bit masking in c geeksforgeeks
How does bitmasking work?
Bitmasking is done by creating a bit mask for the operation that we need to perform. This bit mask will then be followed by a bitwise operation to achieve the desired output. Bitmasking is done by putting a mask (hiding some unnecessary bits based on some criteria) and setting or clearing the remaining bits.
How many bitwise operators are there in C?
There are basically 6 bitwise operators in C that can be used to manipulate bits which are as follows: Using these operators, we perform different bit masking techniques according to the requirements. Let’s discuss these techniques and how to implement them. 1. Setting a Bit
What is a bit mask?
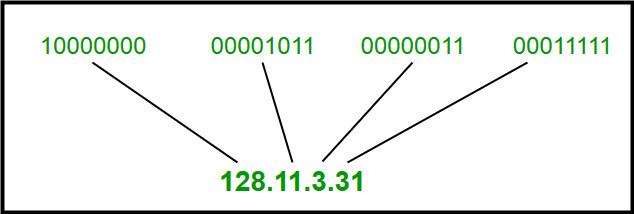
A bit mask is the fundamental technique to achieve bit masking. It is basically a binary pattern used to perform various bit-level operations like set, clear, toggle or checking if a bit is set or not. Assuming that we have the set of numbers, whose binary representation has 8 bits in it, we will use this as a reference in this article.
What is a bitmask in C?
A bitmask is a sequence of bits that can also be known as a bitset or bit field and is used to perform bitwise operations on the given data. There are basically 6 bitwise operators in C that can be used to manipulate bits which are as follows: Using these operators, we perform different bit masking techniques according to the requirements.
General Way to Implement Bitmasking
Sure, here are the steps for implementing bit-masking : 1. Create the list or array you wish to manipulate with bitmasking. 2. Establish the list or array’s size to determine how many bits you’ll need for the binary representation. 3. Check the corresponding bits for each index, then carry out the required operation based on their values. This coul
Applications of Bitmasking
Bitmasking is an effective method with numerous uses in computer science and technologies, such as: 1. Optimization:Algorithm optimization can be achieved using bitmasking, which substitutes bit-level operations for expensive ones. As an illustration, right shifting by one is a substantially faster operation than dividing by two. 2. Memory efficien
Advantages of Bitmasking
Greater speed:Bit-level operations typically occur more quickly than more conventional operations like addition or multiplication. Bitmasking enables a speedy and effective execution of sophisticat
Disadvantages of Bitmasking
Limited range:Bitmasks have a limited range since they can only represent a finite range of values. Bitmasking becomes impossible if there are more potential values than there are bits in the bitmask.Code complexity:Bitmasking can make a program harder to comprehend, especially if it uses complicated bitwise operations.Debugging:Bitwise operations have the potential to bring elusive bugs into programs. A misplaced bitwise operator, for instance, can radically alter the meaning of an expression.Restricted readability:While using bitmasks can make code shorter, those unfamiliar with the method may find it difficult to understand. As a result, maintaining and updating the code over time may
What Else Can You read?
Bitmasking and Dynamic ProgrammingBit Tricks for Competitive ProgrammingTravelling Salesman Problem using Bitmasking and DP geeksforgeeks.org
|
SECTION - A 1.
???/???/???? (ii) Consider a 3-bit error detection and 1-bit error correction ... (c) don't contain anything equivalent of program counter in a 'normal'. |
|
Al-a·•-
(v) When two 4-bit binary number A = (D) fewer masks for fabrication ... (C) latch the 8 bits of address lines. AD7-ADO into an external. |
|
??? ?????
???/???/???? c. 6 d 9. Let X. Y. Z be sets of sizes x y and z respectively. ... A CPU has 24-bit instructions. A program ... a. mask + 0 x 1 pos. |
|
Microelectronics Lab ELCT 708
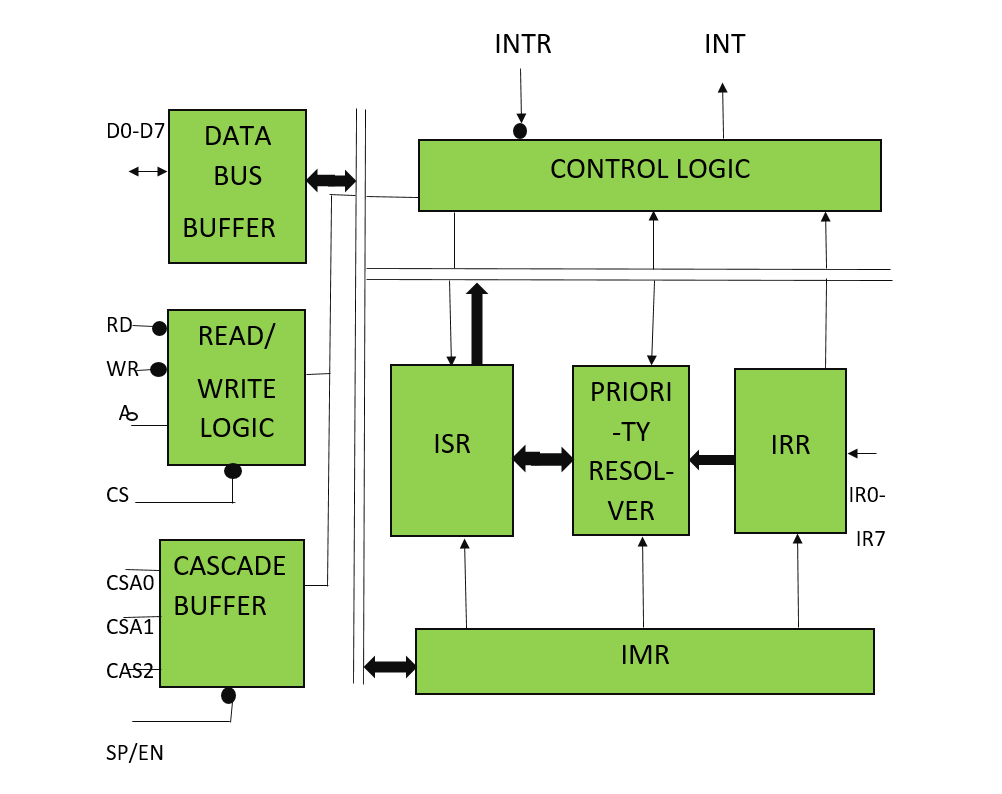
Mask Register. • Bit 0 – TOIE0: Timer/Counter0 Overflow Interrupt Enable. • When this bit is written to one |
|
Untitled
C-style bit manipulation versa by choosing a mask and a proper bit operation. For example the a letter has this binary ... GeeksForGeeks · C++ Articles. |
|
Finite State Machines C Programming on the MSP432 Lecture
C programming fundamentals. • Arrays. • Pointers uint32_t Out; // 6-bit output ... FSM Engine in C (Index into array). 8. Friendly. Mask. 9 SysTick ... |
|
ADSP-21xx (Rev C)
for bit manipulation multiplication |
|
Introduction To MIPS Assembly Language Programming
???/???/???? 3 Integer multiplication using bit shift operations . ... The Program Counter ($pc) register and calling a subprogram . |
|
True random number generators for cryptography: Design securing
???/???/???? C'était un des objectifs principaux du projet HECTOR ... lower bit rate than side channel mask generator does). That is why it is essential ... |
|
FPGA-BASED STEREO VISION SYSTEM FOR AUTONOMOUS
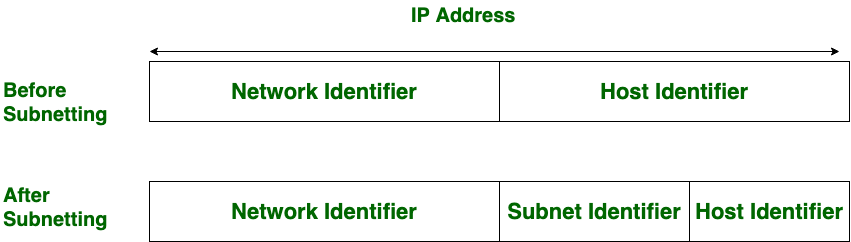
???/???/???? processor is able to send the output data via TCP/IP to a PC ... How many bits are dedicated to each part is defined with a Subnet Mask. |
|
Understanding Integer Overflow in C/C++ - University of Utah School
Our results show that integer overflow issues in C and C++ are subtle and complex, that they The low-level nature of C and C++ means that bit- and byte- level manipulation of register unsigned mask = (value ( value - 1 )); 11 return (value |
|
UNIT-1 notes
The individual flip flops in n-bit register is numbered from 0 in right most to n-1 in 4 different values: B, B', always “1”, or always “0” CSA PVP14 UNIT-1 Page 9 Mask operation : similar to the selective-clear operation, except that the bits of |
|
Unité dEnseignement : [07cm] Concours Programmation
Le langage C comporte plusieurs opérateurs "bit à bit" (et, ou, ou-exclusif, https ://en wikipedia org/wiki/Mask_(computing) c Gilles Menez from : https ://www geeksforgeeks org/add-two-numbers-without-using-arithmetic-operators/ 11 12 |
|
C++ function - RIP Tutorial
C-style bit-manipulation 48 Using std::bitset 48 Set all bits 48 C-style bit- versa by choosing a mask and a proper bit operation GeeksForGeeks · C++ |
|
Tcp ip vs osi model geeksforgeeks - Squarespace
Registry ID (5-bit) : The registry ID specifies the region to which it belongs fe80) C Ip Adresation Program, Subnet Mask & Default Gateway, Introduction |
|
Fusion Trees
the norm until fairly recently, and before that 16-bit We'll assume C integer operators work in Each node is annotated with several values (the masks |