3 tier application architecture security
|
SECURING THREE-TIER SYSTEMS WITH ORACLE8I
A typical security requirement in a three-tier system is that each user be limited to running specific applications on the middle tier depending on the user's |
Qu'est-ce qui caractérise une architecture N-tiers ?
L'architecture N-tier (anglais tier : étage, niveau), ou encore appelée multi-tier, est une architecture client-serveur dans laquelle une application est exécutée par plusieurs composants logiciels distincts.
L'architecture à trois niveaux permet : Une plus grande flexibilité/souplesse ; Une sécurité accrue car la sécurité peut être définie indépendamment pour chaque service, et à chaque niveau ; De meilleures performances, étant donné le partage des tâches entre les différents serveurs.
|
SECURING THREE-TIER SYSTEMS WITH ORACLE8I
This would eliminate much of the value of a three-tier architecture. Oracle's secure application roles enable security in thin client or web-based ... |
|
VIAVI Solutions
The StrataSync application architecture uses a three-tier model with firewalls between each tier to ensure that only traffic associated with specific ports and |
|
Securing Enterprise Web Applications at the Source: An Application
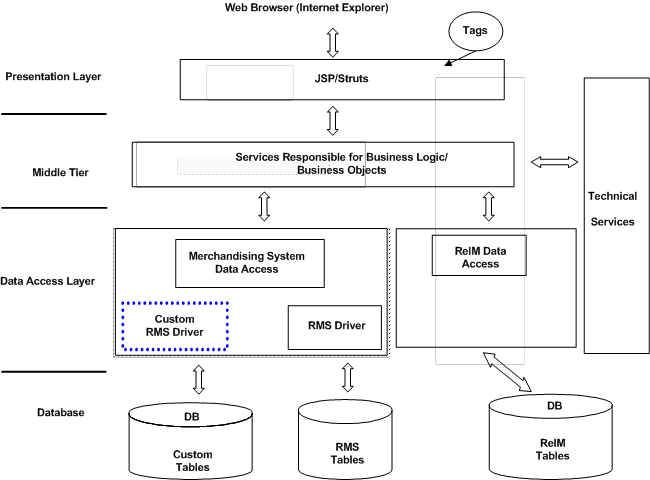
Figure 3: JPetStore 4.0 Application Architecture……………………………………………..30. Figure into the architecture at the middle-tier application server integration with ... |
|
Check Point IPS Engine Architecture: - New Technologies Provide a
The Open. Performance Architecture of the Security Gateway R70 will help your organiza- tion protect its network from evolving application-layer threats |
|
A Technical Overview
three-tier application architecture with an interface layer business logic layer and ... security policy which is the foundation by which all Skillsoft security. |
|
Architecture Guidelines – Application Security
David Deighton IT Architect. 1 / 5. Executive Summary. These guidelines describe best practice for application security for 2 or 3 tier web-based applications. |
|
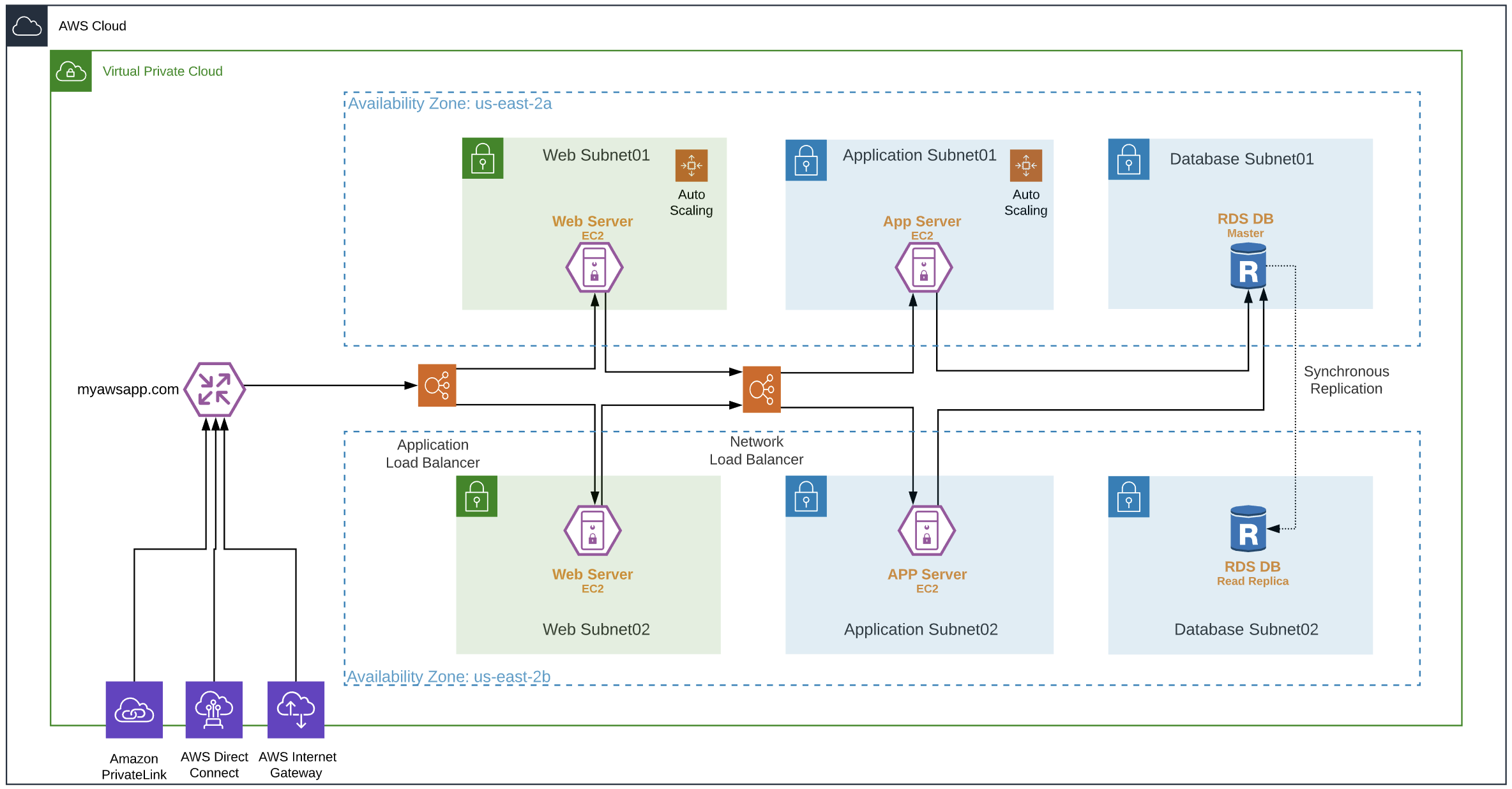
CIS Amazon Web Services Three-tier Web Architecture Benchmark
9 нояб. 2016 г. Check if your application DB instances are configured to use the Data Tier Security. Group: aws rds describe-db-instances --filters. Name=tag ... |
|
Department of Defense Zero Trust Reference Architecture
4 июл. 2022 г. In a scenario where a user makes a request to a three-tier web application traffic would flow to ... N/A. The ability to secure and manage the ... |
|
Application Security Verification Standard 4.0 - Final
V1.3 Session Management Architectural Requirements 1.5.3 Verify that input validation is enforced on a trusted service layer. (C5). ✓ ✓ 602. 1.5.4 Verify ... |
|
AWS Prescriptive Guidance - AWS Security Reference Architecture
4 нояб. 2023 г. ... 3 and. 4) and the application layer (layer 7). Shield Standard is automatically included at no extra cost beyond what you already pay for AWS ... |
|
Design and Implementation of Secure 3-Tier Web Application with
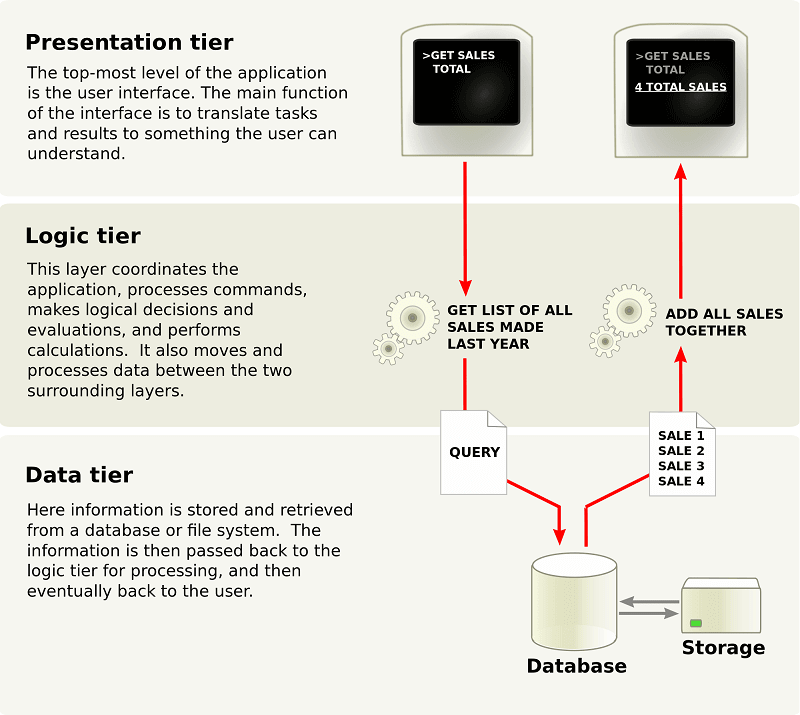
3-tier architecture[4] is a client-server architecture in which the user interface (presentation tier) business logic (middle tier) and data storage or access |
|
Design and Implementation of Secure 3-Tier Web Application with
3-tier architecture[4] is a client-server architecture in which the user interface (presentation tier) business logic (middle tier) and data storage or access |
|
SECURING THREE-TIER SYSTEMS WITH ORACLE8I
In a typical three-tier architecture the middle tier is responsible for authenticating users' A secure application context enables access conditions. |
|
Web Application Hosting in the AWS Cloud - AWS Whitepaper
20 août 2021 hosting architecture that implements a common three-tier web application model ... The application server security group on the other hand |
|
Oracle Database 12c Real Application Security
Over the past 20 years the traditional client server model has given way to the 3-tier model as the prevalent architecture. During this transition security |
|
Securing Enterprise Web Applications at the Source: An Application
the enterprise security architecture where both local risk (Rings 4-5) and enterprise Figure 1: Securing a 3-tiered Enterprise Web Application: At the ... |
|
Oracle Cloud Infrastructure Security Architecture (PDF)
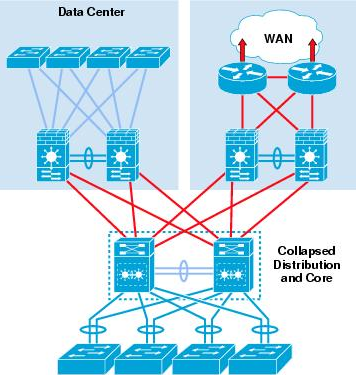
Data centers align with Uptime Institute and Telecommunications Industry Association (TIA) ANSI/TIA-942-A Tier 3 or Tier 4 standards and follow an N2 redundancy |
|
NIST SP 800-39 Managing Information Security Risk: Organization
out at Tier 3. For example the information security architecture portion of the enterprise architecture developed at Tier 2 influences and guides the |
|
CIS Amazon Web Services Three-tier Web Architecture Benchmark
9 nov. 2016 While this Benchmark explicitly covers 3-tier architectures featuring Internet Application and Database tiers (with a Content Distribution ... |
|
SECURITY ISSUES AND COUNTERMEASURES OF THREE TIER
3. IOT Architecture. This section presents the architecture of IoT of three-tiered architectures- application tier network tier and perception tier. |
|
SECURING THREE-TIER SYSTEMS WITH ORACLE8I - CGISecurity
Moreover, application logic in the middle tier can Although security is one of the reasons for moving to a three-tier architecture for enterprise access, there are |
|
Cours - Architecture N-tier - Cedric-Cnam
Exemple d'architecture 3-tier : Tier de présentation : interfaces utilisateurs sur un PC poste de travail, qui s'adressent à des applications serveur Tier des règles |
|
SECURITY ISSUES AND COUNTERMEASURES OF THREE TIER
The IoT provides a three-tier architecture - perception, network and application tiers In perception layer, IoTis deployed with different types of sensors- RFID, |
|
WEB APP ARCHITECTURES:
The 3-Tier Architecture for Web Apps how do we build a web application? how will our web application cope with large numbers of requests? □ Security |
|
Research and Application of the Four-tier Architecture Jiexian Cao
architecture is its security The three-tier architecture hierarchically manages data and programs, data control and application logic independently, that can more |
|
Multi-Level Security of Website: A Review of Use Multitier System
model was present based on three-tier architecture (Client tier, Server tier and The Middle or application server tier consists most of the application logic |
|
Understanding Application Architecture: An Overview
two-tier, three-tier, and n-tier applications and describes how they fit into a modem enterprise The developer does not have to worry about security, concurrent |
|
Security for GIS N-tier Architecture
Current Web Map Servers are a simplification of full functional application server at the mid- dle of the 3-tier industry-standard architecture 2 The second |
|
Building Multi-Tier Scenarios for WebSphere Enterprise Applications
Records 70 - 79 · 2 1 1 Architectural elements for static Web content acceleration 2 3 3 Security 6 1 3 Deploying the application into multiple tiers |
|
91 Two-tier Architecture Typical client/server systems have fallen
systems as the business logic and services such as security, persistence, All the applications should be developed using 3-tier or N-tier architecture in order to |