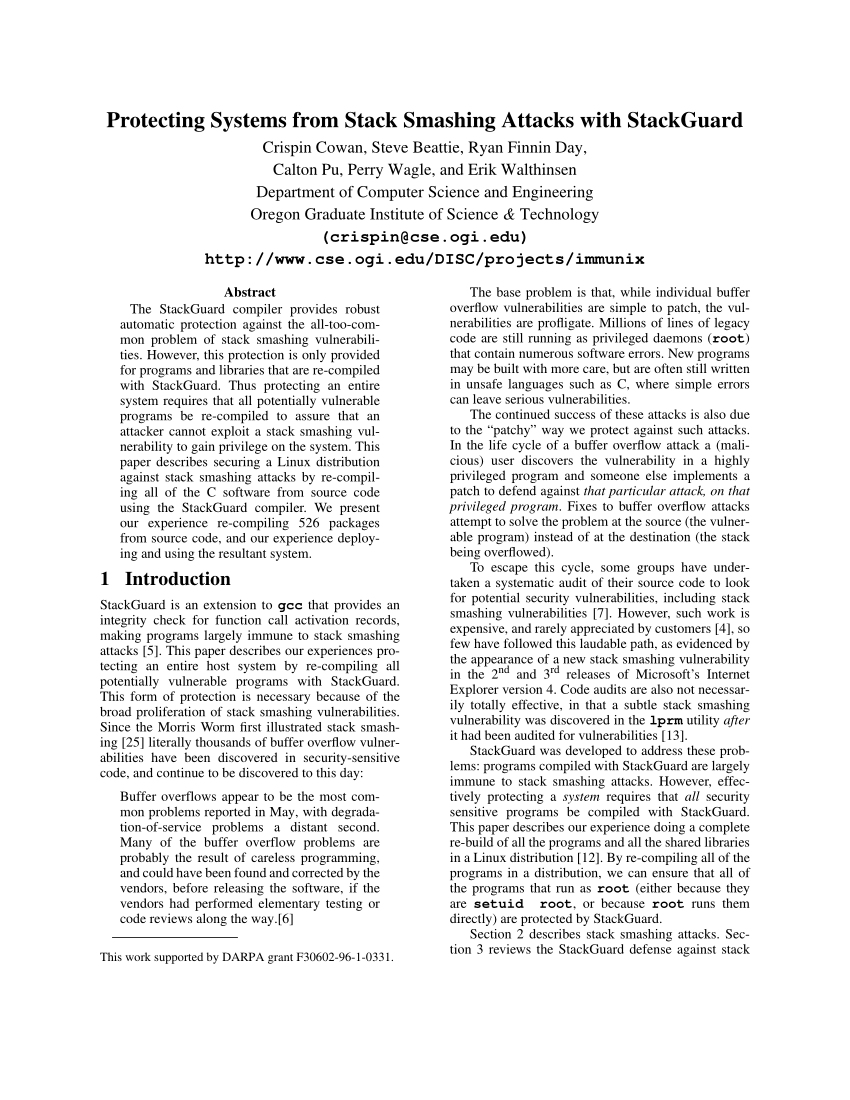
c program stack smashing detected
How to solve stack smashing detected in C?
To correct the problem, verify that all of your buffers are large enough to contain their intended data.
Instead of using unsafe methods like gets(), use secure ones like fgets().
To avoid buffer overflows, validate user input.
Stack protection can be enabled with compiler settings such as -fstack-protector.26 déc. 2023What causes stack smashing in C++?
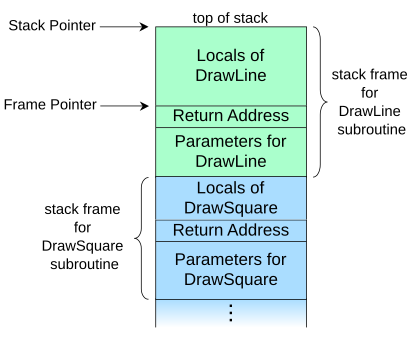
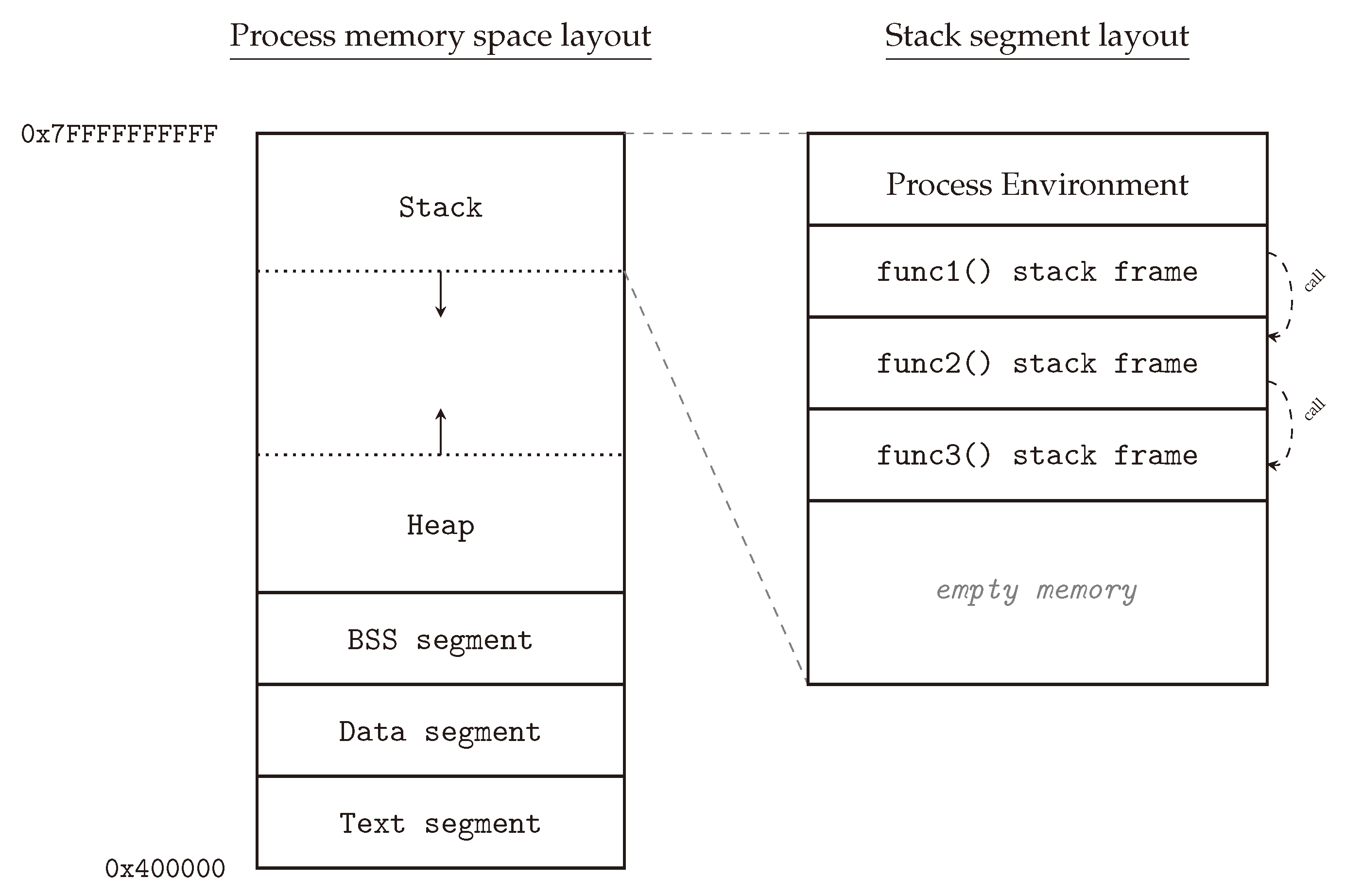
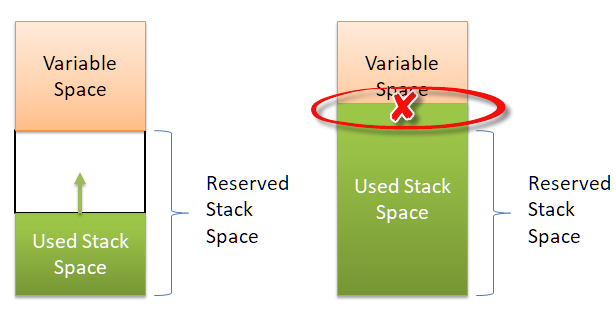
Stack smashing in C++ is a form of buffer overflow.
It happens when a program writes more data to the stack than its available memory allocation, causing adjacent memory locations to be overwritten.What does it mean by stack smashing detected?
This error is a defensive mechanism used to prevent stack-based buffer overflows.
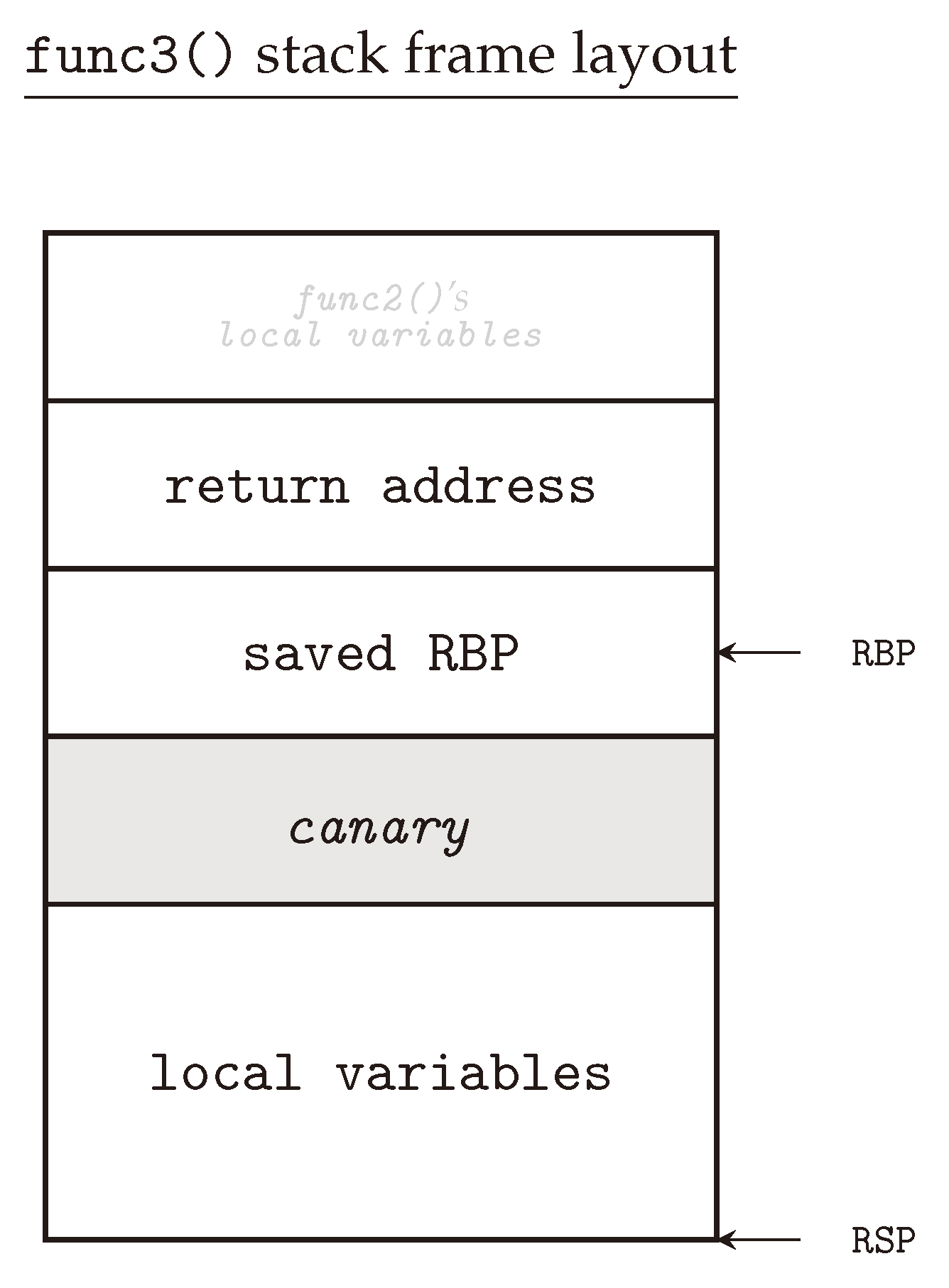
The compiler uses a random sequence of bits called canary to check for buffer overflow and based on that, produces the stack smash detected error in C.
This is a runtime error and leads to the termination of the running program.We can disable it by using the -fno-stack-protector option of gcc.
There are other options of gcc for stack protection.
For example, the -fstack-protector-strong option is like the -fstack-protector option, but it also protects against buffer overflows in functions having local array definitions.
|
[Notification] Dynamic Checking for Corruption in Stack Area for
16 déc. 2018 edition; Detection of Stack Smashing. This feature enables you to check for any corruption in the stack area while running the program. |
|
Smashing The Stack For Fun And Profit Aleph One Introduction
`smash the stack` [C programming] n. On many C implementations it is possible to corrupt the execution stack by writing past the end of an array declared |
|
[Notification] Dynamic Checking for Corruption in Stack Area for
16 déc. 2018 edition; Detection of Stack Smashing. This feature enables you to check for any corruption in the stack area while running the program. |
|
Secure Programming Lecture 5: Memory Corruption III
1 oct. 2019 Question. What should happen if an overflow is detected? GCC's Stack Smashing Protector. Consider this C program: #include <stdio.h>. |
|
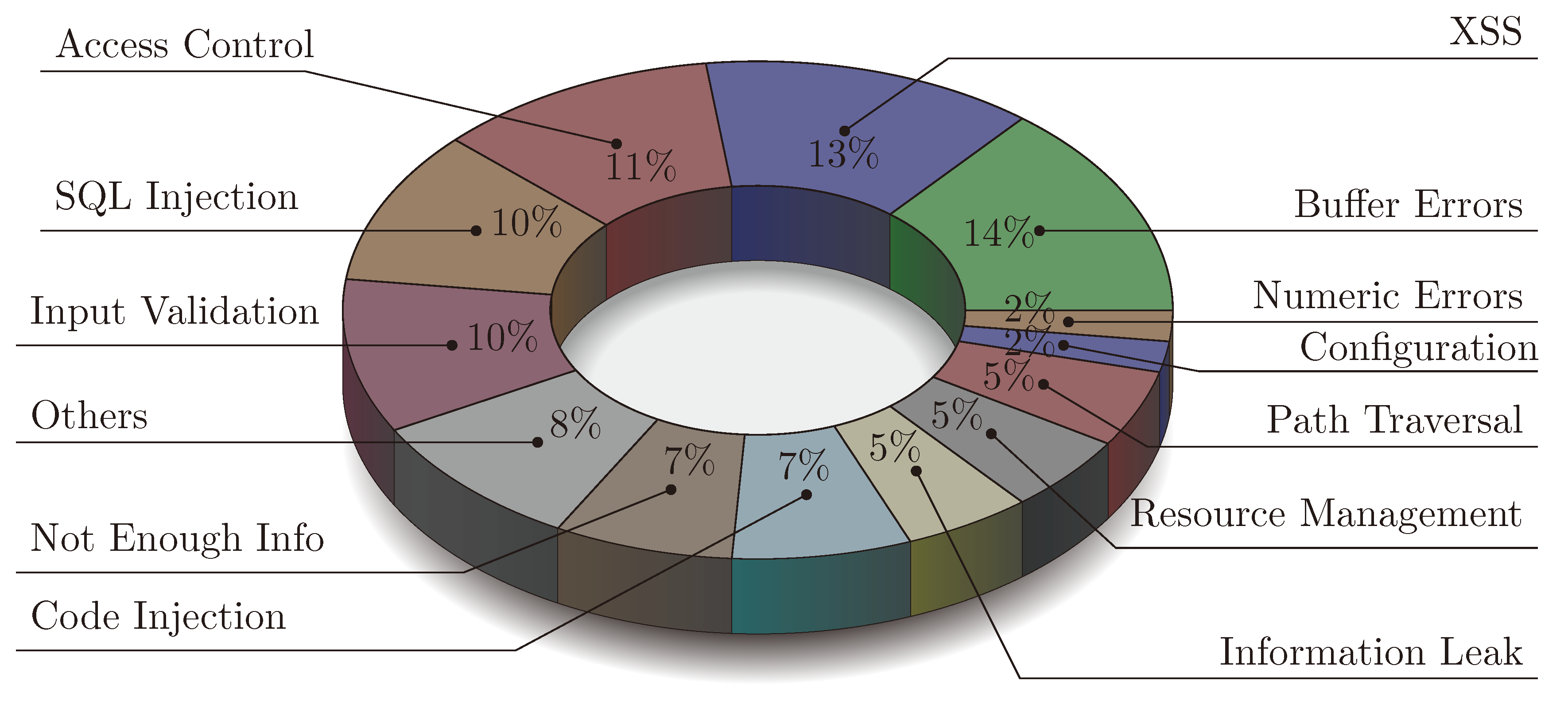
The Security Risk of Lacking Compiler Protection in WebAssembly
4469 C programs with known buffer overflow vulnerabilities to x86 code and to WebAssembly |
|
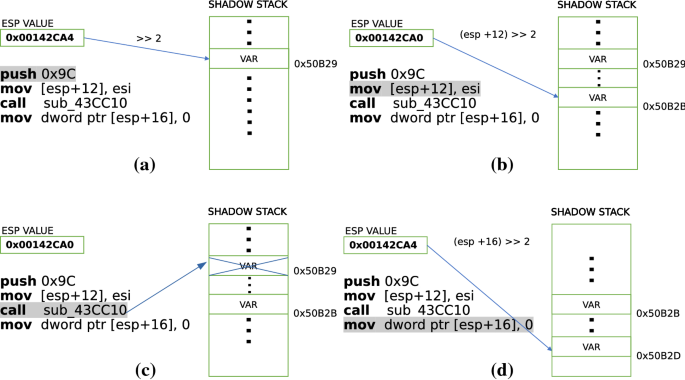
Four different tricks to bypass StackShield and StackGuard protection
StackGuard StackShield |
|
Lecture: Buffer Overflow
char *str ="This is definitely longer than 12"; strcpy(buffer str); return 1;. } 9. Simple Buffer Overflow. Example2.c. *** stack smashing detected *** |
|
T R A N S P A R E N T R U N -T I M E D E F E N S E A G A I N S T S
For this reason heap smashing attacks are far less prevalent. A complete C program to demonstrate the stack smashing attack is shown in Figure 2. |
|
Smashing The Stack For Fun And Profit Introduction
8 nov. 1996 `smash the stack` [C programming] n. ... both discovered and exploited. ... fixed by the program and includes code (instructions) and ... |
|
Smashing the Stack Protector for Fun and Profit
corruption of a specific value on the program's stack. P. Wagle C. Cowan |
|
Four different tricks to bypass StackShield and StackGuard protection
StackGuard, StackShield, and Microsoft's new stack smashing protection Lets see how the compiler translates the following C program, with no pro- And the only way we found to exploit Solaris 2 5 1 named IQUERY buffer overflow in |
|
Security Analysis Outline Introduction Stack Smashing To Avoid
C programs are more susceptible to buffer overflow C allows direct pointer manipulation – since space and Using canary for stack smashing detection? |
|
Buffer overflow vulnerabilities - Departamento de Ciência de
This is a general definition for buffer overflow, that makes no distinction for: language and “relatives” (C++ and Objective-C) buffer until '\0' is found 13 |
|
Transparent Run-Time Defense Against Stack Smashing Attacks
exploit buffer overflow bugs have accounted for ap- A complete C program to demonstrate the stack forming detection and handling of buffer overflow |
|
JUL 2 0 2004 - CORE
2 juil 2020 · Securing Software: An Evaluation of Static Source Code Analyzers by This thesis evaluated five static analysis tools - Polyspace C Verifier illustrated actual buffer overflow vulnerabilities found in various versions of |
|
Lecture: Buffer Overflow
char buffer[12]; char *str ="This is definitely longer than 12"; strcpy(buffer, str); return 1; } 9 Simple Buffer Overflow Example2 c *** stack smashing detected *** |




















![PDF] Stack smashing attack detection methodology for secure PDF] Stack smashing attack detection methodology for secure](https://i1.rgstatic.net/publication/326564308_To_Detect_Stack_Buffer_Overflow_with_Polymorphic_Canaries/links/5dd48462458515cd48ac0074/largepreview.png)


![PDF] ebook Value-Range Analysis of C Programs : Towards Proving PDF] ebook Value-Range Analysis of C Programs : Towards Proving](https://upload.wikimedia.org/wikipedia/commons/thumb/f/f9/Nopsled.svg/200px-Nopsled.svg.png)





![Linux Kernel Exploitation 0x1] Smashing Stack Overflows in the Kernel Linux Kernel Exploitation 0x1] Smashing Stack Overflows in the Kernel](https://images.contentstack.io/v3/assets/blt36c2e63521272fdc/blt47cc0e8dbee9ceab/601c8d545f9b2812764c1ffc/StackCanaries_Fig4.png)