ECC SIEZ 74 2016
|
ADMINISTRATION
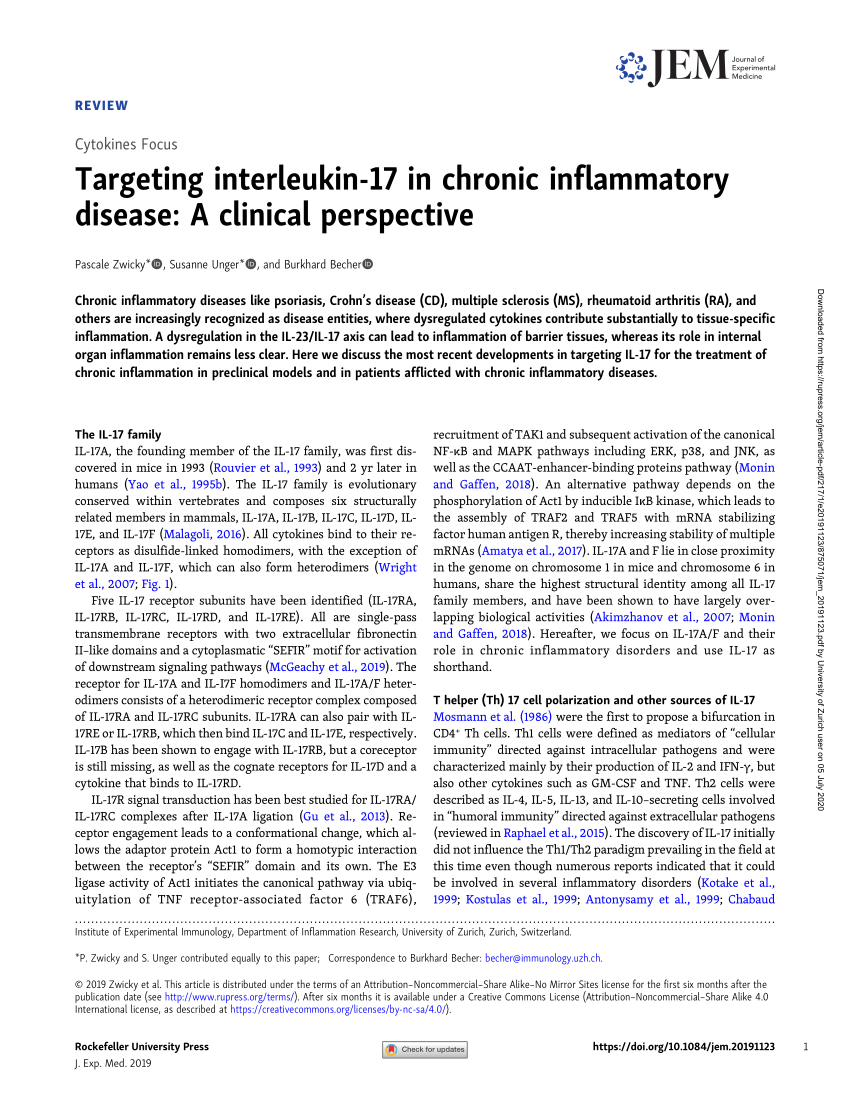
IECC”) as amended by Part 3 of the publication entitled the 2016 Supplement to the New York State Energy Conservation Construction Code (the “2016 Energy Code Supplement”); and (ii) the referenced standards incorporated by reference in 19 NYCRR section 1240 5(b) as amended by Part 3 of the 2016 Energy Code Supplement SECTION ECC 101 |
|
ERC Recommendation 74-01
3 The CEPT/ECC liaison statement should include the implications of the proposal on spectrum engineering parameters such as: effective use of the spectrum requirements of existing services sharing/adjacent band and other regulatory issues; 4 The proposal should be considered in the spirit of the ETSI/ECC MoU with dialogue full consultation |
|
ECC Algorithm & Security in Cloud - IJARCST
Computer Science Technology (IJARCST 2016) 24 Vol 4, Issue 1 (Jan are used for both ECC and RSA which is based on the key size Encryption Block |
|
A Survey of Hardware Implementations of Elliptic Curve
Abstract—Elliptic Curve Cryptography (ECC) has gained The fact that ECC can have smaller key sizes than RSA, while main- 1223-1232, 2016 [13] K C C |
|
Communications in Computer and Information Science, 169
systems, for a given key size, ECC is the most secure public key cryptosystem A survey of various protocols based on ECC has been done in the paper The |
|
High Speed and Low Latency ECC Implementation over GF - CORE
2016 IEEE Personal use multiplier based ECC implementation is the first work reporting the lowest Again, the digit size can affect the performance of ECC; |
|
Mutual Entity Authentication Protocol Based on ECDSA for - CORE
Procedia Computer Science 89 ( 2016 ) 187 – 192 Available online at This enables ECC to work with smaller key size to achieve the same level of security as |
|
RSA and ECC: A Comparative Analysis - Research India Publications
Shamir Adleman) and ECC (Elliptic Curve Cryptography) In algorithm needs a key size of 2048 bits, while ECC needs a Mahto, D and Yadav, D K , 2016 |
|
Comparative Study of ECC Libraries for Embedded - Tjerand Silde
Keywords: ECC Libraries · Embedded Devices · Side-Channel Attacks · Fault Attacks sizes considered “secure” [6]: RSA is considered secure with 2048 bit keys and on A World of Wireless, Mobile and Multimedia Networks (2016) 25 |
|
A New Method of Encryption Algorithm Based on Chaos and ECC
Volume 7, Number 3, May 2016 The security of the ECC is based on the intractability of the elliptic curve discrete cryptographic scheme for different key size |














![Schüco LivIng [PDF] Schüco LivIng [PDF]](http://fr.1001mags.com/images/Couv/M/MaisonDecorationCuisines/19/44920-MaisonDecorationCuisines-19-Page-055.jpg)
















![Power \u0026 Lighting [PDF] Power \u0026 Lighting [PDF]](https://www.researchgate.net/images/template/default_publication_preview_large.png)








