cloudflare nginx exploit
Does Cloudflare have a 'HTTP/2 rapid reset' vulnerability?
This post is also available in 简体中文, 繁體中文, 日本語, 한국어, Deutsch, Français and Español. Earlier today, Cloudflare, along with Google and Amazon AWS, disclosed the existence of a novel zero-day vulnerability dubbed the “HTTP/2 Rapid Reset” attack.
Does Cloudflare have a DDoS attack?
This attack exploits a weakness in the HTTP/2 protocol to generate enormous, hyper-volumetric Distributed Denial of Service (DDoS) attacks. Cloudflare has mitigated a barrage of these attacks in recent months, including an attack three times larger than any previous attack we’ve observed, which exceeded 201 million requests per second (rps).
What is Cloudflare remote browser isolation?
Remote browser isolation: Cloudflare's remote browser isolation solution conducts a user's browsing activity on a supervised cloud environment via sandboxing. Since browsing activity is isolated from users' end devices, those devices are protected from vulnerabilities like zero-day threats.
What is Cloudflare's new zero-day vulnerability?
In late August 2023, our team at Cloudflare noticed a new zero-day vulnerability, developed by an unknown threat actor, that exploits the standard HTTP/2 protocol — a fundamental protocol that is critical to how the Internet and all websites work.
How to Mitigate Cve-2021-44228
Implement one of the following mitigation techniques: Java 8 (or later) users should upgrade to release 2.16.0. Java 7 users should upgrade to release 2.12.2. Otherwise, in any release other than 2.16.0, you may remove the JndiLookup class from the classpath: zip -q -d log4j-core-*.jar org/apache/logging/log4j/core/lookup/JndiLookup.class blog.cloudflare.com
Vulnerability History
In 2013, in version 2.0-beta9, the Log4j package added the “JNDILookup plugin” in issue LOG4J2-313. To understand how that change creates a problem, it’s necessary to understand a little about JNDI: Java Naming and Directory Interface. JNDI has been present in Java since the late 1990s. It is a directory service that allows a Java program to find d
Cloudflare Firewall Protection
Cloudflare rolled out protection for our customers using our Firewall in the form of rules that block the jndi Lookup in common locations in an HTTP request. This is detailed here. We have continued to refine these rules as attackers have modified their exploits and will continue to do so. blog.cloudflare.com

Super Simple Cloudflare and Nginx Proxy Manager Setup Using YOUR Domain

Cloudflare CDN: How to Setup + Purchase Domain + NGINX Proxy Manager on Unraid (2021)

Self Hosting on your Home Server
|
Bypassing Cloudflares reverse proxy: a case study Contornando o
Procedure of vulnerability assessment of the website () remaining authorized while ... https://developers.cloudflare.com/ssl/origin-configuration/ssl-modes. |
|
HTTP/2 Rapid Reset DDoS Vulnerability
10 окт. 2023 г. On October 10 2023 |
|
An Analysis of TLS Handshake Proxying (full version)
[6] CloudFlare Inc. “CloudFlare Keyless SSL |
|
Cyber Threat Index 2023
11 мар. 2022 г. The most popular choices among developers center around jQuery Microsoft IIS |
| Mitigating HTTP Denial-of-Service Attacks on Self-Hosted Web |
|
Can You Tell Me the Time? Security Implications of the Server
This vulnerability is known as a timing side-channel leak. Two and a half decades ago timing attacks which exploit such timing leaks were documented by Kocher |
|
Virtual Host Confusion: Weaknesses and Exploits
This problem applies to all popular web servers such as Apache. Nginx or IIS |
|
Cloudflare
This kind of attack is particularly dangerous as attackers used zero- day exploits (i.e. a vulnerability for which there is no known patch) to remotely |
|
Master Deck 2023 Investor Day
4 мая 2023 г. F5/NGINX Akamai |
|
Déjà vu: Abusing Browser Cache Headers to Identify and Track
16 дек. 2020 г. Nginx. Cloudflare |
|
H2DoS: An Application-Layer DoS Attack Towards HTTP/2 Protocol
H2DoS attack that exploits multiplexing and flow-control mechanisms cloudflare-nginx and nginx are top two that used as implementation softwares. |
|
WHITE PAPER - WEB CACHE DECEPTION ATTACK Omer Gil
An unauthenticated attacker can easily exploit this vulnerability 7. Understanding our cache and the web cache deception attack – Cloudflare blog. |
|
Web Application Firewall (WAF) Evasion Techniques #3
2 sept. 2018 have looked at how to bypass a WAF rule set exploiting a Remote Com- ... with CloudFlare WAF and with the ModSecurity OWASP Core Rule Set. |
|
How To Exploit PHP Remotely To Bypass Filters & WAF Rules
24 déc. 2018 bypass WAF rule set in order to exploit a remote command execution. ... hind the CloudFlare WAF (as always I'm using CloudFlare be-. |
|
Revisiting QUIC attacks: A comprehensive review on QUIC security
1 juil. 2022 instance HTTP/3 is designed to exploit QUIC's fea- ... 9https://github.com/cloudflare/quiche/tree/master/nginx. |
|
Host of Troubles: Multiple Host Ambiguities in HTTP Implementations
Five attacks exploiting Host header ambiguity Nginx. First. Azure. Reject. Huawei. First. Tomcat. First. CloudFlare. First. Kaspersky. |
|
Host of Troubles: Multiple Host Ambiguities in HTTP Implementations
Reverse Proxy. Apache IIS |
|
Revisiting QUIC attacks: A comprehensive review on QUIC security
1 juil. 2022 instance HTTP/3 is designed to exploit QUIC's fea- ... 9https://github.com/cloudflare/quiche/tree/master/nginx. |
|
Déjà vu: Abusing Browser Cache Headers to Identify and Track
tacks are timing attacks that exploit the simple fact that it takes longer to retrieve a Nginx. Cloudflare |
|
The Matter of Heartbleed
tem and (4) exposing real attacks that attempted to exploit the bug. in popular server products including Apache and Nginx. While. |
|
Web Cache Deception Attack - Black Hat
An unauthenticated attacker can easily exploit this vulnerability, as shown in the When a file arrives to Cloudflare servers from a web server, it goes through two shows a configuration that instructs NGINX to cache specific types of static |
|
Web Cache Entanglement: Novel Pathways to - PortSwigger
I notified both and Fastly have now patched, but Cloudflare declined One of my favorite things to do with web cache poisoning is to exploit cache vendor's websites, so let's One form of normalization that nginx applies to the cache key is |
|
Practical Web Cache Poisoning: Redefining - PortSwigger
into obediently patching issues that nobody could actually exploit Network ( CDN) like Cloudflare, with caches scattered across geographical locations Also This system was using NGINX for caching, which was naturally happy to save my |
|
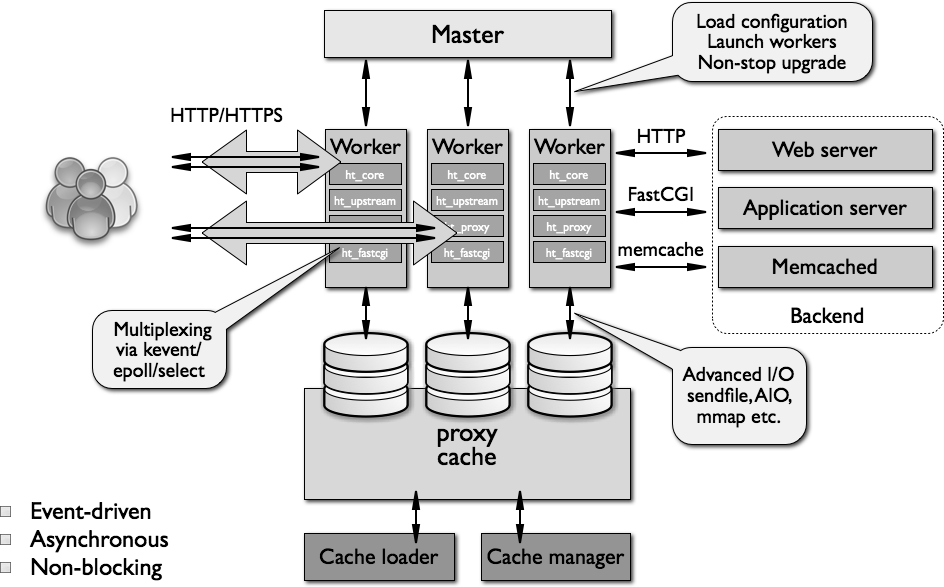
Security Risks in Asynchronous Web Servers - Department of
write vulnerability in Nginx for the proof of concept exploits nerability in Cloudflare's CDN service, due to a memory error in Figure 2: NGINX exploit diagram |
|
Virtual Host Confusion: Weaknesses and Exploits
This problem applies to all popular web servers such as Apache, Nginx or IIS, but also to SSL terminators, CDN frontend servers and other reverse proxy software |
|
Your Cache Has Fallen: Cache-Poisoned Denial-of - CPDoS
cal relevance by identifying one proxy cache product and five CDN services that are host of troubles and response splitting attacks exploit this gap be- tween a cache and an (Apache HTTPD) v2 4 18, Nginx v1 10 3, Varnish v6 0 1, Apache |
|
HDoS: An Application-Layer DoS Attack Towards HTTP/2 Protocol
HTTP DoS HTTP DoS attacks normally exploit seemingly legitimate cloudflare- nginx and nginx are top two that used as implementation softwares of HTTP/2 |
|
CDN Backfired: Amplification Attacks Based on HTTP Range Requests
exploiting the implementation flaws on multi-range requests and by connecting the Cloudflare and Akamai to launch an OBR attack and selecting a 1KB file as the target caused by Nginx's incorrect processing with the Range field |
|
Slides - Jianjun Chen
Five attacks exploiting Host header ambiguity • Large scale Nginx First Azure Reject Huawei First Tomcat First CloudFlare First Kaspersky First ATS |