Our problem now is: how many different keys are possible for given. N
|
Global Trends 2030: Alternative Worlds
One of the key looming issues for GT 2030 was “how other powers would respond to a decline or rapidly developing world but the base is now very low. |
|
Lecture 5 - Comparison-based Lower Bounds for Sorting
show that any deterministic comparison-based sorting algorithm must take the problem where now our goal is to do this for g(n) as large as possible. |
|
Key Substance Use and Mental Health Indicators in the United
Aug 4 2019 Rachel N. Lipari and Eunice Park-Lee were the SAMHSA authors. ... However |
|
Assignment 5 - Solutions.docx
May 30 2022 After this exchange |
|
Section 04: Solutions
Section 04: Solutions. Review Problems. 1. AVL Trees. Draw an AVL Tree as each of the following keys are added in the order given. Show intermediate steps. |
|
Finance on the TI-83/TI-83 Plus/TI-84
You can get to the TVM solver by pressing the [FINANCE] key and selecting option 1 on the TI-83 following except there may be different numbers. |
|
Oecd
keys to success in many jobs and will remain and carefully plan the curriculum |
|
Universal and Perfect Hashing
The keys are nicely spread out so that we do not have too many collisions since collisions affect the time to perform lookups and deletes. 2. M = O(N): in |
|
1 Pancakes with a Problem
Sep 22 2016 this (varying the number I flip) as many times as necessary. If there are n pancakes |
|
Note 17
the m keys to be stored and the bins will be the n locations in the hash table third ball lands in a different bin from the first two balls |
|
12 Encryption keys - Introduction to cyber security: stay safe online
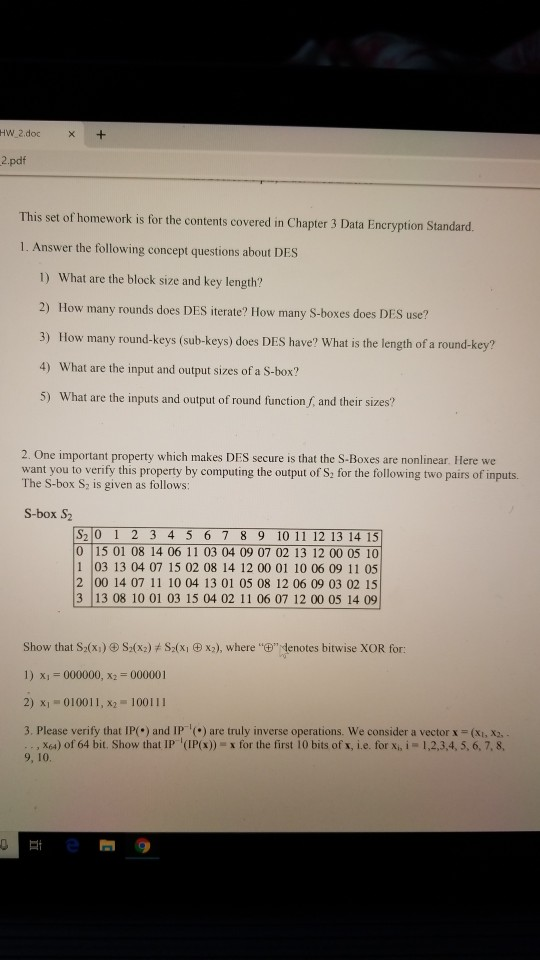
Order does matter in a password and the problem specifies that you can repeat letters So you need a permutations with repetitions formula The different ways you can arrange the letters = 17576 The different ways you can arrange the digits = = 1000 So the number of possible passwords = 17576 × 1000 = 17576000 passwords |
|
Combinatorics and Probability - Stanford University
There are kndi?erent assignments when there are n items and each item is to be assigned one of k values For instance in Example 4 1 we had n = 4 items the houses and k = 3 values the colors We calculated that there were 81 di?erent assignments Note that 34= 81 We can prove the general rule by an induction on n |
How many possible values can a key have?
The number of possible values for a key is simply the total number of values that the key can have. So our one-bit long key can only have two possible values – 0 and 1. If we choose to have a two-bit key it could have one of four possible values – 00, 01, 10 and 11.
How many values can a 3 bit key have?
In fact every time we increase the length of the key by one bit we double the number of possible keys – so a three-bit key has eight possible values – 000, 001, 010, 011, 100, 101, 110 and 111. The total number of keys can be written in scientific form as 2 key length; so a key with a length of eight has 2 8 – that is 256 – values.
How do you divide a problem into three subproblems?
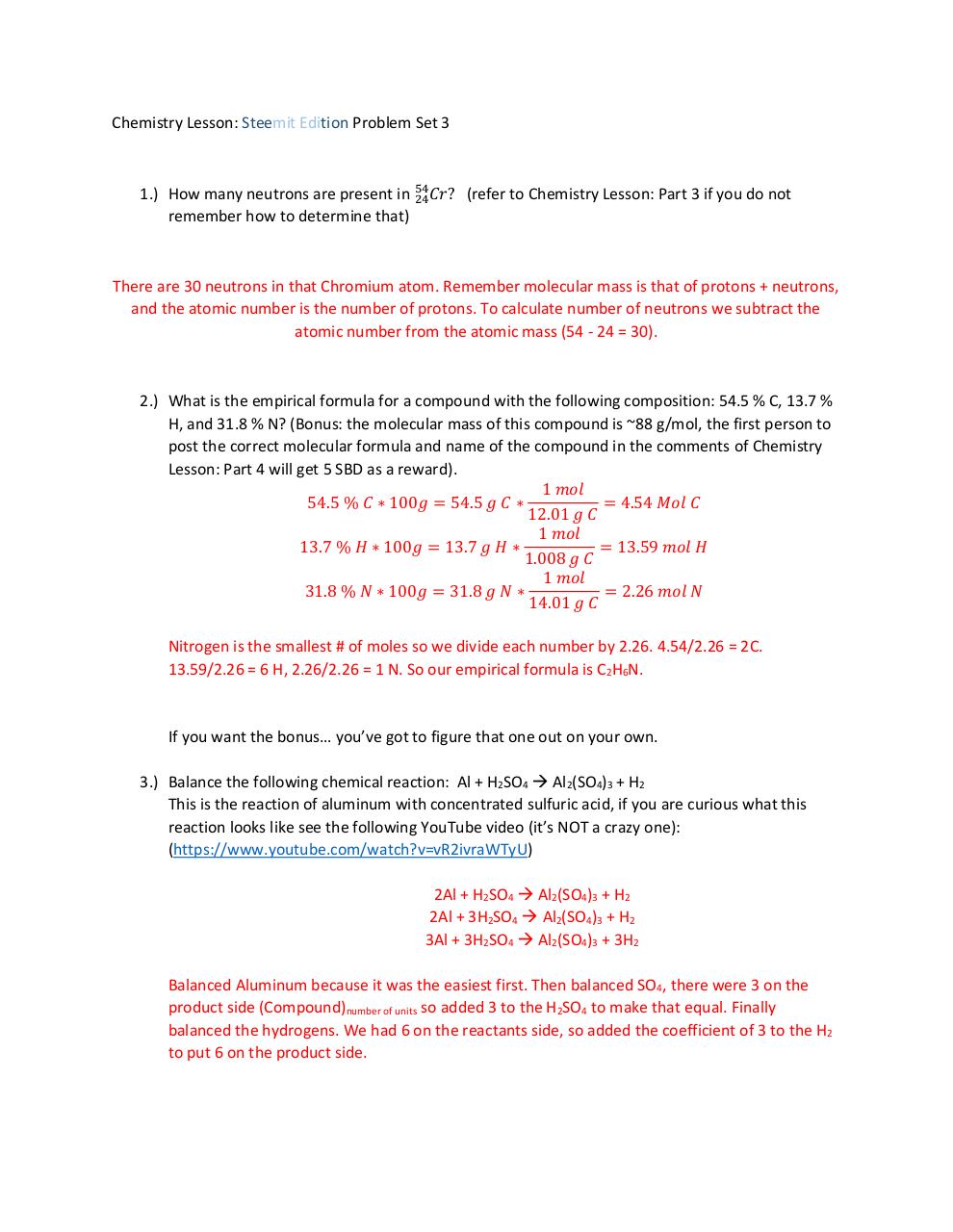
Another approach is to dividethe problem into three subproblems, depending on whether the number of di?erentnumbers showing is 3, 2, or 1. We can count the number of outcomes with three di?erent numbers using thetechnique of Section 4.5. That is, we must select 3 out of the 6possible numberson a die, and we can do so in63= 20 di?erent ways.
What are two paths with no consistent order?
Thetwo paths with noconsistent order never occur. Equation (4.2) tells us that the number of teststmust be at least log23!, which is log26. Since 6 is between 22and 23, we know thatlog26 will be between 2 and 3. Thus, at least some sequences of outcomes in anyalgorithm that sorts three elements must make 3 tests.
|
Public-Key Cryptography RSA Attacks against RSA
The public-key K may be made publicly available, e g , in a publicly available the range [1,pq-1] that are relatively prime to both p and q • The size of Z n * is |
|
Permutations, Combinations and Probability 1 - NUI Galway
eration has m possible outcomes and that a second operation has n Notice that in each case the number of arrangements is given by: How many different five- digit numbers can be formed from the digits, 1, 2, 3, 4 and 5 if: to deal with problems where objects are chosen from two different groups now be selected ? |
|
Affine Ciphers An affine cipher, (like a shift cipher), is an example of
cipher, each time a given letter occurs in the plaintext, it always is replaced by the The encryption key for an affine cipher is an ordered pair of integers, both of { 0, ,n − 1}, where n is the size of the character set being used (for us, the character set is the Now use the table to replace the numbers from step iii with their |
|
Lattice-Inspired Broadcast Encryption and Succinct Ciphertext
The first solution to the broadcast encryption problem was proposed by Boneh, a special case of another cryptographic task which is by itself very interesting, of the scheme scale polynomially with k, d, and in addition, the key size may Using this evaluation procedure, it is possible, given the ciphertext and f,x, to derive |
|
Practical Isogeny-Based Key-exchange with Optimal Tightness
most efficient implementation under the given security constraints Although SIDH-based schemes have been around for a few years now, there are In particular, random self-reducibility of SIDH problems is very hard to achieve A different isogeny-based scheme is CSIDH [CLM+18]: introduced in 2018, it offers a much |
|
A Formal Theory of Key Conjuring - LORIA
plain the security problem we are interested in, and define a restricted class key conjuring operations are of no use to the intruder, and keys into various types, such as data keys, PIN derivation keys We now define our (mostly standard) notation for reason- In Figure 1, we give the symmetric key management subset |
|
Applications of elliptic curves in cryptography and computational
Lectures given during CIMPA summer school Algebraic many different m , and will know a number of no secret keys ever need to be exchanged over the Now user U chooses an integer that the Discrete Logarithm Problem (DLP) in a |
|
Public-key Encryption in a Multi-User Setting: Security - UCSD CSE
problem: in the real world there are many users, each with a public key, sending known attacks, we have no guarantee of security against other similar attacks encryption key is secret, meaning not given to the adversary the security of the El Gamal scheme in the single-user setting; our concern now is the multi-user |