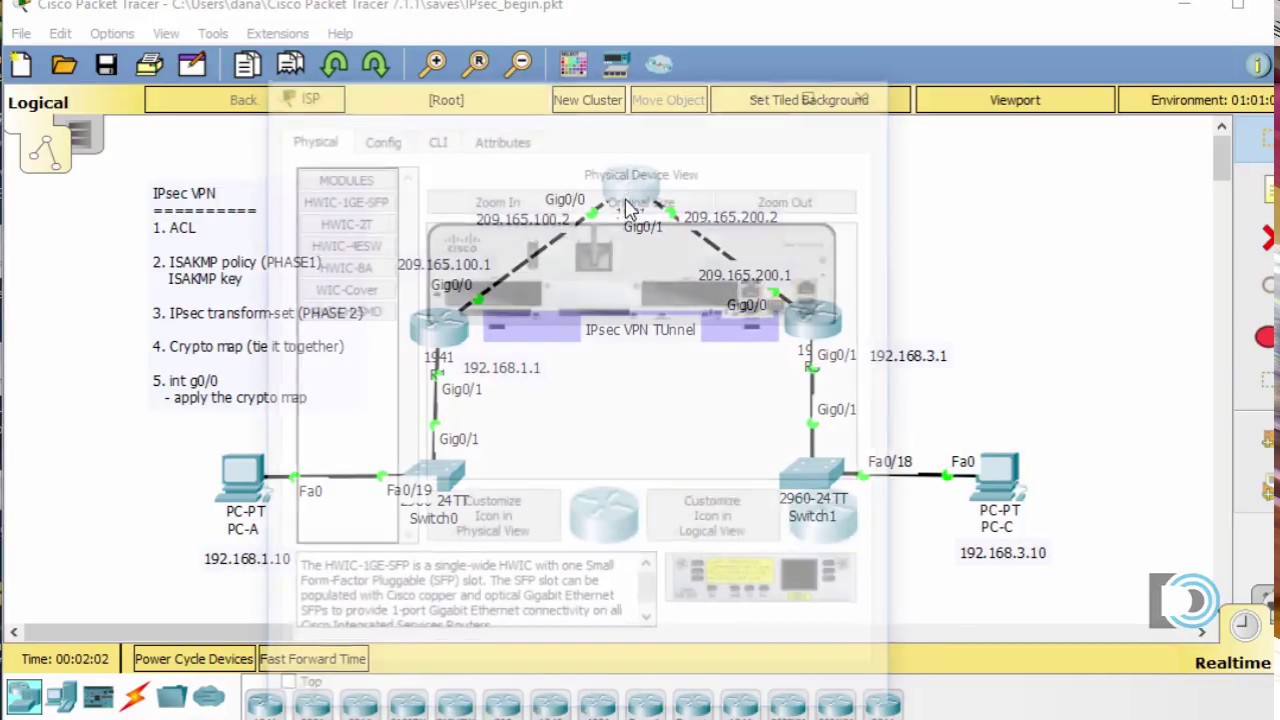
Configuring IPsec Between Two Routers and a Cisco VPN Client 4
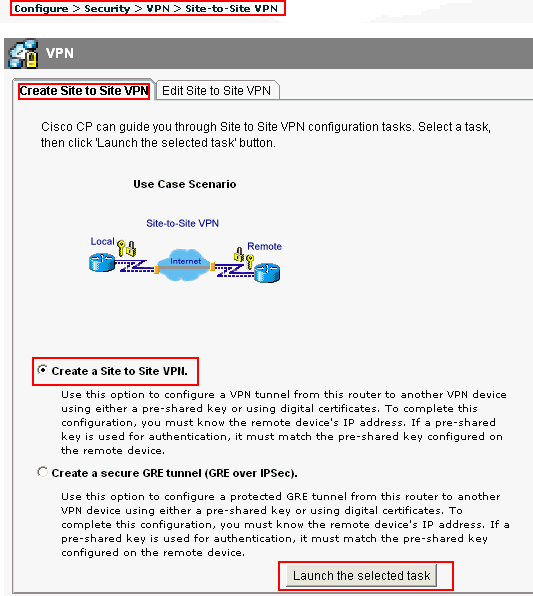
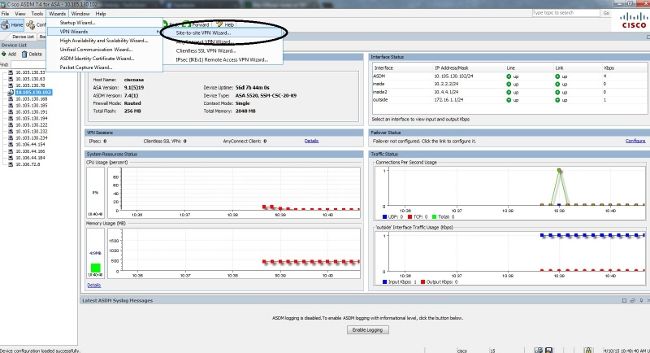
Configure the VPN Client 4 x Follow these steps in order to configure Cisco VPN Client 4 x Launch the VPN Client and then click New in order to create a new connection Input the necessary information and click Save when finished Right−click on the newly created Connection Entry and click Connect in order to connect to the router |
|
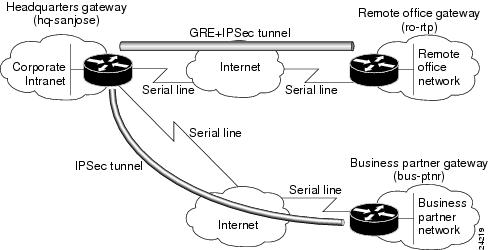
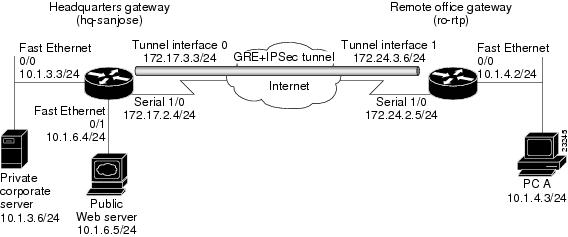
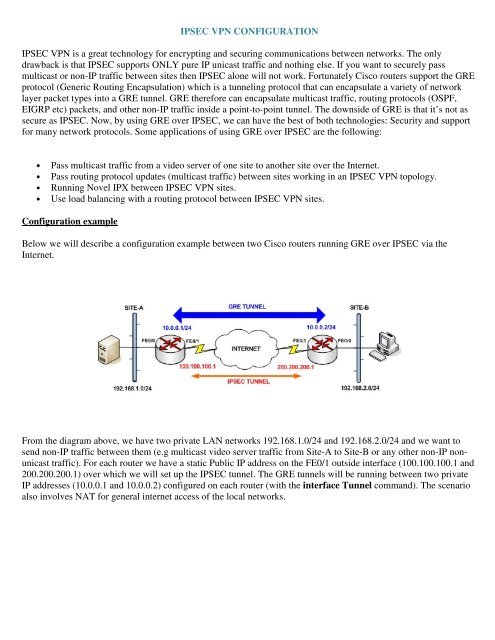
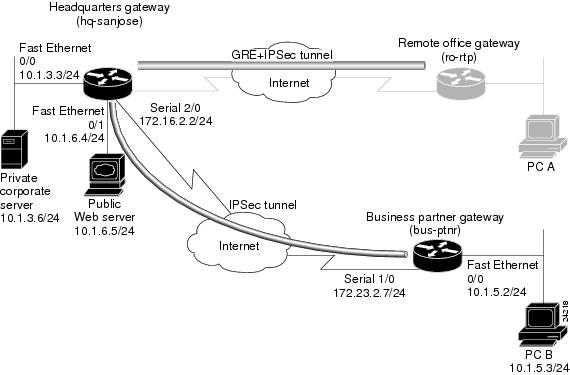
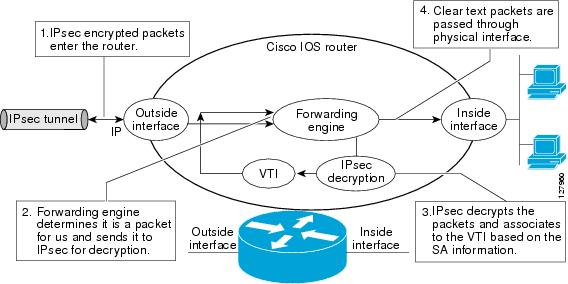
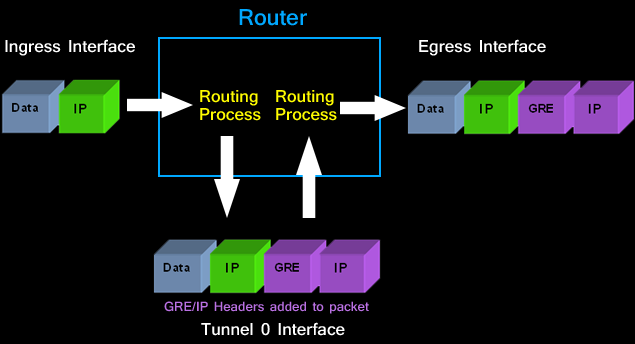
Configuring VPNs Using an IPSec Tunnel and Generic
Perform these steps to configure the IPSec crypto method beginning in global configuration mode: Command or Action Purpose Step 1 crypto ipsec transform-set transform-set-name transform1 [transform2] [transform3] [transform4] Example: Router(config)# crypto ipsec transform-set vpn1 esp-3des esp-sha-hmac Router(config)# |
What are the advantages of using IPsec VPN?
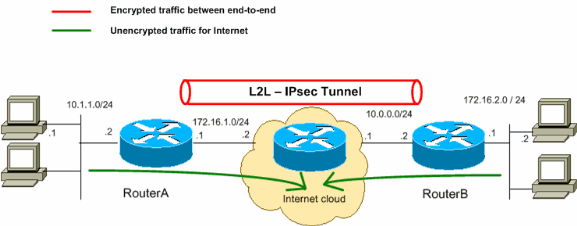
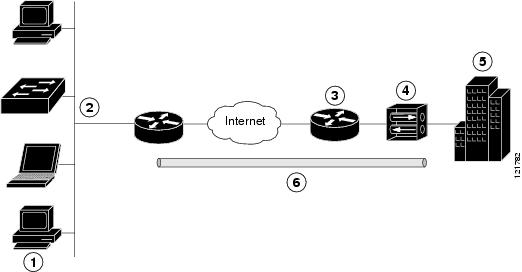
IPsec Virtual Private Network (VPN) technology enables remote users to connect to private computer networks to gain access to their resources in a secure way. For example, an employee traveling or working from home can use a VPN to securely access the office network through the Internet.
What is the purpose of IPsec VPN configuration?
IPsec is a framework of open standards developed by the IETF. It provides security for the transmission of sensitive information over unprotected networks such as the Internet. IPsec acts at the network layer, protecting and authenticating IP packets between participating IPsec devices (“peers”), such as Cisco routers.
What is necessary to initiate the IPSec process?
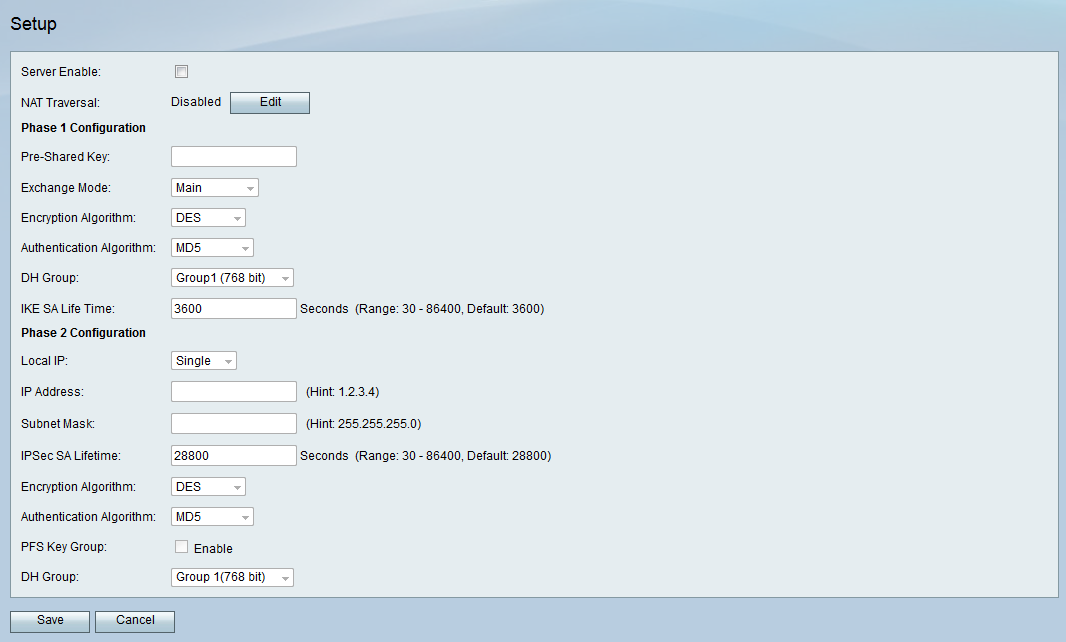
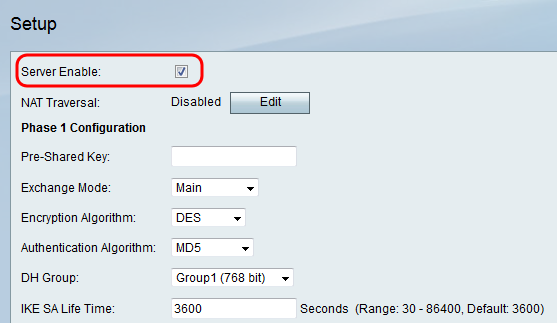
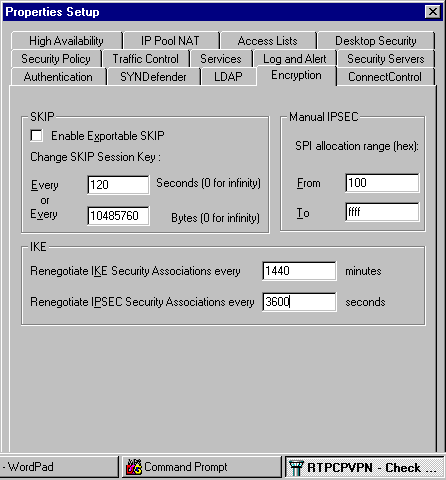
This process requires that the IPSec systems first authenticate themselves to each other and establish ISAKMP (IKE) shared keys. A security association (SA) is a relationship between two or more entities that describes how the entities will use security services to communicate securely.
What are the prerequisites for configuring a Cisco IPsec VPN?
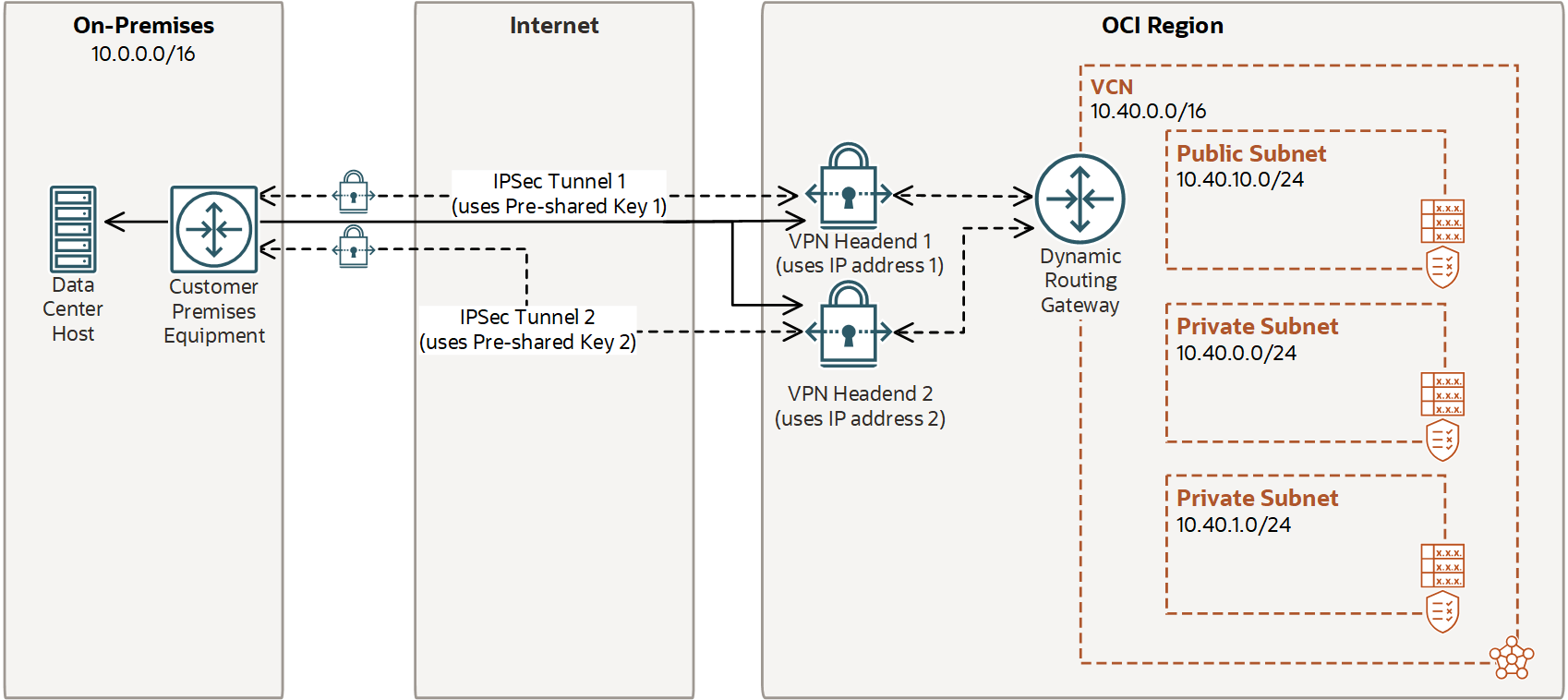
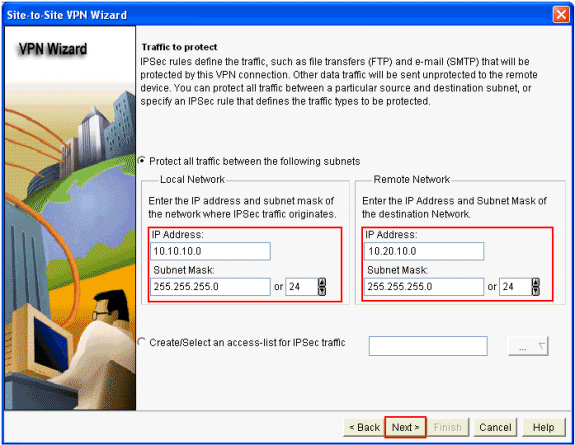
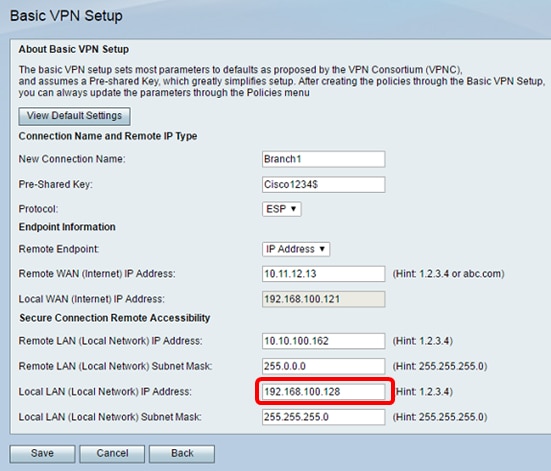
VPN configuration information must be configured on both endpoints; for example, on your Cisco router and at the remote user, or on your Cisco router and on another router. You must specify parameters, such as internal IP addresses, internal subnet masks, DHCP server addresses, and Network Address Translation (NAT).
Introduction
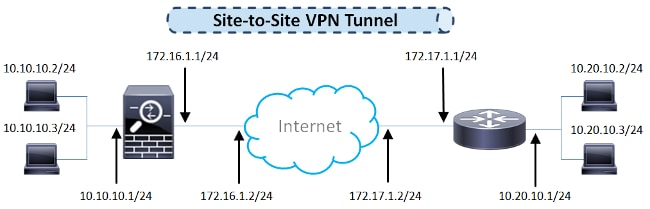
This document describes how to configure a policy-based VPN (site-to-site) over Internet Key Exchange (IKEv1) between two Cisco routers (Cisco IOS or Cisco IOS XE), which allows users to access resources across the sites over an IPsec VPN tunnel. cisco.com
Prerequisites
Requirements There are no specific requirements for this document. Components Used The information in this document is based on a Cisco router with Cisco IOS®Release 15.7. The information in this document was created from the devices in a specific lab environment. All of the devices used in this document started with a cleared (default) configuration. If your network is live, ensure that you understand the potential impact of any command. Conventions Refer to the Cisco Technical Tips Conventionsfor more information on document conventions. cisco.com
Configure
In this section, you are presented with the information to configure the features described in this document. cisco.com
Verify
Use this section in order to confirm that your configuration works properly. The Cisco CLI Analyzer (registered customers only) supports certain show commands. Use the Cisco CLI Analyzer to view an analysis of showcommand output. 1. show crypto ipsec sa - Shows the settings, number of encaps and decaps, local and remote proxy identities, and Securi
Related Information
IPsec Negotiation/IKE ProtocolsTechnical Support & Documentation - Cisco Systems cisco.com

How to Configure Site to Site IPSec VPN Between Two Cisco Router

How to Setup a Cisco Router VPN (Site-to-Site): Cisco Router Training 101

Easy to Configure VPN Site to Site+IPsec on Cisco Router Full Video
|
Configuration dun tunnel IPSec de routeur entre deux réseaux
Pourquoi l'instruction de refus dans l'ACL spécifie-t-elle le trafic. NAT ? Lorsque vous utilisez Cisco IOS IPsec ou un VPN cela équivaut en quelque sorte à |
|
Configuring a VPN Using Easy VPN and an IPSec Tunnel
The Cisco 870 series routers support the creation of Virtual Private Networks (VPNs). Cisco routers and other broadband devices provide high-performance |
|
Exemple de configuration de tunnel IPSec LAN à LAN entre un
Ce document explique comment configurer un tunnel IPSec entre un concentrateur Cisco VPN 3000 et un routeur Cisco en utilisant Advance Encryption Standard |
|
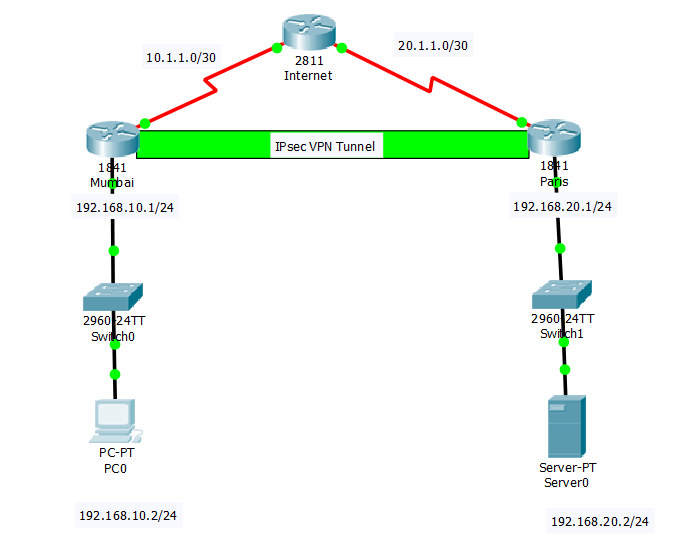
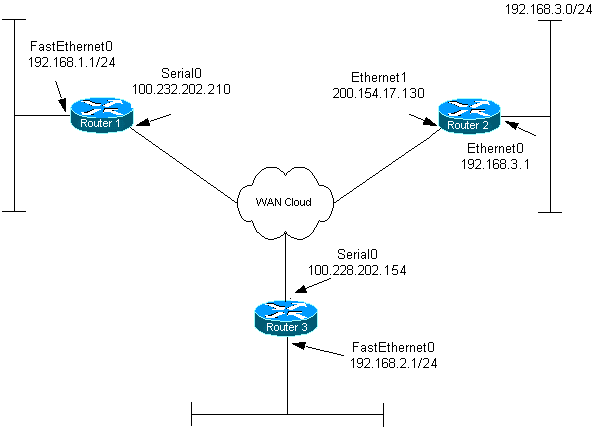
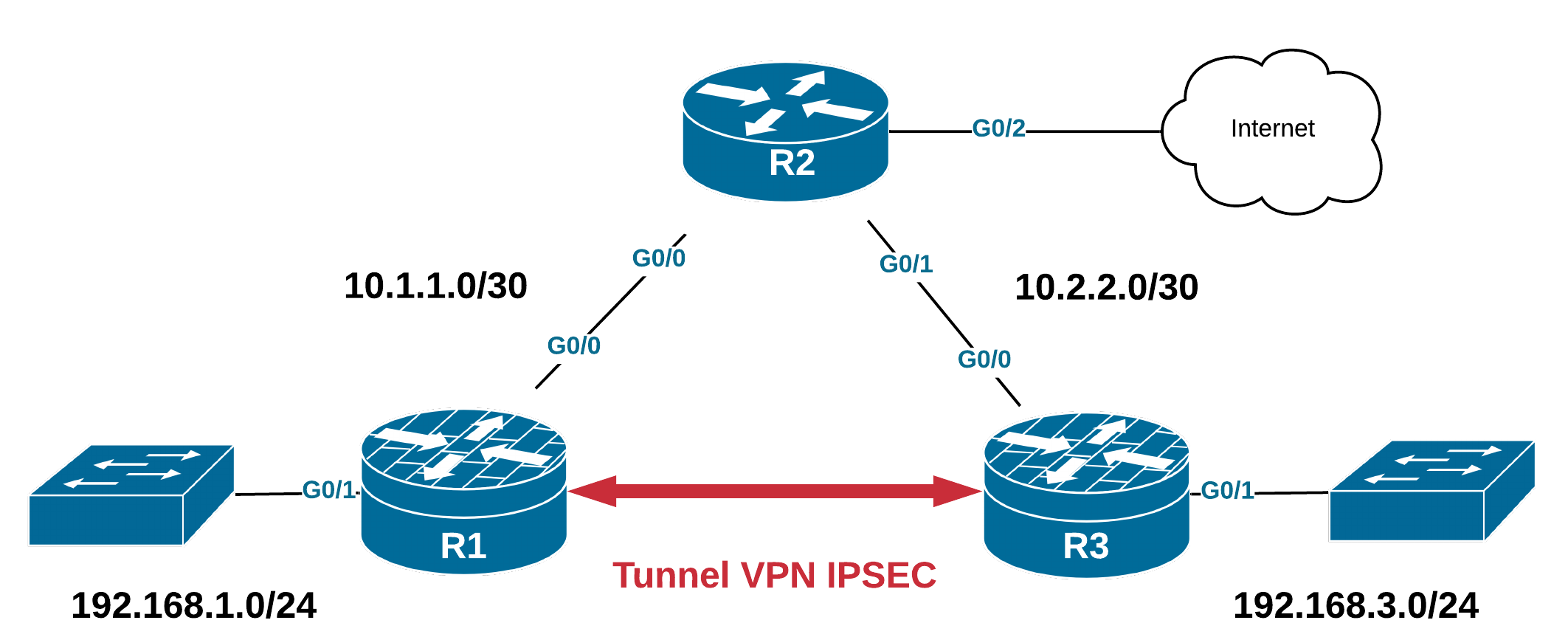
Travaux pratiques VPN IPsec CISCO de site à site
Les routeurs utilisés sont des Cisco 2811. Configuration de base de routeur1. Router>enable. Router#configure terminal. Router(config)#hostname Routeur1. |
|
Exemple de configuration IPSec entre deux routeurs IOS avec
Ce document explique comment configurer le routeur Cisco IOS dans un VPN IPsec site à site dont les adresses de réseau privé se chevauchent derrière les |
|
Security for VPNs with IPsec Configuration Guide Cisco IOS XE 17
Configuration Examples for IPsec VPN 26. Example: Configuring AES-Based Static Crypto Map 26. Additional References for Configuring Security for VPNs with |
|
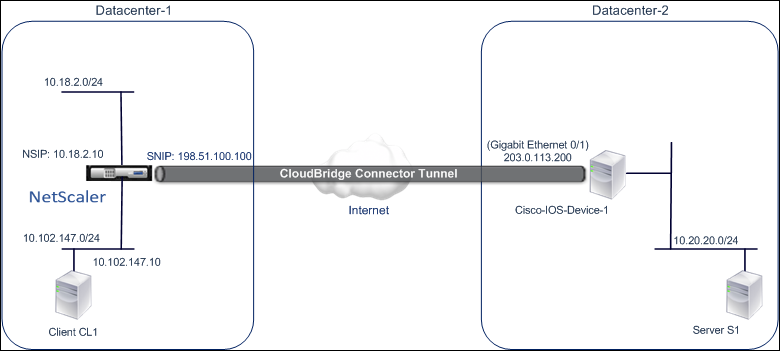
Configuration dun tunnel VPN site à site entre le routeur VPN
Un tunnel VPN IPsec site à site est configuré et établi entre le routeur Cisco RV du bureau distant et l'ISA de la gamme Cisco 500 du bureau principal. |
|
Configuring VPNs Using an IPSec Tunnel and Generic Routing
Cisco routers and other broadband devices provide high-performance connections to the Internet but many applications also require the security of VPN |
|
Cisco RVL200 4-Port SSL/IPsec VPN Router (French)
Configuration Internet simplifiée. Figure 1. Routeur VPN Cisco RVL200 4 ports avec technologie SSL/IPsec. Vue d'ensemble du produit. |
|
Configuring Security for VPNs with IPsec - Cisco
Security for VPNs with IPsec Configuration Guide Cisco IOS XE Fuji 16.7.x-Configuring Security for VPNs with IPsec. |
|
Configuring a VPN Using Easy VPN and an IPSec Tunnel - Cisco
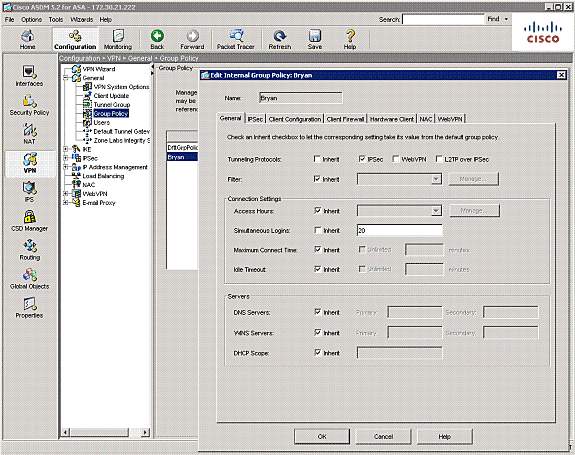
Perform the following tasks to configure your router for this network scenario: • Configure the IKE Policy • Configure Group Policy Information • Apply Mode Configuration to the Crypto Map • Enable Policy Lookup • Configure IPSec Transforms and Protocols • Configure the IPSec Crypto Method and Parameters |
|
Exemple de configuration de tunnel IPSec LAN à LAN entre - Cisco
comment configurer un tunnel d'IPsec entre un concentrateur de Cisco VPN Cisco IOS version 12 2(13)T Afin d'activer AES, votre routeur doit prendre en |
|
Configuring VPNs Using an IPSec Tunnel and Generic - Cisco
Perform the following tasks to configure a VPN over an IPSec tunnel: • Configure the IKE Policy • Configure Group Policy Information • Enable Policy Lookup • Configure IPSec Transforms and Protocols • Configure the IPSec Crypto Method and Parameters • Apply the Crypto Map to the Physical Interface |
|
Security for VPNs with IPsec Configuration Guide, Cisco IOS
You must configure Internet Key Exchange (IKE) as described in the module Configuring Internet Key Exchange for IPsec VPNs Even if you decide not to use IKE, |
|
Travaux pratiques VPN IPsec CISCO de site à site
Les routeurs utilisés sont des Cisco 2811 Configuration de base de routeur1 Router>enable Router#configure terminal Router(config)#hostname Routeur1 |
|
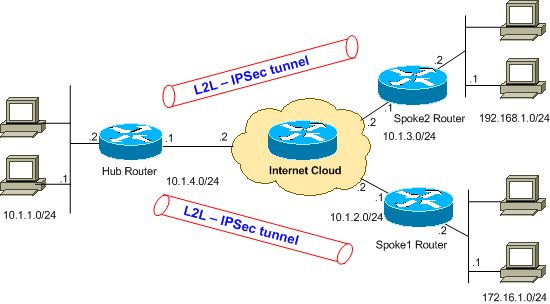
Basic IPsec VPN Topologies and Configurations
VPNs at an aggregation point, or hub IPsec router, in a standard hub-and-spoke design and extend the IPsec Cisco IOS Site-to-Site IPsec VPN Configuration |
|
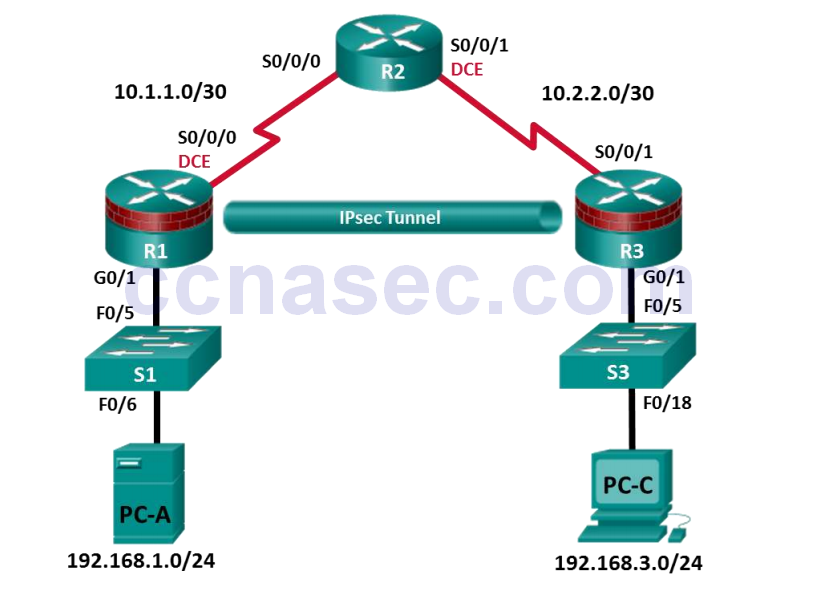
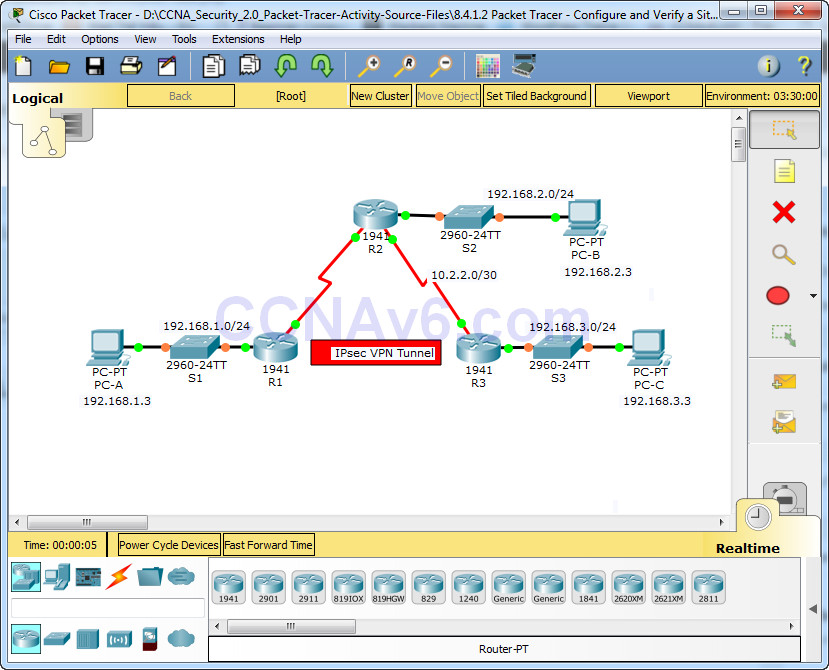
IPsec VPN
You will configure R1 and R3 using the Cisco IOS CLI You then review and test the resulting configuration Task 1: Configure IPsec VPN Settings on R1 and R3 |
|
IPSec Tunnel to Cisco router - AudioCodes
The network connection wizard appears; choose "Connect to a Virtual Private Network over the Internet" and click Next Select "VPN Client or Point-to-Point" and |
|
Configure a Site-to-Site IPsec VPN between an ISR CLI and an ASA
Other routers and Cisco IOS versions can be used See the Router Interface Summary Table at the end of the lab to determine which interface identifiers to use |








![PDF~] The Complete Cisco VPN Configuration Guide PDF~] The Complete Cisco VPN Configuration Guide](https://imgv2-2-f.scribdassets.com/img/document/295691249/298x396/c47a678ad1/1510034473?v\u003d1)







![PDF~] The Complete Cisco VPN Configuration Guide PDF~] The Complete Cisco VPN Configuration Guide](https://imgv2-1-f.scribdassets.com/img/document/238661573/149x198/b4141a8a80/1409847903?v\u003d1)