seteuid exploit
|
Automatic Generation of Data-Oriented Exploits
7 seteuid(0); //set root uid 8 9 seteuid(pw->pw_uid); //set normal uid 10 5 I 0 0 0 Attack 0 Page 32 Pointer Stitch • Corrupt pointers to |
Our Expectation on Audit Daemon
As a threat hunter, our focus is unlike penetration tester nor intruder. While their mission is crytal clear that after gained the low-priv access, is to discover possible security loophole to get the privilege escalation. In fact, we do not know the unknown. What we can do is to capture what is happened. In this case, we know the uid is gonna be s
The Auditd Rule
Audit.rule as the engine of the audit daemon. Without it, no usable information can be captured to solve the puzzle. From part 1, I have mentioned bfuzzy’s auditd rules pack. Below rules would be triggered in this priv-esc technique. medium.com
Capture The setuid Priv-Esc
This exploit basically brought up these 9 events. As you can see, the privilege escalation completed from Process ID (pid) 22215 and pid 22216. And the suid was changed from 1000(bob) to 0(root) while executing bash command (syscall 59). The idea of detecting the priv-esc from altering suid/gid is leveraging cumulative concept in your search. In ot
|
PoLPer: Process-Aware Restriction of Over-Privileged Setuid Calls
Unrestricted capabilities to run setuid calls pose the risk that such code can be exploited through a vulnerability. Inferring Process Behavior Role with a |
|
Automatic Generation of Data-Oriented Exploits
set normal user privilege seteuid(pw->pw_uid);. // execute user's command. Data-Oriented Exploits. • State-of-the-art: Corrupt security-critical data. |
|
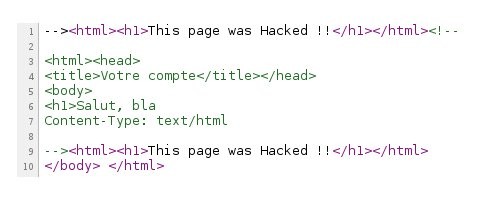
Race Condition Vulnerability
– In Unix we can use seteuid() or setuid() system calls. to disable/enable or delete the power. /* disable the root privilege */. #include <unistd.h>. #include |
|
Setuid Demystified
The vulnerability was caused by the overloaded seman- tics of setuid. Depending on whether a process has the. SETUID capability setuid sets one user ID or all |
|
Automatic Generation of Data-Oriented Exploits
set normal user privilege seteuid(pw->pw_uid);. // execute user's command. Data-Oriented Exploits. • State-of-the-art: Corrupt security-critical data. |
|
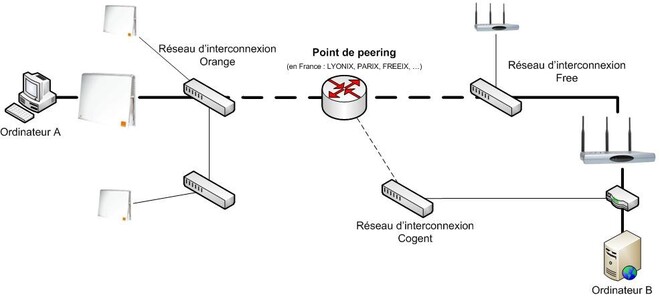
Overview
Forks child process that execs a setuid-root program pt_chown. ? Changes ownership and permissions of Chances of exploit can be greatly increased by:. |
|
MagniComps SysInfo root setuid() Local Privilege Escalation
23 thg 9 2016 The vulnerability exists in .mcsiwrapper. The wrapper relies on the canonical path supplied by the shell to determine its location. |
|
Return-to-libc
Let's take an example on how we are going to exploit it. the first printf should overwrite the argument to setuid and 2nd printf should overwrite the ... |
|
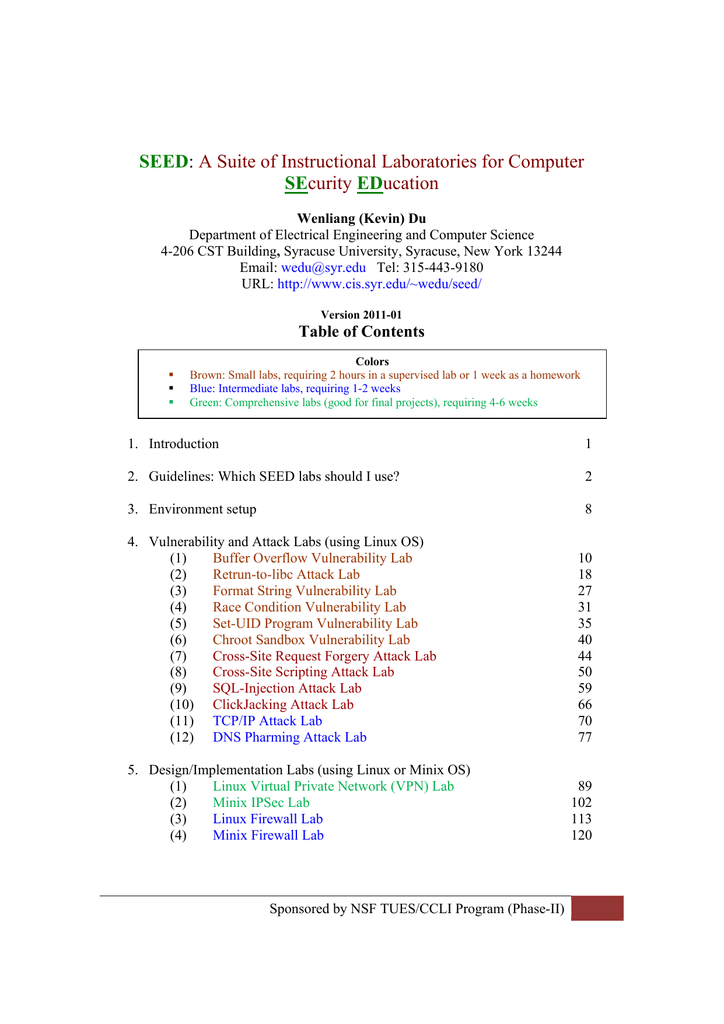
Simple Exploits
Goal: discuss typical vulnerabilities & exploits in Linux. o misspelling exploit ... root) available to everyone via a setuid script: #!/bin/bash –p. |
|
PoLPer: Process-Aware Restriction of Over-Privileged Setuid Calls
Unrestricted capabilities to run setuid calls pose the risk that such code can be exploited through a vulnerability. Inferring Process Behavior Role with a |
|
Set-UID Privileged Programs - Syracuse University
Can you exploit this to cause more severe damage to wedu? seteuid(uid): It sets the effective user ID for the calling process ∗ If the effective user ID of the |
|
Setuid Demystified - UMD CS
The vulnerability was caused by the overloaded seman- tics of setuid Depending on whether a process has the SETUID capability, setuid sets one user ID or all |
|
CS 380S - Theory and Practice of Secure Systems
s setuid, setgid (if directory, files have gid of dir owner) 99 of local vulnerabilities in UNIX systems exploit setuid-root programs to obtain root privileges |
|
Writing Secure Privileged Programs - man7org
Setuid-root program == setuid program owned by root if (seteuid(getuid()) == -1 ) /* Drop privileges */ Chances of exploit can be greatly increased by: |
|
CSC 591 Systems Attacks and Defenses Linux Security
reliably exploiting uninitialized uses on the kernel stack has been int seteuid( uid_t uid) call to setuid(getuid()) to clear privileges (effective UID is root) |
|
Exploiting environment variables
3 oct 2020 · program will call setuid(uid) when we log into the system Let us now try to exploit the second possible attack vector: vulnerable set-uid |
|
Process-Aware Restriction of Over-Privileged Setuid Calls in Legacy
uid to the root ID value using the format string vulnerability in the sudo_debug function as shown in Figure 5 PoLPer detects this attack using a data context shown |
|
PoLPer: Process-Aware Restriction of Over-Privileged Setuid Calls
Real-world Exploits Exploit Pattern Vul Program Exploit Name (EDB) Setuid Syscall Exploited Detected PoLPer CFI NCI Modify Setuid Parameters Sudo |
|
Return-to-libc tutorial
Let's take an example on how we are going to exploit it the first printf should overwrite the argument to setuid and 2nd printf should overwrite the last argument |




![PDF] Principles of Data Flow Integrity: Specification and PDF] Principles of Data Flow Integrity: Specification and](https://img.yumpu.com/18030002/1/500x640/advanced-return-to-libc-exploits.jpg)
![PDF] Support de cours complet sur les bases du hacking methodes et PDF] Support de cours complet sur les bases du hacking methodes et](https://media.springernature.com/original/springer-static/image/chp%3A10.1007%2F978-3-319-47364-2_52/MediaObjects/432299_1_En_52_Fig1_HTML.png)





![PDF] Support de cours complet sur les bases du hacking methodes et PDF] Support de cours complet sur les bases du hacking methodes et](https://slideplayer.com/slide/15975839/88/images/16/Windows+Security+Model.jpg)
