black hat hacking tricks pdf
|
Top Ten Web Attacks
Why would a web server telnet out? Page 8 Futility of Firewalls • E-commerce / Web hacking is unfettered |
|
Beginner to Expert Guide to Computer Hacking Basic Security and
This book will teach you how you can protect yourself from most common hacking attacks -- by knowing how hacking actually works! |
|
Technology Safety and Hacking
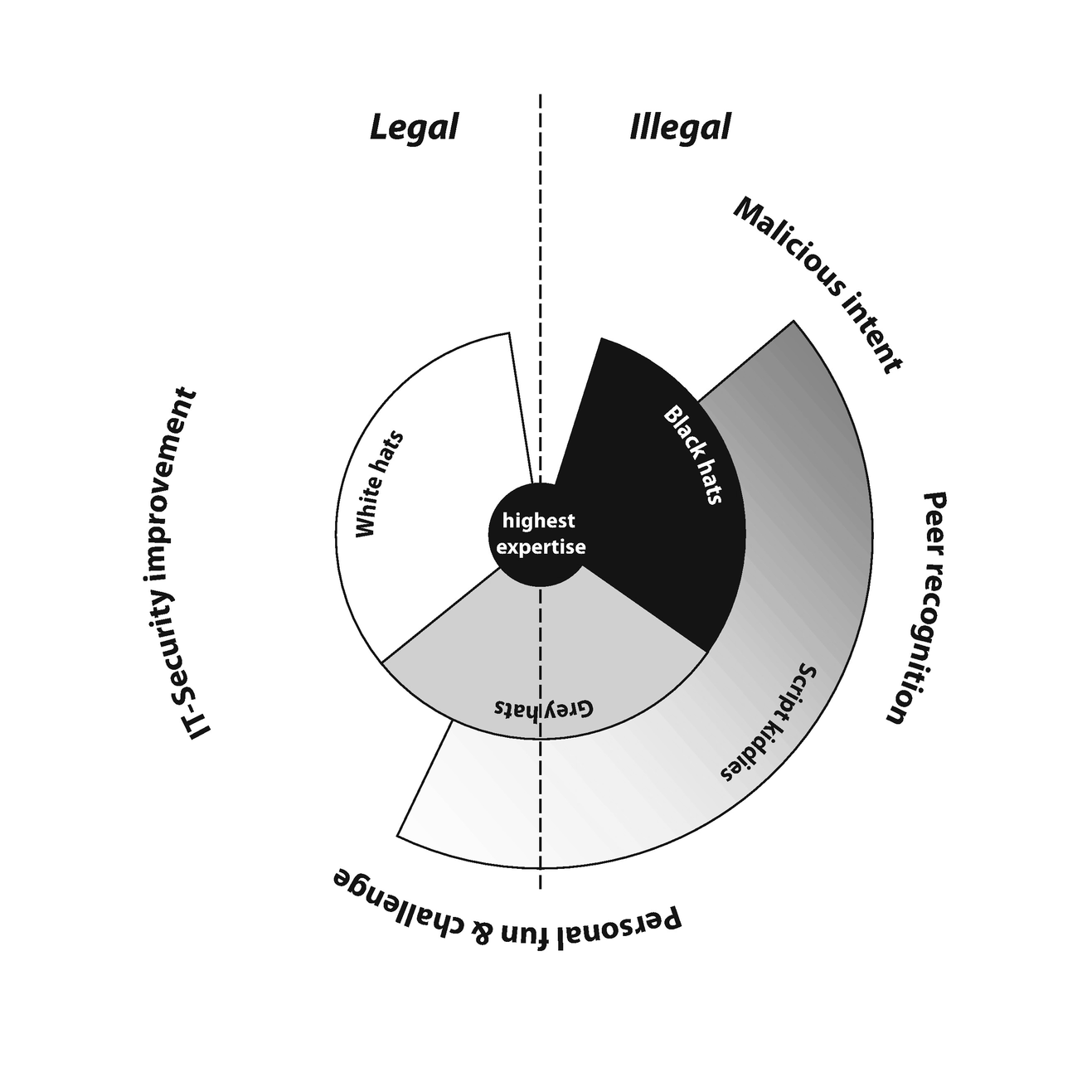
Security researchers – benign hackers called “white hats” find and fix flaws They use the same techniques as other hackers but for good Why do they hack? • |
|
When IoT Attacks:
Hacking A Linux-Powered Rifle Page 2 Who are we? • Runa A Sandvik • Michael Auger Page 3 Page 4 Why are we doing this? • A gun with WiFi and fancy |
What is purple hat hacking?
Purple hat hackers train their skills by hacking their own computer as an exercise.
This entails using one PC to hack another PC that they own, then assessing their hacking techniques.What is blue hat hacker?
Blue hat hackers aren't amateurs or script kiddies like the green hat hackers.
They are experts who focus on penetration tests, malware analysis and vulnerability assessment.
They are hired by organizations or security firms to identify and assess security weaknesses, usually before a product release.
|
Google Hacking for Penetration Testers
INURL:orders. INURL:admin. FILETYPE:php. Putting operators together in intelligent ways can cause a seemingly innocuous query… Page 10. Google Hacking Basics. |
|
Hacking Mifare Classic Cards
Oct 21 2014 hack Mifare Classic cards are developed |
|
FREE-FALL: HACKING TESLA FROM WIRELESS TO CAN BUS
remotely hacking Tesla cars can be feasible. Besides Wi-Fi tricks when in cellular mode we believe that phishing and user mistyping can also lead to. |
|
Our Favorite XSS Filters/IDS and how to Attack Them
XSS. JavaScript Tricks AppsecEU09_CarettoniDiPaola_v0.8.pdf. Other Tricks ... Open source - a lot of people "hack it" in their "free. |
|
Hacking VoIP Exposed
History has shown that most advances and trends in information technology (e.g. TCP/IP Wireless 802.11 |
|
Hacking in a Foreign Language: A Network Security Guide to Russia
Jul 19 2002 Off Topic. How to Defend? Social Engineering. Phreaking. Programming. Trinkets: Buy and Sell. Operating Systems. People: White/Black Lists. |
|
A New Era of SSRF - Black Hat
The largest hacker conference in Taiwan founded by chrO.ot. About Orange Tsai Cat in Carpet https://carpet.vidalondon.net/cat-in-carpet/ ... |
|
Black Hat
Hacking by Air Sea |
|
Bypassing Self-Encrypting Drives (SED) in Enterprise Environments
Nov 2 2015 Finally |
|
Title Track Abstract
Argues relevance/importance of the presentation at Black Hat Since the Aurora Incident brought nation-state hacking into the. |
|
THE HACKING BIBLE: The Dark secrets of the hacking world - Pirate
CHAPTER 7: HACKING TIPS AND TRICKS CONCLUSION Hacking can be dangerous for the Black Hat hackers and it can bring them the death, in the same |
|
Gray Hat Hacking, 2-nd Editionpdf - X-Files
even the novice, Gray Hat Hacking, Second Edition is a fantastic book for anyone Ethical issues among white hat, black hat, and gray hat hackers tools in your bag of tricks to fight the bad guys—technology, knowledge of how to use |
|
Hacking Intranet Websites from the Outside: JavaScript - Black Hat
8 mar 2006 · Hacking Intranet Websites from the Outside Hacking the Intranet More Dirty Tricks Tops the Web Hacking Incident WHXSSThreats pdf |
|
Black Hat Hackers Handbooks
10 jan 2021 · hat hacker home facebook, black hat hacking tutorials pdf free download wordpress com, the hackers underground handbook hacking tricks, hacking |
|
Preview Ethical Hacking Tutorial (PDF Version) - Tutorialspoint
Hacking has been a part of computing for almost five decades and it is a very broad Hacking and make a career as an ethical hacker Black Hat Hackers |
|
Gray Hat Hacking - Caribbean Environment Programme - UNEP
Related with Gray Hat Hacking: The Ethical Hacker's Handbook: 2762314-file Black Hat Python-Justin Seitz 2014-12-14 In Black Hat Python, the latest from Justin process controlUse offensive memory forensics tricks to retrieve password flashcards, a glossary of key terms, and the entire book in a searchable pdf |
|
Computer Hacking: A beginners guide to computer hacking, how to
This book contains helpful information about computer hacking, and the skills required to before the bad guys (aka the black hat hackers) use them against you Some tricks include creating a denial of service by flooding the network with a |
|
Gray Hat Hacking - Computer Sciences User Pages
6 déc 2007 · help with Chapter 16 (and for providing the free PDF analysis tools at http://blog malicious hacker or “black hat” will place hidden text within a page tools in your bag of tricks to fight the bad guys—technology, knowledge |
|
Introduction to Ethical Hacking - Principle Logic, LLC
the good guys wore white cowboy hats and the bad guys wore black cowboy involves the same tools, tricks, and techniques that hackers use, but with one |

![40 Best Hacking Books for Beginners PDF [2018 Collection] 40 Best Hacking Books for Beginners PDF [2018 Collection]](https://cdn.slidesharecdn.com/ss_thumbnails/ebook-pdfuntoldwindowstipsandsecretsankitfadia-130818105655-phpapp02-thumbnail-4.jpg?cb\u003d1376823492)








![Hacking communities in the Deep Web [Updated 2021] - Infosec Resources Hacking communities in the Deep Web [Updated 2021] - Infosec Resources](https://techwafer.com/wp-content/uploads/2018/11/Hacking-Book-PDF.jpg)






