cisco enable secret 5 decrypt
How do I read a Cisco Type 5 password?
... Take the type 5 password, such as the text above in red, and paste it into the box below and click "Crack Password". Javascript tool to convert Cisco type 5 encrypted passwords into plain text so that you can read them. This is done using client side javascript and no information is transmitted over the Internet or to IFM.
What is Cisco password type 0?
Cisco password type 0 is basically clear text password. There is no encryption nor obfuscation. It is the oldest and the most insecure method of storing passwords in Cisco devices. It should never be used. The following example shows type 0 password found in a Cisco configuration: As you can see, there is really nothing to crack or decrypt.
Is it possible to decrypt a password on a Cisco device?
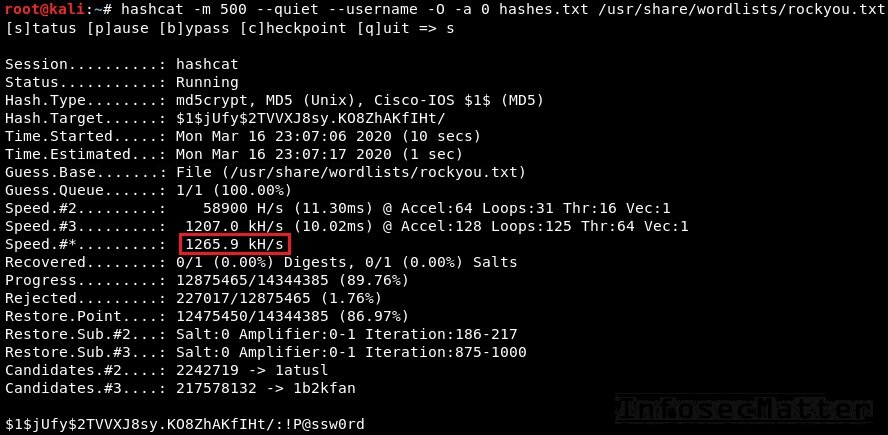
Running it once occasionally on a Cisco device is fine though, this is currently the Best Practice Type password to use. I have not proven it but I believe it is possible that the popular tool HashCat is able to decrypt these.
What is a type 5 secret in Cisco IOS XE?
If a device is upgraded from Cisco IOS XE Fuji 16.9.x, Cisco IOS XE Gibraltar 16.10.x, or Cisco IOS XE Gibraltar 16.11.x to Cisco IOS XE Gibraltar 16.12.x, the type 5 secret is auto-converted to convoluted type 9 secret (password that starts with $14$).
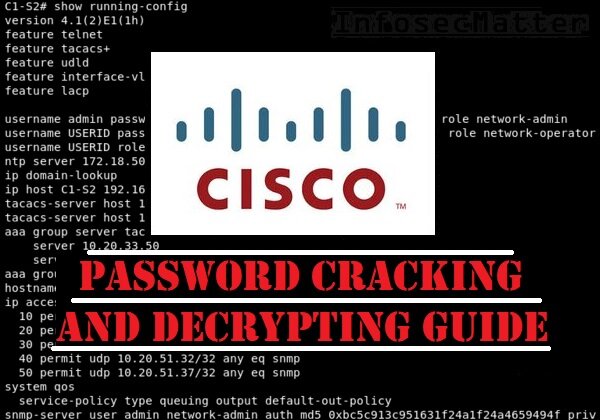
Introduction
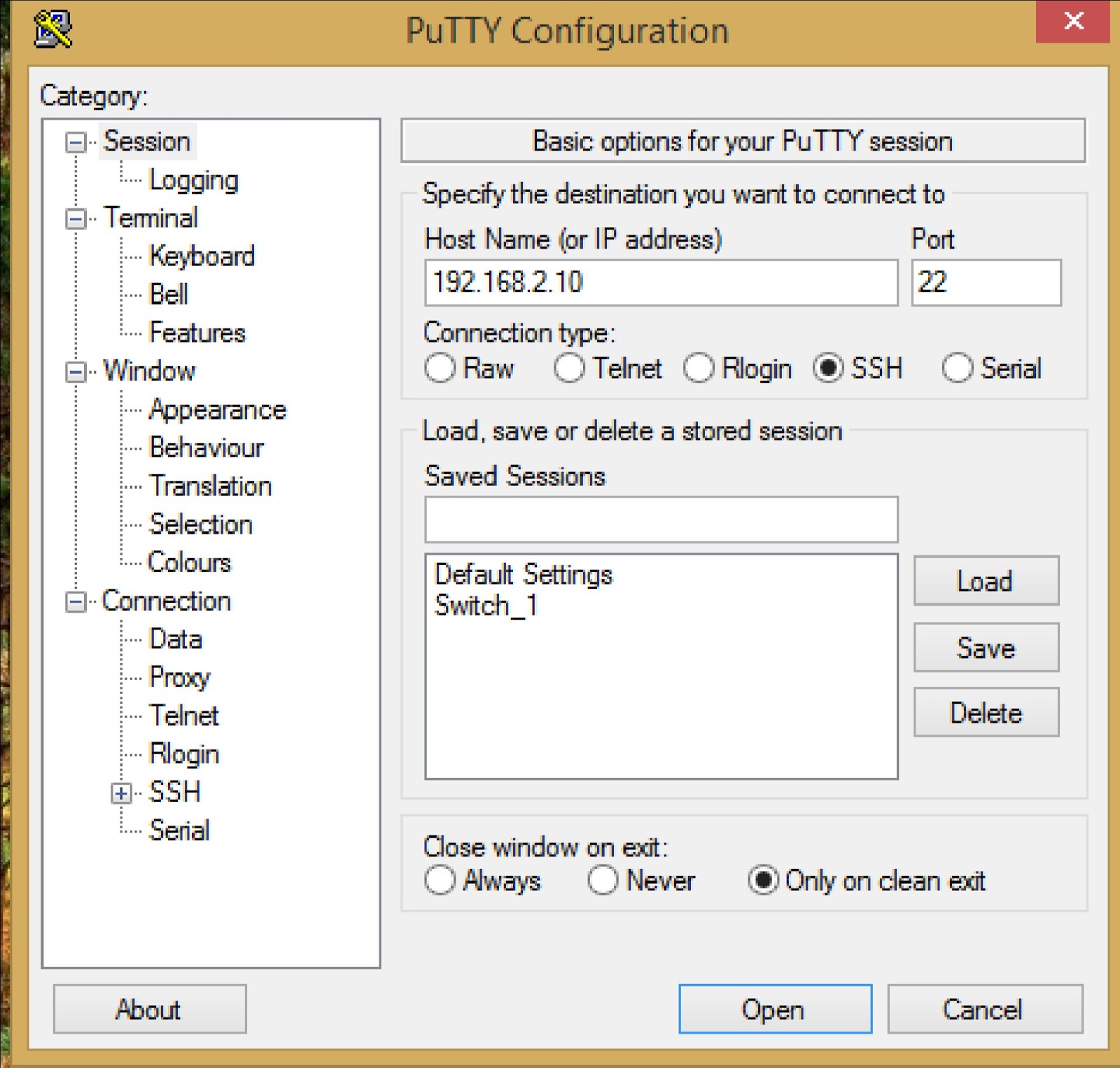
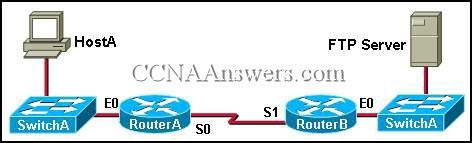
During penetration tests, it is not uncommon to come across a configuration file of a Cisco network device. It may be a configuration backup found laying somewhere on some computer in the network. It may be a console log output (e.g. from PuTTY) containing Cisco configuration snippets. Or we may just flat out break into some Cisco device configured
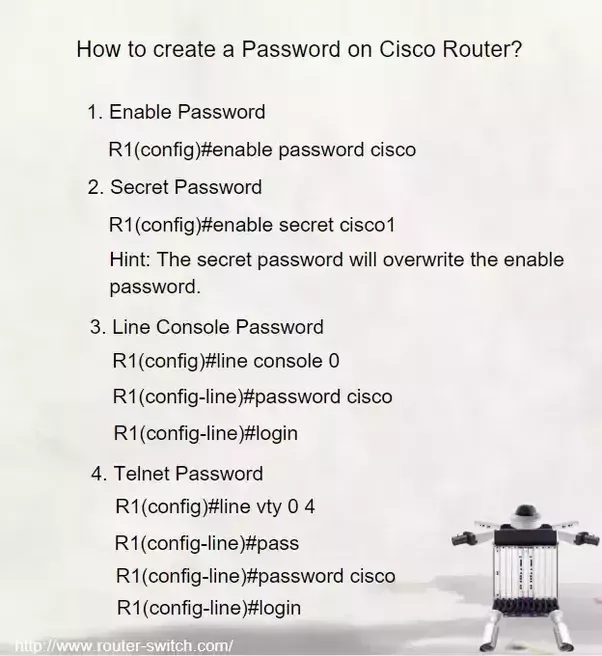
Cisco Type 0 Password
Cisco password type 0 is basically clear text password. There is no encryption nor obfuscation. It is the oldest and the most insecure method of storing passwords in Cisco devices. It should never be used. The following example shows type 0 password found in a Cisco configuration: As you can see, there is really nothing to crack or decrypt. We can
Cisco Type 7 Password
This password type uses Vigenère cipherwhich is essentially a simple alphabetical substitution encryption. The algorithm is reversible and thus it can be deciphered instantly into a plain text without any need for cracking. The following example shows type 7 password found in a Cisco configuration: infosecmatter.com
Cisco Type 4 Password
This password type was designed around 2013 and the original plan was to use PBKDF2 (Password-Based Key Derivation Function version 2) algorithm. But due to an implementation issue, it somehow ended up being a mere single iteration of SHA256 without salt. The following example shows type 4 password found in a Cisco configuration: infosecmatter.com
Cisco Type 5 Password
This password type was introduced around 1992 and it is essentially a 1,000 iteration of MD5 hash with salt. The salt is 4 characters long (32 bits). For modern computers this is not difficult enough and thus in many cases it can be successfully cracked. The following example shows type 5 password found in a Cisco configuration: infosecmatter.com
Cisco Type 8 Password
This password type is a proper implementation of the failed password type 4. This time it really uses the PBKDF2algorithm and 10 character salt (80 bits). Essentially it is 20,000 iterations of SHA256 and this makes it much harder to crack in comparison with the previous password types. The following example shows type 8 password found in a Cisco c
Cisco Type 9 Password
This password type uses Scryptalgorithm. Scrypt was specifically designed to make cracking very difficult even on large-scale cracking rigs with many GPUs or hardware ASICs. This is due to the fact that Scrypt requires large amount of memory to perform its function. The following example shows type 9 password found in a Cisco configuration: infosecmatter.com
Cracking Tips
Use KoreLogic custom rules John the Ripper contains very useful ruleset for generating passwords called KoreLogic. This ruleset originated in DEFCON 2010 contest and it is a great way of generating passwords from patterns or when traditional dictionary attack fails. To make use of it, simply create a dictionary with patterns like this e.g.: Save it into patterns.txtfile. Then simply run john like this: Chain John the Ripper with Hashcat Although there has been some efforts to convert the aforementioned KoreLogic rules into Hashcat, the result is only partial. Fortunately, we can chain together John the Ripper with Hashcat to make it use KoreLogic rules in full. Simply generate the passwords using John the Ripper on the stdout and feed them into Hashcat using pipe like this: The same method can be used for any ruleset that we have created in the john format. Hopefully you can crack some Cisco hashes with these tips. If you li
References
https://learningnetwork.cisco.com/s/article/cisco-routers-password-typeshttps://tools.cisco.com/security/center/content/CiscoSecurityAdvisory/cisco-sa-20130318-type4https://community.cisco.com/t5/networking-documents/understanding-the-differences-between-the-cisco-password-secret/ta-p/3163238 infosecmatter.com

How to Encrypt and Decrypt Cisco console password Switch/Router

Enable Password / Secret and how to encrypt passwords on Cisco devices

Cisco Password Decryption
|
Chapter 5-Replacing or Recovering Passwords
5-1. Cisco uBR10012 Universal Broadband Router Hardware Troubleshooting Guide for Cisco however and must be replaced with a new enable secret password. |
|
User Security Configuration Guide Cisco IOS Release 15MT
8 ?.?. 2546 Configuration Examples for Login Parameters on page 5 ... encryption level used by the service password-encryption command can be decrypted. |
|
Controlling Switch Access with Passwords and Privilege Levels
Username secret password type 5 and enable secret password type 5 must be and configure a master encryption key to encrypt and decrypt passwords. |
|
Controlling Switch Access with Passwords and Privilege Levels
123 at the password prompt. Security Configuration Guide Cisco IOS XE Release 3SE (Catalyst 3850 Switches). OL-30243-01. 5. |
|
Controlling Switch Access with Passwords and Privilege Levels
Username secret password type 5 and enable secret password type 5 must be and configure a master encryption key to encrypt and decrypt passwords. |
|
Controlling Switch Access with Passwords and Privilege Levels
Username secret password type 5 and enable secret password type 5 must be and configure a master encryption key to encrypt and decrypt passwords. |
|
Controlling Switch Access with Passwords and Privilege Levels
With enable secret command password is encrypted but is visible on the terminal when you 4. service password-encryption. 5. end. 6. show running-config. |
|
User Security Configuration Guide Cisco IOS XE Release 3SE
Configuring and Verifying the Enable Secret Password 21 For more information see the Privileged EXEC Mode on page 5. ... to decrypt. The MD5 algorithm ... |
|
Controlling Switch Access with Passwords and Privilege Levels
Username secret password type 5 and enable secret password type 5 must be and configure a master encryption key to encrypt and decrypt passwords. |
|
User Security Configuration Guide Cisco IOS Release 12.2SR
24 ?.?. 2547 Configuring the Enable Secret Password 29 ... Configuration Examples for Login Parameters page 5 ... much more difficult to decrypt. |
|
• enable password, page 2 • enable secret, page 5 - Cisco
Cisco IOS Security Command Reference: Commands D to L, Cisco IOS XE Release 3SE (Catalyst 3650 Switches) -E |
|
Controlling Switch Access with Passwords and Privilege - Cisco
For more information, see Protecting Enable and Enable Secret Passwords with and configure a master encryption key to encrypt and decrypt passwords |
|
System Security - Cisco
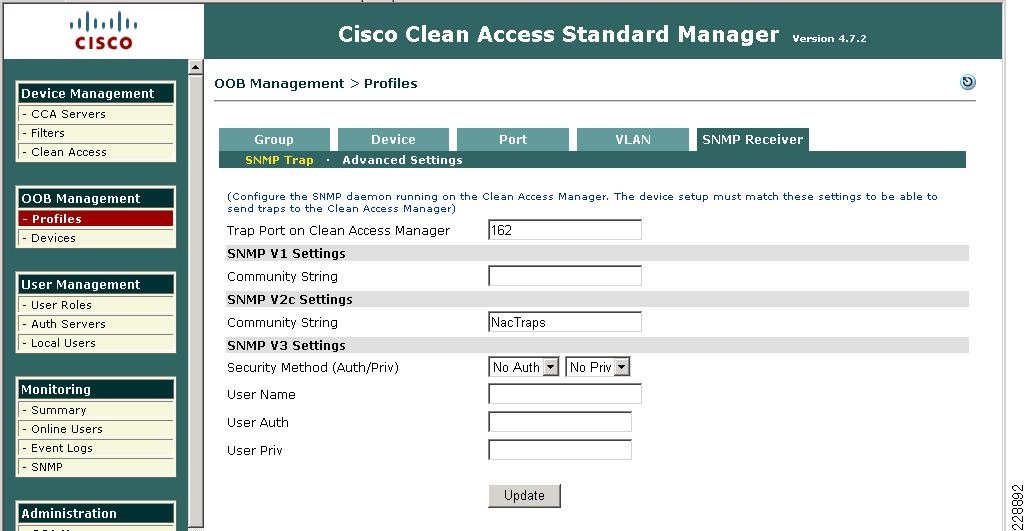
stored within the configuration will be properly decrypted cli-encrypt-algorithm command allows an operator to configure the password/secret encryption |
|
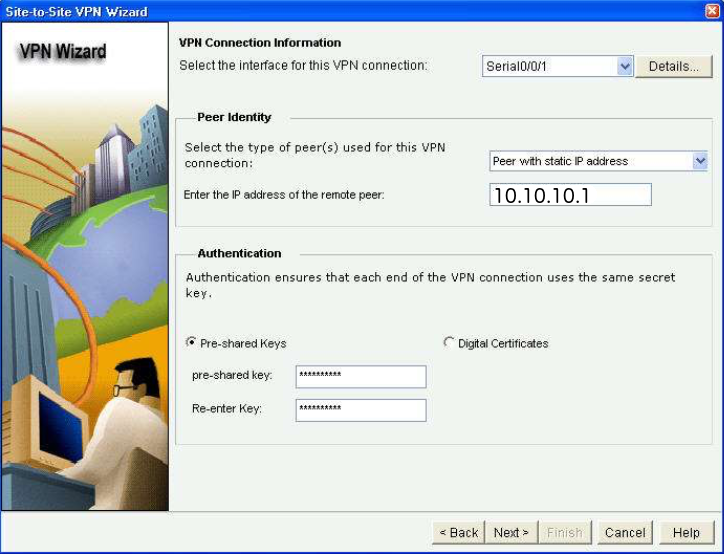
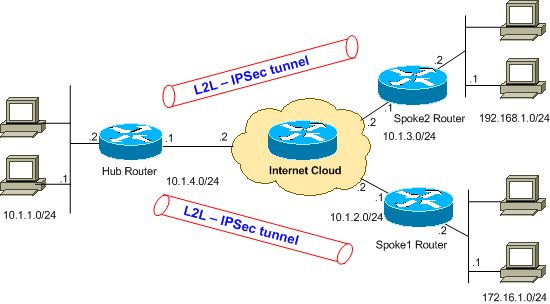
Encrypted Preshared Key - Cisco
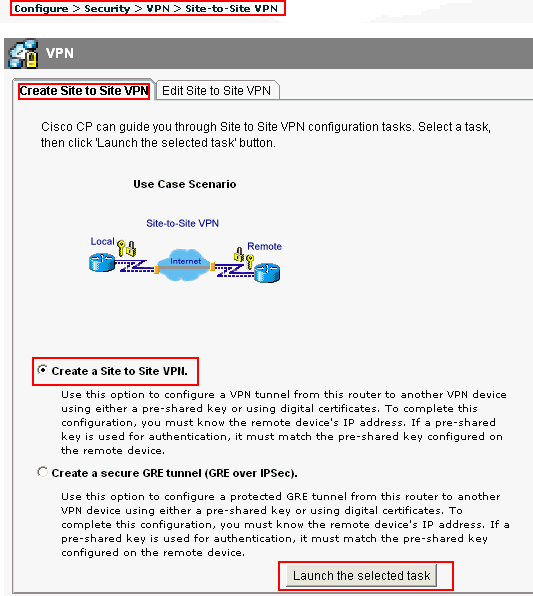
Internet Key Exchange for IPsec VPNs Configuration Guide, Cisco IOS Release passwords can be seen or retrieved, it is difficult to decrypt them to find out the |
|
User Security Configuration Guide, Cisco IOS XE Fuji 169x
Configuring and Verifying the Enable Secret Password 31 Configuring a to decrypt The MD5 algorithm does not send the password to the remote device |
|
Security Configuration Guide, Cisco IOS XE Gibraltar 1611x
29 mar 2019 · Protecting Enable and Enable Secret Passwords with Encryption 6 and configure a master encryption key to encrypt and decrypt passwords |
|
Security Configuration Guide, Cisco IOS XE Gibraltar 1612x
31 juil 2019 · Protecting Enable and Enable Secret Passwords with Encryption 8 The switch attempts to decrypt the TGT by using the password that the |
|
User Security Configuration Guide, Cisco IOS XE Release 3E
Configuring and Verifying the Enable Secret Password 21 service password- encryption command to encrypt passwords creates text strings that be decrypted |
|
Configuring Security with Passwords, Privileges, and Logins - Cisco
page 7 The system administrator uses the enable secret or enable passwordglobal command to encrypt passwords creates text strings that can be decrypted |
|
User Security Configuration Guide, Cisco IOS XE Release 3SE
Configuring and Verifying the Enable Secret Password 22 service password- encryption command to encrypt passwords creates text strings that be decrypted |