ceh v10 pdf
|
CEH v10 Certified Ethical Hacker Study Guide by Ric Messier (z-lib
CEH v10 Certified Ethical Hacker Study Guide by Ric Messier (z-lib org) pdf Files master Breadcrumbs ebooks / CEH v10 Certified Ethical Hacker Study |
|
CEH v10 Certified Ethical Hacker Study Guide by Ric Messierpdf
16 avr 2018 · Page 1 CEHTM v10 Study Guide Page 2 Page 3 CEHTM v10 Certified Ethical Hacker Study Guide Ric Messier CEH GCIH GSEC CISSP Page 4 |
|
CEH v10
Public concerné : La formation et l'examen CEH v10 s'adressent aux: - Responsable sécurité - Auditeur - Professionnel de la sécurité - Administrateur de site |
|
CEH v10: EC-Council Certified Ethical Hacker Complete Training
CEH v10 covers new modules for the security of IoT devices vulnerability documents including Open Office Microsoft Office Adobe InDesign PDF SVG |
|
CEHv10-Brochure.pdf
The Certified Ethical Hacker (C |
|
CEH v10: EC-Council Certified Ethical Hacker Complete Training
CEH v10 covers new modules for the security of IoT devices vulnerability documents including Open Office |
|
CEH Exam Blueprint v4.0
CEH Exam Blueprint v4.0. 02. Domain. Sub Domain. Description. Number of. Questions. Weightage. (%). 1. Information. Security and. Ethical Hacking. Overview. |
|
CEH: Certified Ethical Hacker Study Guide
Entire Book in PDF. SERIOUS SKILLS. Exam 312-50. Exam EC0-350. Y GUIDE. Graves. 312-50. EC0-350. CEH™. C ertifi ed Ethical Hacker |
|
EC-Council
CEH Exam Blueprint. 1. Sec on. Knowledge of: Weight. Number of. I. Background. A. networking technologies (e.g. hardware |
|
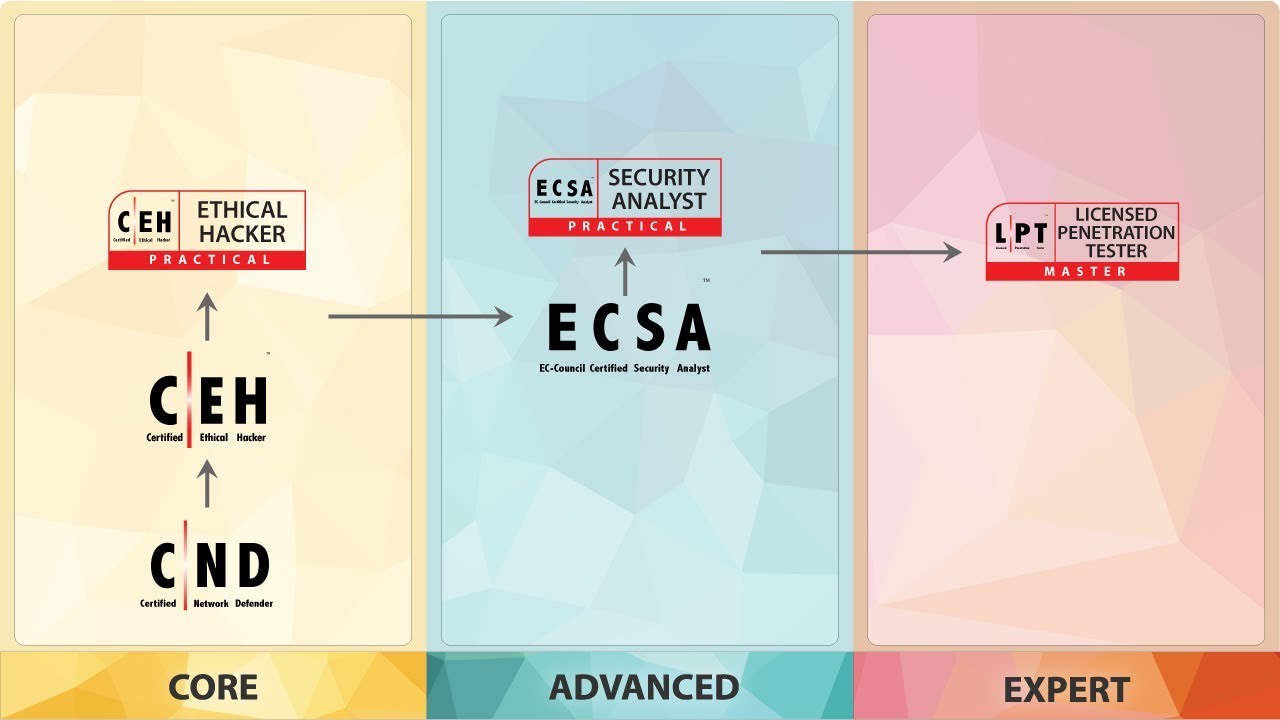
EC-Council Security Analyst v10 (ECSA)
This is a “Professional” level course with the. Certified Ethical Hacker being the “Core” and the Licensed Penetration Tester being the “Master” level. |
|
CHFI-v10-Brochure-1.pdf
CHFI v10 you will learn to unravel these pieces builds individual and team/organization cyber capabilities through the Certified Ethical Hacker. |
|
CEH Exam Blueprint v3.0
Malware (e.g. Trojan |
|
CEH v10: EC-Council Certified Ethical Hacker Complete Training
Cloud Computing technology is the most popular now a day because of its flexibility and mobility support. Cloud Computing allows the access to. |
|
CEH v10 - Hacking Mobile Platforms
We all know the rapid increase of mobile phone users and flexibility of function and advancement to perform every task has brought a dramatic shift. |
|
CERTIFIED ETHICAL HACKER V10 CERTIFIED - EC-Council
The Certified Ethical Hacker (CEH v10) program is a trusted and respected ethical hacking Certification program that any information security professional will |
|
CEH – Certified Ethical Hacker - Exclusive Networks
Le Certified Ethical Hacker (CEH v10) est une formation reconnue et respectée, dont chaque professionnel de la sécurité aura besoin Depuis sa création en |
|
EC-Council Certified Ethical Hacker (CEH) v100 COURSE OUTLINE
EC-Council Certified Ethical Hacker (CEH) v10 0 Students will learn how to scan , test, hack and secure target systems The course covers the Five Phases of |
|
CEH Study Guidepdf
CEH Certified Ethical Hacker is a trademark of EC-Council All other trademarks are the property of their respective owners Wiley Publishing, Inc , is not |
|
Certified Ethical Hacker (CEH) Version 10 Cert Guide - InformIT
Open Source Security Testing Methodology Manual 54 Information Security Systems and the Stack 54 The OSI Model 55 Anatomy of TCP/IP Protocols 57 |
|
Réussir la certification CEH, Certified Ethical Hacker - CERTyou
Réussir la certification CEH, Certified Ethical Hacker (Sécurité) Formation Informatique / Réseaux et Sécurité / Sécurité Qu'est ce que un certifié Certified |
![PDF] CEH v10: EC-Council Certified Ethical Hacker Complete Training PDF] CEH v10: EC-Council Certified Ethical Hacker Complete Training](https://image.slidesharecdn.com/cehv10certifiedethicalhackerstudyguide-191121122604/95/pdffree-library-ceh-v10-certified-ethical-hacker-study-guide-fullpages-1-638.jpg?cb\u003d1574339200)









![PDF] CEH v10: EC-Council Certified Ethical Hacker Complete Training PDF] CEH v10: EC-Council Certified Ethical Hacker Complete Training](https://www.yumpu.com/en/image/facebook/64531157.jpg)




![PDF] CEH v10: EC-Council Certified Ethical Hacker Complete Training PDF] CEH v10: EC-Council Certified Ethical Hacker Complete Training](https://image.isu.pub/180713073244-091ba226e638cbc3e15105d65843be87/jpg/page_1.jpg)





![PDF] CEH v10: EC-Council Certified Ethical Hacker Complete Training PDF] CEH v10: EC-Council Certified Ethical Hacker Complete Training](https://i.ebayimg.com/images/g/-lwAAOSwnuxeV8ym/s-l300.jpg)








![PDF] CEH v10: EC-Council Certified Ethical Hacker Complete Training PDF] CEH v10: EC-Council Certified Ethical Hacker Complete Training](https://imgv2-2-f.scribdassets.com/img/document/424843948/149x198/f4754d2b2b/0?v\u003d1)
![PDF] CEH v10: EC-Council Certified Ethical Hacker Complete Training PDF] CEH v10: EC-Council Certified Ethical Hacker Complete Training](https://www.darkwiki.in/wp-content/uploads/2018/10/Certified-Ethical-Hacker-V10-Course.jpg)


![PDF] CEH v10: EC-Council Certified Ethical Hacker Complete Training PDF] CEH v10: EC-Council Certified Ethical Hacker Complete Training](https://image.slidesharecdn.com/cehcertification-200104134519/95/ceh-certification-version-10-year-2019-1-638.jpg?cb\u003d1578145625)













![News] CEH v10 Certified Ethical Hacker Lab Tools Free Download News] CEH v10 Certified Ethical Hacker Lab Tools Free Download](https://www.certificationsdesk.com/uploads/product_images/1549543397_exam-img.png)












![PDF] READ CEH v10: EC-Council Certified Ethical Hacker Complete Train PDF] READ CEH v10: EC-Council Certified Ethical Hacker Complete Train](https://i.ytimg.com/vi/dOMzick-mQs/maxresdefault.jpg)
