bind dns blackhole list
What is a URI DNSBL query?
For details see RFC 5782. A URI DNSBL query (and an RHSBL query) is fairly straightforward. The domain name to query is prepended to the DNS list host as follows: where dnslist.example.com is the DNS list host and example.net is the queried domain. Generally if an A record is returned the name is listed. Different DNSBLs have different policies.
How do I block a domain in Debian?
One of the easiest way of doing this is within your DNS infrastructure by making your DNS Resolvers authoritative for the domains that you wish to block. Within your BIND configuration file which on Debian based systems is normally located at /etc/bind/named.conf.local you will need to specify which domains you want to block.
Can a named Daemon bind to a restricted port?
Prior to running the named daemon, use the touch utility (to change file access and modification times) or the chown utility (to set the user id and/or group id) on files where BIND should write. If the named daemon is running as an unprivileged user, it cannot bind to new restricted ports if the server is reloaded. 7.3. Dynamic Update Security
What was the first DNSBL?
The first DNSBL was the Real-time Blackhole List (RBL), created in 1997, at first as a Border Gateway Protocol (BGP) feed by Paul Vixie, and then as a DNSBL by Eric Ziegast as part of Vixie's Mail Abuse Prevention System (MAPS); Dave Rand at Abovenet was its first subscriber.
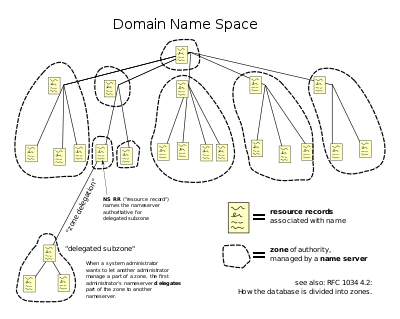
Additional-From-Auth, Additional-From-Cache
additional-from-auth and additional-from-cache control the behaviour when zones have additional (out-of-zone) data or when following CNAME or DNAME records. These options are for used for configuring authoritative-only (non-caching) servers and are only effective if recursion no is specified in a global options clause or in a view clause. The defau
Allow-Query, Allow-Query-On
allow-query defines an match list of IP address(es) which are allowed to issue queries to the server. If not specified all hosts are allowed to make queries (defaults to allow-query {any;};). allow-query-on defines the server interface(s) from which queries are accepted and can be useful where a server is multi-homed, perhaps in conjunction with a
Allow-Query-Cache, Allow-Query-Cache-On
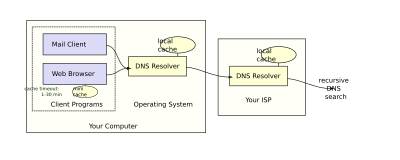
Since BIND 9.4 allow-query-cache (or its default) controls access to the cache and thus effectively determines recursive behavior. This was done to limit the number of, possibly inadvertant, OPEN DNS resolvers. allow-query-cache defines an address_match_listof IP address(es) which are allowed to issue queries that access the local cache - without a
Allow-Recursion, Allow-Recursion-On
Both statements are only relevant if recursion yes;is present or defaulted. allow-recursion defines a address_match_list of IP address(es) which are allowed to issue recursive queries to the server. When allow-recursion is present allow-query-cache defaults to the same values. If allow-recursion is NOT present the allow-query-cachedefault is assume
auth-nxdomain
If auth-nxdomain is 'yes' allows the server to answer authoritatively (the AA bit is set) when returning NXDOMAIN (domain does not exist) answers, if 'no' (the default) the server will not answer authoritatively. NOTE: This changes the previous BIND 8 default setting. This statement may be used in a view or a global optionsclause. zytrax.com
Blackhole
blackhole defines a address_match_list of hosts that the server will NOT respond to, or answer queries for. The default is 'none' (all hosts are responded to). This statement may only be used in a global optionsclause. zytrax.com
Delegation-Only
delegation-only applies to hint and stub zones only and defines whether the zone will only respond with delegations (or referrals). See type for more information. The default is no. This statement may only be used in a zoneclause. zytrax.com
Deny-Answer-Addresses
Allows a receiving recursive name server (full function resolver) to discard a query response which contains any IP address (IPv4 or IPv6) defined in the address_match_list (while a keyparameter is valid within an address_match_list it will be silently ignored in this context). The intent of the statement is to prevent DNS queries to external domai
Deny-Answer-Aliases
deny-answer-aliases is similar to deny-answer-addresses but operates on any CNAME (or DNAME) records returned. The except-from ( name_list ) parameter allows the user to optionally select names which can bypass the filter processing. In the above example if a query returns a CNAME pointing to the domain name (or any subdomain) of either example.com
Disable-Empty-Zone
By default empty-zones-enable is set to yes which means that reverse queries for IPv4 and IPv6 addresses covered by RFCs 1918, 4193, 5737 and 6598 (as well as IPv6 local address (locally assigned), IPv6 link local addresses, the IPv6 loopback address and the IPv6 unknown address) but which is not covered by a locally defined zone clause will automa
|
Build Securely a DNS Sinkhole Step-by-Step Powered by Slackware
Configure Bind as DNS Sinkhole . If you want to use your ISP DNS server list or you are an enterprise that wants to use Split-DNS forwarding ... |
|
DNS Real-time Black hole List System
The RBL server used BIND and the management software is built in PHP with a MYSQL backend. Keywords — DNS RBL |
|
DNS Sinkhole
A basic DNS sinkhole deployment includes the following components: 1. Commodity server. 2. Linux OS with BIND. 3. List(s) of malicious and unwanted hosts |
|
DNS Response Policy Zone (DNSRPZ)
DNS RPZ turns the recursive DNS server into a security hammer … ? Provide the same capabilities of an anti-spam DNSBL. (DNS Block List ne RBL) and RHSBL |
|
Modern DNS as a Coherent Dynamic Universal Database June
The Domain Name System (DNS) allows zone data to change dynamically based on secure blackhole list (RTBL) for e-mail. ... As of ISC BIND9.3 any zone. |
|
ACLs & Views Elements in an address match list Purposes in BIND
*Address match lists are always enclosed in curly braces. blackhole { ACL-name or itemized list; };. }; Allow-transfer ... server answer a DNS query. |
|
Tutorial on Configuring BIND to use Response Policy Zones (RPZ
Developed by Paul Vixie (ISC) and Vernon Schryver (Rhyolite). RPZ was first publicly announced at Black Hat in July 2010. Also referred to as a “DNS firewall”. |
|
CIS ISC BIND DNS Server 9.9 Benchmark
10 juil. 2017 Audit: Attempt to query the server from an address that has been placed in the blackhole list. If properly configured the query will fail. |
|
USING DNS TO PROTECT CLIENTS FROM MALICIOUS DOMAINS
In DNS sinkhole we create two lists called white list and black list. setup either PowerDNS or DNS Bind forwarder and act as DNS sinkhole when. |
|
Licence 3 Systèmes et Réseaux II Chapitre XI : Domain Name
Implemenation du DNS : BIND. (Département IEM / UB). DNS des suffixes génériques qui indique le type d'organisation (gTLDs) liste. |
|
Build Securely a DNS Sinkhole Step-by-Step Powered by Slackware
23 oct 2016 · Configure Bind as DNS Sinkhole If you want to use your ISP DNS server list or you are an enterprise that wants to use Split-DNS forwarding, |
|
DNS Response Policy Zone (DNSRPZ) - FTP Directory Listing
BIND's New Security Feature: the "DNS Firewall" Provide the same capabilities of an anti-spam DNSBL https://lists isc org/mailman/listinfo/dnsrpz-interest |
|
Tutorial on Configuring BIND to use Response Policy Zones (RPZ
RPZ was first publicly announced at Black Hat in July, 2010 Also referred to as a “DNS firewall” RPZ provides a way to “rewrite” a DNS response Normally a |
|
DNS and BIND - Deer Run Associates
available in the O'Reilly DNS and BIND book, as well as at http://www deer-run com/~hal/dns-sendmail/ and lists contact information for the domain ( hostmaster sysiphus com instead of Now you can essentially black-hole all attempts to |
|
USING DNS TO PROTECT CLIENTS FROM MALICIOUS - IDRBT
blacklist whereas the white list contains known important URLs The URLs setup either PowerDNS or DNS Bind forwarder and act as DNS sinkhole when |
|
DNS BIND 90 – 95 - Information Security
4 mai 2009 · This document, Security Configuration Benchmark for ISC BIND 9 5, provides prescriptive To obtain a list of DNS registrars, see Attempt to query the server from an address that has been placed in the blackhole list If |
|
The Center for Internet Security DNS BIND Benchmark
bind • bind-chroot • bind-libs • bind-utils Page 22 The Center for Internet Security DNS BIND Benchmark Draft v0 16 Page 22 of 41 2 Directory permissions |