black hat hacking course pdf
|
$atellite Hacking for Fun & Pr0fit!
Started doing this in late 90's – So err why did it take so long to publish? Page 4 Feed Hunting ○ Look for 'interesting' satellite feeds |
|
Ethical hackingpdf
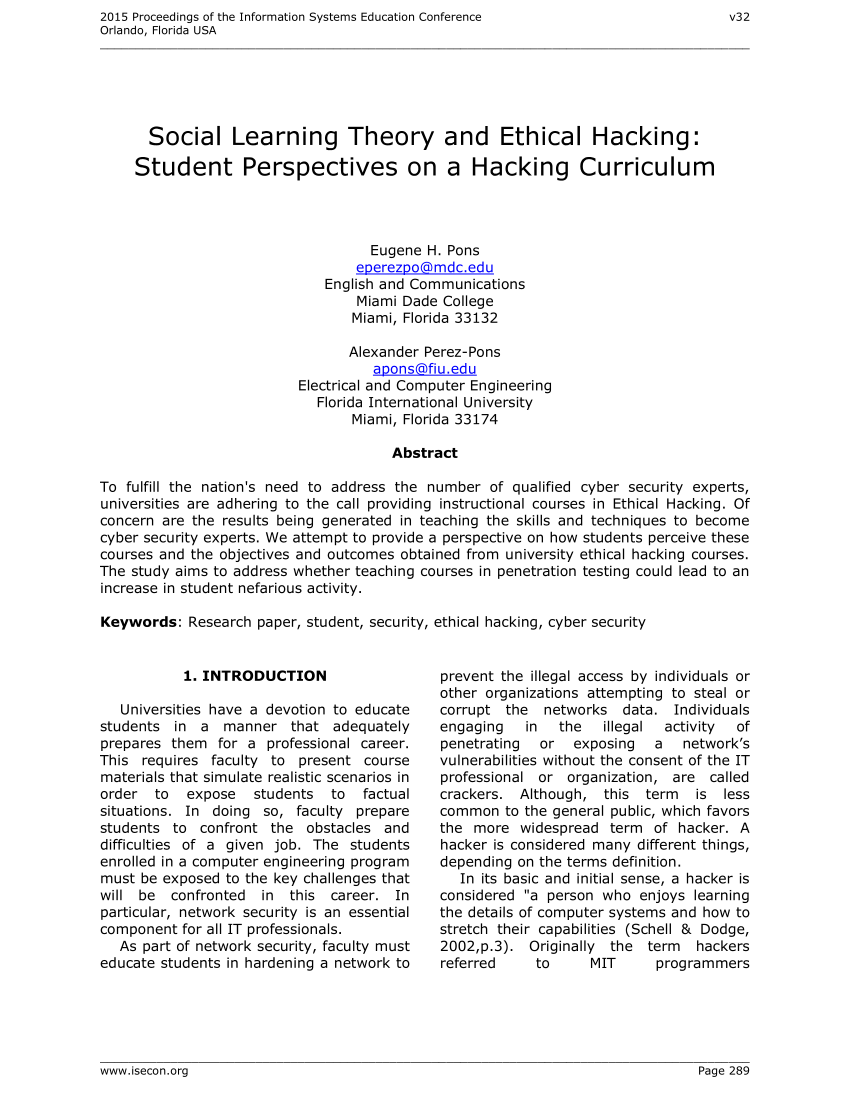
Grey hat Script kiddies Hacktivist A hacker who is in between ethical and black hat hackers He/she breaks into computer systems without authority with a |
|
Google Hacking for Penetration Testers
Payment details! can return devastating results! Page 11 Google Hacking Basics Let's take a look at some basic techniques: |
|
Black Hat Hacker White Hat Hacker Gray Hat Hacker
Black-hat Hackers are also known as an Unethical Hacker or a Security Cracker These people hack the system illegally to steal money or to achieve their own |
|
Computer Hacking Security TestingPenetration Testing and Basic
By learning how to hack! That's right It would be inconceivable to expect to protect yourself and property from hackers without first understanding how hacking |
Red hat hackers have a unique goal: to chase and bring down cyber security threat actors.
These hackers take matters into their own hands rather than relying on the authorities.
What is black hat training?
Black Hat Briefings (commonly referred to as Black Hat) is a computer security conference that provides security consulting, training, and briefings to hackers, corporations, and government agencies around the world.
What black hat hackers use?
Black hat hacking makes use of ransomware, malware, and other tactics to break through a system's defenses.
The black hat hackers can then access, steal, and leverage the data found.
Some of their techniques involve social engineering, botnets, DDoS attacks, spyware, and more.
What coding language do black hat hackers use?
Black hat hackers use SQL to develop hacking programs based on SQL injection.
Hackers use it to run unauthorized queries to obtain unhashed passwords.
|
Becoming a Black Hat Hacker
Since the person is becoming a Blackhat Hacker there is absolutely no reason to with Photoshop tutorials in the form of PDF files containing viruses. |
|
$atellite Hacking for Fun & Pr0fit!
– Bluetooth. – RFID. – Full Disclosure / White Hat! ? Freelance research / training / lecturing. Page 3 |
|
Google Hacking for Penetration Testers
Advanced operators can be combined in some cases. Advanced Operators at a Glance. Page 6. Crash course in advanced operators. |
|
Hacking in a Foreign Language: A Network Security Guide to Russia
2002?7?19? Off Topic. How to Defend? Social Engineering. Phreaking. Programming. Trinkets: Buy and Sell. Operating Systems. People: White/Black Lists. |
|
Black Hat Hacker White Hat Hacker Gray Hat Hacker
Black-hat Hackers are also known as an Unethical Hacker or a Security Cracker. These people hack the system illegally to steal money or to achieve their own |
|
Hacking a Professional Drone
The goal of this talk is to give insights into the security of. Unmanned Aerial Vehicles (UAVs) and to show that professional. |
|
Hacking Databases for Owning your Data
You can see why cyber criminals are going for your data of course on black market the prices won't be the same (maybe yes) |
|
FREE-FALL: TESLA HACKING 2016
Keen Security Lab of Tencent. (aka KeenLab or KeenTeam). • Researchers in KeenLab who are focusing on the cutting-edge security research of smart cars. |
|
FREE-FALL: HACKING TESLA FROM WIRELESS TO CAN BUS
In September 2016 our team (Keen Security Lab of Tencent) successfully implemented a remote attack on the Tesla Model S in both Parking and Driving mode. |
|
Modern Intrusion Practices Modern Intrusion Practices
Training “Hacking Inside-Out”. Ascure nv/sa http://www.ascure.com/education/Sheet%20Training%20HackingInsideOut%20v4.pdf. ISS's from Ethical Hacking course |
|
Becoming a Black Hat Hacker - DocDroid
Since the person is becoming a Blackhat Hacker, there is absolutely no reason would create Portuguese websites with Photoshop tutorials in the form of PDF |
|
Gray Hat Hacking, 2-nd Editionpdf - X-Files
Ethical issues among white hat, black hat, and gray hat hackers This book has So where do we stand on hacking books and hacking classes? Directly on top |
|
Blackhat Hacking - BlARROW
Blackhat Hacking How to hack and not get caught Brady Bloxham End user training but it should reflect current threat environment – Configure spam filter |
|
The Hackers Underground Handbook
should be regarded as “Ethical Hack” or “Ethical hacking” respectively You implement the Imagine a black hat discovers a vulnerability and codes an exploit for it For those of you that are visual learners, below are two great video courses |
|
Hacking
Ethical issues between a white hat and a black hat hacker This book has not pages/frontline/shows/hackers/risks/csi-fbi2000 pdf How Does This Stuff So where do we stand on hacking books and hacking classes? Directly on top of a slip- |
|
Brochure - Black Hat
Briefings Training Europe 2005 29 March-1 •Obtain in-depth knowledge at hands-on Training classes preceding Google Hacking for Penetration Testers |
|
$atellite Hacking for Fun & Pr0fit - Black Hat
– Bluetooth – RFID – Full Disclosure / White Hat ○ Freelance research / training / lecturing Page 3 |
|
Johnny Long - Black Hat
6 juil 2004 · Results 1 - 10 of aboul 633,000 for google hacker (0 24 seconds) [PDF] The Google Hacker's Guide Crash course in advanced operators |
|
Hacking Training - Claranet
Claranet Cyber Security - Hacking Training conventions such as Black Hat through to individual companies with a small Software (Browser, PDF, Java) 15 |









![Hacking communities in the Deep Web [Updated 2021] - Infosec Resources Hacking communities in the Deep Web [Updated 2021] - Infosec Resources](https://d2sofvawe08yqg.cloudfront.net/web-hacking-101/hero2x?1549474931)
![Web Hacking 101 by Peter Yaworski [Leanpub PDF/iPad/Kindle] Web Hacking 101 by Peter Yaworski [Leanpub PDF/iPad/Kindle]](https://4.bp.blogspot.com/-F7K85WIl1PU/UmZj3p65CqI/AAAAAAAAFOM/JqvLYlOxsEU/s1600/3.gif)




