bind dnssec
What is the BIND 9 DNSSEC guide?
The BIND 9 DNSSEC Guide, now an appendix to the BIND Administrative Reference Guide, is a long-format guide that explains a lot of the background and the “why” of DNSSEC, as well as the “how.” It includes the KASP (Key and Signing Policy) tool. The BIND 9 Administrator Reference Manual (ARM) on ReadTheDocs.
Can bind sign all DNSSEC zone files automatically?
It’s possible to tell BIND to sign all zone files automatically by setting an appropriate option in named.conf.options but since this is our first DNSSEC zone we want to do them one at a time.
How do I enable DNSSEC on a slave server?
The slave servers only require DNSSEC to be enabled and the zone file location to be changed. Edit the main configuration file of BIND. Place these lines inside the options { } section if they don’t exist. dnssec-enable yes; dnssec-validation yes; dnssec-lookaside auto; Edit the file option inside the zone { } section.
How secure is a BIND DNS?
This is not secure enough since the IP can be easily forged or spoofed. The DNS resolver is not designed to detect any forged response to one of its queries. Securing the BIND DNS is important since it precludes attackers from tampering with the DNS response, masquerading and manipulating the authoritative DNS cache.
Step 1: Install Bind DNS Server
This setup requires the latest BIND version, probably any version above 9.9. The BIND server can be installed using the aid provided in the below guides: 1. Configure Master BIND DNS on Rocky Linux / AlmaLinux 9 2. Configure BIND Master DNS Server on Debian 3. Configure Slave BIND DNS Server on Ubuntu Once installed, check the version with the comm
Step 2: Enable DNSSEC on The Bind Master
Edit the master configuration and enable DNSSEC. Ensure the below lines are available in the config; computingforgeeks.com
Step 3: Generate Key Pair For ZSK and KSK
To generate the key pair for DNSSEC, switch to the BIND directory as root Remember the above directory should contain your zone files. Generate the Zone Signing Key for your zone with the command: For this guide, I will be using: 1. zone names: 1.1. computingforgeeks.localas the forward zone 1.2. 205.168.192.in-addr.arpaas the reverse zone. 2. Zone
Step 4: Sign The Generated Keys
Now sign the zone keys using the dnssec-signzonecommand with the below syntax: For example in my Forward zone: Reverse Zone: Sample output: After this, you will have new zone files as forward.signed, and reverse.signed. Now edit the below file to accommodate the newly signed zone files; Make the changes to the file. For example on CentOS; Set the r
|
Key & Signing Policy (KASP) in BIND 9.16
auto-dnssec maintain;. }; ? Zone must be either Dynamic or have inline-signing set. ? Expects keys to be created with dnssec-keygen. |
|
BIND 9.7 DNSSEC for Humans
“DNSSEC for Humans”. Take the pre-9.7 commands for creating a typical set of DNSSEC keys in BIND with. NSEC: ZSK: dnssec-keygen –a RSASHA1 –b 1024 –n. |
|
Hands-On Lab
Jum. I 8 1437 AH Hands-On Lab. Configuring BIND + DNSSEC + Hyperlocal ... Connecting to the server to install and configure BIND. |
|
CommunityDNS Performance testing of BIND NSD and CDNS
As more and more zones are being signed with DNSSEC and more DNS queries requesting a signed answer CommunityDNS (CDNS) ran tests to asses the readiness of |
|
DNSSEC HOWTO
BIND DNSSEC tools if you use a name different from the domain name you might confuse those tools. The algorithm_id identifies the algorithm used: 1 for RSA |
|
A Story on Unsupported DNSSEC Algorithms
rm unsupported algorithms. ? RFC 6944. ? draft-ietf-dnsop- algorithm-update. ? Removed in BIND 9: – RSAMD5. – GOST. – DSA. – DSA-NSEC3-SHA1 |
|
ISC - Entrust solution for high integrity DNSSEC verification
integrity DNSSEC verification. Entrust delivers high assurance signing solution to enhance security for BIND. HIGHLIGHTS. • Mitigate threats to the DNS by. |
|
Enabling DNSSEC validation with the root trust anchor in BIND
NOTE: This is only for the purpose of this lab - on the Internet you would simply use "unbound-anchor" to download the real root.key |
|
DNSSEC for BIND Quick Reference Guide
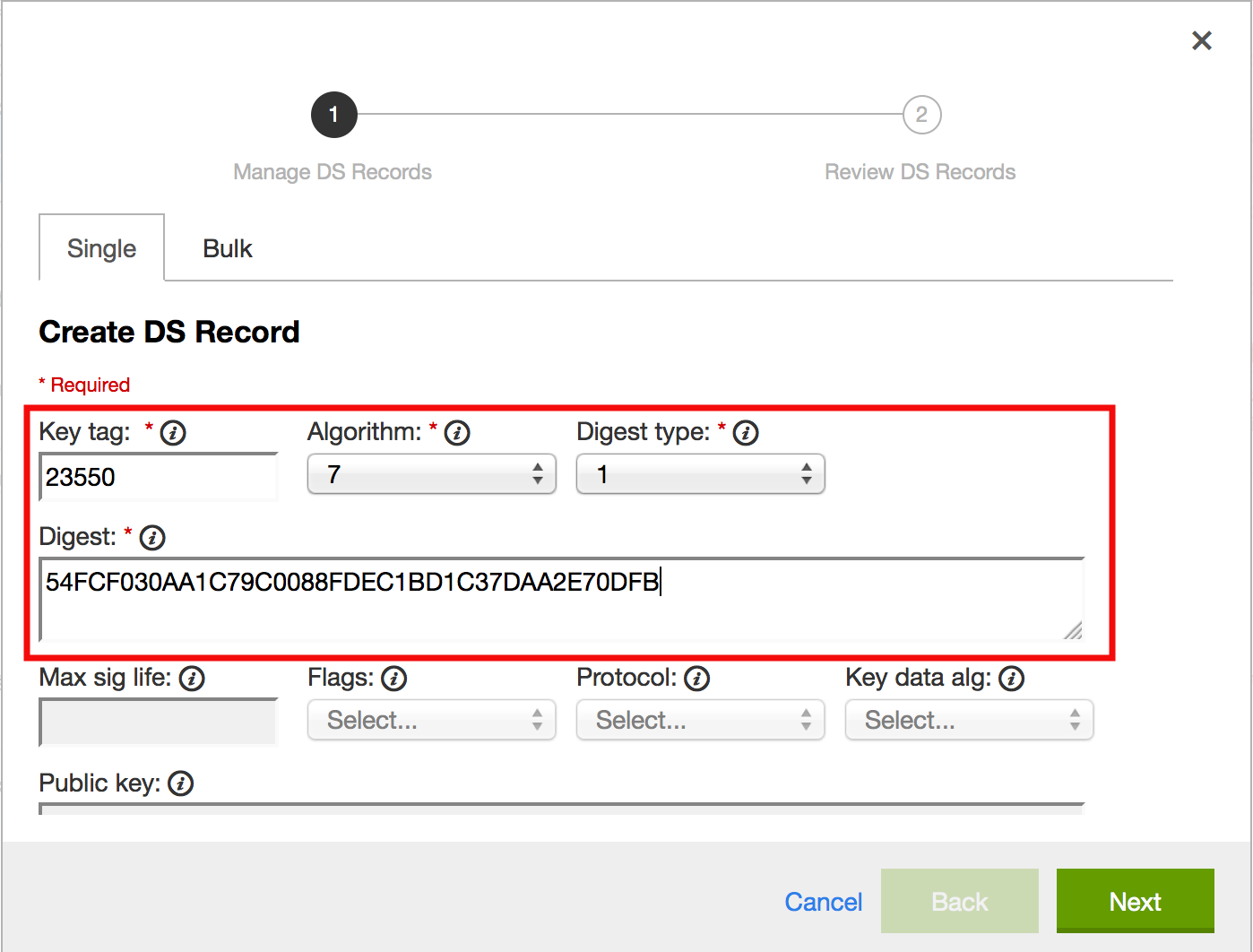
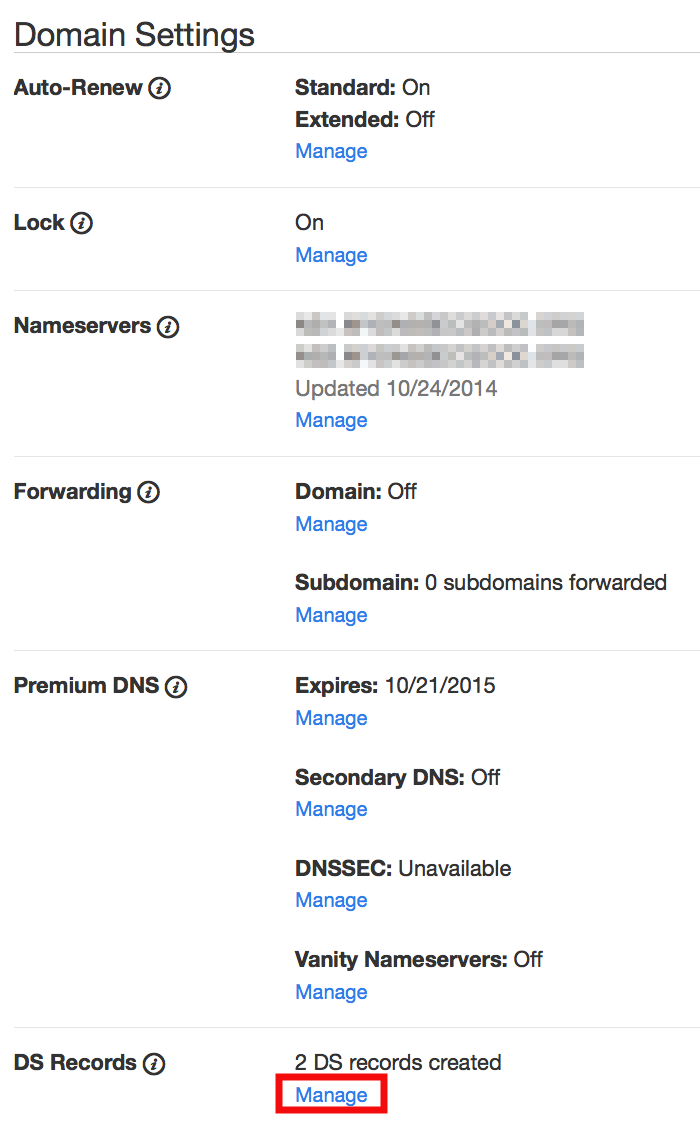
corporate rules for use of cryptography. Server requirements. BIND 9.10 or higher installed. Registrar or parent zone supports. DNSSEC via DS records. |
|
DNSSEC Validation Performance Testing
What is the performance hit on a typical ISP resolver if they would enable. DNSSEC validation for .SE today? Page 3. • ISC BIND 9.3.2. • Nominum CNS 1.6.0.3. |
|
Déployer DNSSEC, comment, quoi, où ? - Afnic
3 jui 2015 · gestion de DNSSEC avec les logiciels OpenDNSSEC+NSD ou avec BIND Ensuite le document décrira les étapes nécessaires à la mise en |
|
BIND 97 DNSSEC for Humans
Take the pre-9 7 commands for creating a typical set of DNSSEC keys in BIND with NSEC: ZSK: dnssec-keygen –a RSASHA1 –b 1024 –n ZONE example com |
|
DNSSEC for BIND Quick Reference Guide - FTP Directory Listing
BIND 9 10 or higher installed Registrar or parent zone supports DNSSEC via DS records Server's network environment supports TCP and large UDP for DNS |
|
DNSSEC HOWTO
To ease the process BIND introduces keysets A keyset is a small file, with the same syntax as a zone file, that contains one or more key signing keys of the |
|
A Best Practices Architecture for DNSSEC - Infoblox
Since 1997, when Eugene Kashpureff capitalized on a weakness in the implementation of the BIND name server to poison the caches of name servers around the |
|
Dnssec - Internet Systems Consortium
14 jui 2016 · DNSSEC provides digital signatures that allow validating clients to prove that DNS data BIND 9 7 ("DNSSEC for Humans") made life easier |
|
DNSSEC Tutorial - Shumon Huque
3 nov 2013 · popular ISC BIND DNS software and will cover both using DNSSEC to cryptographically sign your own DNS zones and configuring DNS |
|
Tutorial de DNSSEC: Firmado de zonas - LACNIC
12 sept 2018 · cd /var/cache/bind/keys # Generate a KSK sudo -u bind dnssec-keygen -a RSASHA256 -b 2048 -n ZONE -T DNSKEY -f KSK dnsseclab nz |