cisco ise how to
|
Overview of Cisco ISE
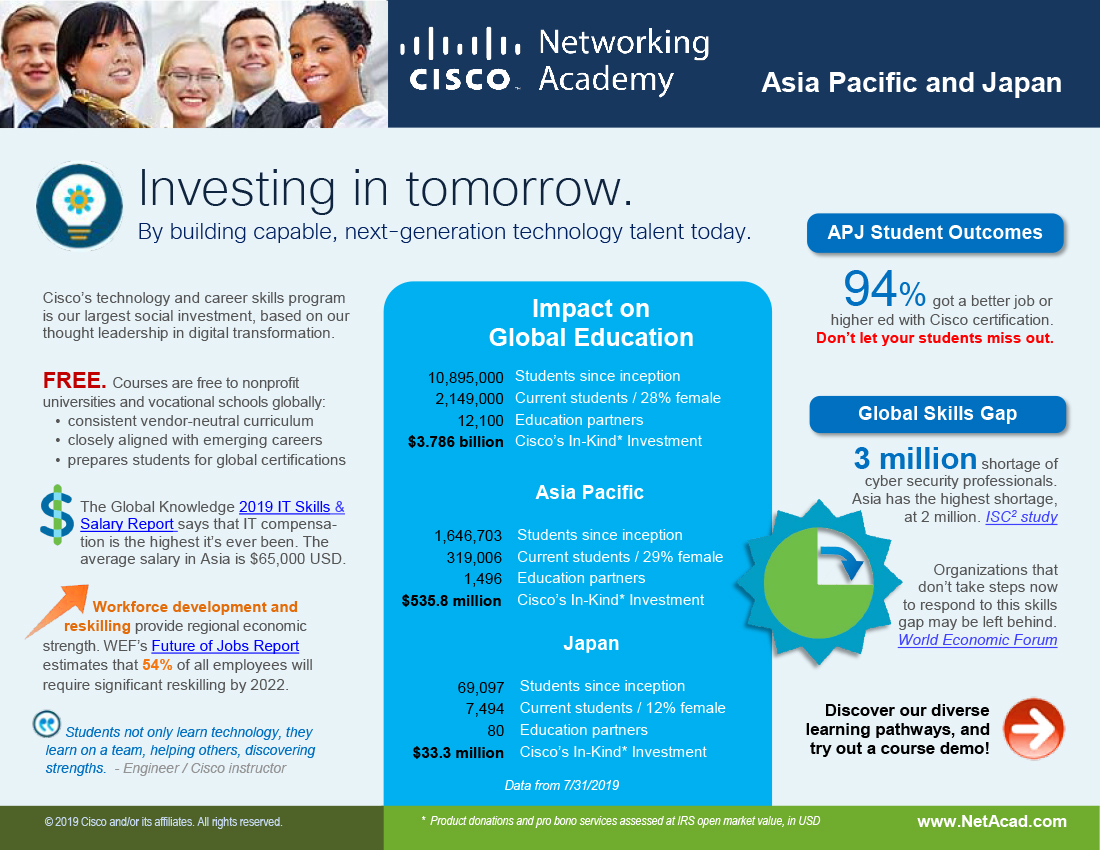
Provide Identity-Based Network Access The Cisco ISE solution provides context-aware identity management in the following areas: Cisco ISE determines whether users are accessing the network on an authorized policy-compliant device Cisco ISE establishes user identity location and access history which can be used for compliance and reporting |
What is the Cisco Identity Services Engine Cross-Site Request Forgery Vulnerability?
A vulnerability in the web-based management interface of Cisco Identity Services Engine (ISE) could allow an unauthenticated, remote attacker to conduct a cross-site request forgery (CSRF) attack and perform arbitrary actions on an affected device.
What are the benefits of using Cisco ISE?
Cisco ISE has improved the policy engine which handles the access layer infrastructure. ISE can authenticate everything in the wired, wireless network and VPN access points. So, it provides assurance that all the devices on the network should be there.
How can the Cisco Identity Services Engine be used?
Cisco Identity Service Engine (ISE) is a network access control and policy enforcement platform. Network devices are the main avenues for wired network, Wireless and VPN connection to allow the users and the endpoint to connect to the network to access various services.
What is the vulnerability in the Cisco Identity Services Engine?
A vulnerability in the web-based management interface of Cisco Identity Services Engine (ISE) could allow an authenticated, remote attacker to bypass authorization and access system files. This vulnerability is due to improper access control in the web-based management interface of an affected device.

Cisco ISE Installation Guide

Cisco ISE Guest Access Basics Part I

Building ISE RADIUS Policy Sets
|
Cisco ISE Ports Reference
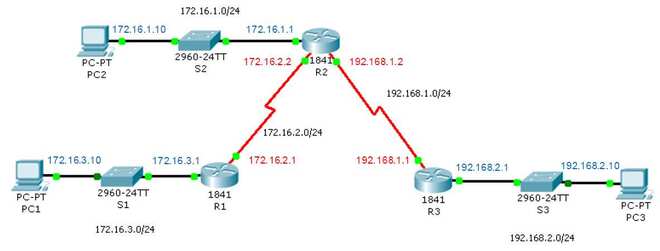
Cisco ISE management is restricted to Gigabit Ethernet 0. • RADIUS listens on all network interface cards (NICs). • Cisco ISE server interfaces do not support |
|
Cisco Identity Services Engine Upgrade Guide Release 3.1
However you can carry out backup and restore of configuration data. When you restore the data in a Cisco ISE AWS instance |
|
ISE Configuration Guide v7.3.2
Verify the ISE Configuration. 13. Edit or Delete a Saved Cisco ISE cluster. 14. Configure ISE Integration Failover. 15. Adjusting Stealthwatch Configuration |
|
Managing Identities and Admin Access
Each role in Cisco ISE defines a set of access policies permissions |
|
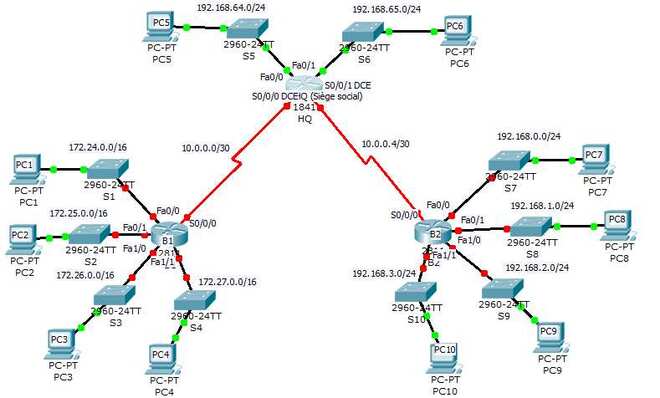
Configuration de Catalyst 9800 WLC iPSK avec Cisco ISE
Cet article traite de la configuration d'un WLAN sécurisé iPSK sur un contrôleur LAN sans fil Cisco 9800 avec Cisco ISE comme serveur RADIUS. |
|
Configure Repository on ISE
ISE Repositories can be configured from both the GUI and the CLI of the ISE and can be used for these purposes: Backup and Restore of ISE Configuration and |
|
Managing Cisco ISE Backup and Restore Operations Overview of
This chapter describes the Cisco Identity Services Engine (ISE) database backup and restore operations which include Cisco ISE application configuration |
|
ISE: Mécanismes de récupération de mot de passe - Cisco
Mettez la machine virtuelle Cisco ISE hors tension. Étape 3. Cliquez avec le bouton droit sur ISE VM dans la liste et sélectionnez Edit Settings. (modifier les |
|
ISE Configuration Guide v7.0
0 to Cisco ISE pxGrid. Technical Details. To connect Stealthwatch and Cisco ISE it's required that certificates are deployed correctly for trusted |
|
Configure ISE 3.0 REST ID with Azure Active Directory
All of the devices used in this document started with a cleared (default) configuration. If your network is live ensure that you understand the potential |
|
Cisco ISE (Identity Services Engine)
Une approche différente est nécessaire pour la gestion et la sécurité de l' entreprise mobile en constante évolution Elle repose sur la solution Cisco® ISE (Identity |
|
Overview of Cisco ISE
Cisco Identity Services Engine (ISE) is a next-generation identity and access control policy platform that enables enterprises to enforce compliance, enhance |
|
Cisco ISE Features
Cisco ISE assigns services based on the assigned user role, group, and associated policy (job role, location, device type, and so on) Cisco ISE grants authenticated users with access to specific segments of the network, or specific applications and services, or both, based on authentication results |
|
7-Mettre en oeuvre et configurer la solution Cisco Identity Services
Cette formation concerne Cisco Identity Services Engine (ISE) version 1 1 1, une plate forme de contrôle d'accès et d'identité qui fournit un plan de stratégie |
|
ISE - Cisco Live
What is Identity Services Engine (ISE)? Network Resources Access Policy Traditional Cisco TrustSec® BYOD Access Threat Containment |
|
Session Presentation - Cisco Live
Cisco ISE supports device administration using the TACACS+ security protocol to control and audit the configuration of network devices Context Exchange |
|
ENET-WP037A-FR-P, Déploiement de services didentité dans une
Ethernet) utilise le moteur Identity Services Engine (ISE) de Cisco pour prendre en charge l'accès sécurisé Le moteur Cisco ISE est utilisé en conjonction avec |
|
Configure & Troubleshoot Cisco Identity Services Engine
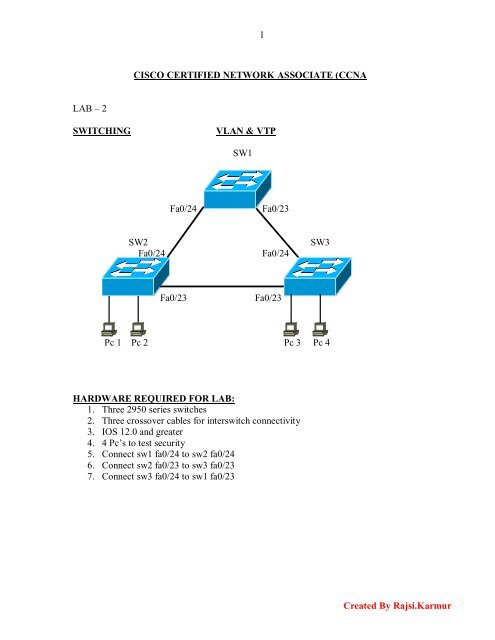
ISE as a part of Cisco TrustSec ▫ ISE Architecture: nodes, functions, personas ▫ Deployment options ▫ Scaling Cisco ISE, resources estimation |
|
Cisco ISE
Cisco ISE simplifies the delivery of consistent, highly secure access control across wired, wireless, and VPN connections Learn more |
![PDF] Configuration Routeur Cisco cours et formation gratuit PDF] Configuration Routeur Cisco cours et formation gratuit](https://img.yumpu.com/37659748/1/500x640/cisco-ios-commands-pdf-format.jpg)
![Cisco CCNA par François-Emmanuel Goffinet [PDF/iPad/Kindle] Cisco CCNA par François-Emmanuel Goffinet [PDF/iPad/Kindle]](https://brandingstyleguides.com/wp-content/guidelines/2017/12/cisco-brand-book-1000x647.jpg)





![PDF~] The Complete Cisco VPN Configuration Guide PDF~] The Complete Cisco VPN Configuration Guide](https://www.micvce.com/wp-content/uploads/2018/07/300-135.png)
![2018 PDF Free Download] 2018 New Cisco Business Value Specialist 2018 PDF Free Download] 2018 New Cisco Business Value Specialist](https://images-eu.ssl-images-amazon.com/images/I/418+KmudjhL._AC_US400_.jpg)
![PDF] Configuration Routeur Cisco cours et formation gratuit PDF] Configuration Routeur Cisco cours et formation gratuit](https://www.computer-pdf.com/documents/covers/0608-interconnecting-cisco-networking-devices-part-1.pdf.png)
![PDF] Interconnecting Cisco Networking Devices (ccna) Part 1 free PDF] Interconnecting Cisco Networking Devices (ccna) Part 1 free](https://www.networkstraining.com/wp-content/uploads/2015/12/Cisco-Switch-Commands-Cheat-Sheet.jpg)






![PDF~] 101 Labs for the Cisco CCNA Exam PDF~] 101 Labs for the Cisco CCNA Exam](https://docplayer.net/docs-images/46/21300653/images/page_7.jpg)



![CCNA Study Material Videos Ebooks and Tutorials: [Cisco] CCNA CCNA Study Material Videos Ebooks and Tutorials: [Cisco] CCNA](https://img.over-blog-kiwi.com/3/38/81/23/20190628/ob_8ab7e9_certswarrior-new-two.PNG)

![PDF~] Cisco ASA Configuration (Networking Professional's Library) PDF~] Cisco ASA Configuration (Networking Professional's Library)](https://0.academia-photos.com/attachment_thumbnails/58590105/mini_magick20190309-29730-ldrctf.png?1552191318)
![Latest Cisco DTCSM 820-605 Dumps PDF [2020] – Pass With 100 Latest Cisco DTCSM 820-605 Dumps PDF [2020] – Pass With 100](https://image4.slideserve.com/7999311/cisco-n.jpg)