bit masking in embedded c
How to combine masks using a bitwise OR operator?
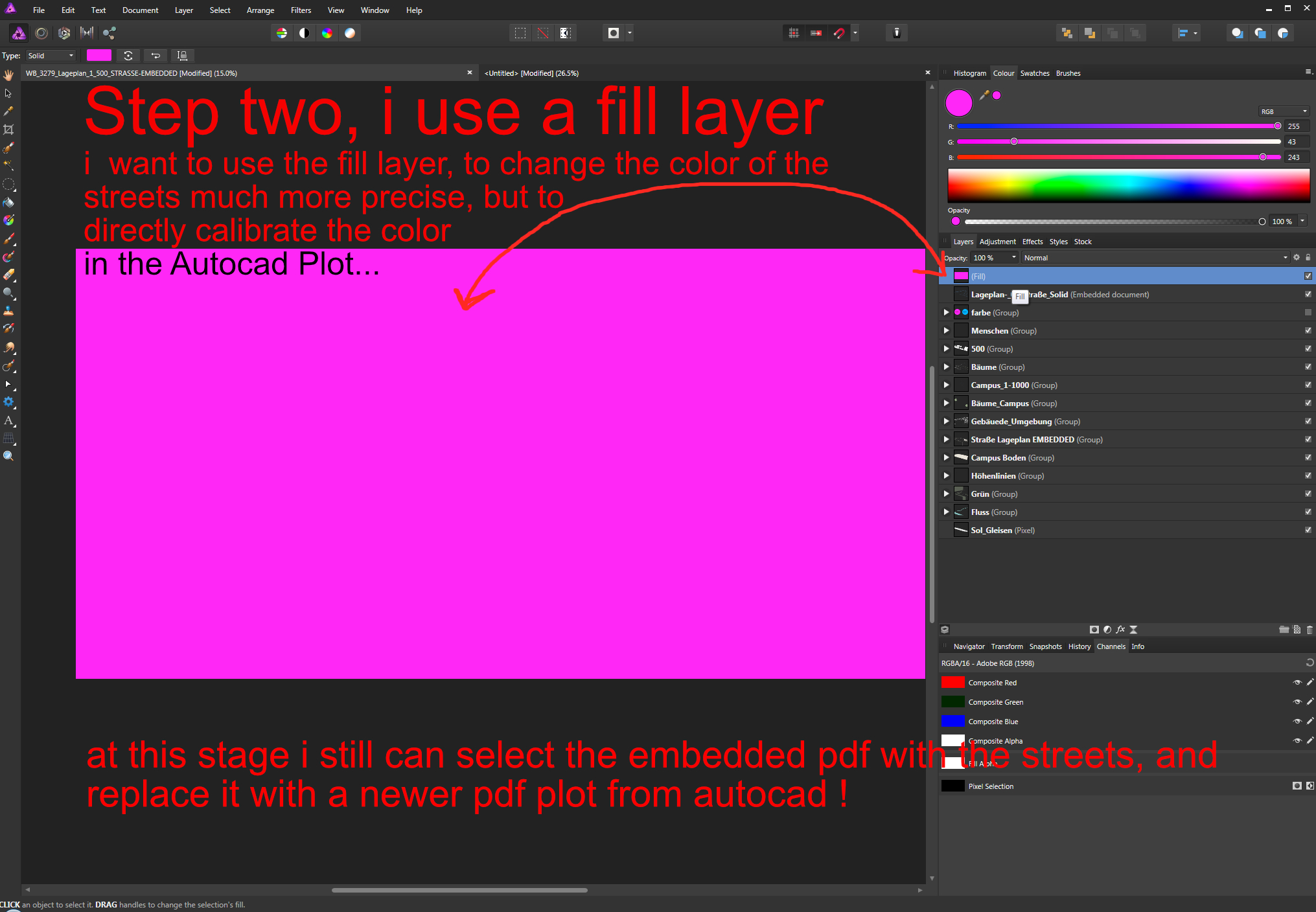
In conclusion, we can combine masks using the bitwise OR operator. The resulting mask will be an overlay of the individual masks. This operation uses the principle that the AND operator returns 0 if any of its inputs are 0. Let hence revise the AND truth table as
What is bit masking?
Bit masking allows you to use operations that work on bit-level. Checking if particular bit values are present or not. You actually apply a mask to a value, where in our case the value is our state 00000101 and the mask is again a binary number, which indicates the bits of interest.
How many bitwise operators are there in C?
There are basically 6 bitwise operators in C that can be used to manipulate bits which are as follows: Using these operators, we perform different bit masking techniques according to the requirements. Let’s discuss these techniques and how to implement them. 1. Setting a Bit
|
• A bit more on bit masking • Communicating between devices
Andrew H. Fagg: Embedded Real-. Time Systems: Serial Comm. 1. Today. • A bit more on bit masking. • Communicating between devices Mega8 UART C Interface. |
|
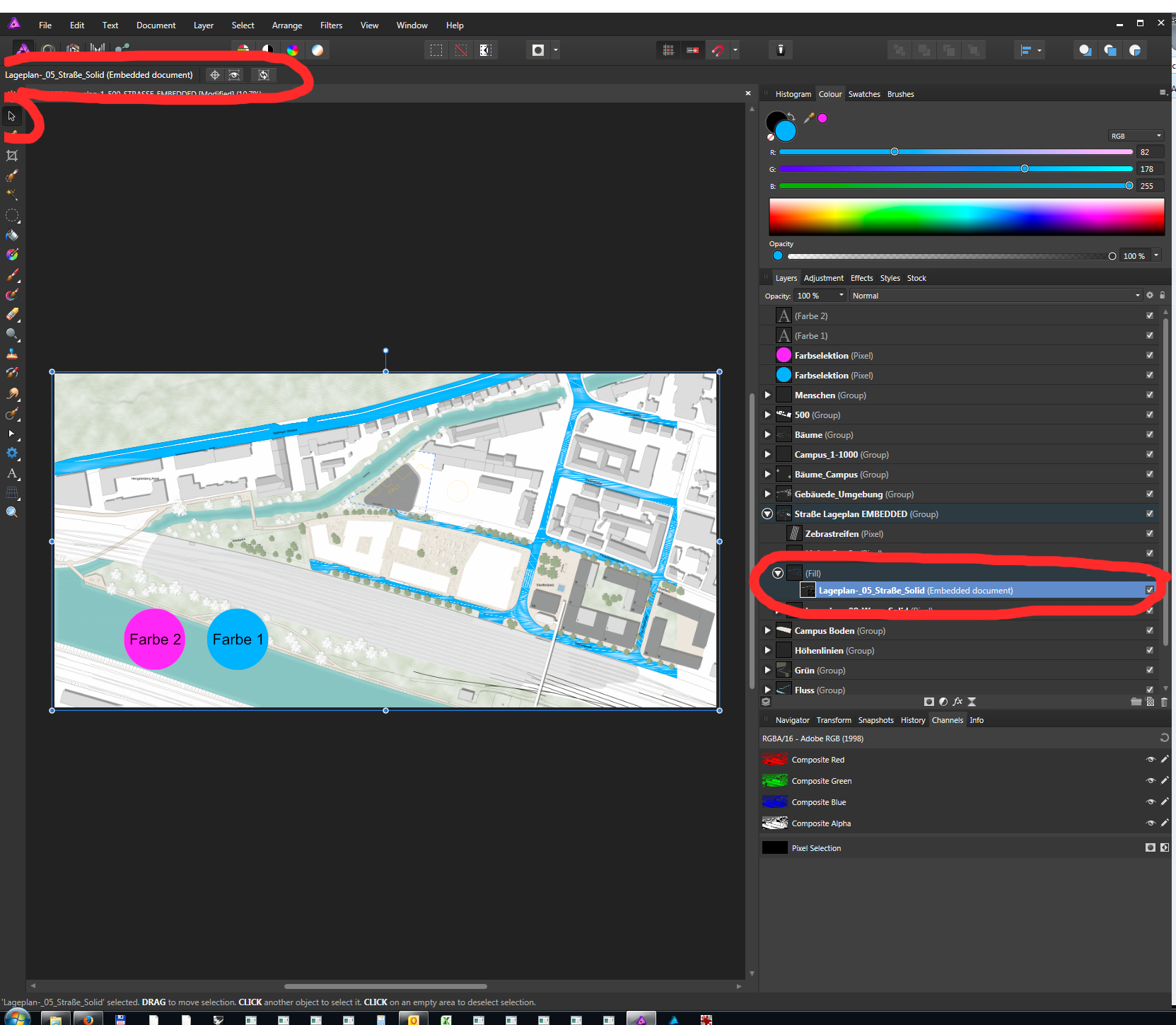
C Programming and Embedded Systems
I/O Registers within the address range 0x00 - 0x1F are directly bit- accessible using the SBI and CBI instructions. In these registers the value of single bits |
|
C programming for embedded system applications
C programming for embedded ELEC 3040/3050 Embedded Systems Lab (V. P. Nelson) ... Use a “mask” to select bit(s) to be altered. C = A & 0xFE;. |
|
C Programming and Embedded Systems
Pxn represents nth bit in Port x Note: “writing” a logic 1 to a bit in the PINx Register ... Controlling Port I/O makes bit masks invaluable. |
|
PIC1000: Getting Started with Writing C-Code for PIC16 and PIC18
To ensure compatibility with most PIC C compilers the code examples in this Bit Masks and Bit Field Masks. ... Embedded Solutions Engineer (ESE). |
|
ECE 3567 Microcontrollers Lab Lecture #2 – The Microcontroller
Bit 7 Bit 6 Bit 5 Bit 4 Bit 3 Bit 2 Bit 1 Bit 0 MOST Important Operators in Embedded C ... In C programming the |
|
Week 4: Embedded Programming Using C
Remember |
|
Experiment 2 - C Language Programming
the programming language reduced and embedded systems moved onto C as the Bit masking is using the bits in one word to “mask off” or select part of the ... |
|
Bitslicing Arithmetic/Boolean Masking Conversions for Fun and Profit
develop the first open-source embedded (Cortex-M4) implementations of Kyber768 and Saber masked at arbitrary order. The implementations based on the new bit |
|
C Programming and Embedded Systems
AB |
|
A Bitmask-Based Code Compression Technique for Embedded
For example, if we use a 8-bit mask pattern, and want to consider all 32-bit mismatches, it requires four 8-bit masks, and extra two bits (to identify one of the 4 bytes) |
|
• A bit more on bit masking • Communicating between devices
– Then, the value of the 2nd bit is used – Etc Page 6 Andrew H Fagg: Embedded Real- Time Systems: Serial Comm |
|
E91 Embedded System
Embedded Systems are ubiquitous • Embedded Systems more common i d d d Set bit 0 in “P1DIR” this makes it an output (next page) Loop to waste time |
|
CprE 288 – Introduction to Embedded Systems
Why Bitwise Operation Why use bitwise operations in embedded systems programming? Each single bit may have its own meaning – Push button array: Bit n is |
|
Embedded Software Engineering - 中正大學
Bit Manipulation ▫ pTimerStatus ▫ A pointer to a timer status register ▫ Least Significant Bit (LSB) ▫ bit 0 ▫ represented by 0x01 ▫ Most Significant Bit |
|
DPA, Bitslicing and Masking at 1 GHz - Cryptology ePrint Archive
ern gigahertz embedded processors Our experimental platform is a Sitara ARM Cortex-A8 32-bit RISC processor mounted on a Beaglebone Black (BBB) plat- |
|
Bitsliced Masking and ARM: Friends or Foes? ⋆ - Cryptology ePrint
permutation pattern, instead of relying on bit extraction, insertion and shifting bauwhede, editors, Cryptographic Hardware and Embedded Systems - CHES |
|
Real-Time Embedded Implementation of the Binary Mask Algorithm
Scaling factors are based on powers of 2 so that re-scaling can be performed quickly using simple bit shifting arithmetic The input signal is amplified prior to |