identity and access management
|
Identity and Access Management
This platform provides a comprehensive view of users across all of the entity's business and utility operations silos and the access rights granted those users |
|
Identity and Access Management/Governance
In 2015 CLUSIF decided to produce a new document on Identity Access Management (IAM)/Identity Access Governance (IAG) drawing on plentiful feedback from |
|
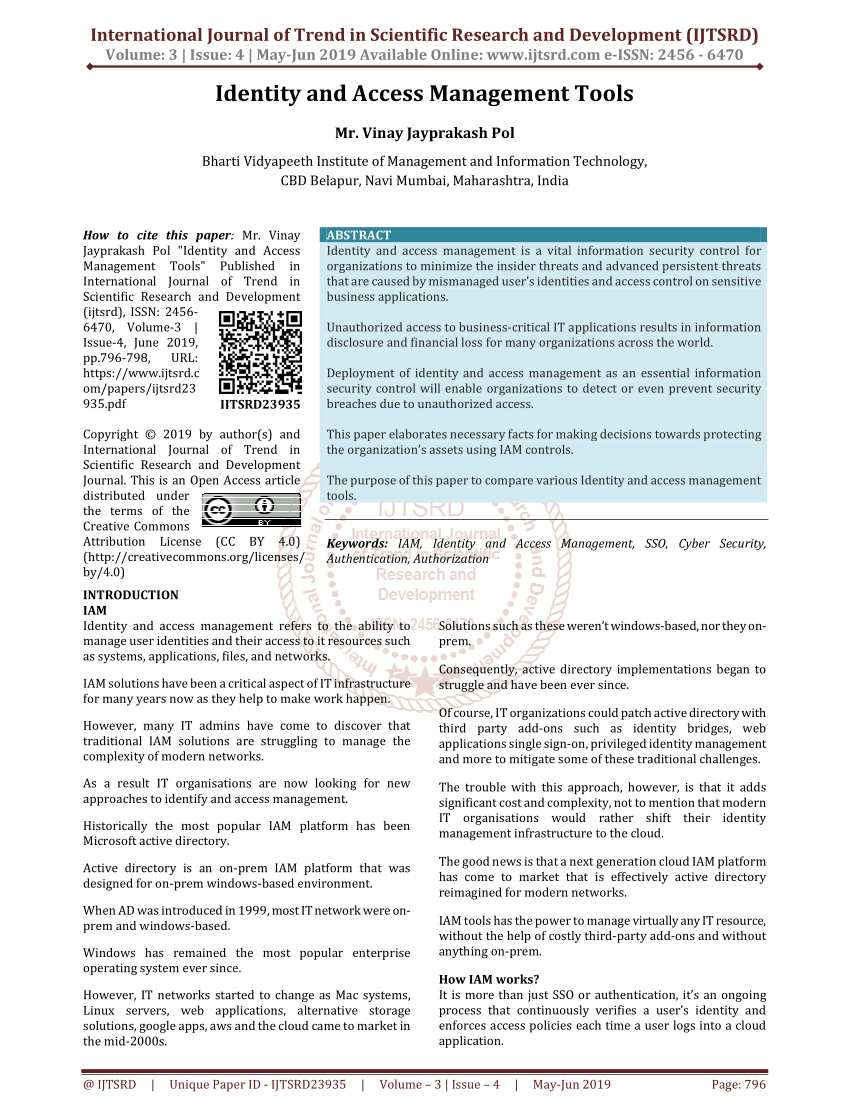
IDENTITY AND ACCESS MANAGEMENT: CONCEPT
Abstract: Identity and Access Management is important in today's evolving world It is the process of managing who has access to what information over time |
|
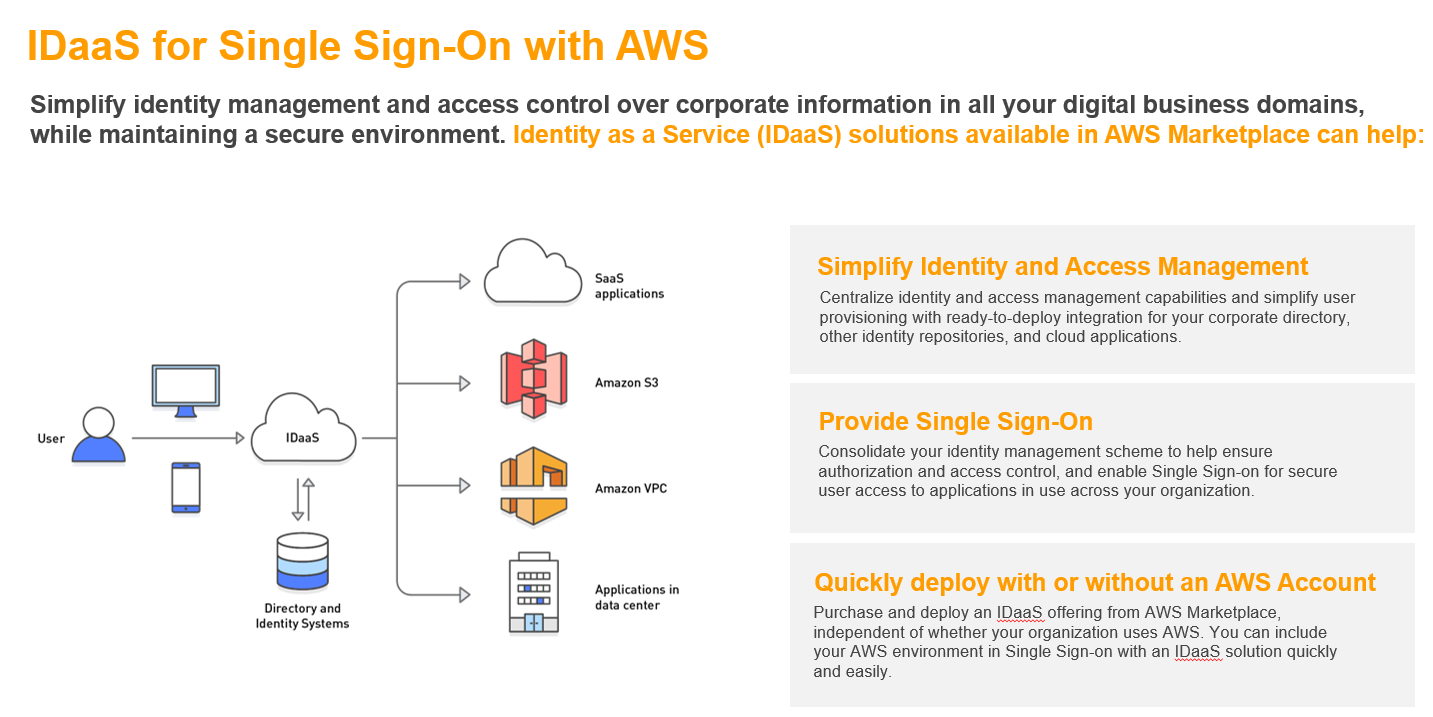
Complete identity and access management (IAM)
One Identity provides a comprehensive access management solution portfolio that complements existing IAM setup for AWS Centralized identity management |
|
Identity and Access Management Overview
IdM manages an identity's lifecycle through a combination of processes organizational structure and enabling technologies Processes Page 6 6 Identity and |
|
IDENTITY AND ACCESS MANAGEMENT PROGRAM OVERVIEW
Identity and Access Management refers to a set of business processes and supporting technologies that enable the creation maintenance and use of a digital |
|
Identity and Access Management PROGRAM PLAN
The purpose of this plan is to provide a comprehensive overview of all facets of the Identity and Access Management (IAM) program within a three-year horizon |
|
Identity and Access Management Recommended Best Practices for
21 mar 2023 · pdf Page 23 Identity and Access Management: Recommended Best Practices for Administrators 19 It is important to note that organizations may |
|
Identity and Access Management
This platform is described in this NIST cybersecurity Identity and Access Management practice guide pdf Page 109 NIST SP 1800-2C: Identity and Access |
It boosts security and provides greater control of user access to your system.
This helps organizations mitigate data breaches, identity theft and illegal access to sensitive corporate information.
What is the role of IAM?
An IAM role is an IAM identity that you can create in your account that has specific permissions.
An IAM role is similar to an IAM user, in that it is an AWS identity with permission policies that determine what the identity can and cannot do in AWS.
Is Active Directory an IAM?
To protect the data, companies must control who has access to private information and what they can do with it.
This is where Identity and Access Management systems come in and, by extension, Active Directory.
What does IAM mean?
AWS Identity and Access Management (IAM) is a web service that helps you securely control access to AWS resources.
With IAM, you can centrally manage permissions that control which AWS resources users can access.
You use IAM to control who is authenticated (signed in) and authorized (has permissions) to use resources.
|
AWS Identity and Access Management - Guía del usuario
Uso de IAM para dar a los usuarios acceso a sus recursos de AWS. AWS Identity and Access Management (IAM) es un servicio web que lo ayuda a controlar de ... |
|
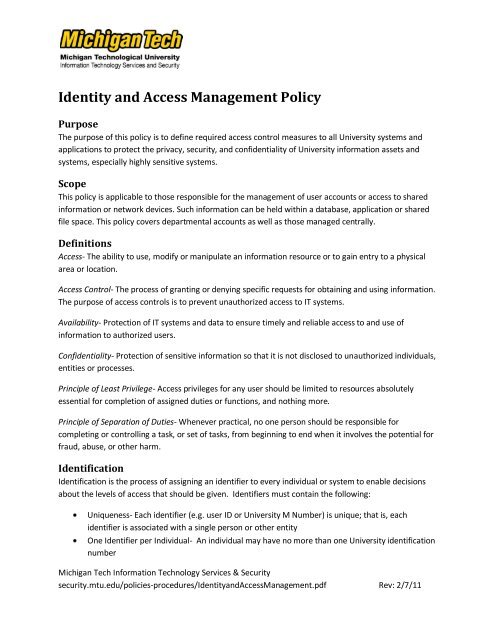
VA Identity and Access Management
15 ene 2016 implement VA Directive 6510 VA Identity and Access Management |
|
VA Identity and Access Management
15 ene 2016 PURPOSE: This Directive defines the policies for enterprise identity and access management (IAM) for the Department of Veterans Affairs (VA). |
|
AWS Identity and Access Management - User Guide
5 nov 2013 Using IAM to give users access to your AWS resources . ... Creating an IAM admin user and user group . |
|
Participant Portal Identity and Access Management (IAM)
The main principles of the identity and access management (IAM) do not change: • Access rights of a person are based on an ECAS account (European Commission. |
|
Funding & Tenders Portal Identity and Access Management (IAM)
Each EU Login account is linked to all the roles that the user has in projects and/or organisations through IAM. One user can have as many roles as necessary. |
|
Título de una o dos líneas si es necesario
Identity and Access. Management. Tendencia Global Identity Management. • Conclusiones ... Arquitectura Global de IAM. |
|
Identity and Access Management (IAM)
worried it's not very secure.” OUTCOMES OF A SUCCESSFUL IAM PROGRAM. REDUCE. AUDIT EXPOSURE. OPERATIONS CHANGE. MANAGEMENT. DRIVE ADOPTION |
|
National HIE Governance Forum - Identity and Access Management
20 dic 2013 Identity and Access. Management for Health. Information Exchange. The Level of Assurance (LOA) Continuum: A resource for governing entities ... |
|
Additional License Authorizations for Identity and Access
5 jul 2021 If an Identity and Access Management product is not listed below the product-specific license terms in the end user license agreement (EULA) ... |
|
7 DRIVERS TRANSFORMING IDENTITY & ACCESS - Wavestone
1 IAM ON THE CUSP OF CHANGE In the context of IAM, organisations have traditionally focused on managing identities and controlling who accesses what |
|
Identity and Access Management - Capgemini
Identity and Access Management is a central asset in today's enterprise landscape It comprises processes and information technologies that are interrelated and |
|
The Challenges and Benefits of Identity and Access Management
Strong IAM solutions can enable enterprises to boost employee productivity and bolster their overall security postures However, the growth of cloud computing |
|
Cloud and Identity and Access Management - Deloitte
A sound IAM strategy is also fundamental for an effective migration to the cloud as it provides for an integrated access solution that is cost-effective, agile, and |
|
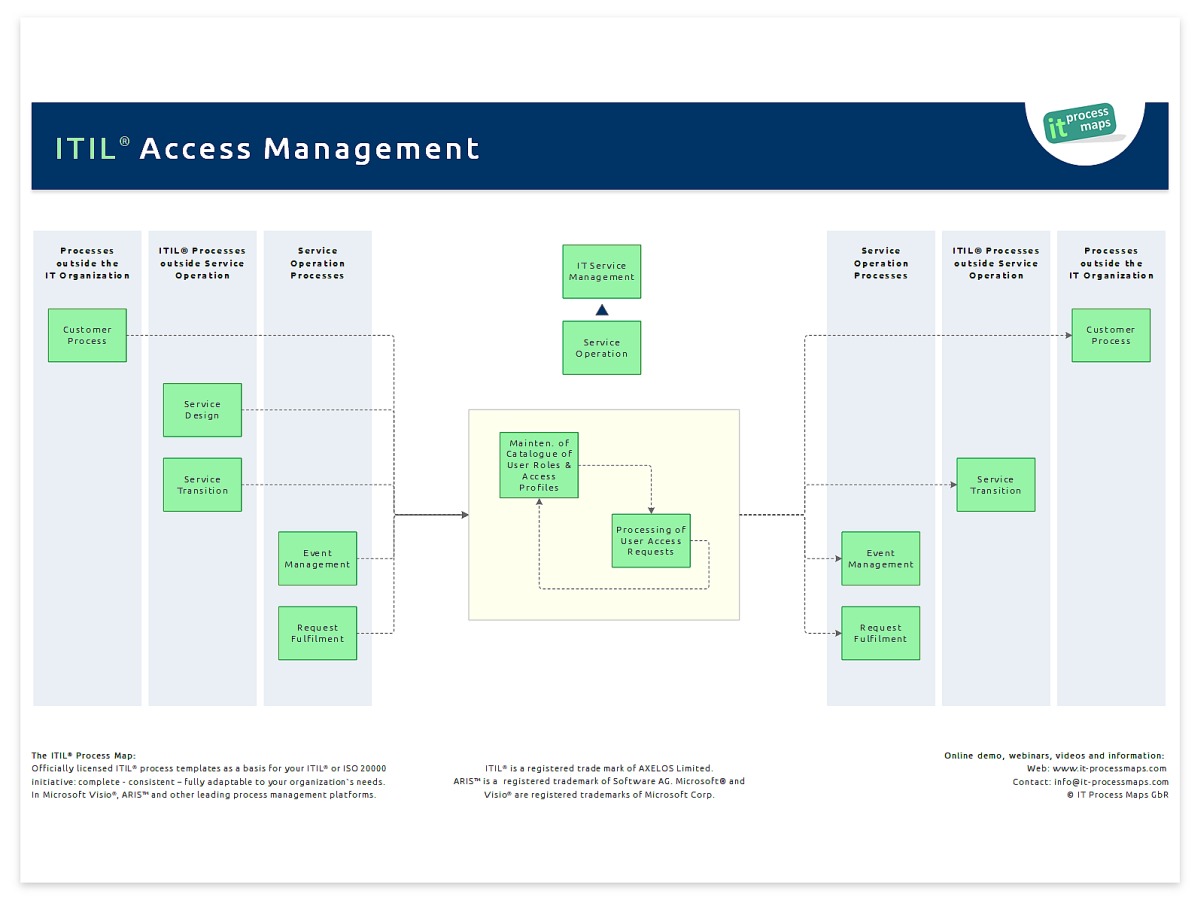
IDENTITY AND ACCESS MANAGEMENT PROGRAM OVERVIEW
Identity and Access Management refers to a set of business processes and supporting technologies that enable the creation, maintenance, and use of a digital identity |
|
Identity & Access Management - assetskpmg
regulatory pitfalls Identity Access Management KPMG provides services around the planning, design, delivery and support of comprehensive enterprise, |
|
Identity and Access Management PROGRAM PLAN - Harvard Web
The IAM program originated from the need to eliminate perceived complexities surrounding identity Above all, the IAM program's activities and deliverables will |

![PDF~] Mastering Identity and Access Management with Microsoft Azure PDF~] Mastering Identity and Access Management with Microsoft Azure](https://0.academia-photos.com/attachment_thumbnails/33860258/mini_magick20190328-14863-yobv9f.png?1553811639)




![Consumer Identity \u0026 Access by SIMON MOFFATT [PDF/iPad/Kindle] Consumer Identity \u0026 Access by SIMON MOFFATT [PDF/iPad/Kindle]](https://dbac8a2e962120c65098-4d6abce208e5e17c2085b466b98c2083.ssl.cf1.rackcdn.com/identity-access-management-for-real-world-access-management-pdf-3-w-1638.jpg)



























![Compliance \u0026 Identity access management - [PDF Document] Compliance \u0026 Identity access management - [PDF Document]](https://online.pubhtml5.com/yonr/nppp/files/large/2.jpg)