mdm byod policy
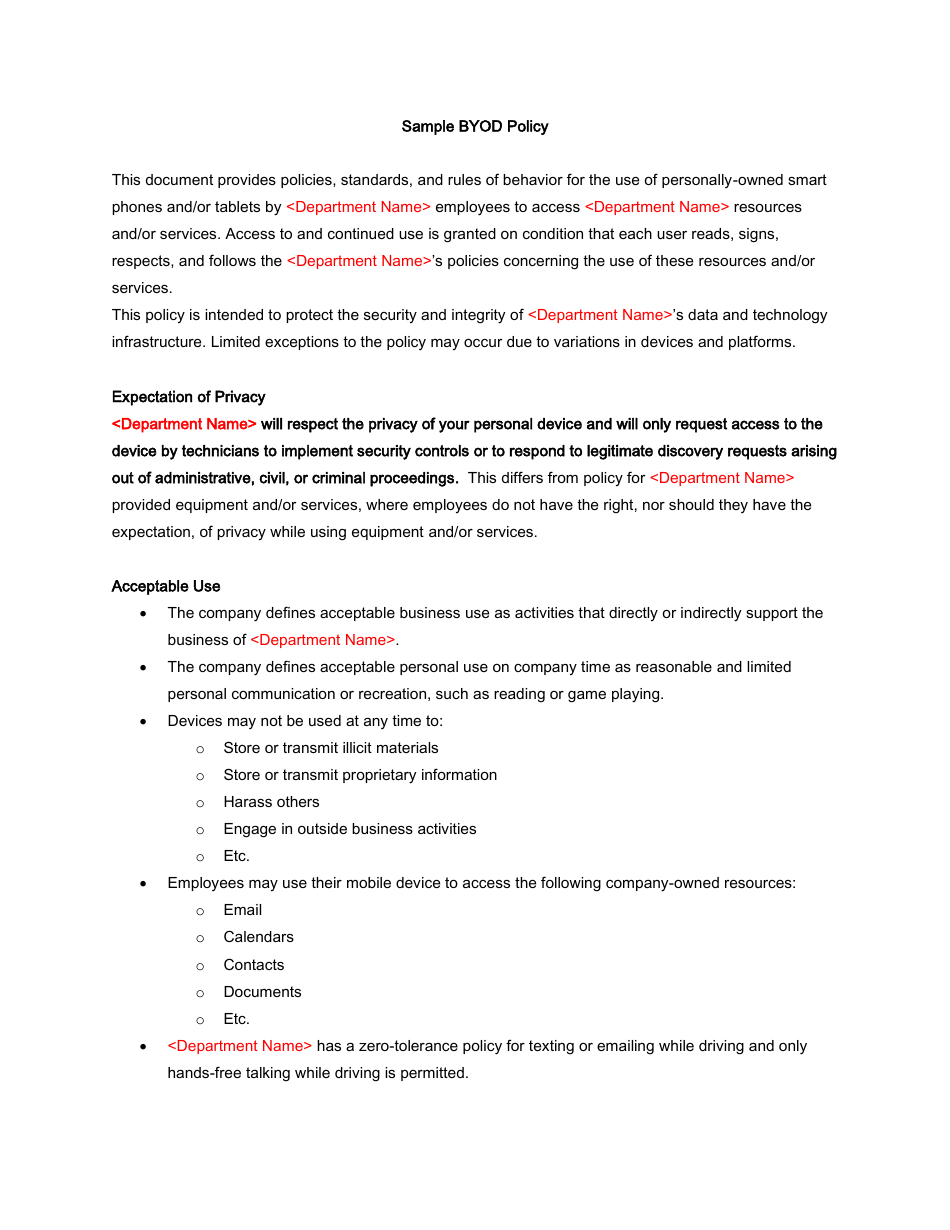
Passwords and other confidential data, as defined by [company name]'s IT department, are not to be stored unencrypted on mobile devices.
Any mobile device that is being used to store or access [company name] data must adhere to the authentication requirements of [company name]'s IT department.
How does MDM work with BYOD?
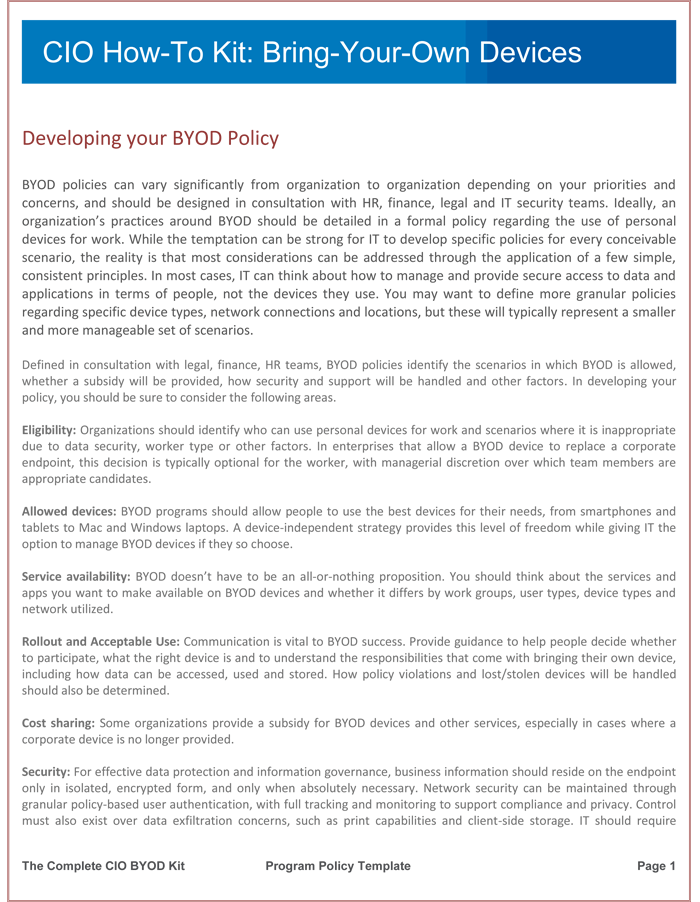
With BYOD, employees use their own devices to work, whereas Mobile Device Management usually applies to company-owned devices.
However, MDM and BYOD can sometimes be used simultaneously, if MDM software is installed on employees' personal devices.16 août 2022
What is a MDM policy?
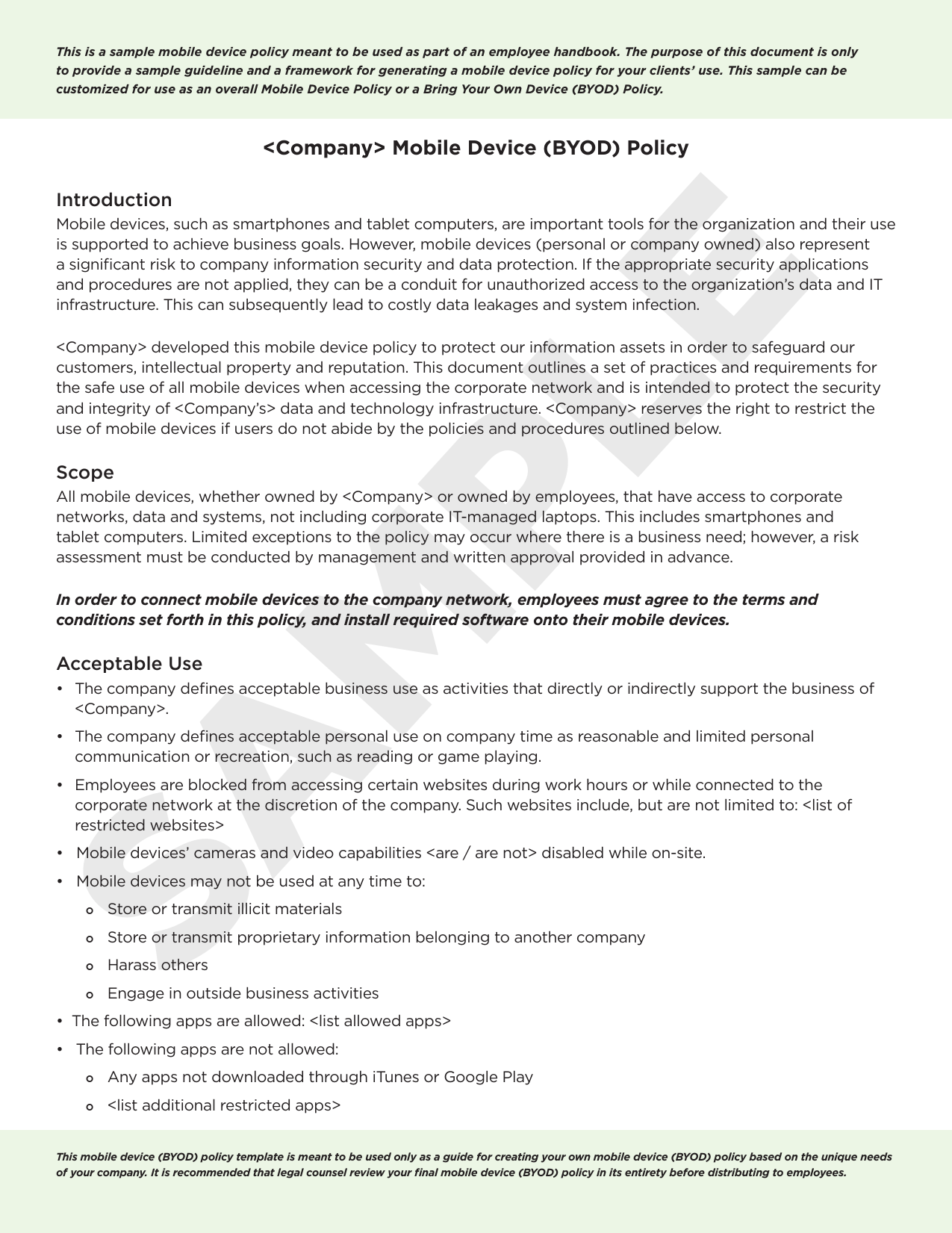
What Is a Mobile Device Management Policy? A mobile device management policy establishes rules for how mobile devices are used and secured within your company.
Without mobile usage guidelines, you leave your company open to cybersecurity threats, theft and corporate espionage attempts.
|
BYOD Policy for Microsoft Intune Devices - Deployment Guide
May 15 2020 The device access management framework leverages mobile device management (MDM) services so that you can use familiar Pulse Connect Secure ... |
|
Bring Your Own Device Policy APPLICABILITY: I. Description II
The BYOD program includes this Policy accessibility technology |
|
Mobile Device Security: Bring Your Own Device (BYOD)
Mar 18 2021 Mobile Device Management that provisions configuration profiles to mobile devices |
|
Apple Business
framework and your mobile device management (MDM) solution. User-owned devices also known as “bring your own device” (BYOD) |
|
Definitions – Terms Specific to the Policy
Title Bring Your Own Device (BYOD) (MDM) software secures monitors |
|
Ten rules for Bring Your Own Device (BYOD)
To effectively use mobile device management (MDM) technology for employee owned devices you still need to decide on policies. These policies affect more. |
|
Airwatch MDM and Android: a policy and technical review
This paper examines the use of AirWatch as a Mobile Device Management Platform. Page 3. Android BYOD |
|
Commonwealth of Virginia
Feb 1 2022 COV & Bring Your Own Device ... Objective 4: Identify the rules for BYOD smart devices. Purpose ... Mobile Device Management. (MDM). |
|
DoD Mobility
Jun 17 2015 Mobile Device Management / ... Policy. Automatic App Vetting. Computer Network Defense ... + Bring Your Own Device (BYOD). |
|
The New BYOD: Best Practices for a Productive BYOD Program
An MDM solution such as AirWatch which supports all major device The BYOD policy should clearly define the rules of the program |
|
Sample Mobile Device Security Policy - Sophos
Mobile Device Management systems and policies Security must be central to an organization's workforce mobility strategy in order to protect corporate data, |
|
ICT Security Policy - Southern Health NHS Foundation Trust
3 juil 2020 · Bring Your Own Device, BYOD, Personal Devices, Mobile Working, Tablet, Smartphone, Mobile Device Management, MDM Target audience |
|
IDENTIFYING BEST PRACTICES FOR A BYOD POLICY - CORE
Keywords: byod, bring your own device, byot, bring your own technology, byod Management - MDM) and non-technical (e g ICT or BYOD security policies) |
|
Best practices with BYOD - NCC Group Research
While the use of BYOD, as well as Mobile Device Management (MDM) systems password policy complying with security industry best practice as well as the |
|
Enabling Bring Your Own Device (BYOD) In the Enterprise
Enabling Bring Your Own Device (BYOD) In the Enterprise v 2012 10 When these devices are not secured by Mobile Device Management (MDM), this |
|
Regulatory Considerations for BYOD Policies - Attachmate History
The introduction of MDM platforms as a part of BYOD policy provides a solution to many issues introduced by regulation: control and security over corporate data |
|
Understanding the Bring-Your-Own- Device landscape By - Deloitte
Bring-Your-Own-Device (BYOD) is not a single idea or way of working Rather it Mobile Device Management (MDM) or a secure container approach |
|
Mobile Device Policy with BYOD - INgov
Employee agreement to allow IT to load a mobile device management software agent and any other software deemed necessary by the organization on |












-Policy-Template.jpeg)
![BYOD (Bring your own device) Policy Template [Free PDF] - Word BYOD (Bring your own device) Policy Template [Free PDF] - Word](https://kooringal-h.schools.nsw.gov.au/content/dam/doe/sws/schools/k/kooringal-h/localcontent/BYOD.jpg.thumb.1280.1280.jpg)