dolphin attack inaudible voice commands
|
Dolphin Attack: Inaudible Voice Commands 1 Target system
Dolphin Attack: Inaudible Voice Commands 1 Target system service (Contributed by Taehwa Lee and TA) - VCS: Voice Controllabe System - An approach to |
|
DOLPHIN ATTACK: INAUDIBLE VOICE COMMANDS
An approach to inject inaudible voice commands at VCS by exploiting the • Inaudible attacks to SR systems • Dolphin Attack leverages amplitude modulation |
|
DolphinAttack: Inaudible Voice Commands
30 oct 2017 · Since attackers have little control of the VCSs the key of a successful attack is to generate inaudible voice commands at the attacking |
|
DolphinAttack: Inaudible Voice Commands
Machine Learning Attacks Malware DolphinAttack Page 9 How can an attacker exploit this attack? Page 10 How can an attacker exploit this attack? ○ Visiting |
|
Inaudible Voice Commands: The Long-Range Attack and Defense
We attack the system with various ultrasound commands both from literature as well as our own LipRead demonstrates defense against all attacks with 97 |
|
DolphinAttack: Inaudible Voice Commands
30 oct. 2017 less audible. In this work we design a completely inaudible attack |
|
DolphinAttack: Inaudible Voice Commands
An approach to inject inaudible voice commands at voice controllable systems by exploiting the ultrasound How can an attacker exploit this attack? |
|
DolphinAttack: Inaudible Voice Commands
31 août 2017 In this work we design a completely inaudible attack |
|
Inaudible Voice Commands: The Long-Range Attack and Defense
Dolphin and other attacks sidestep this problem by operating at low power thereby forcing the output of the speaker to be almost inaudible. This inher- ently |
|
Inaudible Voice Commands: The Long-Range Attack and Defense
9 avr. 2018 Dolphin and other attacks sidestep this problem by operating at low power thereby forcing the output of the speaker to be almost inaudible. |
|
Robust Sensor Fusion Algorithms Against Voice Command Attacks
2 déc. 2021 voice command (removing the inaudible voice attack commands). ... The Dolphin Attack [9] launched voice commands using ultrasonic carriers ... |
|
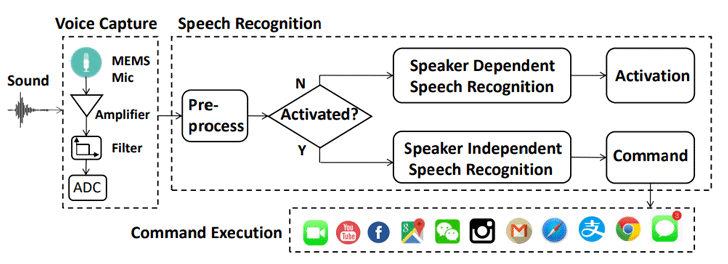
EarArray: Defending against DolphinAttack via Acoustic Attenuation
Thus the demodulated voice command will be the same as normal voice commands making it very difficult to directly detect the inaudible voice commands attack. |
|
A Survey on Amazon Alexa Attack Surfaces
23 févr. 2021 The root cause of dolphin attacks and other inaudible voice commands is that unfortunately most commercial microphones attached to smart ... |
|
Audio Adversarial Examples: Targeted Attacks on Speech-to-Text
30 mars 2018 In the audio space both hidden voice commands and Dolphin Attack's inaudible voice commands are effective over-the-air when played by a speaker ... |
|
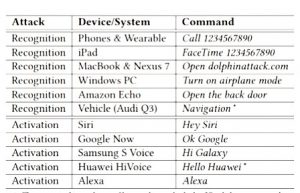
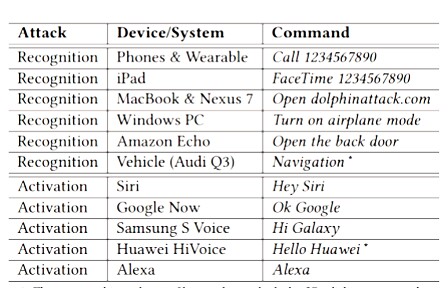
DolphinAttack: Inaudible Voice Commands
Many security studies on voice controllable systems focus on attacking either the speech recognition algorithms [10] or command execution environment (e.g. |
|
DolphinAttack: Inaudible Voice Commands - ACM CCS Blog
30 oct 2017 · less audible In this work, we design a completely inaudible attack, DolphinAttack, that modulates voice commands on ultrasonic carriers (e g , f > |
|
Inaudible Voice Commands: The Long-Range Attack and Defense
Thus, when shi is played through speak- Page 2 ers, it will also undergo the frequency shift, producing an audible slow Dolphin and other attacks sidestep this |
|
Inaudible Voice Commands: The Long-Range Attack and - USENIX
Inaudible Voice Commands: 1 How to launch long-range (realistic) attacks? 50k 60k 70k 80k 90k 100k Amplitude Inaudible Audible Microphone filter |
|
DolphinAttack: Inaudible Voice Commands - Wayne State University
14 nov 2018 · Introduction ▷ Background and Threat model ▷ Attack Design ▷ Feasibility experiments across VCS ▷ Impact quantification ▷ Defenses |
|
DOLPHIN ATTACK - Wayne State University
Dolphin Attack Major Contributions • Attackers can use inaudible sounds (> 20kHz) to activate and control voice Inaudible Voice Command Cancellation |
|
Smart Home Personal Assistants: a Security and Privacy Review
19 mar 2019 · tackle issues related to authorization, speech recognition or profiling, to name a few [37] develop a long-range version of Dolphin attack Likewise, their defense only considers inaudible voice attack ignoring finding the |














![PDF] Inaudible Voice Commands: The Long-Range Attack and Defense PDF] Inaudible Voice Commands: The Long-Range Attack and Defense](https://i1.rgstatic.net/publication/324055823_An_Overview_of_Vulnerabilities_of_Voice_Controlled_Systems/links/5abce11f45851584fa6e7303/largepreview.png)









![PDF] Inaudible Voice Commands: The Long-Range Attack and Defense PDF] Inaudible Voice Commands: The Long-Range Attack and Defense](https://image.slidesharecdn.com/50cf379143925a3926298f881d3c19ab-applicationpdf-170908100206/95/dolphinattack-inaudible-voice-commands-15-638.jpg?cb\u003d1504943361)

