chrome extension vulnerability scanner
|
Security Analysis of Chrome Extensions
12 mai 2016 · We have evaluated the permissions model used by Google Chrome browser extensions and have identified areas where the permissions model fails to |
|
Development of a browser extension for web application
This paper presents the development of a browser extension for web application vulnerability detection avoidance and Usually vulnerability scanner detects |
Avast Online Security & Privacy
Avast Online Security & Privacy is a browser extension that offers real-time protection against threats, trackers, and scams.
This plugin checks websites you visit, from social media to online banking, and has a user base of over 10 million.
What is the Chrome extension for Askpdf?
AskYourPDF Chrome extension lets you seamlessly have intelligent conversations with your PDF documents.
Whether you're working together with others or making notes for yourself, the extension makes it quick and straightforward to extract valuable information, all without leaving the comfort of your browser.
What is the Chrome extension to check vulnerability?
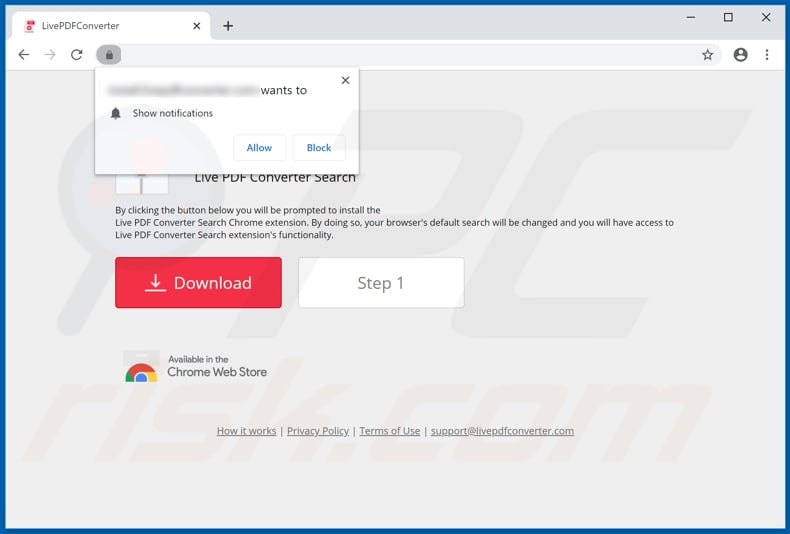
Tarnish Chrome Extension Analyzer
Tarnish is a service that helps developers and security researchers audit Chrome extensions for security vulnerabilities, with features such as manifest.20 fév. 2023
What is a website vulnerability scanner?
Web Application Vulnerability Scanners are automated tools that scan web applications, normally from the outside, to look for security vulnerabilities such as Cross-site scripting, SQL Injection, Command Injection, Path Traversal and insecure server configuration.
|
Qualys Web Application Scanning Getting Started Guide
18-Sept-2020 automated vulnerability scanning of web applications for teams using ... Qualys Browser Recorder – This new Chrome extension allows users to ... |
|
Qualys Web Application Scanning Getting Started Guide (Beta)
21-Sept-2020 automated vulnerability scanning of web applications for teams using ... Qualys Browser Recorder – This new Chrome extension allows users to ... |
|
GETTING STARTED WITH WEB APPLICATION SCANNING
WAS provides comprehensive vulnerability scanning for modern web applications. Its the Chrome extension provided by Tenable. In addition to the benefits ... |
|
Qualys-browser-recorder-user-guide.pdf
22-Oct-2020 The scripts allow the scanner to navigate complex authentication and workflows. - This new Chrome extension is designed to be essentially a ... |
|
Analysis of Open Source Node.js Vulnerability Scanners
Command line scanner. 2. Grunt plugin. 3. Chrome extension. 4. Firefox extension. 5. Burp and OWASP zap plugin. For reviewing the scanners this paper uses |
|
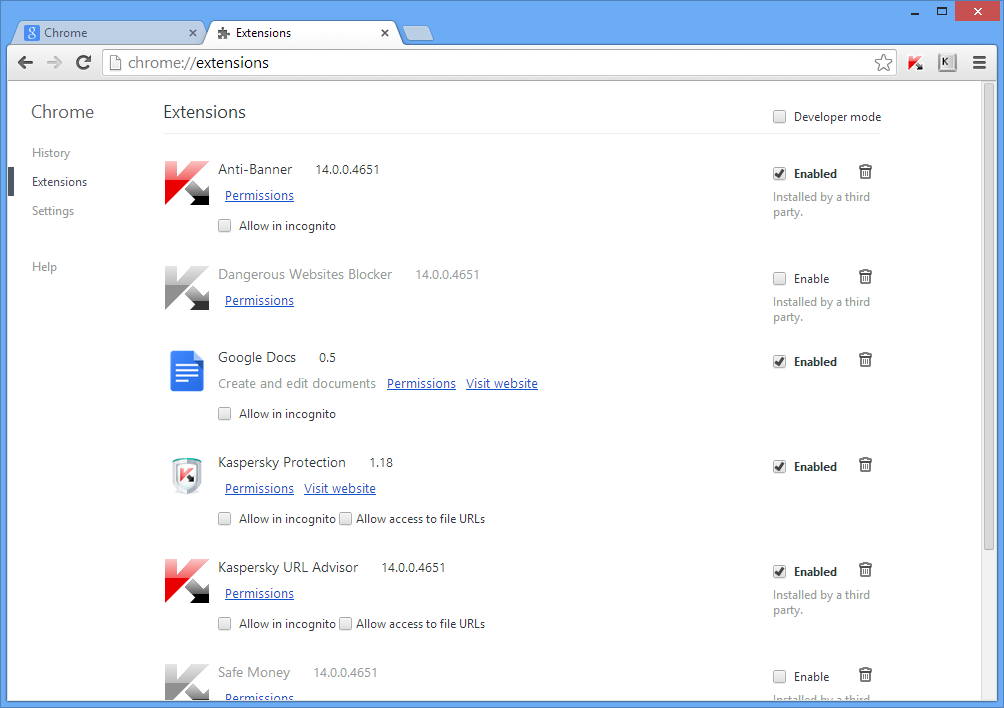
Protecting Browsers from Extension Vulnerabilities
18-Dec-2009 ity. Our design has been adopted as the Google Chrome extension system. 1 Introduction. Web browser extensions are phenomenally popular:. |
|
A Web Application Vulnerability Scanner
14-Apr-2020 of work and the vulnerability extensions shall be prioritised over the ... headless versions of Chrome |
|
Measurement and detection of security properties of client-side web
5.3.2 Vulnerability Scanner Capability Test and Log Analysis . Content Security Policy for Extensions Chrome extensions leverage Content Security. |
|
Security Analysis of Chrome Extensions
12-May-2016 Finally we will recommend some changes to the permissions model to help mitigate the vulnerabilities we discovered. 2 Extension Security ... |
|
Malicious Browser Extensions at Scale: Bridging the - USENIX
seeking to exploit Internet services Such attacks are par- scan Malicious action Should Scan? Logout user No, Log in Malware Cleanup Yes Malware threshold, or (ii) in the case of Chrome extensions, if the extension is live on the |
|
Exploiting Leaky Chrome Extension API - csail - MIT
15 mai 2019 · attempts to exploit Chrome extensions through a malicious website Finally basic security scans for plugin behavior and code style to identify |
|
Security Analysis of Chrome Extensions - csail
12 mai 2016 · used by Google Chrome browser extensions, and have identified areas permissions model to help mitigate the vulnerabilities we discovered it is on the Chrome Web Store (there is ostensibly some review/scanning |
|
Effective Detection of Vulnerable and Malicious Browser Extensions
6 août 2014 · Mozilla Firefox, Google Chrome) to enrich the browser with various function- effective as they exploit vulnerable extensions to deploy malicious Some network level attacks (e g , denial of service, port scanning) can be |
|
Analysis of Open Source Nodejs Vulnerability Scanners - IRJET
Retire js can be used in different ways: 1 Command line scanner 2 Grunt plugin 3 Chrome extension 4 Firefox extension 5 Burp and OWASP zap plugin |
|
Qualys Web Application Scanning Getting Started Guide - Qualys, Inc
18 sept 2020 · automated vulnerability scanning of web applications for teams using the Qualys Browser Recorder – This new Chrome extension allows |
|
Attacking Browser Extensions - Nicolas Golubovic
3 mai 2016 · extensions in its associated Chrome Web Store, some of them amassing over 10 million active users authors of vulnerable extensions and better mitigations from browser vendors sparse-bruteforce-addon-scanner html |