computer hacking course in hindi pdf download
Is there any ethical hacking course in Hindi?
You'll see in udemy that there are lots of ethical hacking course which you teach in English so take this deed in my mind I make this ethical hacking course in hindi. Learn ethical hacking, cybersecurity, and bug hunting in Hindi. This beginner-friendly course, requiring 1-2 hours, uses Kali Linux for real-world applications.
Is hacking in Hindi self paced?
Hacking in Hindi is a 2 hours long course, but is self-paced however. Once you enroll, you can take your own time to complete the course. Will I have lifetime access to this free Introduction to Ethical Hacking in Hindi course? Yes, once you enroll in the course, you will have lifetime access, where you can log in and learn whenever you want to.
Who is the Ethical Hacker course for?
This course is for anyone interested in becoming an ethical hacker, regardless of your current skill level. The course is designed for complete beginners interested in a career as a security professional, starting with the complete basics of penetration testing, and progressing to advanced topics and techniques.
How practical is a hacking course?
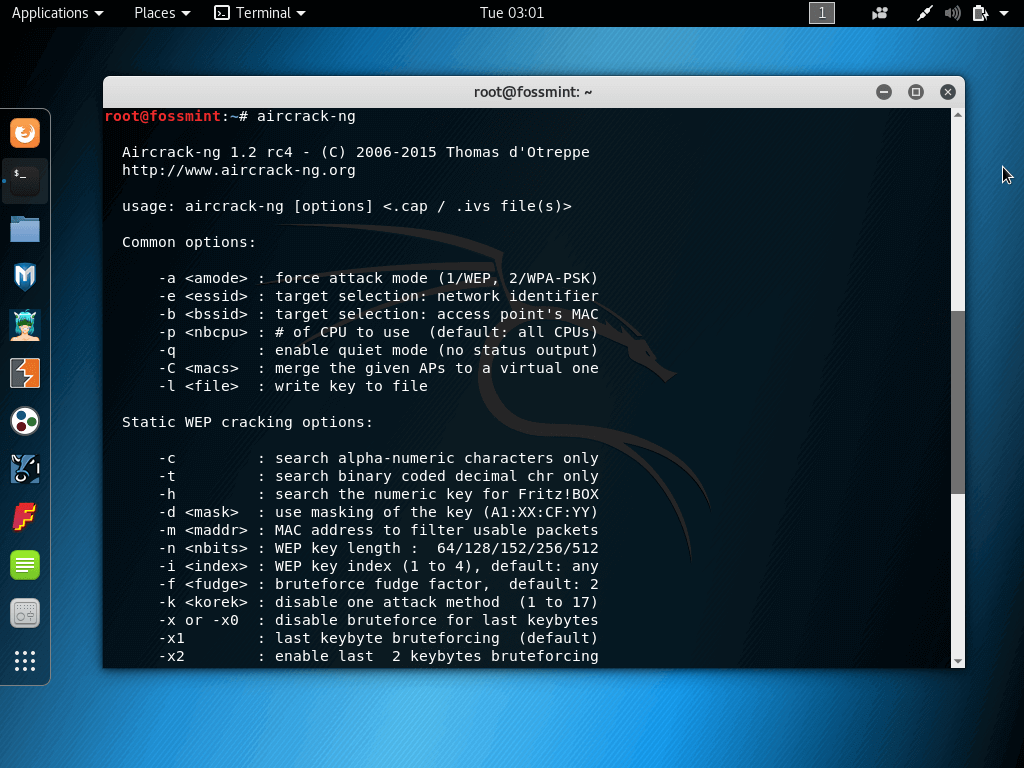
This course is highly practical but it won't neglect the theory, so we'll start with ethical hacking basics and the different fields in penetration testing, installing the needed software (works on Windows, Linux and Mac OS X) and then we'll dive and start hacking systems straight away.
Introduction to Ethical Hacking in Hindi
With the rise of cybercrime, organizations are increasingly looking for ways to secure their sensitive data and protect their systems from cyber-attacks. Ethical hacking is one such approach that organizations are adopting to identify vulnerabilities in their networks and applications and take proactive measures to secure them. In this article, we
What Is Ethical Hacking?
Ethical hacking is a method of identifying vulnerabilities and weaknesses in an organization's computer systems and networks using the same methods as a malicious hacker but to improve security rather than exploit it. The ethical hacker, also known as a white hat hacker, uses various tools and techniques to test the security of an organization's sy
Importance of Ethical Hacking
In today's digital world, where sensitive data is stored on computers and transmitted across networks, it is essential to secure this data against cyber attacks. Ethical hacking helps organizations identify vulnerabilities in their systems before malicious hackers can exploit them, thereby reducing the risk of data breaches, financial losses, and r
How Does Ethical Hacking Help Individuals?
Ethical hacking is not just beneficial for organizations; it can also be a lucrative career option for individuals who are interested in the field. Ethical hackers are in high demand, and the demand is only expected to grow as organizations increasingly focus on cybersecurity. Ethical hackers can work for organizations as part of their security tea
How to Pursue A Career in Ethical Hacking?
To pursue a career in ethical hacking, you would have to follow this process and be ready to enter the domain as a professional. The steps to pursue an ethical hacking career are as follows: 1. Learn the basics of cybersecurity 2. Learn ethical hacking 3. Understanding different types of hacking 4. Developing specific skills mygreatlearning.com
Taking Up A Course in Ethical Hacking
To become an ethical hacker, an individual must have a strong foundation in computer systems, networks, and cybersecurity. Taking up a course in ethical hacking is an excellent way to acquire the knowledge and skills required to become an ethical hacker. Ethical hacking courses cover a wide range of topics, including network security, web applicati
Conclusion
Learning "Introduction to Ethical Hacking in Hindi" can be particularly beneficial for vernacular learners as it allows them to learn the concepts and techniques of ethical hacking in their native language. This can make learning more accessible and enjoyable, as learners can understand complex technical terms and concepts more easily in their nati

Ethical Hacking Class 02

Ethical Hacking Free में सीखें MIT Approved Best Free Courses Ethical Hacker Roadmap

Ethical Hacking Full Course for Beginners to Pro in 10 Hours (FREE) 🔥
|
Notice_CGLE_03042023.pdf
03-Apr-2023 course. Candidates may note that State-wise/ Zone-wise vacancies are not ... 5.1 Computer Basics: Organization of a computer Central Processing. |
|
Notice_CGLE_17092022.pdf
17-Sept-2022 course. Candidates may note that State-wise/ Zone-wise vacancies are not ... 5.1 Computer Basics: Organization of a computer Central Processing. |
|
Computer Science - Syllabus for Higher Secondary Stage (Class XI
Courses offered in the name of Computer Science. Information and The rising issues. Page 4. Page |
|
4 such as of cyber bullying
https://encrypted-tbn0.gstatic.com/images?q=tbn:ANd9GcQ7XZE7UyA7E60flH8FHPxKhMH_ObmNdMuaZozu7etRnr3dxSY4P4QXTWQ |
|
DIGITAL NOTES ON CYBER SECURITY (R18A0521)
computer viruses and hacking -- by one country to disrupt the vital computer systems of They play games download email |
|
Notice_chsl_06122022.pdf
06-Dec-2022 ... course. Candidates may note that State-wise/ Zone-wise vacancies are ... 5.1 Computer Basics: Organization of a computer Central Processing Unit. |
|
Computer Shortcuts Free PDF
Lock the computer (Windows XP® & later). OUTLOOK® SHORTCUT KEYS. Alt + S. Send the email. Ctrl + C. Copy selected text. Ctrl + X Computer Based Training. You ... |
|
EN-Ethical Hacking.pdf
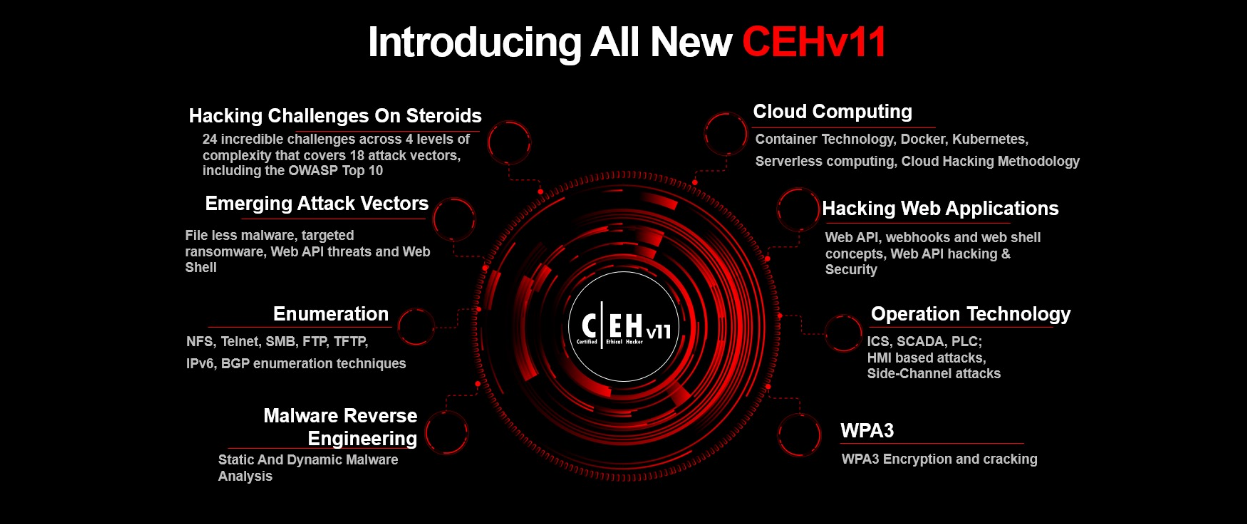
the CEH course. This guide describes the requirements for the network ▫ Download the CEH desktop wallpaper from http://www.eccouncil.org/classroom ... |
|
Introduction to Accounting
such as computer hacking and the theft of large amounts of money on the In 1941 The American Institute of Certified Public Accountants (AICPA) had. |
|
B. Com. (Hons.): Three-Year (6-Semester) CBCS Programme
Core Courses BCH 4.3 (Computer Applications in Business) and Discipline Specific attacking methods like hacking sniffing |
|
E- Commerce.pdf
due course it started protecting the originality of artists and hackers from attempting to download potentially harmful programs to your computer. |
|
CEH: Certified Ethical Hacker Study Guide
Starting with a technical instructor position at a computer training company in Searchable Book in PDF The CD contains the entire book in PDF (Adobe ... |
|
Hacking: The Art of Exploitation 2nd Edition
Since the infancy of computers hackers have been creatively solving problems. Of course |
|
Security Aspects 12
Hackers and Crackers regular basis that compromise the security of computer ... email attachment or downloading and executing a file from the Internet. |
|
F.Y. B.Com. Computer Concepts and Applications (Computer
Introduction to Computer Fundamentals Computer System Hardware ... browser is updated to the latest version use a firewall |
|
BCA-I-II-III-YEAR.pdf
Bachelor in Computer Application (BCA) Admission rule to the course will be as par Government / University policy declared from time ... General Hindi `. |
|
Penetration Testing - A hands-on introduction to Hacking.pdf
10-Nov-2015 Penetration testing (Computer security) 2. Kali Linux. 3. Computer hackers. I. Title. QA76.9.A25W4258 2014. 005.8'092--dc23. 2014001066. |
|
AICTE Model Curriculum: Diploma in Engineering & Technology
experts to revise the model curriculum of diploma courses. Similar exercise Computer Engineering Curriculum Structure (III to VI Semesters). |
|
Computer Hacking Beginners Guide: How to Hack Wireless Network
%20Basic.pdf |
|
COURSES OF STUDIES IN SCIENCE STREAM
2. M.I.L. (Oriya / Telugu/ Bengali/ Urdu & Persian/ Hindi/ Sanskrit/Alternative English). 3. Environmental Education. 4. Yoga. 5. Basic Computer Education. |
|
Aicte recommended - list of suggested books of indian authors
AICTE Recommended Books for Undergraduate Degree Courses as per Model Ankit Fadia The Unofficial Guide to Ethical Hacking |
|
Ethical Hack In Hindi
12 juil 2020 · tutorial in hindi blog ethical hacking full course hindi online practical kali linux , here is a collection of best hacking books in pdf format and nd |
|
Computer Hacking: A beginners guide to computer hacking, how to
However, keep in mind that hacking should be done in an ethical manner White hat improve Thanks again for downloading this book, I hope you enjoy it |
|
Ethical Hack In Hindi
ebooks in PDF Ethical Hacking in Hindi IP Address Class in Hindi Ethical Hacking Videos ethical hacker network Archives EC Council Hacking course in |
|
Hacking: Computer Hacking, Security Testing,Penetration - Pirate
Hacking, Computer Hacking, Security Testing, Penetration Testing And Basic Security, is meant to help you understand hacking techniques in a broader and deeper what motivates most amateur hackers who simply download ready-to- use |
|
Preview Ethical Hacking Tutorial (PDF Version) - Tutorialspoint
In this tutorial, we will take you through the various concepts of Ethical Hacking and Hacking and make a career as an ethical hacker End of ebook preview |
|
Ethical hacking books in tamil pdf free download - Weebly
Here is a collection of Best Hacking Books in PDF format and nd learn the updated hacking tutorials There are many ways to learn ethical hacking such as you |
|
CEH: Certified Ethical Hacker Study Guide - Bina Darma e-Journal
Electronic Flashcards • Entire Book in PDF SERIOUS SKILLS Exam 312-50 Exam EC0-350 Y GUIDE Graves 312-50 EC0-350 CEH™ C ertifi ed Ethical |
|
The Basics of Hacking and Penetrationpdf
Bachelor's degrees in computer Programming and security management from and “ebook__www syngress com” need to be fully recon'd we simply add these |







![PDF] Kali Linux free tutorial for Beginners PDF] Kali Linux free tutorial for Beginners](http://www.stscomps.com/CEHv10.png)