protocole vpn pdf
|
Guide to IPsec VPNs
A VPN is a virtual network built on top of existing physical networks that provides a secure communications mechanism for data and control information transmitted between co mputers or networks IPsec is also used as a component that provides the security for many other internet protocols The User Datagram Protocol (UDP) usage guidelines |
|
AN INTRODUCTION TO VPN
There are mainly two kinds of VPN: Point to Point Tunneling Protocol (PPTP) and Layer 2 Tunneling Protocol (L2TP) Both can link a remote computer to a network but only L2TP offers strong security If you must transmit sensitive information do not use PPTP Remember that when you set up VPN you\'re offering a way into your office network |
|
What Is a Virtual Private Network?
Before describing the various VPN technologies and models it is useful to first describe the various customer and provider network devices that are relevant to the discussion Devices in the customer network fall into one of two categories: Customer (C) devices—C devices are simply devices such as routers and switches located within the customer n |
|
What is a VPN?
What is a VPN? A VPN is a shared network where private data is segmented from other traffic so that only the intended recipient has access The term VPN was originally used to describe a secure connection over the Internet Today however VPN is also used to describe private networks such as Frame |
|
How Virtual Private Networks Work
Oct 13 2008 · VPN is a private network that uses a public network (usually the Internet) to connect remote sites or users together Instead of using a dedicated real−world connection such as leased line a VPN uses \"virtual\" connections routed through the Internet from the company\'s private network to the remote site or employee What Makes a VPN? |
What devices are used in a VPN?
Other device types used in VPNs include Network Access Servers (NAS) and VPN gateways/concentrators. A NAS is a device that interfaces between an access network (such as a Public Switched Telephone Network [PSTN]) and a packet-switched network (such as an IP backbone). In a remote access VPN, a NAS can serve as a tunnel endpoint.
What protocols are used to enable site-to-site VPNs?
Protocols and technologies used to enable site-to-site VPNs include IP Security (IPsec), Generic Routing Encapsulation (GRE), the Layer Two Tunneling Protocol version 3 (L2TPv3), Draft Martini pseudowires (emulated circuits), IEEE 802.1Q tunneling (Q-in-Q), and MPLS Label Switched Paths (LSP).
What encapsulating protocol is used in a VPN?
Protocols such as IPX and NetBeui, which would normally not be transferred across the Internet, can safely and securely be transmitted. For site−to−site VPNs, the encapsulating protocol is usually IPsec or Generic Routing Encapsulation (GRE).
Is IPsec a VPN?
But one of the most important advances has been in Virtual Private Networking (VPN) Internet Protocol security (IPSec). IPSec is one of the most complete, secure, and commercially available, standards-based protocols developed for transporting data. What is a VPN?
VPN Devices
Before describing the various VPN technologies and models, it is useful to first describe the various customer and provider network devices that are relevant to the discussion. Devices in the customer network fall into one of two categories: Customer (C) devices—C devices are simply devices such as routers and switches located within the customer n
VPN Technologies and Protocols
A number of technologies and protocols are used to enable site-to-site and remote access VPNs. These protocols and technologies are described in the sections that follow. ptgmedia.pearsoncmg.com
Technologies and Protocols Used to Enable Remote Access VPNs
Protocols used to enable remote access VPNs (discussed later in this chapter) include the following: The Layer Two Forwarding (L2F) Protocol—L2F is a Cisco proprietary protocol that is designed to allow the tunneling of PPP (or Serial Line Interface Protocol [SLIP]) frames between a NAS and a VPN gateway device located at a central site. Remote acc
Customer Provisioned Site-to-Site VPNs
Customer provisioned site-to-site VPNs are configured on CE devices such as routers and firewalls. In this case, tunnels are configured between CE devices in the VPN, and customer data traffic is sent over these tunnels. Protocols used to encapsulate user data traffic as it is sent over the tunnels between VPN sites include GRE and IPsec. ptgmedia.pearsoncmg.com
Other Methods of Categorizing VPNs
Yes, there are yet more methods of categorizing VPNs VPNs can be further categorized depending on whether they are connection oriented or connectionless, whether they are overlay or peer to peer, and whether they are secure or trusted. ptgmedia.pearsoncmg.com
Connection-Oriented and Connectionless VPNs
VPNs can be either connection oriented or connectionless depending on whether VCs or tunnels are provisioned to carry VPN traffic. Connection-oriented and connectionless VPNs are described as follows: Connection-oriented VPNs—In connection-oriented VPNs, VCs or tunnels are set up to carry VPN traffic. Examples of connection-oriented VPNs are those
And Finally. . .
And finally, here are two or three sundry VPN classifications: Transport/Application Layer VPNs—SSL sits on top of TCP in the protocol stack, and SSL VPNs are therefore sometimes referred to as either Transport or Application Layer VPNs. Internet VPNs—Designed to run over the public Internet. Multiservice VPNs—Provide a framework for converged serv
Summary
This chapter introduced, explained, and compared VPN devices, protocols, technologies, and models. VPNs may be service provider or customer provisioned and fall into one of two broad categories: Site-to-site VPNs connect the geographically dispersed sites of an organization or organizations. Remote access VPNs connect mobile or home-based users to
Scalability
Very good Very good Very good Very goodVery goodVery good (with hardware Good (with hardware acceleration) acceleration) ptgmedia.pearsoncmg.com
|
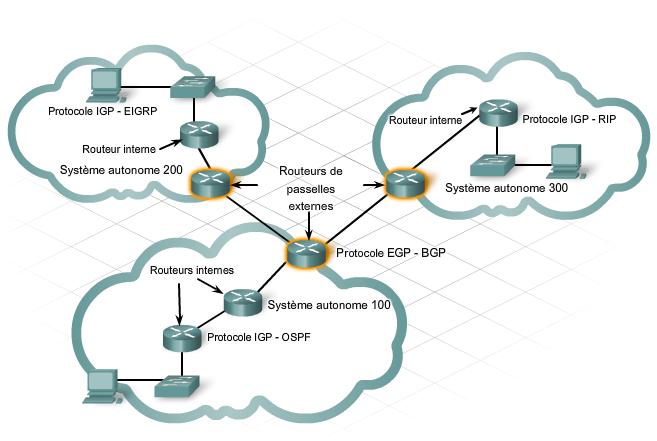
Les Réseaux Privés Virtuels (VPN) Définition dun VPN
Différents protocoles: • Passenger Protocol – Les données originales (IP…) à transmettre. • Encapsulating Protocol – Le protocole (GRE IPSec |
|
Configuration dun tunnel VPN site à site entre le routeur VPN
Le protocole ISAKMP (Internet Security Association and Key Management Protocol) est utilisé pour négocier le tunnel VPN entre deux points d'extrémité VPN. |
|
Exemple de configuration dun VPN client sur un réseau local sans
La mise en œuvre de la phase 1 se fait généralement par le protocole IKE (Internet Key Exchange). Si l'homologue. IPSec distant ne peut pas exécuter IKE vous |
|
Rseaux Privs Virtuels - Vpn
2.1 - Principe général. Un réseau Vpn repose sur un protocole appelé "protocole de tunneling". Ce protocole permet de faire circuler les. |
|
Cours de sécurité
s Solutions très correctes au niveau réseau avec le protocole IPSEC s 3 Intégrité s Performances en VPN: souvent beaucoup de surcharges (protocoles. |
|
Guide des solutions sécurité et VPN Cisco Systems
Routage intégral jusqu'à la couche 3 y compris les protocoles de routage externes |
|
VPN.pdf - I. Le concept de réseau privé virtuel
C'est un protocole très proche des protocoles PPTP et L2F et est normalisé dans un RFC. Cette fois les trames PPP sont encapsulées dans le protocole L2TP lui- |
|
Réseaux privés virtuels (VPN) Comment fonctionne le PATH MTU
V3PN (VoIP/Video Enabled IPSec VPN) Configuration du concentrateur est dynamique ... –NHRP – Next Hop Resolution Protocol. |
|
Chap-8-Les VPN.pdf
Le principe du protocole PPTP est de créer des paquets sous le protocole PPP et de les encapsuler dans des datagrammes IP. Le tunnel PPTP se caractérise par une |
|
How Virtual Private Networks Work - Cisco
13 oct. 2008 Most VPNs use one of these protocols to provide encryption. IPsecInternet Protocol Security Protocol (IPsec) provides enhanced security features ... |
|
Les Réseaux Privés Virtuels (VPN) Définition dun VPN
Un VPN est un réseau privé qui utilise un réseau Protocoles de "tunneling" des VPN négocier des variables de configuration, assignation des adresses, |
|
I Le concept de réseau privé virtuel - Zenk - Security
Le VPN repose sur un protocole de tunnelisation qui est un protocole permettant de La SPD (Security Policy Database) est la base de configuration de IPSec |
|
VPN - Département Informatique - Cnam
s Solutions très correctes au niveau réseau avec le protocole IPSEC s 3 Intégrité s Pratiquement s Performances en VPN: souvent beaucoup de surcharges ( protocoles supplémentaires configuration ou de comptabilité : s Associées à la |
|
Réseaux privés virtuels (VPN) Comment fonctionne le PATH - Cisco
Configuration du concentrateur est dynamique Configuration – Site Central – suite Paquet GRE avec en-tête: protocol 47 (avec la nouvelle adresse de |
|
VPN
protocoles les plus utilisés sur Internet (en particulier IP) Généralités Page 8 8 Réseaux : Virtual Private Network |
|
VPN et Solutions pour lentreprise
Un VPN permet d'interconnecter des sites distants => Réseau Private : PPTP : Point to Point Tunneling Protocol □ L2TP: Layer two Tunneling Protocol |
|
Mémoire de fin de cycle Mise en place dune solution VPN sur pare
1 2 9 Le protocole DHCP (Dynamic Host Configuration Protocol) 10 3 1 Comparaison entre les protocoles PPTP, Open VPN, L2TP/IPsec [25] |
|
Les VPNs IP Internet : principes et usage nomade - Orange Developer
VPN L2TP et L2TP/IPSec : Layer 2 Tunneling Protocol • VPN SSL Exemples d' implémentation : Cf (Configuration VPN L2TP/IPSec sur Pocket PC et usages |
|
IP security Protocol
– La sécurité, La mobilité, – La configuration automatique des stations – La qualité de service, etc Solutions IPsec avec IPv6 – CISCO IOS 12 2 et supérieure – |
|
Livre Blanc Smile - VPN open source - ASPROM
œuvre et configuration, afin d'aider le lecteur dans la sélection d'outils adaptés à serveurs Heureusement, nous verrons que certaines protocoles de VPN ne |
![Fiche de protocole [pdf] Fiche de protocole [pdf]](https://www.fichier-pdf.fr/2019/06/15/alexandre-nimubona--protocole-rss2016/preview-alexandre-nimubona--protocole-rss2016-1.jpg)


![PDF] Protocole HTTP méthodes GET et POST cours et formation gratuit PDF] Protocole HTTP méthodes GET et POST cours et formation gratuit](https://s1.studylibfr.com/store/data/002545464_1-c3110a3a946b04d4673f12800f219776.png)






![Télécharger] Protocole de routage OSPF: Open Shortest Path First Télécharger] Protocole de routage OSPF: Open Shortest Path First](https://imgv2-2-f.scribdassets.com/img/document/150322306/original/7c68a0d5bc/1612020388?v\u003d1)




![PDF] Introduction aux réseaux informatiques protocole SNMP - Cours PDF] Introduction aux réseaux informatiques protocole SNMP - Cours](https://book.coe.int/6866/pdf-protocole-damendement-a-la-convention-pour-la-protection-des-personnes-a-legard-du-traitement-automatise-des-donnees-a-caractere-personnel-serie-des-traites-du-conseil-de-leurope-no-223.jpg)















![Les Protocoles des Sages de Sion [Ebooks Pdf Epub Livres] Les Protocoles des Sages de Sion [Ebooks Pdf Epub Livres]](https://www.levert.ma/wp-content/uploads/2020/06/Capture-d%E2%80%99e%CC%81cran-2020-06-26-a%CC%80-14.34.29-1024x991.png)



