adfs load balancing persistence
|
Load Balancing Microsoft AD FS
Aug 7 2019 · Using the WebUI navigate to: Cluster Configuration > Layer 7 – Real Servers and click Add a new Real Server next to the newly created Virtual Service Enter an appropriate name (Label) for the first AD FS server e g ADFS1 Change the Real Server IP Address field to the required IP address e g 192 168 2 110 |
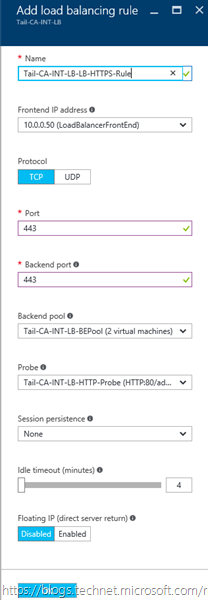
Which load balancer should I use for session persistence?
Option 1: Base the session persistence on a session cookie set by the load balancer. This option is recommended because it allows the load to be spread more evenly among the back-end servers. It requires a layer 7 load balancer with this capability and that can handle the HTTP traffic and terminate the TLS connection.
How do I access a load balanced AD FS server?
Create a suitable DNS entry for the load balanced Proxy Servers, i.e. for the VIP on the load balancer. For additional guidance on diagnosing and resolving any issues you may have, please also refer to Diagnostics & Troubleshooting. The load balanced AD FS servers should now be accessible using the DNS entry for the VIP.
Can I use source IP persistence for AD FS?
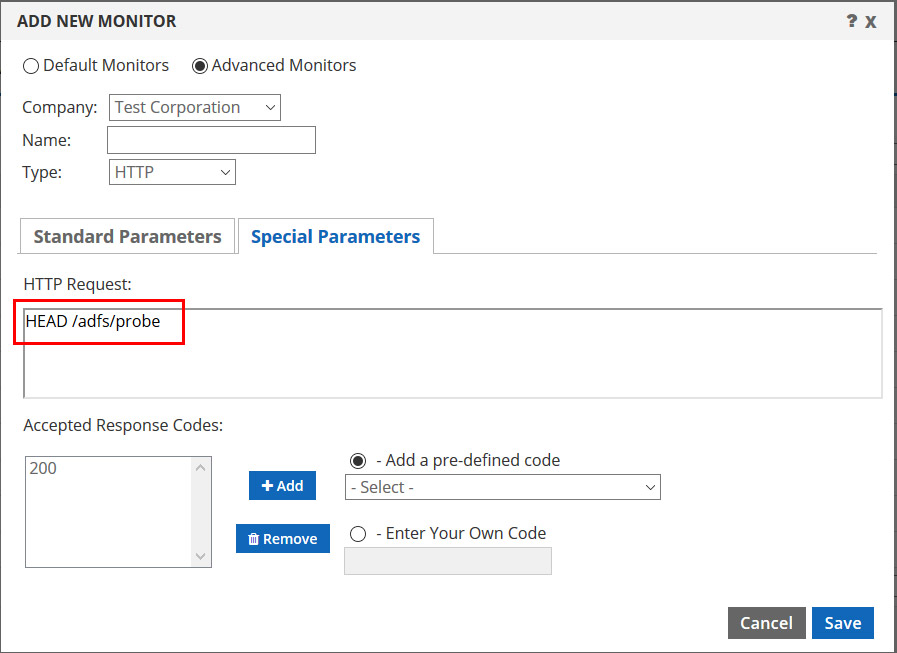
As mentioned here, Microsoft do not recommend using source IP persistence (affinity) For AD FS. However, under certain complex scenarios persistence may be required for the Federation Server VIP. Source IP, clicking Update and reloading/restarting HAProxy. 5.4. Server Health checking
What are the requirements for deploying Active Directory Federation Services (AD FS)?
The following are the requirements for deploying Active Directory Federation Services (AD FS): Each AD FS and Web Application Proxy server has a TLS/SSL certificate to service HTTPS requests to the federation service. The Web Application Proxy can have extra certificates to service requests to published applications.
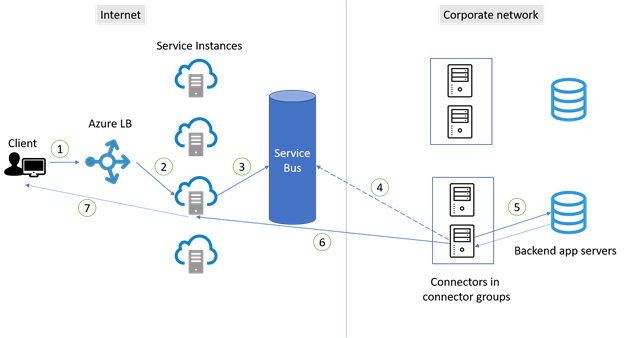
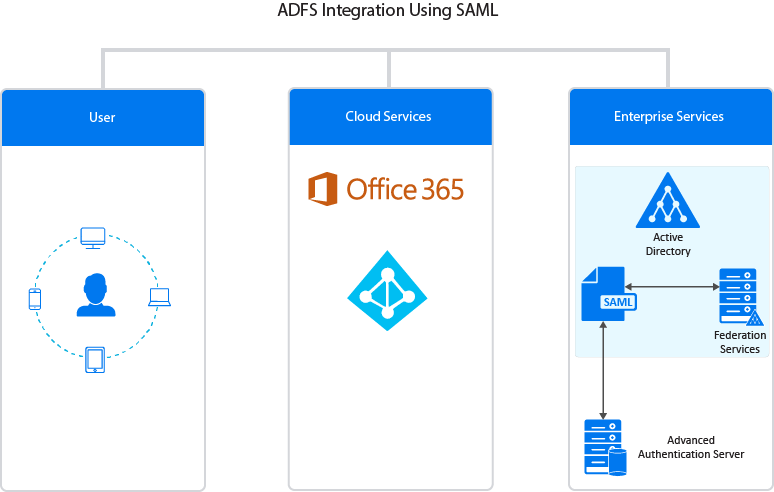
Overview
This document provides best practices for the secure planning and deployment of Active Directory Federation Services (AD FS) and Web Application Proxy (WAP). It contains recommendations for additional security configurations, specific use cases, and security requirements. This document applies to AD FS and WAP in Windows Server 2012 R2, 2016, and 2019. These recommendations can be used for either an on-premises network or in a cloud hosted environment such as Microsoft Azure. learn.microsoft.com
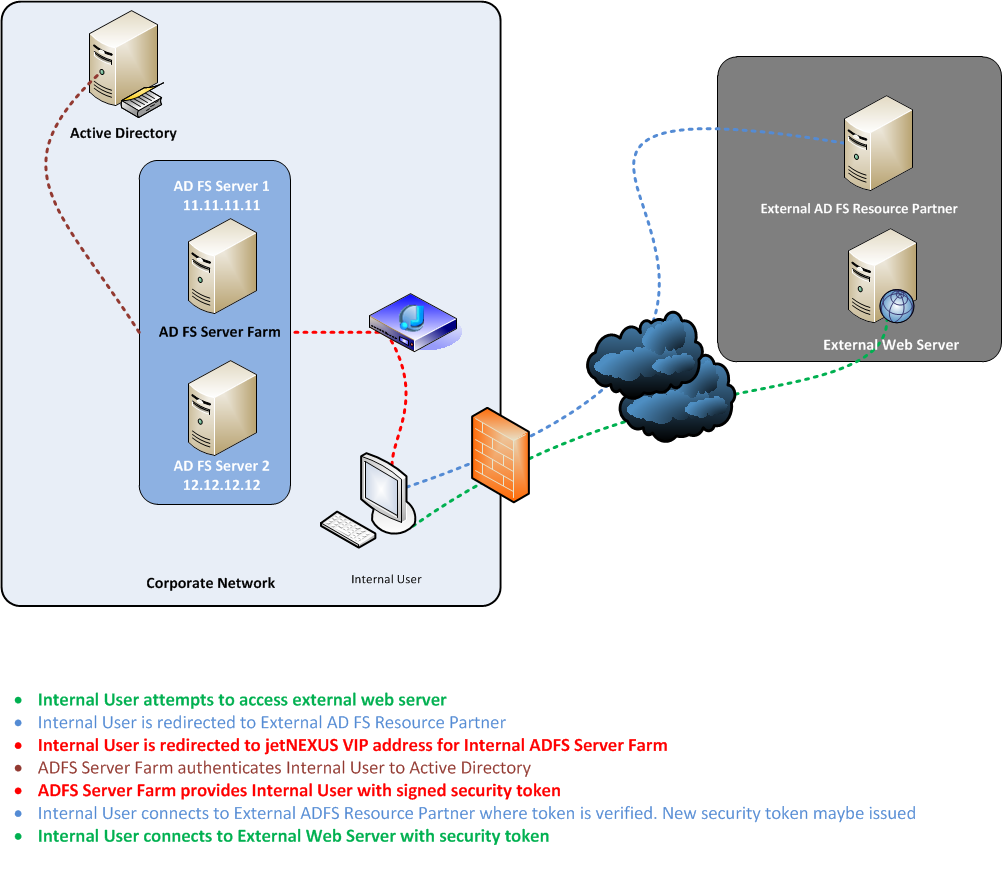
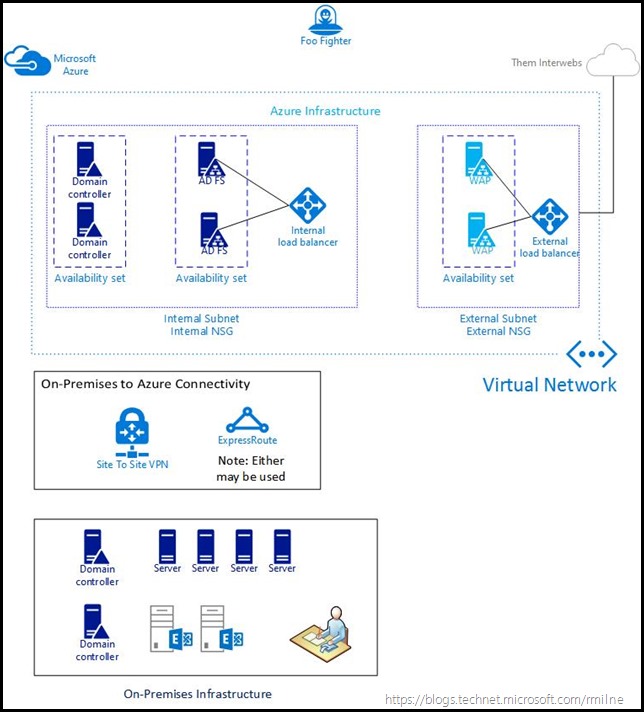
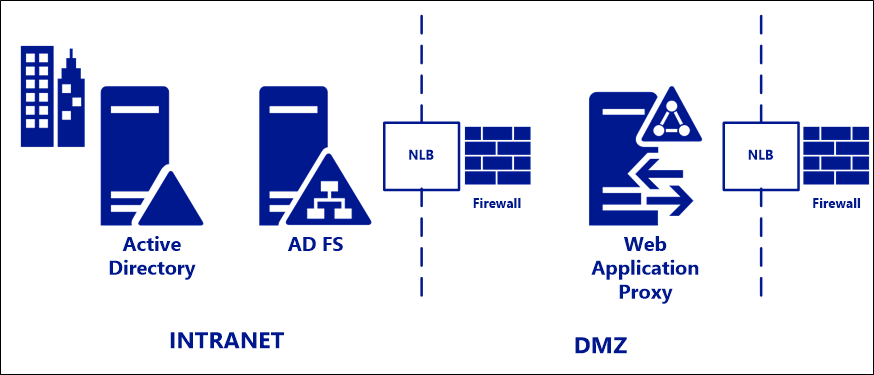
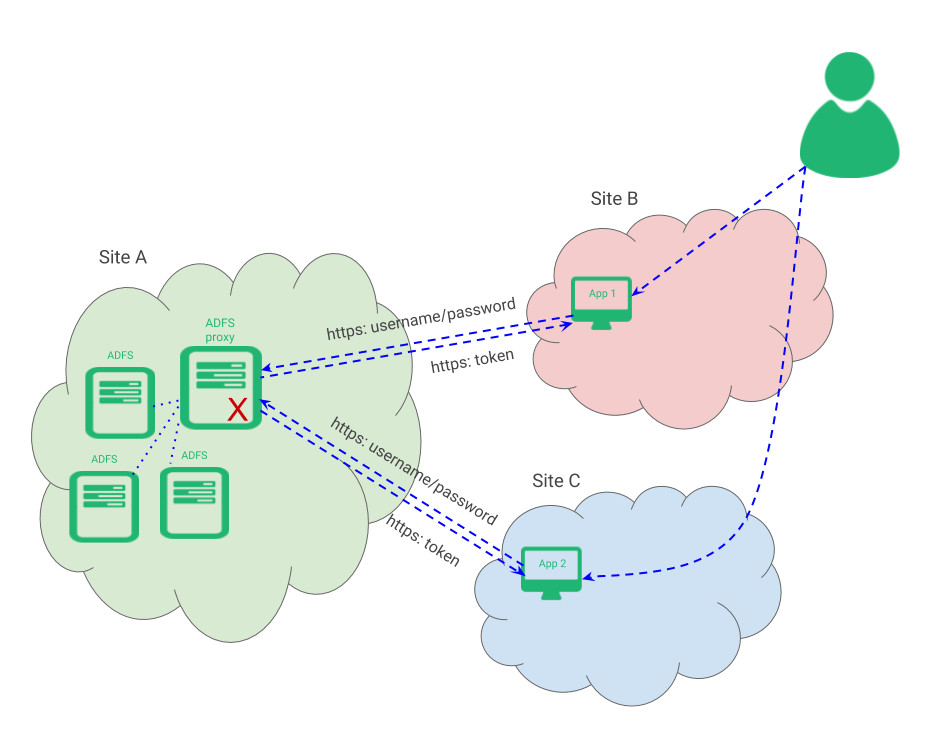
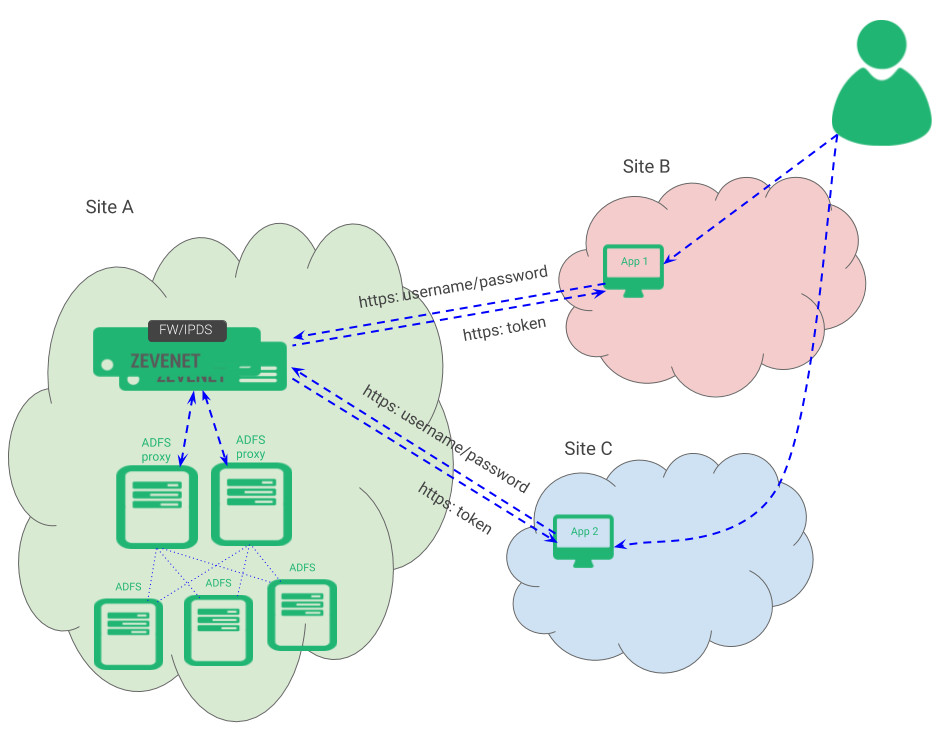
Standard deployment topology
For deployment in on-premises environments, we recommend a standard deployment topology consisting of: •One or more AD FS servers on the internal corporate network. •One or more Web Application Proxy (WAP) servers in a DMZ or extranet network. At each layer, AD FS and WAP, a hardware or software load balancer is placed in front of the server farm, and handles traffic routing. Firewalls are placed, in front of the external IP address, of the load balancer as needed. learn.microsoft.com
Ports required
Communication between Federation Servers Federation servers on an AD FS farm communicate with other servers in the farm and the Web Application Proxy (WAP) servers via HTTP port 80 for configuration synchronization. Make sure that only these servers can communicate with each other and no other is a measure of defense in depth. Organizations can do achieve this state, by setting up firewall rules on each server. The rules should only allow inbound communication from the IP addresses of the servers in the farm and WAP servers. Some Network Load Balancers (NLB) use HTTP port 80 for probing the health on individual federation servers. Make sure that you include the IP addresses of the NLB in the configured firewall rules. Microsoft Entra Connect and Federation Servers/WAP This table describes the ports and protocols that are required for communication between the Microsoft Entra Connect server and Federation/WAP servers. WAP and Federation Servers This table describes the ports and protocols that are required for communication between the Federation servers and WAP servers. learn.microsoft.com
Recommended security configurations
Ensure all AD FS and WAP servers receive the most current updates. The most important security recommendation for your AD FS infrastructure is to ensure you have a means in place to keep your AD FS and WAP servers current with all security updates, as well as those optional updates specified as important for AD FS on this page. The recommended way for Microsoft Entra customers to monitor and keep current their infrastructure is via Microsoft Entra Connect Health for AD FS, a feature of Microsoft Entra ID P1 or P2. Microsoft Entra Connect Health includes monitors and alerts that trigger if an AD FS or WAP machine is missing one of the important updates specifically for AD FS and WAP. learn.microsoft.com
Best practice for securing and monitoring the AD FS trust with Microsoft Entra ID
When you federate your AD FS with Microsoft Entra ID, it is critical that the federation configuration (trust relationship configured between AD FS and Microsoft Entra ID) is monitored closely, and any unusual or suspicious activity is captured. To do so, we recommend setting up alerts and getting notified whenever any changes are made to the feder
Additional security configurations
Extranet "soft" lockout protection for accounts With the extranet lockout feature in Windows Server 2012 R2, an AD FS administrator can set a maximum allowed number of failed authentication requests (ExtranetLockoutThreshold) and an observation window time period (ExtranetObservationWindow). When this maximum number (ExtranetLockoutThreshold) of authentication requests is reached, AD FS stops trying to authenticate the supplied account credentials against AD FS for the set time period (ExtranetObservationWindow). This action protects this account from an AD account lockout, in other words, it protects this account from losing access to corporate resources that rely on AD FS for authentication of the user. These settings apply to all domains that the AD FS service can authenticate. You can use the following Windows PowerShell command to set the AD FS extranet lockout (example): For reference, see Configuring AD FS Extranet Lockout to learn more about this feature. Disable WS-Trust Windows endpoints on the proxy from extranet WS-Trust Windows endpoints (/adfs/services/trust/2005/windowstransport and /adfs/services/trust/13/windowstransport) are meant only to be intranet facing endpoints that use WIA binding on HTTPS. Exposing them to extranet could allow requests against these endpoints to bypass lockout protections. These endpoints should be disabled on the proxy (i.e. disabled from extranet) to protect AD account lockout by using following PowerShell commands. There is no known end user impact by disabling these endpoints on the proxy. Differentiate access policies for intranet and extranet access AD FS has the ability to differentiate access policies for requests that originate in the local, corporate network vs requests that come in from the internet via the proxy. This differentiation can be done per application or globally. For high business value applications or applications with sensitive information, consider requiring multifactor authentication. Multifactor authentication can be set up via the AD FS management snap-in. learn.microsoft.com
|
Load Balancing Microsoft AD FS
Load Balancing AD FS . Persistence (Server Affinity) Requirements & Options. ... Source IP persistence can easily be enabled by modifying the VIP ... |
|
Load Balancing Microsoft AD FS
token session persistence (affinity) is not typically required for load balancing AD FS. The exception to this maybe when the application being accessed is |
|
Deploying the BIG-IP System v11 with Microsoft Active Directory
9 Sept 2015 h If you are forwarding traffic from AD FS Proxy servers to a virtual server load balancing AD FS servers and using the iApp. |
|
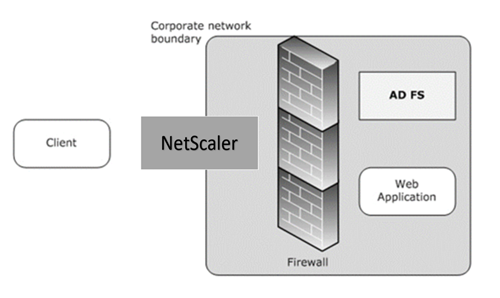
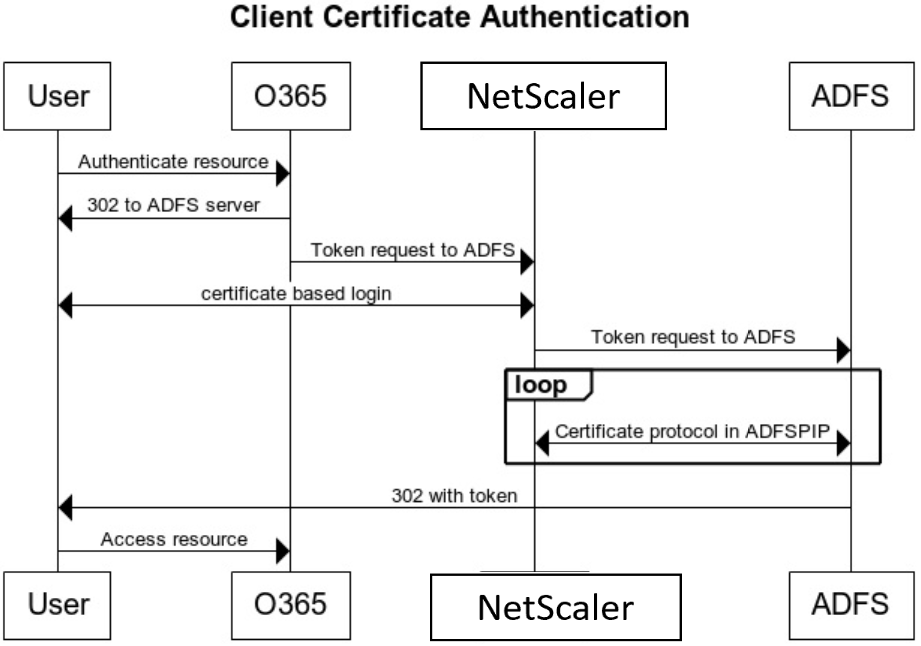
NetScaler as ADFS Proxy Deployment Guide
If you are using the NetScaler ADC for load balancing of your. ADFS proxy farm and other key services only one additional step is needed to set up |
|
Deployment Guide - AX Series with Active Directory Federation
Deployment Guide for ADFS 2.0 and Office 365 Accessing the AX Series Application Load Balancer . ... Cookie Persistence Configuration . |
|
Load Balancing Vmware Horizon
Configuring the VIP & RIPs for the Primary Protocol (Cookie persistence) . It covers the configuration of the load balancers and also any VMware Horizon. |
|
Deploying the BIG-IP System v11 with Microsoft Dynamics CRM 2011
15 Aug 2012 Configuring the BIG-IP system for load balancing ADFS. 7. Configuring BIG-IP Access Policy ... Select the Persistence profile you created. |
|
Deploying the BIG-IP System with Microsoft Dynamics CRM 2015
describes how to configure the BIG-IP system to load balance these AD FS requests. The load balancing pool is the LTM object that contains the servers. |
|
FortiADC Handbook
28 Jan 2022 Configuring AD FS Proxy ... Layer 7—Persistence load balancing |
|
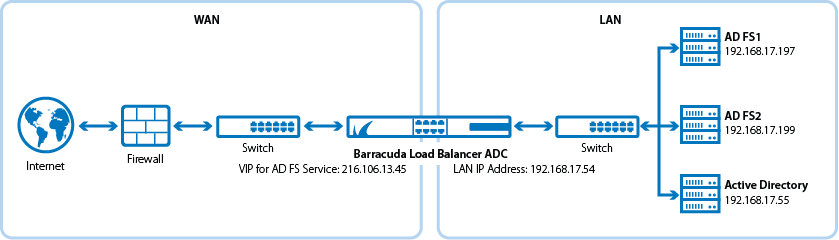
Microsoft Windows AD FS Deployment
and reliability of your Microsoft Active Directory Federation Services (AD FS) deployment. The. Barracuda Load Balancer ADC also improves the performance of |
|
Load Balancing Microsoft AD FS - Loadbalancerorg
Load Balancing AD FS This helps ensure that users can be authenticated and obtain access to the required systems and applications by constantly checking the health of the AD FS servers and only forwarding client authentication requests to functional servers |
|
ADFS Deployment Guide - F5
9 sept 2015 · h If you are forwarding traffic from AD FS Proxy servers to a virtual server load balancing AD FS servers, and using the iApp template, you must |
|
NetScaler as ADFS Proxy Deployment Guide - Citrix
If you are using the NetScaler ADC for load balancing of your ADFS proxy farm Proxy must persist to same STS for multi-legged NTLM auth flow Persistency |
|
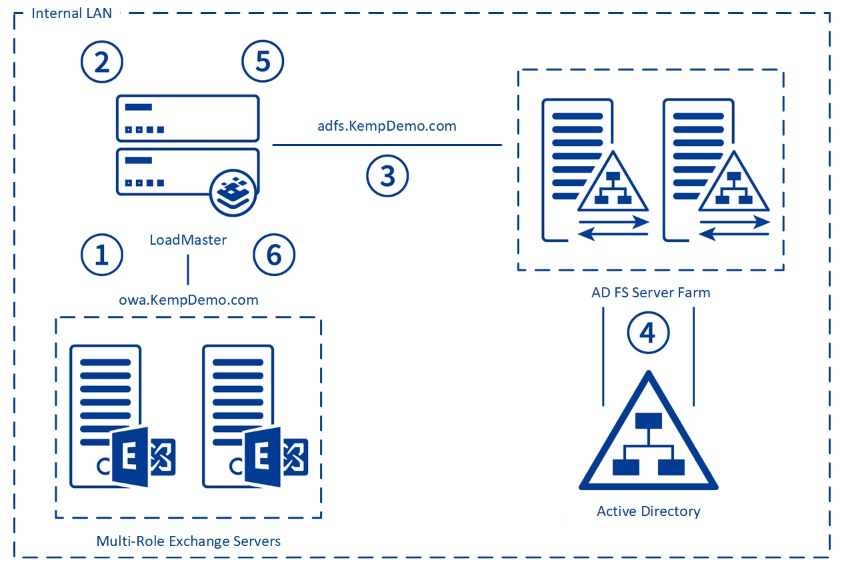
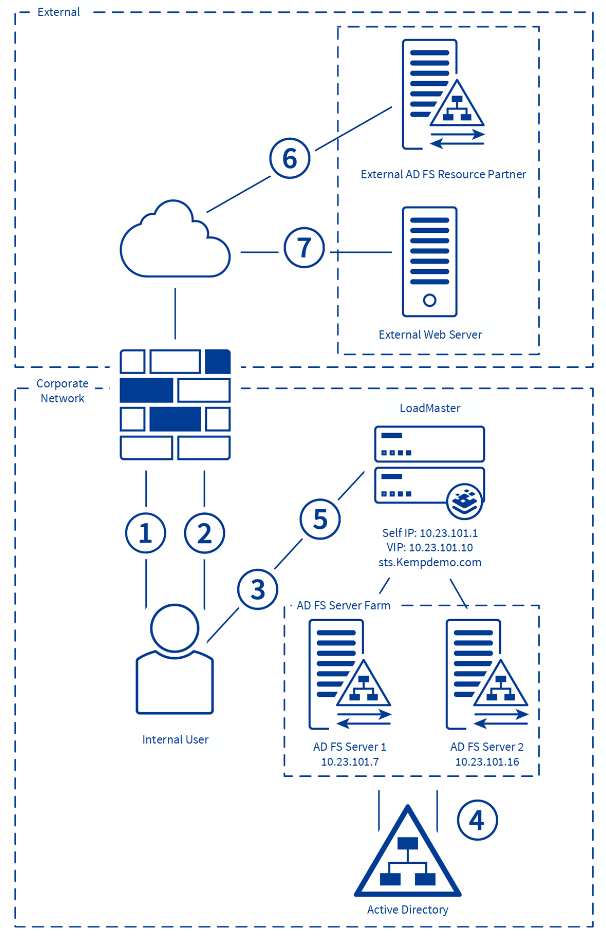
AD FS v3 - Kemp Technologies
3 1 Load Balancing Internal AD FS Servers 6 3 2 Load Balancing AD FS Proxy ( WAP) Servers 7 to allow for the more intelligent forms of persistence that are |
|
Solution Brief - Barracuda Networks
balancing and Global Server Load Balancing (GSLB) capabilities Microsoft Active Directory Federation Services (ADFS) is an Identity and Access The Barracuda Load Balancer ADC's session persistence capabilities also ensure that |
|
Microsoft AD RMS - Array Networks
methods, such as firewalls and ACLs, AD RMS protection is persistent; your AD RMS solution is load-balanced and highly available, even across can deliver high availability for ADFS 2 0 proxy servers that provide secure connections for |
|
BigIP and ADFS Part 1а–а“Load balancing the ADFS Farm” Load
13 mai 2015 · Therefore, specifying a persistence profile is not necessary SSL TUNNELING, ( preferred method)а–аWhen SSL tunneling is utilized, encrypted |
|
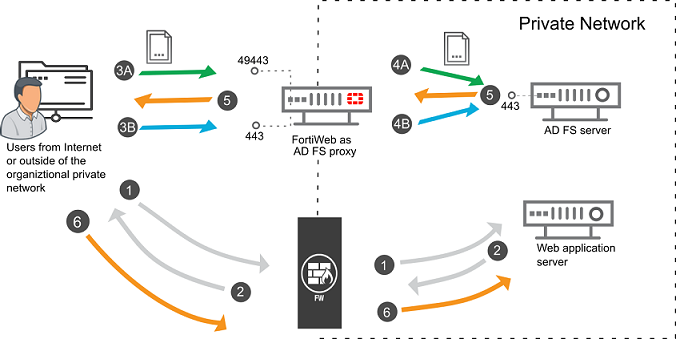
FortiADC Handbook - AWS
2 mai 2019 · The ADFS Proxy is a service that brokers a connection between external users Layer 7 load-balancing, user authentication, and persistence |
|
FortiADC Handbook - AWS
28 août 2020 · Step 6: Configure a basic server load balancing policy Customers can define any persistence rule to distribute real server via Lua script, The ADFS Proxy is a service that brokers a connection between external users and |