c pointers stack overflow
What are pointers in C stack overflow?
In computer science, a pointer is a programming language data type whose value refers directly to (or "points to") another value stored elsewhere in the computer memory using its address.30 sept. 2008
There are several methods for detecting stack overflow in C / C++ programs:
There are several methods for detecting stack overflow in C / C++ programs:
1One of the most reliable ways is to use a memory debugging tool, such as Valgrind.
2) Valgrind can detect a range of memory issues, including stack overflows, and it can also provide detailed information about the source of the problem.
How to avoid stack overflow in C?
1Use a debugger: Debuggers allow you to inspect the program's execution and examine the call stack.
2) Enable compiler warnings: Modern compilers often provide warnings or hints about potential stack overflow issues.
3) Code review and testing: Review your code for recursive functions, large local variables, and deep nesting.
What happens when stack overflow in C?
When a stack overflow occurs, the excess data can corrupt other variables and address data, effectively changing variable values and overwriting return addresses.
In some cases, this will cause the program to crash.
|
Proceedings of the 12th USENIX Security Symposium
8 août 2003 Protecting Pointers From Buffer Overflow Vulnerabilities ... we provided the StackGuard defense [9] against stack. |
|
More Exploits of Buffer Overflows and Countermeasures
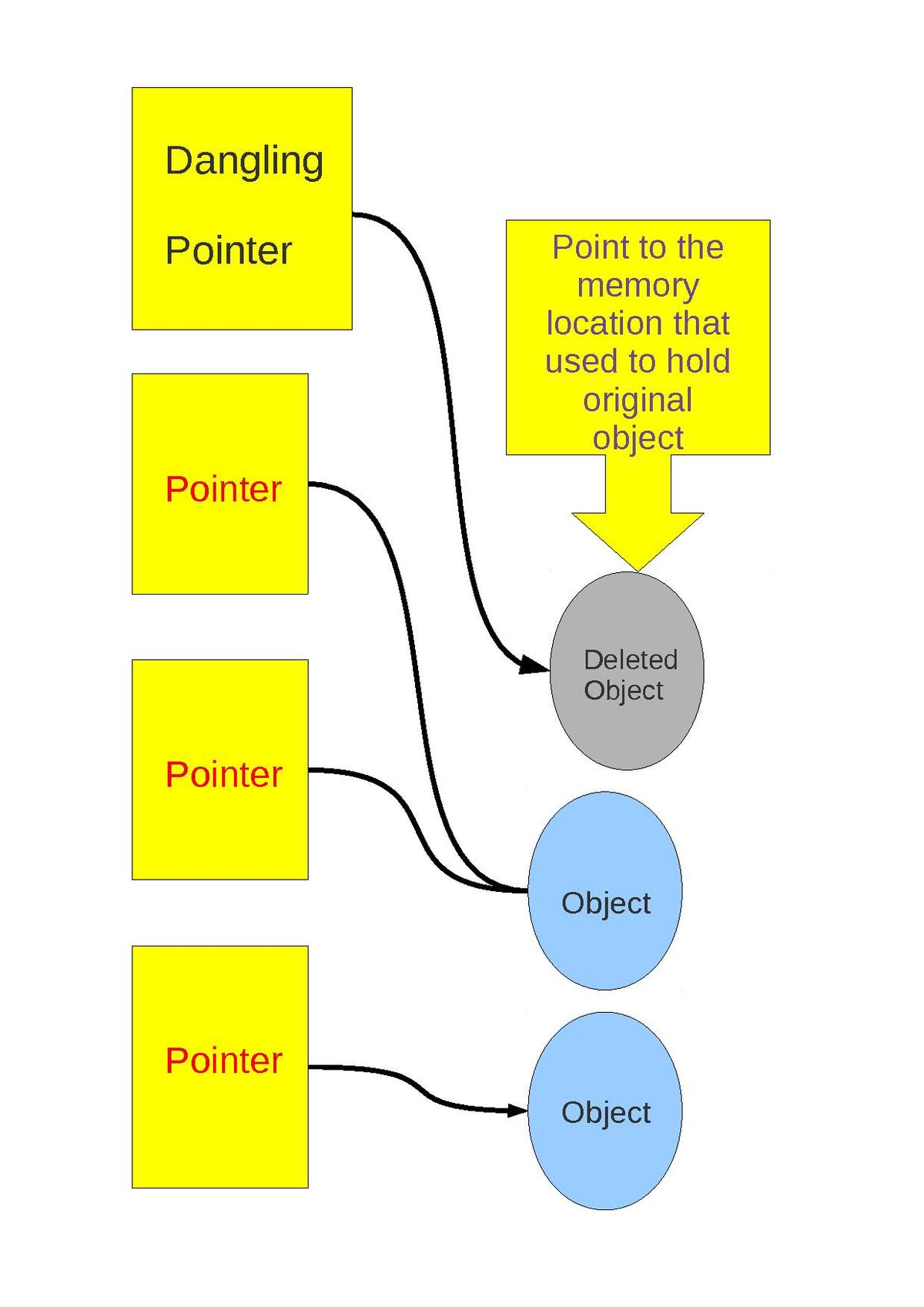
C++: call to a member function passes as an argument “this” pointer to an object on the stack. Stack overflow can overwrite this object's vtable pointer and. |
|
Online Stack Overflow Detection on the TMS320C28x DSP
1 mai 2003 A stack overflow in an embedded DSP application generally produces a ... C-source code is provided that contains functions for implementing. |
|
Delta Pointers: Buffer Overflow Checks Without the Checks
Despite decades of research buffer overflows still rank among the most dangerous vulnerabilities in unsafe languages such as C and. C++. Compared to other |
|
Smashing The Stack For Fun And Profit Aleph One Introduction
buffer we are trying to overflow will be. Here is a little program that will print its stack pointer: sp.c unsigned long get_sp(void) {. |
|
Delta Pointers: Buffer Overflow Checks Without the Checks
19 juin 2018 Delta Pointers: Buffer ... Buffer overflows still very common today ... c y. (m s. ) Throughput (x1000 reqs/s). Baseline. Delta Pointers. |
|
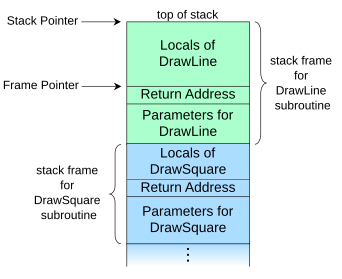
Chapter 4 - Buffer Overflow Attack
It is called frame pointer. This register points to a fixed location in the stack frame so the address of each argument and local variable on the stack frame |
|
3.1 Pointers and Strings Security Module
Buffer overflow problems arise in C style languages that provide programmers with pointers to allocated memory entrusting the programmer to write code that |
|
A Study of Overflow Vulnerabilities on GPUs
24 nov. 2017 and function pointer overflow in struct also can be exploited on GPUs. ... overflow b and consequently corrupt the stack variable c that ... |
|
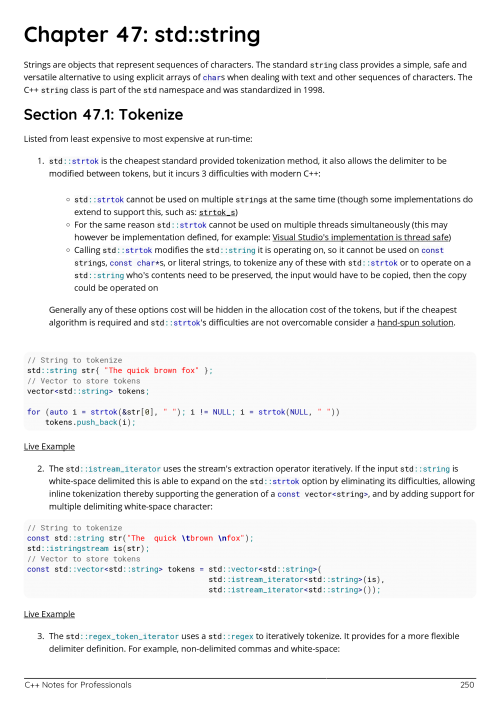
Module 5: Buffer Overflow Attacks
Stack Pointer Register: Stores the memory address to which the stack pointer (the current top of gets(string)- C routine vulnerable for buffer overflow. |
|
Buffer Overflow Attacks - Washington
Stack Pointer: points to the top of the stack (lowest address) Attack 1: Stack- based Buffer Overflow Clobber the Attack 2: Heap-based Buffer Overflows |
|
Stack & Heap Overflows
25 jan 2018 · the fixed information in every stack frame: the frame pointer and return address Stack overflow exploit return address attack code buffer |
|
A New Data Randomization Method to Defend Buffer Overflow Attacks
for non-stack overflow it can do nothing In this paper, we use the randomization on the array and pointer variables in the program space to protect the buffers, |
|
Overflowing the stack on Linux x86 - USC
is used to overflow a buffer stored on the stack We begin you will learn • the technique of stack overflow, or stack pointer – the program must know this |
|
Module 5: Buffer Overflow Attacks - Jackson State University
The locations could hold other program variables or parameters or program control flow data (like return addresses and pointers to stack frames) – The buffer |
|
Delta Pointers: Buffer Overflow Checks Without the Checks - VUSec
In C and C++, a programmer can allocate a buffer object, which is a sequence of bytes somewhere in the address space For instance, variables on the stack are |



![PDF] Learning C language free tutorial for Beginners PDF] Learning C language free tutorial for Beginners](https://i140.photobucket.com/albums/r18/reeferx/stacktrace.png)

![RTOS Support] vApplicationStackOverflowHook although stack size RTOS Support] vApplicationStackOverflowHook although stack size](https://imgv2-1-f.scribdassets.com/img/document/441155085/298x396/1bcf59512c/1577592038?v\u003d1)