best web vulnerability scanner
What is Wireshark free vulnerability scanner?
The Wireshark free vulnerability scanner is open-source, free to download and use, and relies on packet sniffing to get the picture of network traffic, which can help administrators to come up with efficient countermeasures.
What factors affect user satisfaction for vulnerability scanner products?
Produce reports analyzing known vulnerabilities and new exploits "Has the product been a good partner in doing business?", "Detection Rate", "Automated Scans", and "Configuration Monitoring" are the top four factors that positively impact user satisfaction for Vulnerability Scanner products.
How do vulnerability scanners work?
They work by maintaining an up-to-date database of known vulnerabilities, and conduct scans to identify potential exploits. Vulnerability scanners are used by companies to test applications and networks against known vulnerabilities and to identify new vulnerabilities.
What is Mister scanner web security scan?
Mister Scanner’s web security scan is trusted by more than 150,000 businesses worldwide. It scans web applications for vulnerabilities such as SQL injection, cross-site scripting, cross-site request forgery, the OWASP top ten, malware, and more.

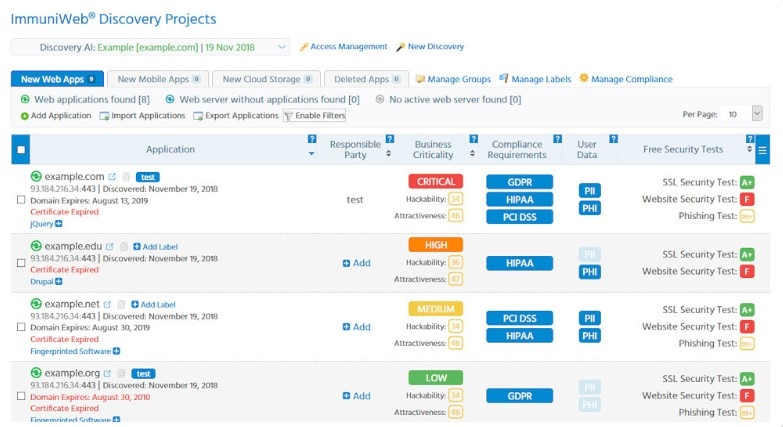
Introduction To Vulnerability Scanning

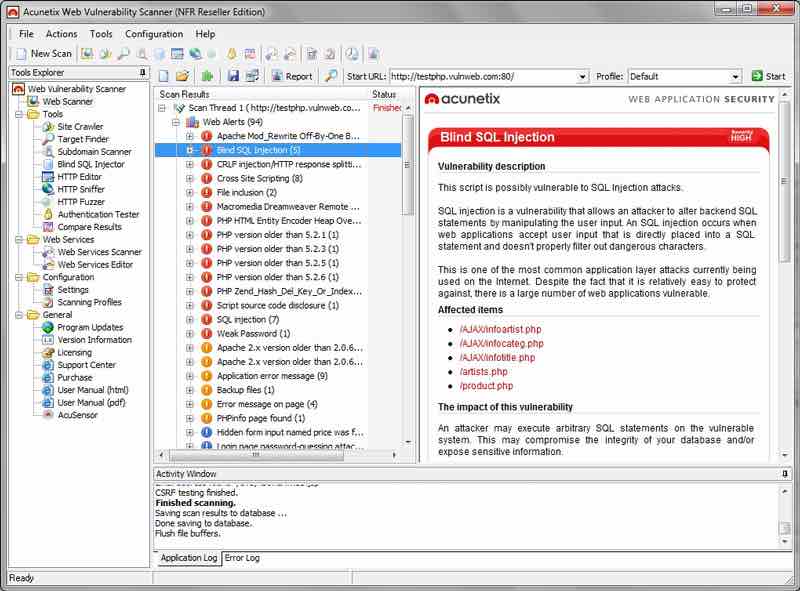
Web Vulnerability Scanner Acunetix Website Vulnerability Scanner

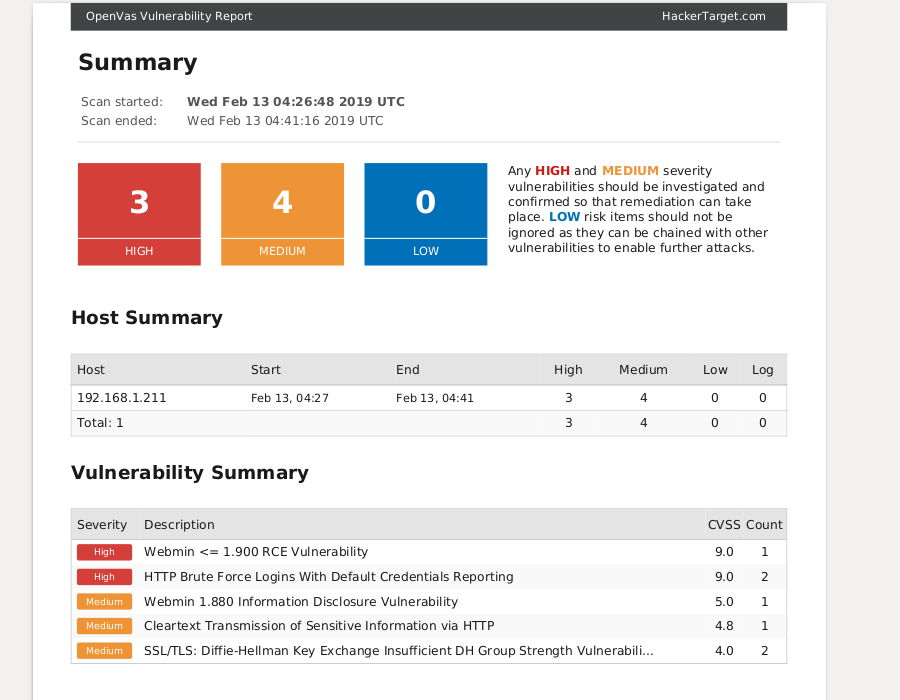
Best FREE Vulnerability Scanner: Nessus Vs OpenVAS (Greenbone)
|
Web Vulnerability Scanners: A Case Study Angel Rajan Emre
and size of websites increases the need for better securing those websites. Acunetix is an automated web vulnerability scanner which scans any web ... |
|
Web Application Vulnerability Testing with Nessus
host vulnerability scanner. Server Supported on: • Window. • Linux. • Mac OS. • UNIX. Clients: Web based and Mobile (IOS Android). |
|
Qualys Web Application Scanning Getting Started Guide
18-Sept-2020 A discovery scan finds information about your web application without performing vulnerability testing. This is a good way to understand where ... |
|
Enemy of the State: A State-Aware Black-Box Web Vulnerability
Black-box web vulnerability scanners are a popular by better education of web developers or by the use of security-aware web application development ... |
|
HHS.gov
25-Apr-2019 How do web vulnerabilities fit into the big picture ... 14 Best Open Source Web Application Vulnerability Scanners [Updated for 2019] ... |
|
Web Unique Method (WUM): An Open Source Blackbox Scanner for
scanners; web vulnerabilities crawling; security scanner. I. INTRODUCTION. Web applications are the best way of providing standard. |
|
Evaluation of Web Application Security in Afghanistan
12-Dec-2021 get a better idea about the current situations among students and ... Keywords— web application vulnerability |
|
GETTING STARTED WITH WEB APPLICATION SCANNING
AND BEST PRACTICES THAT CAN POSITION YOUR WAS PROGRAM FOR result using Tenable.io® Web Application Scanning (WAS) requires a different approach to. |
|
SecuBat: A Web Vulnerability Scanner
Many web application security vulnerabilities result from generic input validation problems. To the best of our knowledge SecuBat is the first open-. |
|
Performance Evaluation of Web Application Security Scanners for
Web vulnerability scanners which are tools to regularly audit web applications |
|
SecuBat: A Web Vulnerability Scanner - WWW2006
Many web application security vulnerabilities result from generic input validation problems Examples of such vulner- abilities are SQL injection and Cross-Site |
|
The Ultimate Guide to Vulnerability Scanning - Webflow
Web application vulnerability scanners are a specialised type of vulnerability scanner which focus on finding weaknesses in web applications and websites |
|
Free Web Scanning Resources - HHSgov
25 avr 2019 · assessment, secure configuration assessment, web application scanning, digital certificate and public cloud management and the ability to |
|
A complete guide to securing a website - Acunetix
To secure a website or a web application, one has to first understand the target good web vulnerability scanner sometimes needs to be pre-configured |
|
Designing vulnerability testing tools for web services: approach
evaluated, in a total of 11 scanners To test the tools, the authors introduced different types of vulnerabilities in a real- istic web application, challenging the |
|
Web Unique Method (WUM): An Open Source Blackbox Scanner for
At present, a number of web application vulnerabilities scanners have been proposed by research community, such as ZED Attack Proxy (ZAP) by AWASP, Wapiti |









![PDF] Port and Vulnerability Scanning Packet Sniffing Intrusion PDF] Port and Vulnerability Scanning Packet Sniffing Intrusion](https://d1uyme8f6ss6qi.cloudfront.net/image/home/home-banner-vmdr-graphics.png)



![PDF] Port and Vulnerability Scanning Packet Sniffing Intrusion PDF] Port and Vulnerability Scanning Packet Sniffing Intrusion](https://assets.qwikresume.com/resume-samples/pdf/screenshots/it-security-analyst-1510205758-pdf.jpg)