annotated bibliography hacks
|
Annotated Bibliography Cheat Sheet
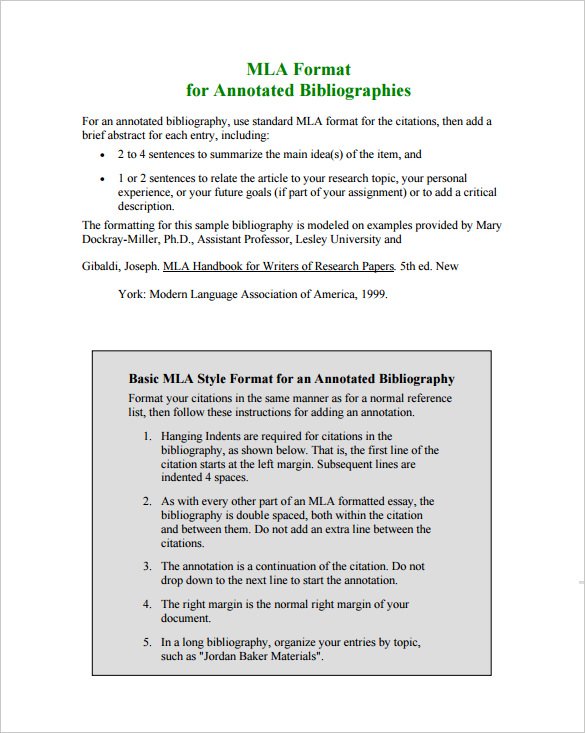
Annotated Bibliography Cheat Sheet The list should be titled “Annotated Bibliography” or “Annotated List of Works Cited ” The list can be organized alphabetically by author or title (as for a normal list of works cited) by date of publication or by subject |
|
ANNOTATED BIBLIOGRAPHY
An annotated bibliography can be a useful step in your research process helping you understand your topic narrow your focus and develop your thesis Annotated bibliographies may be standalone assignments or they may be part of larger research projects Writing an annotated bibliography is an effective way for you to determine if the sources |

APA-MLA Annotated Bibliography: Complete Guide to the Annotated Bib Part 4

APA-MLA Annotated Bibliography: Complete Guide to the Annotated Bib Part 2

APA-MLA Annotated Bibliography: Complete Guide to Writing the Annotated Bib Part 1
|
CYBERCRIME: AN ANNOTATED BIBLIOGRAPHY OF SELECT
Hackers obtain botnets commercially using them to access bank accounts. Page 6. Library of Congress – Federal Research Division. Cybercrime: An Annotated |
|
ANNOTATED BIBLIOGRAPHY OF GEORGIA GEOLOGY 1965
Georgia: Hack J. T. |
|
Hacks Cracks
https://core.ac.uk/download/pdf/217321721.pdf |
|
Cyber Terrorism Research Review
1 июн. 2017 г. Annotated Bibliography - Legislation & Countermeasures ... Menn and Volz's online news article provides an analysis on the hacks against Dyn Corp. |
|
A Pocket Style Manual by Diana Hacker
> Model papers > MLA annotated bibliography: Orlov. > APA annotated bibliography: Haddad. 1. 2. 3. 4. Page 111. 28c res. 101 keeping records • annotated |
|
Cyber Terrorism Research Review
29 июн. 2017 г. Annotated Bibliography - Propaganda Radicalisation and Recruitment. ... Menn and Volz's online news article provides an analysis on the hacks ... |
|
Smuggling of Migrants: A Global Review and Annotated
The description and classification of countries and territories in this study and the arrangement of the material do not imply the expression of any opinion |
|
An Annotated Bibliography on Research by Design
and Hack G. 1984. Site Planning 1 |
|
The
The so ware used in the cyber-attack was FinSpy which was produced by Gamma Group |
|
CYBERCRIME: AN ANNOTATED BIBLIOGRAPHY OF SELECT
An Annotated Bibliography Prepared by the Federal Research Division particular crimes: spamming |
|
Novels and Short Stories about Work: An Annotated Bibliography.
Novels and Short Stories about Work: An Annotated. Bibliography. INSTITUTION. National Center for Research in Vocational Education. Berkeley |
|
Edward A. Hacker. The I Ching Handbook: A Practical Guide to
annotated bibliography (see the Preface p. vii). The author is not a sinologist |
|
Cyber Terrorism Research Review
Jun 29 2017 Hacking Financial Institutions and Money Laundering. 86. Drug-Terror System in Afghanistan. 87. Annotated Bibliography - Financing Terrorism. |
|
Online Child Exploitation Material – Trends and emerging Issues
Nov 4 2016 Annotated Bibliography – Live Streaming of CEM . ... Annotated Bibliography - Hacking & Phishing . |
|
HackEd: A Pedagogical Analysis of Online Vulnerability Discovery
HackEd: A Pedagogical Analysis of Online Vulnerability Discovery Exercises annotated bibliography. maa notes number 1. 1983. [79] SDSLabs. backdoor. |
|
Hacker-MLA-Handbook.pdf
An in-text citation names the author of the source often in a signal phrase |
|
Citizen
This Annotated Bibliography compiles and summarizes relevant literature on Bahraini Activists Hacked by Their Government Go A er UK Spyware Maker. |
|
Ransomware: Hostage Situation
This annotated bibliography explores literature on the issues of malware and ransomware attacks its nature |
|
Running head: SAMPLE ANNOTATED BIBLIOGRAPHY 1 Sample
project or paper, an annotated bibliography follows each source with a short “ annotation,” http://dianahacker com/ pdf s/Hacker-Haddad-APA-AnnBib pdf |
|
CYBERCRIME - Office of Justice Programs
This annotated bibliography reviews the findings of major academic research particular crimes: spamming, cyber stalking, hacking, infecting computers with |
|
An Annotated Bibliography on Research by Design - Publications
Lynch and Hack identify twelve design methods: 1) learning probes 2) subconscious suggestion, 3) brainstorming, 4) evaluation criteria, 5) well spaced |
|
CYBERCRIME - New OJP Resources Office of Justice Programs
An Annotated Bibliography Prepared by the Federal Research Division, particular crimes: spamming, cyber stalking, hacking, infecting computers with viruses, |
|
Sample APA Formatted Paper
31 oct 2004 · Marginal annotations indicate APA-style formatting and effective writing Sample APA Formatted Paper Page 2 Source: Diana Hacker (Boston: |
|
An Annotated Bibliography - University of Washington
30 jui 2014 · The Practice of Science 2014 - an Annotated Bibliography I've focused Hale- Evans, Ron (2006) Mind Performance Hacks: Tips and Tools for |
|
Annotated Bibliography - The Citizen Lab
7 oct 2020 · This Annotated Bibliography compiles and summarizes relevant Bahraini Activists Hacked by Their Government Go After UK Spyware Maker |