access definition computer
What does access mean?
Access, in the context of security, is the privilege or assigned permission to use computer data or resources in some manner. For instance, a user may be allowed read access to a file, but will not be allowed to edit or delete it.
What is the difference between Microsoft Access and Excel?
Microsoft Access is a helpful data analysis tool for businesses. Microsoft Access is a database management system (DBMS) used to store and manage data. Access is part of the Microsoft 365 suite, and is made for business and enterprise users. While they both involve tracking data, Access and Excel are very different programs.
How does Microsoft Access store data?
Microsoft Access stores data in its own format based on the Access Database Engine (formerly Jet Database Engine). It can also import or link directly to data stored in other applications and databases. Software developers, data architects and power users can use Microsoft Access to develop application software.
What can I do with access?
Take advantage of your data with the power of Access—without writing code or becoming a database expert: Use templates to build databases quickly. Easily find and report on data stored in Access. Create rich data entry forms. Import, transform, and export a variety of data sources. Want more? Need more help? Want more options?
Try it
Do you have an idea for a database to help your team work more efficiently? With Access, you don’t have to be a developer to implement it. Take advantage of your data with the power of Access—without writing code or becoming a database expert: •Use templates to build databases quickly. •Easily find and report on data stored in Access. •Create rich data entry forms. •Import, transform, and export a variety of data sources. support.microsoft.com
Want more?
Taking a scenic drive through AccessWhat's new in AccessExcel trainingOutlook training support.microsoft.com

What is Microsoft Access? What is a Microsoft Access Database?

What is Microsoft Access and What Do You Use It For?

Access: Getting Started
|
19-783 Van Buren v. United States (06/03/2021)
3 juin 2021 computer to access a law enforcement database to retrieve information ... the definition: “to access a computer with authorization and. |
|
ETSI GS MEC 003 - V2.1.1 - Multi-access Edge Computing (MEC
In addition to the definitions for the generic reference architecture in clause 6.1 the following new architectural assumptions apply: •. The MEC platform is |
|
A Code-Based Approach to Unauthorized Access Under the
means to access a computer without authorization and in terms of what it means to exceed authorized access. Congress failed to define key terms in the CFAA. |
|
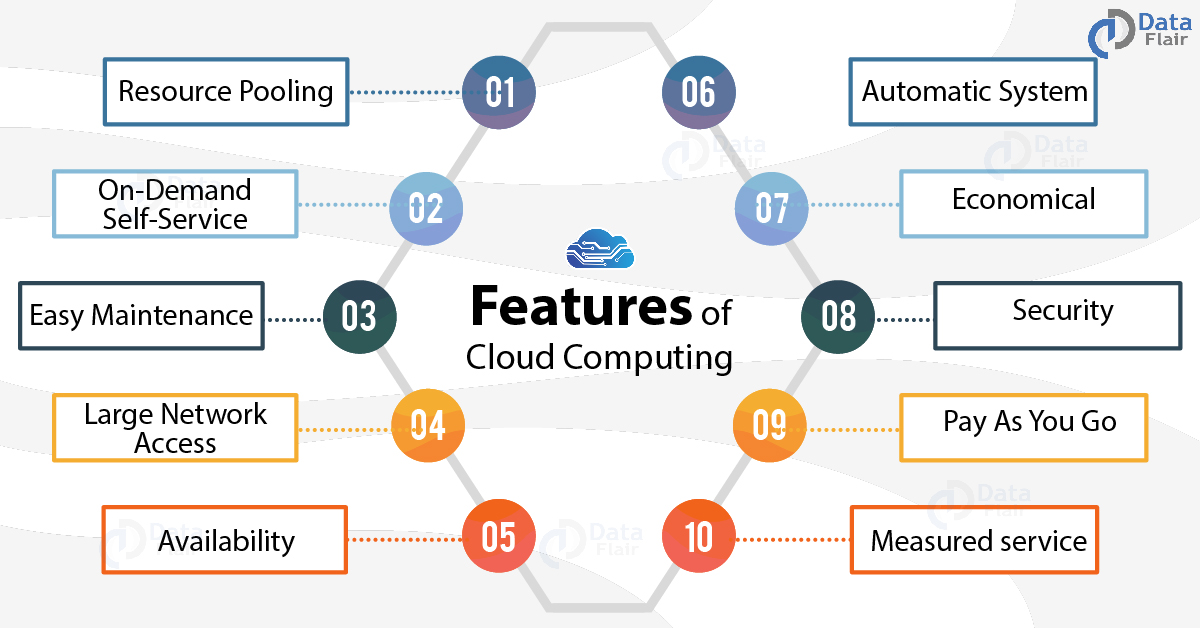
NIST SP 800-145 The NIST Definition of Cloud Computing
Cloud computing is a model for enabling ubiquitous convenient |
|
Offense of Unauthorized Access in Computer Crimes Legislation - A
We are going to discuss this question in the next two subsections. B. Definition and the Scope of the Act Criminalized. Unauthorized access which is also |
|
A Code-Based Approach to Unauthorized Access Under the
means to access a computer without authorization and in terms of what it means to exceed authorized access. Congress failed to define key terms in the CFAA. |
|
Guide to Attribute Based Access Control (ABAC) Definition and
National Institute of Standards and Technology. Attn: Computer Security Division Information Technology Laboratory. 100 Bureau Drive (Mail Stop 8930) |
|
Transborder access and jurisdiction: What are the options?
19 See the broad definition of computer data in Article 1 Budapest Convention. 20 6HH WKH GHILQLWLRQ RI ³WUDIILF GDWD´ LQ $UWLFOH %XGDSHVW &RQYHQWLRQ. |
|
COMPUTER TRESPASS (Access to Computer Material) Penal Law
to believe that he or she had authorization to use the computer.]1. The following terms used in that definition have a special meaning:. |
|
Prosecuting Computer Crimes
It is relatively easy to define the universe of individuals who lack any authorization to access a computer. When someone from this group of people. |
|
CYBER CRIMES
30 jan 2008 · Offenses against computer data and systems C Important definitions trespass”; illegal access may result in damage to computer systems |
|
Cybercrimes Scope: Interpreting Access and - NYU Law Review
enacted computer crime statutes that prohibit "unauthorized access" to computers No one meaning of crimes such as murder, burglary, and theft is broadly |
|
Manual for measuring ICT access and use by households and - ITU
technology (ICT) statistics, based on internationally agreed definitions and including some ICT variables: presence of computer, access to Internet, access to |
|
2nd revision of the OECD Model Survey on ICT Access and Usage
For the updated definitions of e-commerce and ICT industries, products and occupations, Households with computer access at home ( of all households) |
|
Computer Fraud and Abuse Act - Department of Justice
Broadened the definition of “protected computer” in 18 U S C § 1030(e)(2) to can exceed authorized access within the meaning of section 1030(e)(6) when |
|
A Semantic Context-Aware Access Control Framework for Secure
for Secure Collaborations in Pervasive Computing Environments the definition of access control policies in dynamic scenarios like inter-organizational |
|
The Basics of Cloud Computing - US-CERT
1 1For more information please see The NIST Definition of Cloud Computing at important part of the equation is having internet access Your email is not |
![PDF] Introduction to Access 2016 free tutorial for Beginners PDF] Introduction to Access 2016 free tutorial for Beginners](https://0.academia-photos.com/attachment_thumbnails/40797077/mini_magick20190220-7802-irngr2.png?1550686103)

![A To Z] Computer Related Full Form PDF » GKPUR A To Z] Computer Related Full Form PDF » GKPUR](https://i1.rgstatic.net/publication/342753218_Attribute-Based_Encryption_for_Cloud_Computing_Access_Control_A_Survey/links/5f2c24f2a6fdcccc43adfff1/largepreview.png)




![PDF] Access Database Design free tutorial for Beginners PDF] Access Database Design free tutorial for Beginners](https://upload.wikimedia.org/wikipedia/commons/thumb/0/03/Flow-diagram-computer-booting-sequences.jpg/220px-Flow-diagram-computer-booting-sequences.jpg)