black hat hacking tutorials pdf
What are the 3 types of hackers?
White hat hackers probe cybersecurity weaknesses to help organizations develop stronger security; black hat hackers are motivated by malicious intent; and Gray hat hackers operate in the nebulous area in between — they're not malicious, but they're not always ethical either.
|
Google Hacking for Penetration Testers
Google Hacking Basics. INURL:orders. INURL:admin. FILETYPE:php. Putting operators together in intelligent ways can cause a seemingly innocuous query… |
|
Becoming a Black Hat Hacker
I will be assuming the person becoming a Blackhat has no previous knowledge about hacking and only knows the basics of computer systems much like an average |
|
Becoming a Black Hat Hacker
I will be assuming the person becoming a Blackhat has no previous knowledge about hacking and only knows the basics of computer systems much like an average |
|
Hacking in a Foreign Language: A Network Security Guide to Russia
19-Jul-2002 redirected to a Russian hacker site. • Russian server at 217.107.218.147. – Loaded backdoor and key logger onto victim. |
|
$atellite Hacking for Fun & Pr0fit!
– Bluetooth. – RFID. – Full Disclosure / White Hat! ? Freelance research / training / lecturing. Page 3 |
|
Hacking Mifare Classic Cards
21-Oct-2014 hack Mifare Classic cards are developed what completely jeopardized the card reputation. ... Mifare.pdf ... Curtouis Dark-Side Attack. |
|
Hacking Databases for Owning your Data
You can see why cyber criminals are going for your data of course on black market the prices won't be the same (maybe yes) |
|
Top Ten Web Attacks
Net-Square. BlackHat Asia 2002 Singapore Increased —web hacking“ activity. • Worms on the web. ... Essentially |
|
Untitled
Praise forGray Hat Hacking: The Ethical Hacker's Handbook Second Edition Ethical issues among white hat |
|
Hacking a Professional Drone
The goal of this talk is to give insights into the security of. Unmanned Aerial Vehicles (UAVs) and to show that professional. |
|
Becoming a Black Hat Hacker - DocDroid
I will be assuming the person becoming a Blackhat has no previous knowledge about hacking and only knows the basics of computer systems, much like an |
|
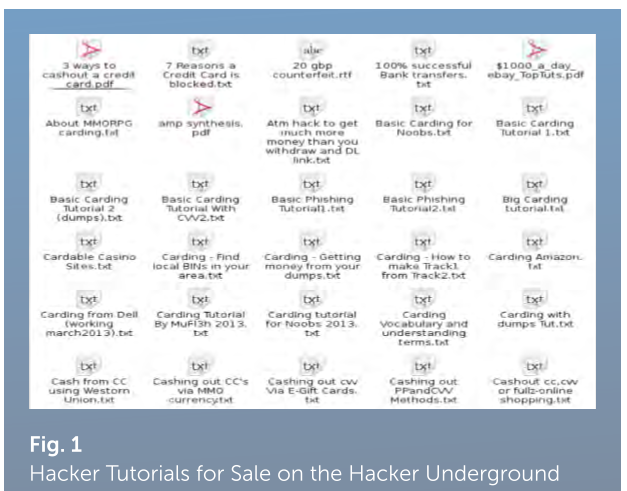
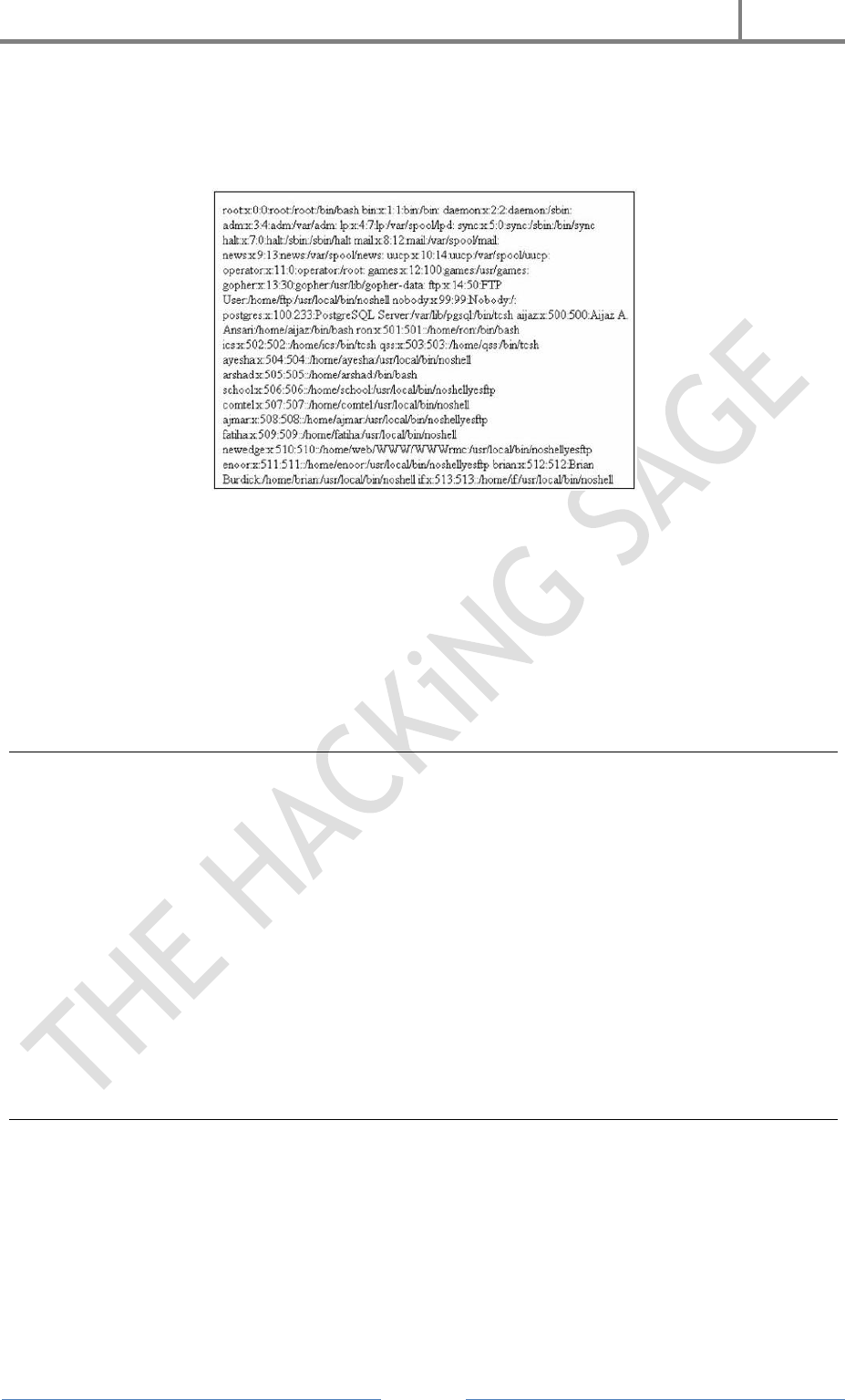
The Hackers Underground Handbook
reader develop a hacker defense attitude in order to prevent the attacks discussed Imagine a black hat discovers a vulnerability and codes an exploit for it |
|
Gray Hat Hacking, 2-nd Editionpdf - X-Files
tations of a gray hat hacker This section: • Clears up the confusion about white, black, and gray hat definitions and characteristics • Reviews the slippery ethical |
|
Preview Ethical Hacking Tutorial (PDF Version) - Tutorialspoint
place in 1960 at MIT and at the same time, the term "Hacker" was originated Hacking and make a career as an ethical hacker Black Hat Hackers |
|
$atellite Hacking for Fun & Pr0fit - Black Hat
Started doing this in late 90's – So, err why did it take so long to publish? Page 4 Feed Hunting ○ Look for 'interesting' satellite feeds – Scan all satellites |
|
Johnny Long - Black Hat
6 juil 2004 · [PDF] The Google Hacker's Guide FL Forn: PDFAdobe Acrobat - View HTML Tra c ker's Guide johnnyihackslun com http:/johnny ihackstuff |
|
Top Ten Web Attacks - Black Hat
Content/Application based attacks are still perceived as rare Page 9 The Web Hacker's Toolbox Essentially, all a web hacker needs |
|
Making money on the Web, the black hat way
“You're a hacker? Can you hack a bank?” Application Service Providers (ASP) offer hosting for banks, credit unions, and other financial services companies |
|
Black Hat Python Programming For Hackers And Pentesters Justin
systems and application security have you ever been involved orblack hat hacking tutorials pdf april 14 at 8 20pm black hat python python programming for |











![Hacking communities in the Deep Web [Updated 2021] - Infosec Resources Hacking communities in the Deep Web [Updated 2021] - Infosec Resources](https://img.wonderhowto.com/img/01/35/63530139573578/0/hack-like-pro-spoof-dns-lan-redirect-traffic-your-fake-website.w1456.jpg)

![PDF] C++ Hacker's Guide free tutorial for Beginners PDF] C++ Hacker's Guide free tutorial for Beginners](https://miro.medium.com/max/1200/1*LqUoEOyj80ZcwV47wtgdZA.png)



![Web Hacking 101 by Peter Yaworski [Leanpub PDF/iPad/Kindle] Web Hacking 101 by Peter Yaworski [Leanpub PDF/iPad/Kindle]](https://www.ceos3c.com/wp-content/uploads/2020/12/Best-Hacking-Books-Featured.jpg)






![PDF] Hacking Secret Ciphers with Python free tutorial for Beginners PDF] Hacking Secret Ciphers with Python free tutorial for Beginners](https://allfasr590.weebly.com/uploads/1/2/4/9/124999688/411632539.jpg)



![PDF] Hacking \u0026 Tor: The Complete Beginners Guide To Hacking Tor \u0026 PDF] Hacking \u0026 Tor: The Complete Beginners Guide To Hacking Tor \u0026](https://img.wonderhowto.com/img/84/78/63672151053917/0/to-hack-android-device-with-termux-android-part-1-over-internet-ultimate-guide.w1456.jpg)



