symlink race condition
How do you solve race condition?
To solve race conditions, various concurrency control techniques can be used.
These techniques allow the database to manage concurrent access to shared data in a controlled manner and can help to prevent race conditions from occurring.What are race conditions in vulnerability?
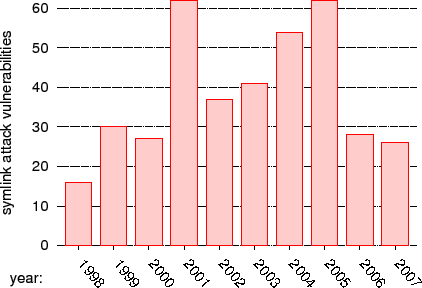
Race conditions occur when a system/ device attempts to execute multiple threads concurrently.
But the threads don't get executed in the correct sequence for several reasons.
Attackers may exploit race conditions to execute malicious activities and evade security mechanisms.Programmers use dynamic and static analysis tools to identify race conditions.
Static testing tools scan a program without running it.
However, they produce many false reports.
Dynamic analysis tools have fewer false reports, but they may not catch race conditions that aren't executed directly within the program.
What is the symlink race condition protection?
The symlink race condition vulnerability
The FollowSymlinks option exposes Apache to a symlink security vulnerability.
This symlink vulnerability allows a malicious user to serve files from anywhere on a server that strict operating system-level permissions do not protect.2 mai 2023
|
Race Condition Vulnerability Lab
26-Jul-2020 If a malicious attacker can somehow make /tmp/XYZ. Page 3. SEED Labs – Race Condition Vulnerability Lab. 3 a symbolic link pointing to a ... |
|
Symlink attacks
▽Checks OK but the attack succeeds! Page 3. Race condition examples. ◇ access/open. ◇ chmod/chown. ◇ Directory renames. □ Root invokes rm -r on /tmp/* to |
|
Secure programmer: Prevent race conditions
07-Oct-2004 (When accessed a symbolic link file |
|
Secure Coding in C and C++ Race Conditions
A symbolic link is a directory entry that references a target file or directory. A symlink vulnerability involves a programmatic reference to a file name that |
|
Race conditions
○ Symlink is a directory entry that references a target file or directory ○ Race condition detection is NP complete. ○. Hence approximate detection. ○. C ... |
|
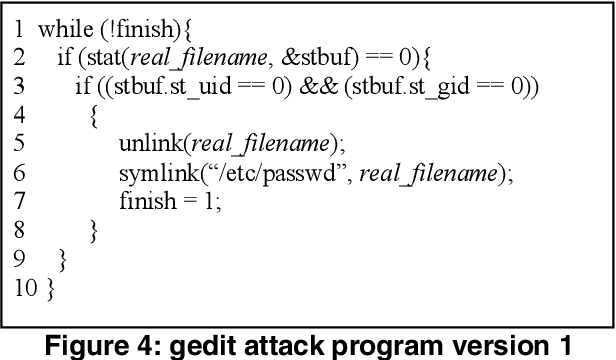
Race Condition Vulnerability Lab
symlink("/etc/passwd""/tmp/XYZ");. 3.3 Improving success rate. The most critical step (i.e. |
|
CS 380S - Theory and Practice of Secure Systems
◇Essentially a race condition. ◇Most famously in the file system but can When to insert symlink? ◇After access started: • Monitor access time on a ... |
|
Race Condition Vulnerability Lab
unlink("/tmp/XYZ"); symlink("/etc/passwd""/tmp/XYZ");. You can also use Linux command "ln -sf" to create symbolic links. Here the "f" option means that if the |
|
SEED Labs – Race Condition Vulnerability Lab
You can call C function symlink() to create symbolic links in your program. Since Linux does not allow one to create a link if the link already exists we need |
|
SEED Labs – Race Condition Vulnerability Lab
In the simulated attack we use the "ln -s" command to make/change symbolic links. Now we need to do it in a program. We can use symlink() in C to create |
|
Race Condition Vulnerability Lab
Jul 26 2020 Sticky symlink protection. • Principle of least privilege. Readings and videos. Detailed coverage of the race condition attack can be found ... |
|
Race conditions
Concurrency and Race condition. ? Concurrency Necessary properties for a race condition ... Creation of symlink is not checked to ensure that the owner. |
|
Symlink attacks
Do not assume that symlinks are trustworthy: ? Example 1 ?Attacker creates a symlink with same name that points to an ... Race condition examples. |
|
Race Condition Vulnerability Lab
race-condition vulnerability attackers can run a parallel process to /tmp/XYZ a symbolic link pointing to /etc/shadow |
|
RACES and LINKS Simple Race Condition
Basic symlink attack. ? Known or predictable file name. ? Defense: Randomness. ? Symlink attacks on insecure temporary files. ? Race conditions (148 |
|
Secure Coding in C and C++ Race Conditions
Within the race window the attacker alters the meaning of the file name by creating a symbolic link. Page 35. 35. TOCTOU Vulnerability with stat() if (stat |
|
SEED Labs – Race Condition Vulnerability Lab
Race condition vulnerability. • Sticky symlink protection. • Principle of least privilege. Readings and related topics. Detailed coverage of the race |
|
Symbolic Links Considered Harmful Jeremy Allison Samba Team
The Rust Security Response WG was notified that the std::fs::remove_dir_all standard library function is vulnerable to a race condition enabling symlink |
|
Fixing Races for Fun and Profit: How to abuse atime
niques for exploiting race conditions shows that races the victim changes the symbolic link activedir to ... countermeasure to this race condition. |
|
SEED Labs – Race Condition Vulnerability Lab
Race condition vulnerability. • Sticky symlink protection. • Principle of least privilege. Readings and videos. Detailed coverage of the race condition |
|
Race Condition Vulnerability Lab - UTC
A race condition occurs when multiple processes access and manipulate the same data concurrently, and the outcome of the execution depends on the particular order in which the access takes place |
|
Race conditions
Concurrency and Race condition ○ Concurrency Necessary properties for a race condition Creation of symlink is not checked to ensure that the owner |
|
Race Condition Vulnerability Lab - Syracuse University
Ubuntu 11 04 and 12 04 come with an built-in protection against race condition attacks This scheme works by restricting who can follow a symlink According to |
|
Symlink attacks - Secure Systems Lab
▽Checks OK, but the attack succeeds Page 3 Race condition examples ◇ access/open ◇ chmod/chown |
|
RACES and LINKS Simple Race Condition
Basic symlink attack ▫ Known or predictable file name ▫ Defense: Randomness ▫ Symlink attacks on insecure temporary files ▫ Race conditions (148 |
|
Race Condition Vulnerability
19 fév 2019 · Race Condition Vulnerability Create a regular file X inside /tmp directory Pass the access() check Change “/tmp/X” to symbolic link, pointing |
|
Part 1: Race Condition Vulnerability Lab - SPAR
Race condition vulnerability • Sticky symlink protection • Principle of least privilege Readings and related topics Detailed coverage of the race condition attack |
|
Race Condition Vulnerability - Moodle UPorto
Race Condition Vulnerability Create a regular file X inside /tmp directory Pass the access() check Change “/tmp/X” to symbolic link, pointing to “/etc/passwd” |
|
Secure programmer: Prevent race conditions - LiU IDA
7 oct 2004 · Summary: Learn what a race condition is and why it can cause symbolic link file, also called a symlink, redirects the requester to another file |

![PDF] Multiprocessors May Reduce System Dependability under File PDF] Multiprocessors May Reduce System Dependability under File](https://imgv2-1-f.scribdassets.com/img/document/128923691/298x396/81200fa1c3/1362594129?v\u003d1)
![PDF] File-based Race Condition Attacks on Multiprocessors Are PDF] File-based Race Condition Attacks on Multiprocessors Are](https://mk0resourcesinf5fwsf.kinstacdn.com/wp-content/uploads/031316_1417_RaceConditi5.jpg)













![PDF] Multiprocessors May Reduce System Dependability under File PDF] Multiprocessors May Reduce System Dependability under File](http://slideplayer.com/slide/17458852/102/images/6/Race+Condition+Vulnerability.jpg)