apache tomcat http request smuggling vulnerability
|
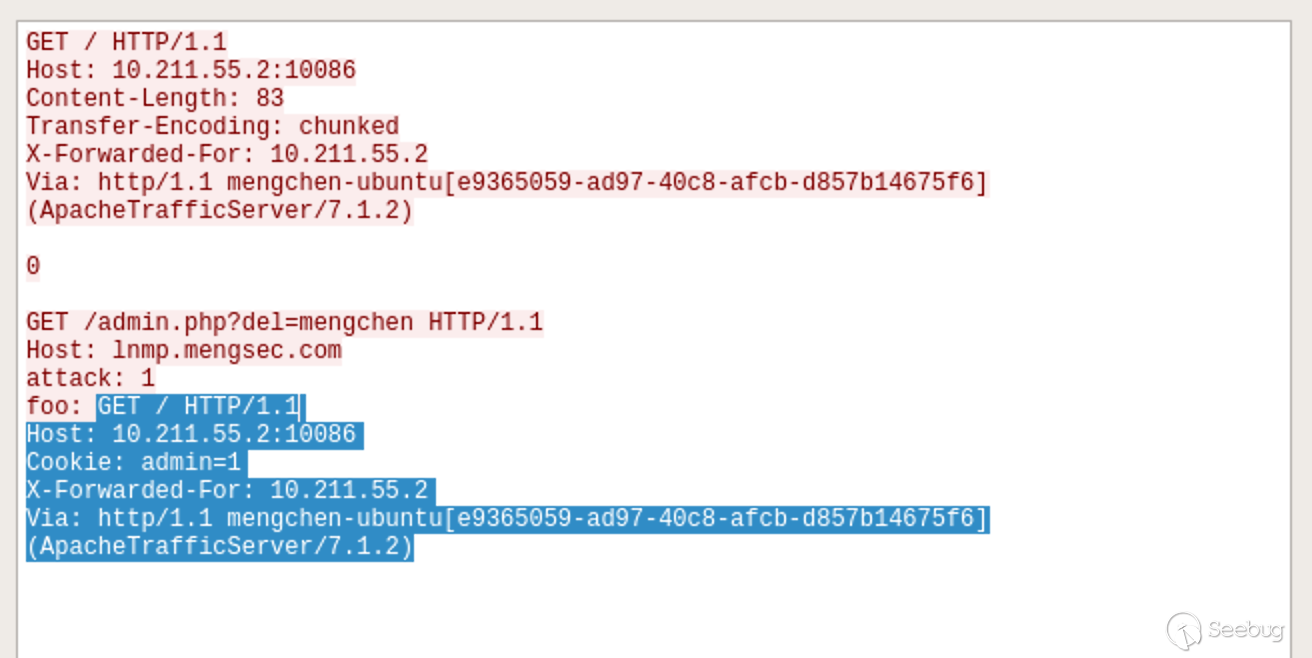
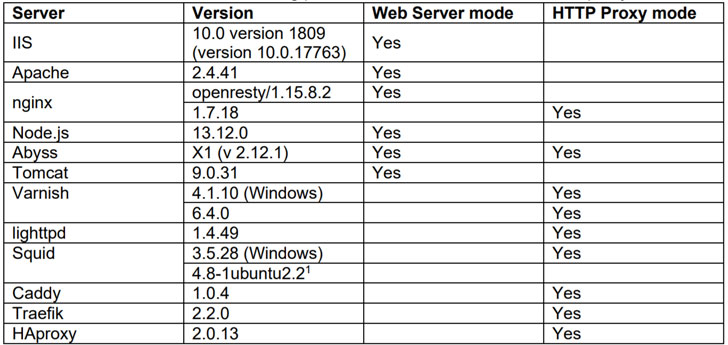
HTTP Request Smuggling in 2020
17 juil 2020 · Are “mainstream” web/proxy servers vulnerable? • Scope: IIS Apache nginx node js Abyss Tomcat Varnish lighttpd Squid Caddy |
|
HTTP REQUEST SMUGGLING
In the web cache poisoning attack this smuggled request will trick the cache server into unintentionally associating a URL to another URL's page (content) and |
|
T-Reqs: HTTP Request Smuggling with Differential Fuzzing
15 nov 2021 · ABSTRACT HTTP Request Smuggling (HRS) is an attack that exploits the HTTP processing discrepancies between two servers deployed in a proxy- |
HTTP Smuggling (CAPEC-33 and CAPEC-273) is different from HTTP Splitting due to the fact it relies upon discrepancies in the interpretation of various HTTP Headers and message sizes and not solely user input of special characters and character encoding.
What is a Desync attack?
What is a client-side desync attack? A client-side desync (CSD) is an attack that makes the victim's web browser desynchronize its own connection to the vulnerable website.
This can be contrasted with regular request smuggling attacks, which desynchronize the connection between a front-end and back-end server.
What are the risks of HTTP request smuggling?
This can cause either the front-end or the back-end server to incorrectly interpret the request, passing through a malicious HTTP query.
Request smuggling vulnerabilities let cybercriminals side-step security measures, attain access to sensitive information, and directly compromise various application users.
How can we mitigate HTTP request smuggling?
How to prevent HTTP request smuggling vulnerabilities
Use HTTP/2 end to end and disable HTTP downgrading if possible. Make the front-end server normalize ambiguous requests and make the back-end server reject any that are still ambiguous, closing the TCP connection in the process.|
HTTP Request Smuggling in 2020
Are “mainstream” web/proxy servers vulnerable? • Scope: IIS Apache |
|
HTTP Request Smuggling in 2020 – New Variants New Defenses
HTTP Request Smuggling (AKA HTTP Desyncing) is an attack technique that exploits devices they may be able to find additional vulnerable combinations. |
|
HDiff: A Semi-automatic Framework for Discovering Semantic Gap
from well-known HTTP software including Apache |
|
Web Application (OWASP Top 10) Scan Report
14 thg 12 2015 The XML External Entity vulnerability |
|
HTTP Request Smuggling.pdf
It is also possible to exploit a vulnerability in the web application (using the same fundamental vulnerability used in cross-site scripting attacks dubbed XSS |
|
Are Source Code Metrics ``Good Enough in Predicting Security
6 ngày tr??c Apache Tomcat has 22 distinct security vulnerabilities listed on the Apache ... Finally a Request Smuggling vulnerability occurs with ... |
|
HTTP Request Smuggling.pdf
It is also possible to exploit a vulnerability in the web application (using the same fundamental vulnerability used in cross-site scripting attacks dubbed XSS |
|
HDiff: A Semi-automatic Framework for Discovering Semantic Gap
from well-known HTTP software including Apache |
|
T-Reqs: HTTP Request Smuggling with Differential Fuzzing
15 thg 11 2021 Namely |
|
Testing Guide
Testing for Cross Site Request Forgery (CSRF) (OTG-SESS-005). Testing for logout functionality 8080/tcp open http Apache Tomcat/Coyote JSP engine 1.1. |
|
HTTP Request Smuggling in 2020 - Black Hat
mainstream” web/proxy servers vulnerable? • Scope: IIS, Apache, nginx, node js, Abyss, Tomcat, |
|
HTTP REQUEST SMUGGLING
2005 · Cité 1 fois — HTTP Request Smuggling enables various attacks – web cache possible to exploit a vulnerability in the web application (using the same Some servers ( e g , IIS and Apache) reject such a request, but it |
|
Countering Web Injection Attacks - School of Computer
Cité 3 fois — HTTP Request/Response Smuggling Web injection attacks are a set of web vulnerabilities intended to exploit the web application's also server-side platforms such as Apache |
|
OWASP Top 10 - Carson & SAINT
Web server allows HTTP method Apache Tomcat Denial of Service vulnerability vulnerability, Chunked Transfer vulnerability, and request smuggling vulnerability |
|
Your Cache Has Fallen: Cache-Poisoned Denial-of - CPDoS
2019 · Cité 7 fois — interpretation of HTTP requests in caching systems and origin servers can The host of troubles [7] attack is another vulnerability targeting misbehavior in the cache and origin server as the request smuggling |
|
SSRF bible Cheatsheet - OWASP Cheat Sheet Series
ng examples Apache web-server HTTP parser Nginx web-server HTTP parser Vulnerabilities |
|
Host of Troubles: Multiple Host Ambiguities in HTTP
Cité 17 fois — rect HTTP request (such as by using Flash on a victim's to evaluate whether their networks are vulnerable to such Apache, IIS, Lighttpd, LiteSpeed, Nginx, Squid, Varnish (4 1 2) |
|
Ai miei Genitori, per tutto il supporto e per avermi dato la
sites › filesPDF |