cisco network security baseline pdf
|
Create baselines
You will see your two new baselines Create a weekend baseline Create a baseline to monitor the network during weekends Procedure Step 1 Access All data |
|
Product Security Baseline Linux Distribution Requirements Version 10
1 Introduction This document seeks to assist Cisco product teams in formulating plans for the acquisition of Linux OS distributions |
|
Chapter 5: Network Security and Monitoring
Troubleshoot suspicious LAN traffic using SPAN Chapter 5 - Sections Objectives Page 3 3 © 2016 Cisco and |
|
User Security Configuration Guide
baseline level of security for your networking devices It focuses on the least complex options available for implementing a baseline level of security If |
|
Network Infrastructure Security Guide
15 jui 2022 · While the guidance presented here can be applied to many types of network devices the National Security Agency (NSA) has provided sample |
|
Network Security Baseline
Network Security Baseline OL-17300-01 Chapter 1 Introduction Cisco Security Framework Overview http://www cisco com/application/ pdf /en/us/guest/netsol/ |
|
Introduction to Network Security
Building a baseline of what should be considered normal behavior This is Network Security Principles and Practices ISBN: 1587050250 Cisco Secure Internet |
What is network security PDF?
Network Security is a concept of securing data through wireless transmission with the help is used to ensure the contents of a message which are confidentiality means of cryptography.
A set of specifications for a system, or Configuration Item (CI) within a system, that has been formally reviewed and agreed on at a given point in time, and which can be changed only through change control procedures.
The baseline configuration is used as a basis for future builds, releases, and/or changes.
How to configure a router PDF?
To configure the router, perform one or more of these tasks:
1• Configure Global Parameters.2• Configure Fast Ethernet LAN Interfaces.3• Configure WAN Interfaces.4• Configuring a Loopback Interface.5• Configuring Command-Line Access to the Router.What is an example of a baseline configuration?
Baseline configuration is a snapshot of the configuration at a specific time.
For example, if we retrieved the configuration for a server or router that information is a snapshot of how the device was configured at the time we retrieved it.
This is what is meant by baseline configuration.
|
Network Security Baseline
Network Security Baseline. OL-17300-01. Chapter 1 Introduction. Cisco Security Framework Overview http://www.cisco.com/application/pdf/en/us/guest/netsol/ ... |
|
Protect Your Network with Security and Support - Cisco
The first layer is the enforcement of the fundamental elements of network security. Cisco® Security Solutions provide these elements to form a security baseline |
|
Introduction to Network Security - Cisco
Why Create a Security Policy? • To create a baseline of your current security posture. • To set the framework for security implementation. • To define allowed |
|
Cisco Solution Support for Network Security At-a-Glance
Cisco® Security. Solutions provide these elements to form a security baseline creating a strong foundation on which more advanced technologies can be built |
|
Cisco Connect Toronto 2019
30-Oct-2019 Baseline Cyber Security. Controls for Small and. Medium Organizations. Mapping Cisco Security to Security Controls. 72. Presentation ID. Page 72 ... |
|
Cisco Secure Development Lifecycle Overview
We conduct a gap analysis and risk assessment to establish the product's security and privacy posture compared with Cisco and industry standard baseline |
|
Product Security Baseline Linux Distribution Requirements Version 1.0
This document does not contain Cisco proprietary information and can be shared with third party Linux vendors. The initial version of this document |
|
Cisco IP Phone 6800 7800
https://www.cisco.com/c/dam/en/us/td/docs/solutions/PA/security/MPP_security_technical_paper.pdf |
|
Cisco Cyber Vision GUI User Guide Release 4.1.0
01-Jan-2021 Security to control remote accesses and insecure activities. • Control system integrity |
|
Webex Calling Security White Paper
Webex and Webex Calling are backed by. Cisco's rich history and expertise in security — from the network to endpoints |
|
Cisco Secure Development Lifecycle Overview
We conduct a gap analysis and risk assessment to establish the product's security and privacy posture compared with Cisco and industry standard baseline |
|
Cisco Solution Support for Network Security At-a-Glance
layer is the enforcement of the fundamental elements of network security. Cisco® Security. Solutions provide these elements to form a security baseline |
|
EN 303 645 - V2.1.0 - CYBER; Cyber Security for Consumer Internet
Apr 20 2020 CYBER;. Cyber Security for Consumer Internet of Things: Baseline ... The content of the PDF version shall not be modified without the ... |
|
Security standard SS-018: Network Security Design
Mar 30 2020 Secondly |
|
Untitled
2019 Cisco and/or its affiliates. All rights reserved. Cisco Public. Product Security Baseline (PSB) Requirements. • Incorporates requirements into. |
|
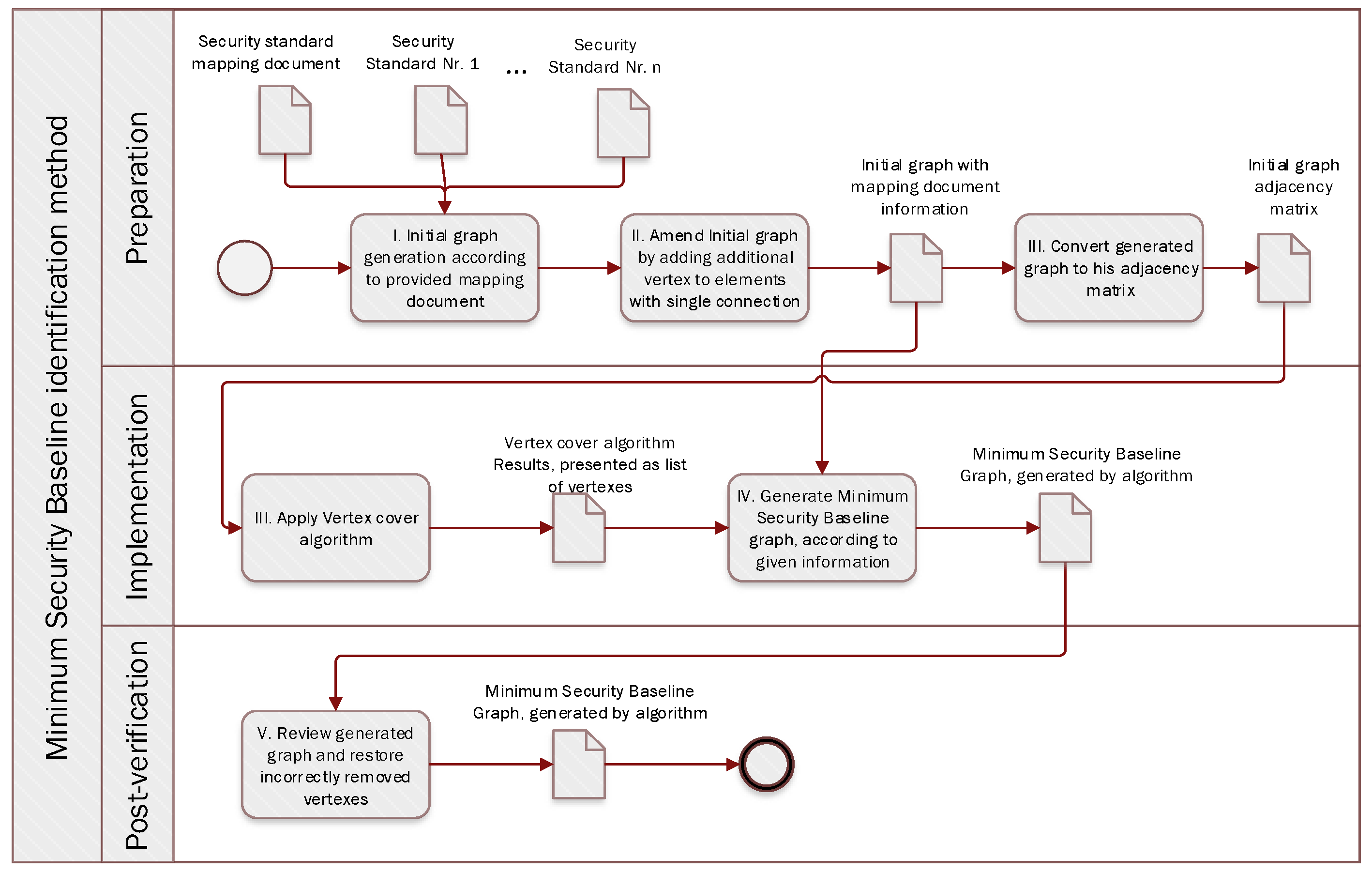
Defining the Minimum Security Baseline in a Multiple Security
Feb 17 2019 Vertex cover problems are widely used in the information technology area |
|
Cisco Cyber Vision GUI User Guide Release 3.1.0
May 26 2020 Security |
|
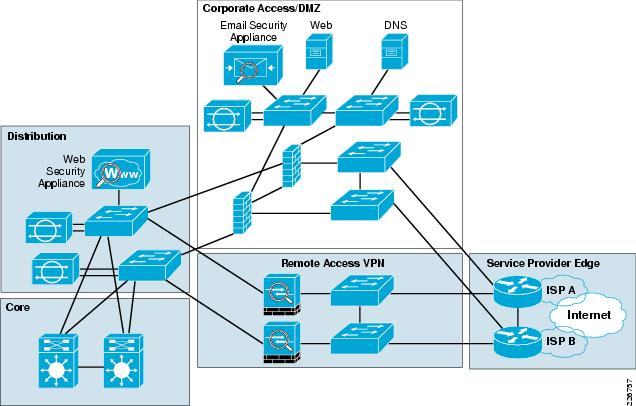
Network Security within a Converged Plantwide Ethernet Architecture
Collection of tested and validated architectures developed by subject matter authorities at Cisco and Rockwell Automation. The content of CPwE is relevant to |
|
Cisco Cyber Vision GUI User Guide Release 4.0.0
Jul 23 2021 Security |
|
Cisco Cyber Vision GUI User Guide Release 3.2.0
Nov 17 2020 Security |
|
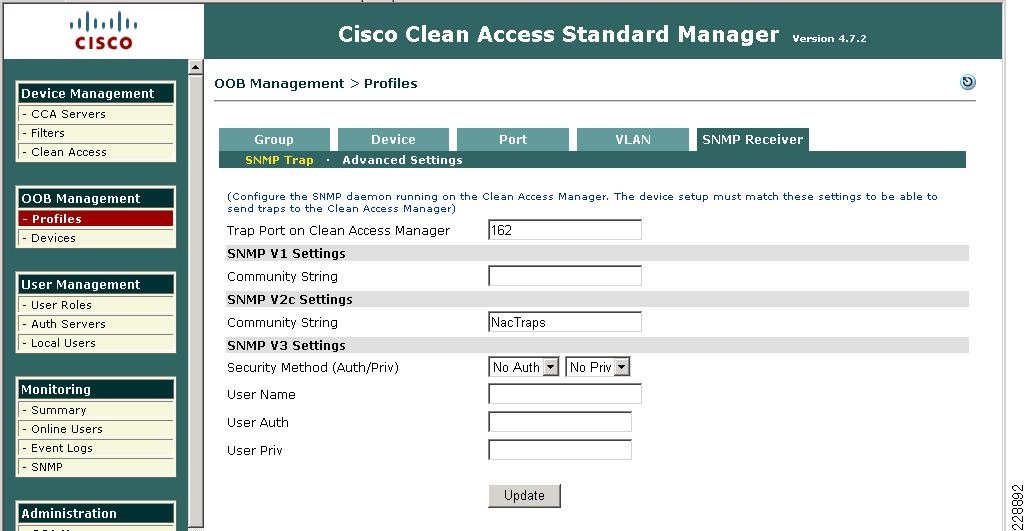
Network Security Baseline - Cisco
Network Security Baseline Getting Started with Security Baseline 8-1 Manual image verification may be initiated from the CLI using the verify command: |
|
White Paper Enterprise Security Baseline September 2015 - Cisco
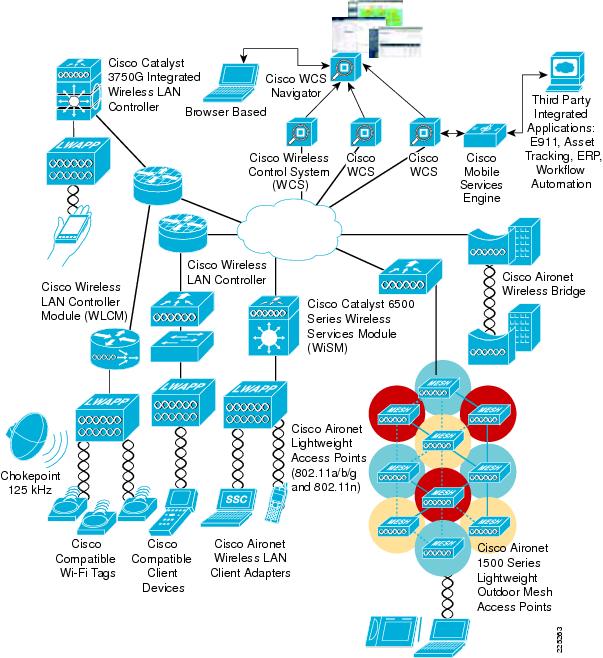
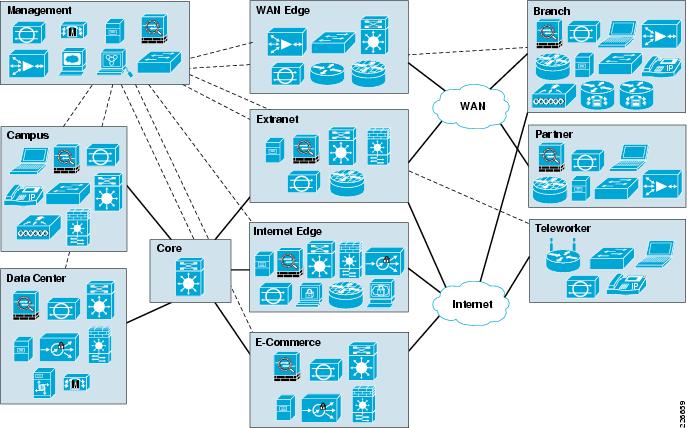
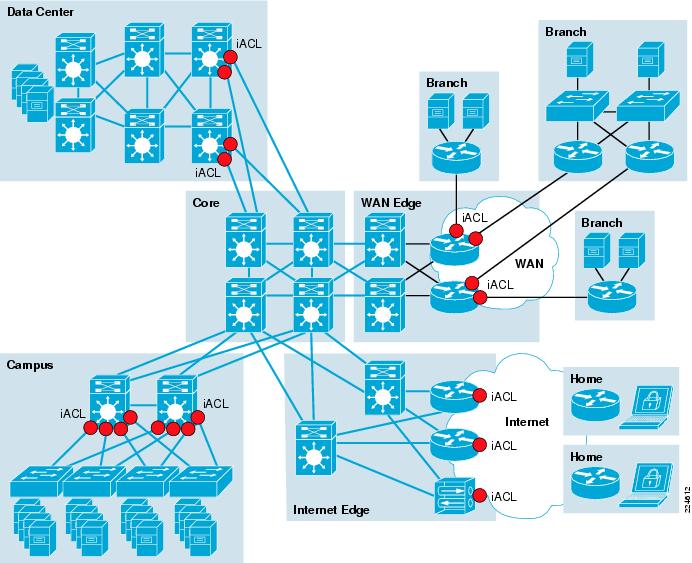
Deploying baseline security features for the the enterprise LAN, WLAN, and for basic network security based on leading practices for typical deployments, RP configuration to remain flexible to change over time and to reduce manual over- |
|
Getting Started with Security Baseline - Cisco
Step 2 Define server groups: Set server groups of all AAA servers If possible, use a separate key per server Set source IP address for TACACS+ or RADIUS |
|
Cisco Network Security Little Black Book
The disadvantage is that manual configuration is needed to populate the database You can also configure the Cisco Secure ACS server to authenticate |
|
Implementing Cisco IOS Network Security (IINS - Cisco Press
She is a Cisco Certified Network Professional (CCNP) and a CCNP Security Catherine is also a Cisco Network Foundation Protection and Cisco Configuration Professional 111 Manual Interface Assignment 291 EUI-64 Interface ID |
|
Network Security
NTW 2000 Network Security Components Source: Cisco Security Posture Assessments network mapper is a utility for port scanning large networks: Viewable in plain text in configuration http://www cert org/reports/ dsit_workshop pdf |
|
Network Security Tutorial
19 fév 2019 · A weakness in security procedures, network design, or implementation that can be xml/ios/iproute_bgp/configuration/xe-3s/irg-xe-3s-book/irg-origin-as pdf • Juniper Packet encapsulation protocol developed by Cisco |
|
Hardening Network Devices - MENOG
Network security includes the detection and prevention of unauthorized access to The attacker broadcasts out an STP configuration/topology change BPDU in Authentication Protocol over LAN (EAPOL), Cisco Discovery Protocol (CDP), |
|
Center for Internet Security Benchmark For Cisco IOS Version 22
No network, system, device, hardware, software, or component can be made fully that is in a txt, pdf , doc, mcw, or rtf format, provided that all such copies are configuration of the router, and the authentication and authorization of router |
|
Cisco IOS Switch Security Configuration Guide
21 jui 2004 · enterprise networks [5]; Cisco's Product Security Advisories and Notices [4]; and NSA's Cisco Router Security Configuration Guide for more details on the principles for http://www nsa gov/snac/routers/cisco_scg-1 1b pdf ) |











![New Version] Best Cisco CCNA Wireless 200-355 Dumps Exam Training New Version] Best Cisco CCNA Wireless 200-355 Dumps Exam Training](https://assets.qwikresume.com/resume-samples/pdf/screenshots/network-security-engineer-1566815736-pdf.jpg)